Robert Templeman from the Naval Surface Warfare Center in Crane, Indiana and several of his friends from Indiana University recently developed an Android application that is capable of gathering pictures and videos from mobile devices in order to reconstruct a user's environment in 3D. The malware would come coded inside of a camera application that the user would download. The malware, called PlaceRaider, would then randomly take pictures throughout the day and carefully piece them together ...

The pictures we upload online are something we tend to think of as self-expression, but these very images can carry code to steal our passwords and data. Profile pictures, avatars, and image galleries are used all over the internet. While all images carry digital picture data — and many also carry metadata regarding camera or photo edits — it's far less expected that an image might actually be hiding malicious code.

February 21st is going to be a busy day for Android smartphones. Samsung has already scheduled its "Unpacked" event to show off their new Galaxy S7 and S7 Edge handsets, and now LG is joining in on the action, as it will unveil the G5 on the same day, at the Mobile World Congress in Barcelona.

Snapchat hit back at its arch-rival Facebook this week with a number of new Group features, including custom stories. Facebook and Instagram both rolled out clone Story options this year, but Snapchat is obviously trying to up the ante in this arena.

If you're spending hours on your phone playing games like Angry Birds and Candy Crush Saga, or posting online to Google+ and Pinterest, you're probably being spied on. The latest releases from NSA whistle blower Edward Snowden reveal that the National Security Agency, and its UK counterpart, GCHQ, are mining the ad networks utilized in these apps to collect a trove of information on you.
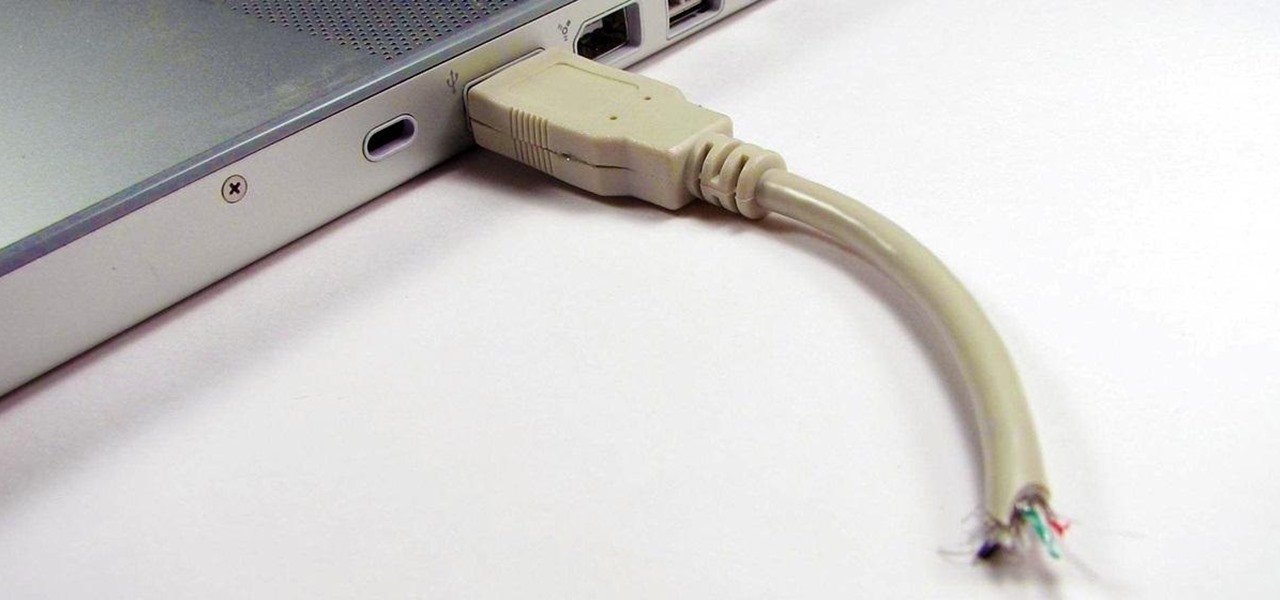
Having a flash drive is more or less a must, but the biggest downside is that they often get stolen, and it's not hard to figure out why. They're small, so they easily fit into pockets, and a lot of people store valuable information on them. Want to pretty much guarantee no one takes yours? Disguise it as a broken USB cable like Windell Oskay of Evil Mad Science Labs so it just looks like a piece of junk to would-be thieves. The materials are pretty simple: a flash drive (the smaller the bett...

It's 3 a.m. and you're wide awake—your mind is running wild with worries, workplace stress, and panic about the day that lies ahead. How can you possibly slip back into sleep and snag a few more hours of rest when you're so anxious?

A long time ago, we recommended the Hover Zoom extension for Chrome as an easy way to blow up small image thumbnails without actually have to "click" on the images themselves. Over the past year, there have been reports that Hover Zoom now collects and sells your browsing data to third-party advertisers without your consent.

Many popular apps automatically share your personal data. While I have accepted a certain amount of data collection from Google, to know companies such as Facebook perform this without my consent bothers me. After some researching, I've found a great solution, and it doesn't require root.

While Wi-Fi networks can be set up by smart IT people, that doesn't mean the users of the system are similarly tech-savvy. We'll demonstrate how an evil twin attack can steal Wi-Fi passwords by kicking a user off their trusted network while creating a nearly identical fake one. This forces the victim to connect to the fake network and supply the Wi-Fi password to regain internet access.

Identity theft typically occurs when someone uses your personal information such as social security numbers, credit card numbers or account information to perform various misdeeds, and you are left to clean up the mess.

If you're scared of using public Wi-Fi networks with Firesheep out and about, then maybe you should fight back. Don't switch to another web browser— keep using Firefox safely with the help of a new Firefox Add-on that combats Firesheep's password stealing capabilities. It's called BlackSheep, and when installed and running, it will alert you whenever Firesheep is active on your network connection.

There's nothing more maddening than opening the office fridge and discovering your lunch is gone. Put an end to the stealing with some of these strategies. This video will show you how to deter coworkers from stealing your lunch.

Want to learn how to play Chuck Wicks on the guitar? With this tutorial you can learn how to play "Stealing Cinderella" by Chuck Wicks on the acoustic guitar. The capo is on the 1st fret used in standard tuning. This version is a simplified version of the song and is not exactly how Chuck Wicks play it. This lesson is geared towards intermediate guitarists because it assumes prior knowledge of guitar playing. Watch this how to video and you will be able to sing and play along to "Stealing Cin...

She thinks just because you're related that your closet is her closet; and if she ever gives your things back, they're never washed. If it's time to stop your sister from being a closet bandit, check out this video. This tutorial is full of tips for gettinf rid of that pesky sibling and keeping your clothes all to yourself.

Does your network begin to crawl right around the time your sinister-looking next-door neighbors get home from work? Do you harbor suspicions that one or more of them may be stealing your Wi-Fi? It's easy to find out. And equally easy to give freeloaders the boot. In the guide below, we'll show you how to secure your wireless connection in three easy steps.

When downloading any application on an Android device, you will always be prompted by the following... Whether it's Angry Birds, Shazaam, or Chrome, every application will ask for permissions. If you try and deny these permissions, it won't install, leaving you with no other option but to accept. So what can you do?

This guide is a little humerous, but it details the way in which you can hide your chests in Minecraft so that you can stop people from stealing your items in the game. The trick involves a pretty crafty way to build your house.

JavaScript is one of the most common languages used on the web. It can automate and animate website components, manage website content, and carry out many other useful functions from within a webpage. The scripting language also has many functions which can be used for malicious purposes, including stealing a user's cookies containing passwords and other information.

Developed by Open Whisper Systems, Signal is a free, open-source encrypted communications app for both mobile and desktop devices that allows users to make voice calls, send instant messages, and even make video calls securely. However, a vulnerability was recently discovered for the desktop version that can be turned into a USB Rubber Ducky payload to steal signal messages with a single click.

If you live in New York City and are itching to sell your Yeezys, you're at risk of falling victim to thieves. A devious duo is searching Facebook to find people selling the popular sneakers and then robbing them at gunpoint when they meet up in person.

If you need a tiny, flexible attack platform for raining down human-interface-device (HID) attacks on unattended computers, the USB Rubber Ducky is the most popular tool for the job. By loading the Ducky with custom firmware, you can design new attacks to be effective against even air-gapped computers without internet access. Today, you'll learn to write a payload to make "involuntary backups" through copying a targeted folder to the Ducky's USB mass storage.

All-Star Harold Reynolds shows the proper techniques for stealing, running the bases more effectively and mastering the base paths! Baserunning is a valuable skill for earning runs and stealing bases. Steal and run the bases with Harold Reynolds.

On MLB channel, Rickey Henderson shares some base-stealing secrets with Barry Larkin and Harold Reynolds. Henderson has a record for stolen bases. It requires speed, agility, good judgment and decisiveness. Steal bases with Rickey Henderson.

The Call of Duty Black Ops Zombies (that's a mouthful) map Ascension introduced perk-stealing monkey to the bestiary of enemies. They are quite annoying, and this video will teach you how to deal with and dispatch them easily, keeping your precious perks intact for better zombie slaying.

SCRABBLE. To some it's just a game, but to me it's life or death. Well, not really, but it feels that way anyway. On a normal weekend, a game becomes much like Jon Thomas' "friendly game of death Scrabble."

Want to hack a LAN? Well, hacking local area networks is easier than you'd think. And by watching a few short videos, you can become a master hacker, something every techie wants to achieve. And what's the best way to hack a LAN? Ettercap, a password sniffing program.

Someday, maybe not today, maybe not tomorrow, but someday, you'll find yourself on the road in your car, maybe on the highway, and you'll hear something.

This video will teach you how to hack a WEP wifi network on a Mac. You'll need to follow the link, grab the prog and follow the steps. It's not too hard, so give it a try. Remember, stealing is illegal!

Girls around the world bemoan their boyfriends constantly stealing their shampoo when they run out, and now it's time for payback. This video demonstrates a hair bleach and shampoo prank that will devastate dark-haired shampoo-stealers.

In this video, presented by the experts at the St. Louis Community Credit Union, learn how to prevent thieves from stealing your identity or account information. These days, between paper bills, Internet banking, social networking and all the other ways we interact, there are many ways for crooks to get into our private lives.

Okay, so first things first: the con presented in this bar trick video is illegal since you're basically stealing money, so perform at your own risk!

In this episode of Full Disclosure we are explaining the website attack known as Cross-Site Scripting (XSS). Cross-Site Scripting is a type of security vulnerability that affects web applications that do not sanitize user input properly. This kind of vulnerability allows an "attacker" to inject HTML or client side script like JavaScript into the website. Cross-Site Scripting is most commonly used to steal cookies. Cookies are used for authenticating, tracking, and maintaining specific informa...

Check out this strength trick from Revision3, Brian Brushwood and Scam School. We're back with another dirty trick, designed to teach you how to FAKE your way into (almost) duplicating the feats of the world's strongest men.

Want to get a pantload of energy and silver in about half a minute, with no damage to your karma or reputation meters? You can raid the Silver Rush casino by sneaking around and stealing the various caches from the store.

In this clip, learn how to turn a delicious sandwich into a moldy mess. This sandwich is perfect for Halloween, April Fools Day or just a fantastic way to keep other kids from stealing your school lunch. With a little powdered sugar and a bit of food coloring, you can turn an ordinary PB&J into a fuzzy, green treat.

Geoff walks us through getting the "Chain Reaction" Achievement in GTAIV.

Because life's just not fun unless someone is getting pranked. Whether you need to pull these pranks out for a party or to get back at your younger brother for stealing that last piece of fried chicken, you'll learn a whopping list of 8 different pranks in this video.

Cranberry sauce is one of the most important side dishes to any Thanksgiving dinner—even Christmas dinner! And if you're like me, you usually buy a can of cranberry sauce for the holidays because you don't have the extra time to go homemade with the turkey stealing the show.

Looking for something fun to do with all those office supplies you've been stealing from work? Or maybe you just want to goof around in your cubicle? It's possible that you are an honest, dedicated, hard worker, but whatever the case may be- no judgement, just a video guide to making an office supply catapult.