
How to Hack Databases: Hacking MySQL Online Databases with Sqlmap
Welcome back, my amateur hackers!


Welcome back, my amateur hackers!

Welcome back, my greenhorn hackers! I've been writing these Linux tutorials in an attempt to fill the void in the education of some aspiring hackers into the Linux operating system. There is a lot to know, and in this tutorial, we'll look at Linux file permissions. Step 1: Checking Permissions

A stager is a small piece of software that's typically used by malware to hide what's happening in the early stages of infection and to download a larger payload later.

Samsung Health has become one of the most comprehensive wellness apps thanks to features that cover everything from step counting to nutrition logging and symptom diagnosis. But because the app has so much to offer, it can be easy to overlook some smaller, but useful features.

Razer just released their first flagship Android smartphone, appropriately named the Razer Phone. While mobile gaming fans are sure to enjoy the Razer Phone, the buttery-smooth 120 Hz display makes this an appealing option for anyone in the market for a new phone. If you've just picked up the Razer Phone or it's piqued your interest, here are ten awesome tips to hit the ground running.

Welcome to the sequel to the latest post on writing 64 bit shellcode! This tutorial will assume that you are aware of everything mentioned in the last one, as I will try to make this tutorial void of formalities and straight to the point! If you have not read the last one, I suggest doing so unless you are familiar with basic assembly programming and system calls. This is by no means rocket science, so therefore I will simply repeat my TL;DR from last time before we get started, so that the a...

People who know that I am a professional hacker often ask me what they can do to make their computers and personal information safe from people like me. The answer, of course, is that nothing will make you completely safe, but there are a number of measures any computer user can take to reduce the chances of being a victim of a hacker.

Despite its name, the Frequently Used section on your iPhone's emoji keyboard features both frequently and recently used emoji, and it may contain emoji you've never even touched. If you want to remove all of those recommendations, there's an easy way to reset what you in Frequently Used to the defaults.

While iOS 11.3 doesn't have as many new features as iOS 11.2, there's still a lot to love about Apple's latest update for iPad, iPhone, and iPod touch, even if some of the best features we were expecting didn't make the cut.

One of the smaller frustrations of the coronavirus pandemic is unlocking your iPhone with Face ID while wearing a mask. If you have an iPhone with Touch ID, you won't need to punch in your passcode every time Face ID fails since you can use your fingerprint. But for those of us without Home buttons, unlocking our iPhones just got a lot easier — even if we're wearing a mask.

Apple's scheduled to show off the first look of iOS 13 at WWDC 2019 on June 3, but what will the new operating system hold for iPhone? Rumors suggest that many features initially planned for iOS 12 will show up in iOS 13, codenamed "Yukon," and dark mode will be the big ticket item this year.

Think back to when you last wanted to transfer some music or videos to your friend's smartphone and how difficult and slow it was. As powerful as our phones are, the default file sharing options are limited. There are, fortunately, some better options which make moving files easy, secure, and painless.
You're probably sharing a ton of information on your iPhone with other people, apps, and services without really realizing it. Now there's a new tool to show you just how much, and it can be an eye-opener as well as a fast way to manage sharing permissions and review your account security.

Your voice is the key to unlocking many features on your iPhone. For example, you can ask Siri to send a text message to a friend, add items to a list, run a custom shortcut, or turn on your lights, but Apple does not allow you to unlock your iPhone with a Siri voice command. Instead, you can turn to a lesser-known feature to unlock your iPhone without Face ID, Touch ID, or typing your passcode.

While there's no denying that iPads are better when it comes to multitasking and productivity, your iPhone has a few tricks up its sleeve to rival even the best iPad features. One thing about iPadOS is that it's really easy to highlight editable text with gestures, but it's just as simple on iOS if you know all the secrets.
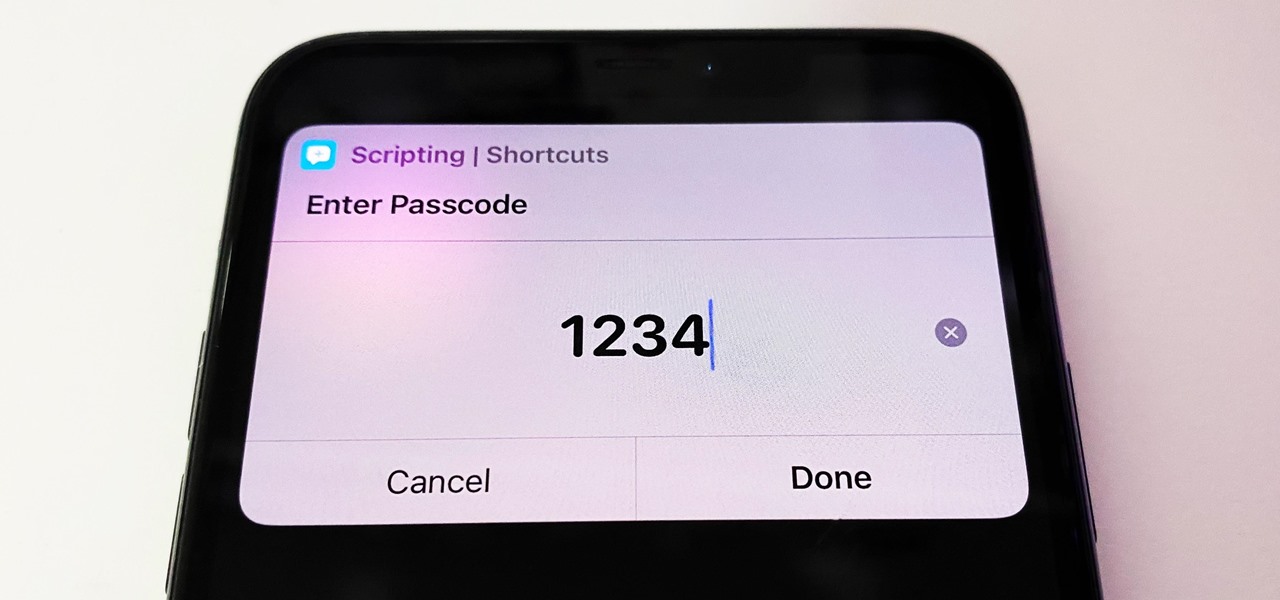
Some iOS and iPadOS apps give you an option to lock them behind Face ID, Touch ID, or a passcode, but there aren't many.

Are you tired of endless rows and columns of apps on your home screen? Before iOS 14, your only option was to hide apps in folders, uninstall them, or use some sort of elaborate workaround. You could hide a few stock apps easily enough, but that's it. Now, in the latest version of iOS, you can hide apps for real, and even hide entire home screen pages, and still access the apps in one convenient drawer.

The Calculator app is probably one of Apple's most-used iPhone apps, yet I always meet people who don't know all the little tricks there are to using it more efficiently. You may know most of them, but there's a chance you don't or at least forget about some of them.

Apple's stock keyboard for iPhone has gone through many changes over the years. Some have been significant, and others more subtle. Overall, most of these updates have been fairly obvious, so you're probably already using them — but there are more than a few interesting features that were slipped in under the radar that you may not know about.

This is one of the many great features of Windows 7 and If you don't have windows 7 I would definitely recommend it. This feature allows you to have multiple background images and windows change them to however often you choose.

The Motorola XOOM was just released last week to Android-hungry fans waiting the next best thing to Apple's iPad. But should it have been released, considering Verizon's switching to the 4G LTE network soon?

This video demonstrates how to add a data table to an Excel 2007 chart. From the people who brought you the Dummies instructional book series, brings you the same non-intimidating guides in video form. Watch this video tutorial to learn how to add a data table to an Excel 2007 chart, For Dummies.
To create an elegant WordPress blog or website from scratch without being noticed that you're a complete beginner, you need that drive and pairs of eyes and ears. It may seem difficult at first but it can truly be fun and exciting.

100% functional LEGO ATM by Ronald McCrae. This bonafide brick bank performs the following functions:
QR Code is a 2D barcode symbology capable of encoding all types of data, such as numeric, alphabetic characters, Kanji, binary, text, url etc. To build a qr code generator in Microsoft Visual Studio, we can use a qr code generator .NET DLL by Avapose.com and follow these steps:

Alan Parekh's latest creation is a clock made from wooden gears. Parekh says on Hacked Gadgets:

More password cracking action from Null Byte! Today we aren't going to be cracking passwords per se, rather, we are going to learn the basics of generating rainbow tables and how to use them. First, let's go over how passwords are stored and recovered.

Gone are the days when you had to carry a clunky DynaTAC to make phone calls, pocket phone book for you contact list, Sony Discman for your tunes, and wallet for you cash and credit cards. Today, all you need is your smartphone. To be specific, Google's Nexus S 4G on Sprint.

From ZDNet: "A group of students in China have created PhotoSketch, a project that does exactly what I just described: it takes a rough, hand-drawn sketch, scours the web for photos that match, and runs them through an algorithm, stitching it all together."

Last week's round up was all about third party services that sprang up to fill any Google+ voids. This week, I'll let you know how to keep up with the latest Google+ updates, and give you some great tips for interacting with your followers.

This 3D software tutorial shows you how to use the affect region modifier in 3ds Max. The Affect Region modifier is a 3D Studio Max surface modeling tool, primarily used with vertex sub-object selections while surface modeling. With Affect Region, transforming a selection of vertices can also transform vertices in the region that surrounds the selection. This can help you form a bubble or indentation in the surface of an object. The easiest way to see this modifier’s effect is with a shallow,...

In these text messaging how to videos for cell phone users, learn how to send text messages. It’s easy. Our expert will walk you through different types of mobile phones and the text features they have. Then learn how to use a numeric keypad to type in letters, numbers and symbols, as well as how to use the T9 texting tool that most phones have available. Once you’ve composed your missive, learn how to send the text message, using a cell phone, a smart phone or PDA. It’s no use talking to you...