The keyboard is one of the biggest weak points of iOS devices, in part due to the lack of an option to add a number row. Fortunately, there is a way to quickly switch between the numeric and alphabet layouts on your iPhone or iPad's keyboard.
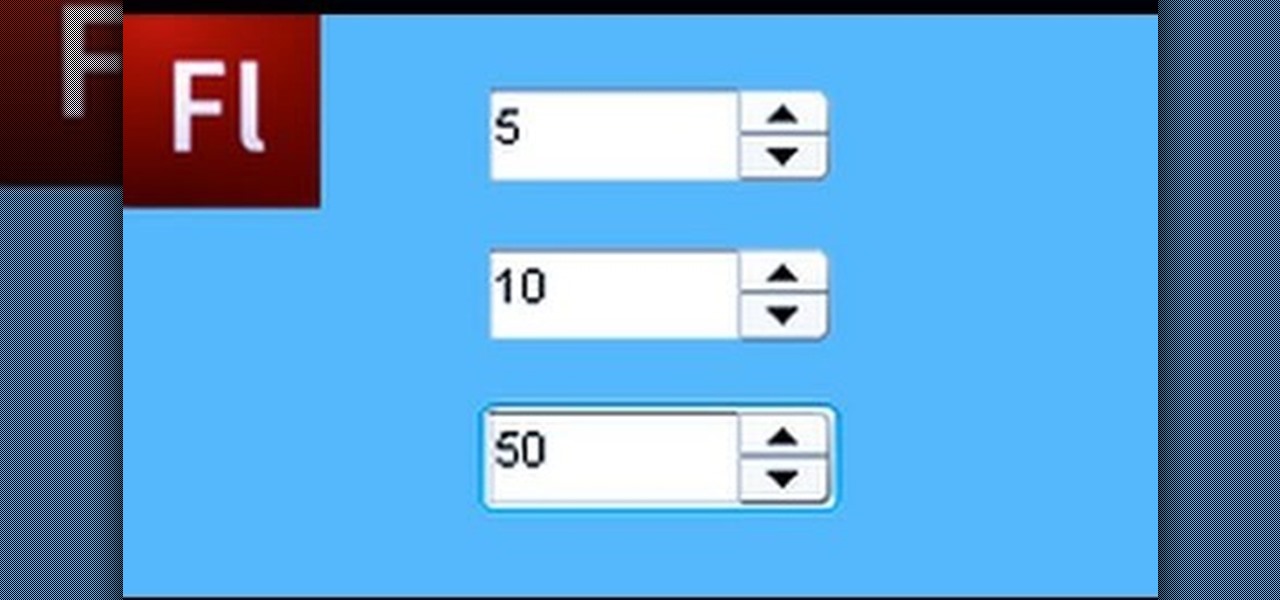
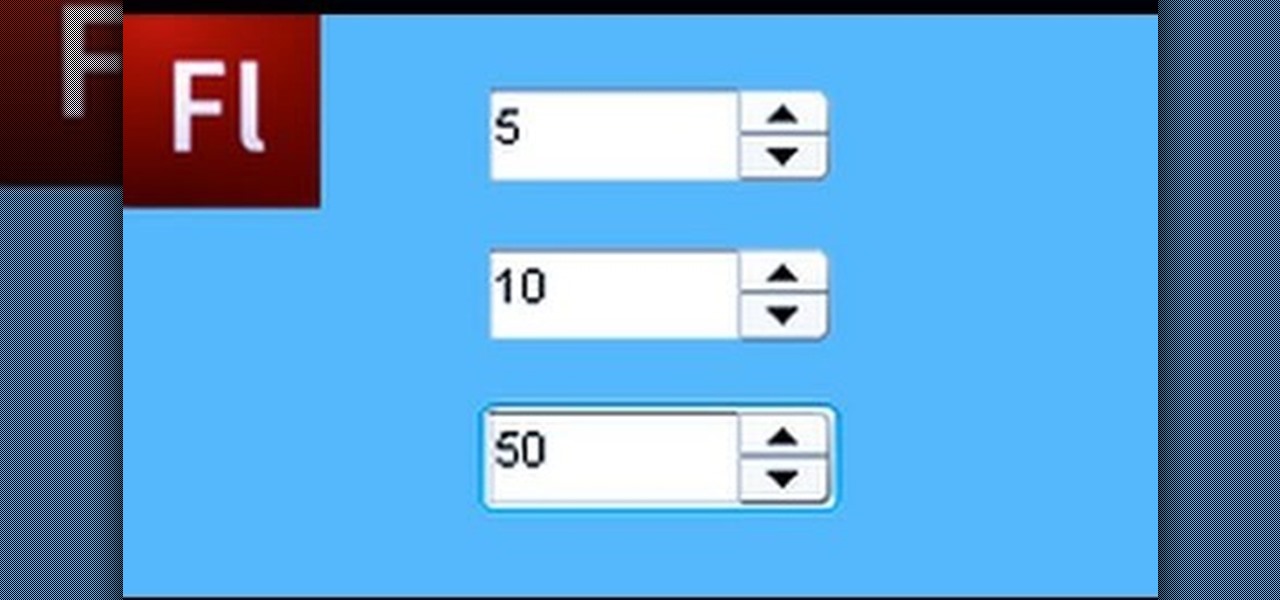
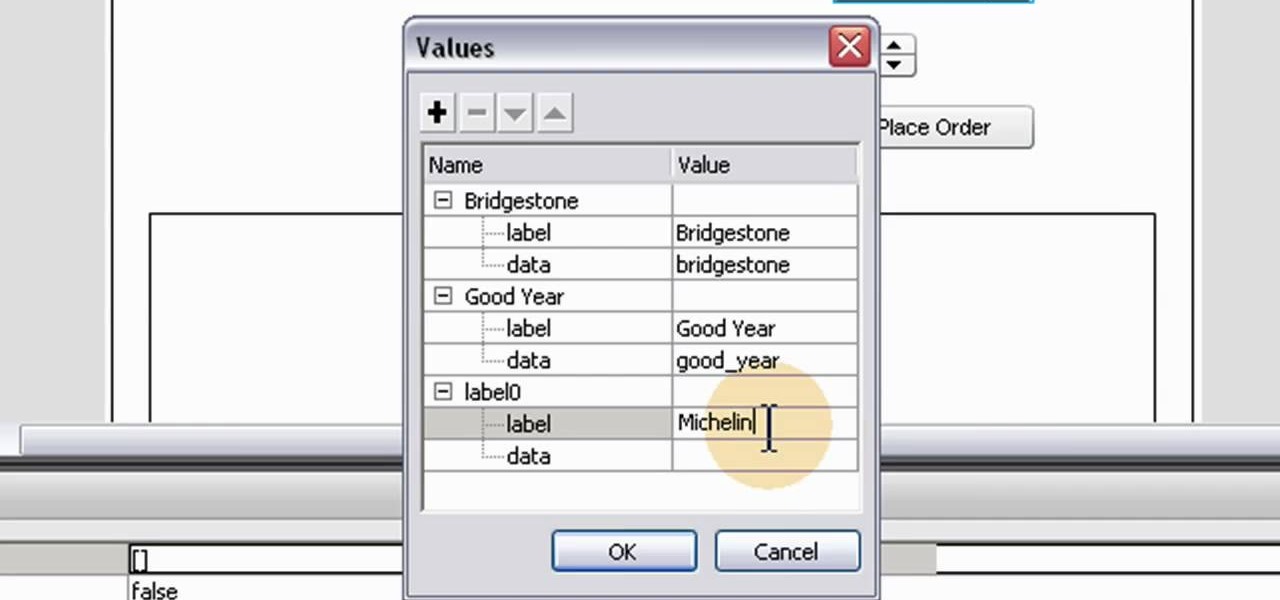
The Numeric Stepper component in Adobe Flash CS 4 is a small but very useful feature which allows users to select any number in a particular quantity - such as giving a birthday or indicating how many of a particular product they want to buy. Watch this tutorial to learn how you can use the Numeric Stepper component for your own projects.
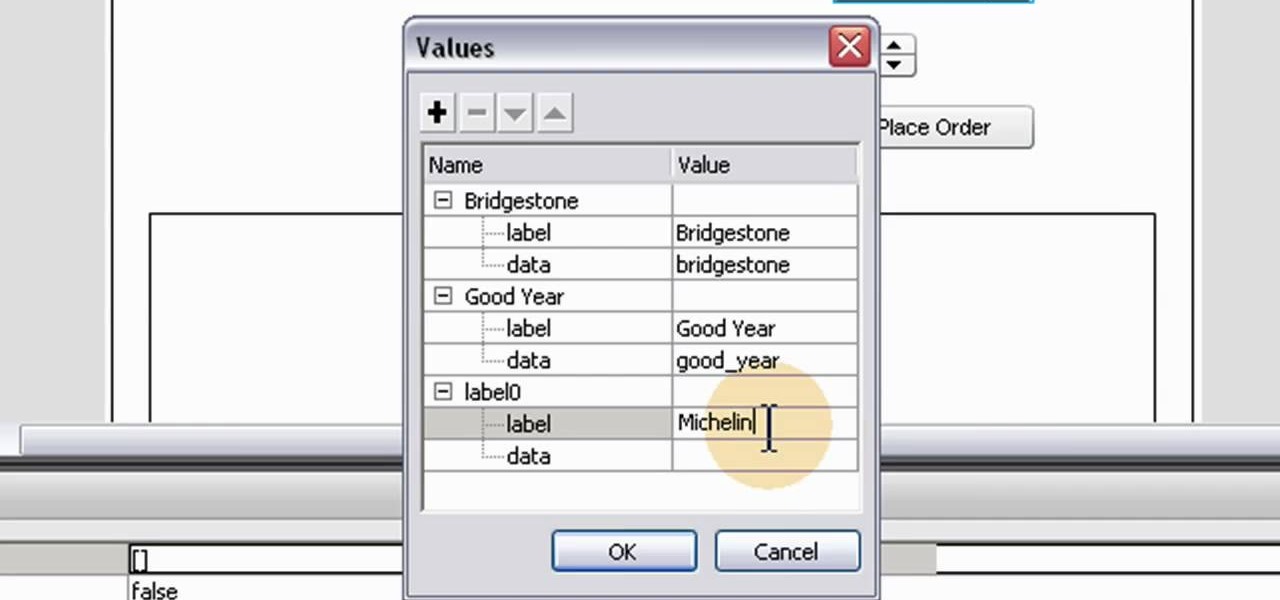
A numeric stepper component is one which you can add to your website to allow users to select numbers or from a list of avaiable items - useful, for instance, if you wanted a webstore which allowed for a quantity function. This Adobe Flash CS3 tutorial shows you how to create and use a numeric stepper component.
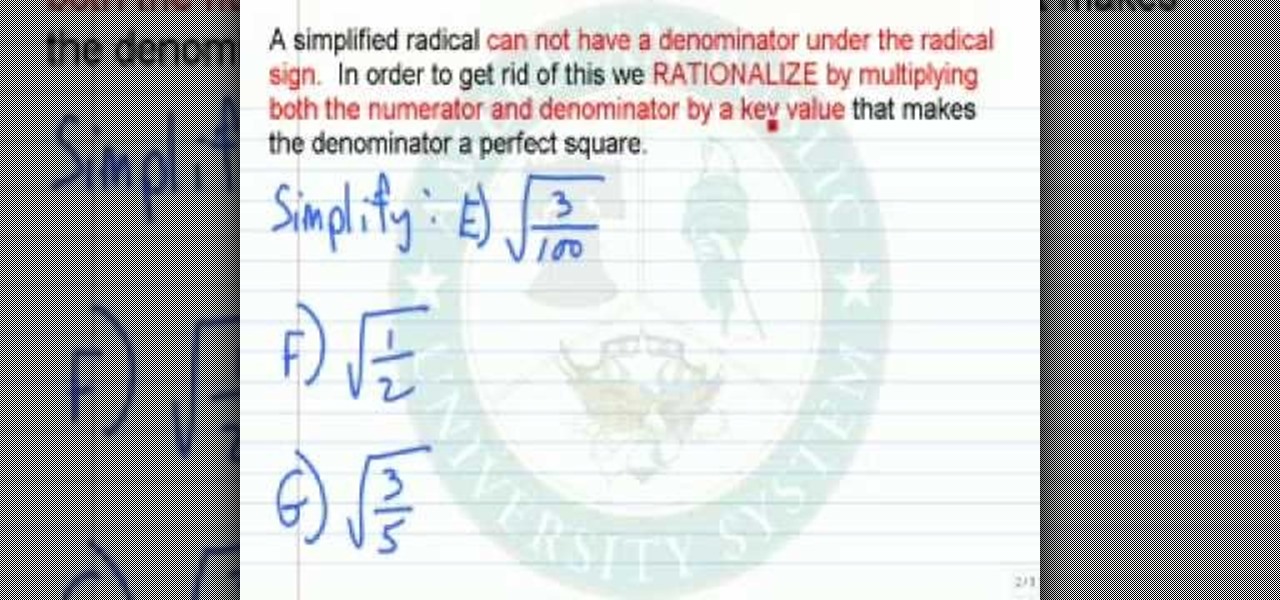
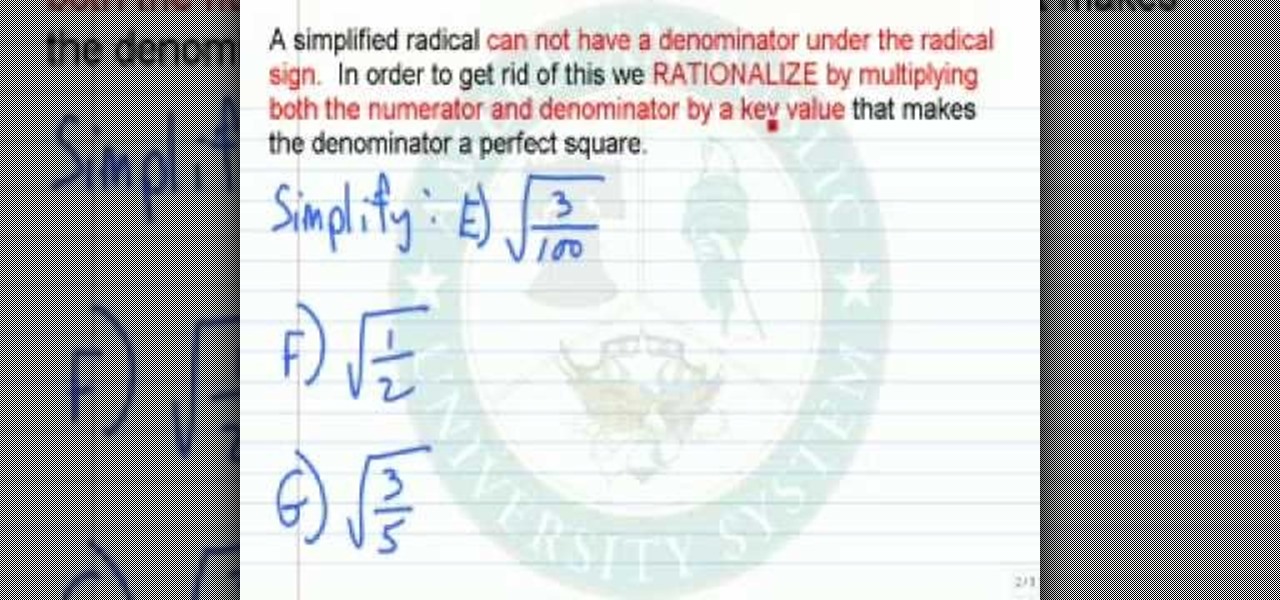
In this video tutorial, viewers learn how to simplify expressions involving numeric radicals. This can be very frustrating to work with if you have not memorized the tables of square, cubes and fourths. If you are taking the square root of a number that is not a perfect square and you wish to simplify it, the key is to write it as the product of a perfect square or another number. This video is very descriptive and clearly explains the functions of the formula. This video will benefit those v...
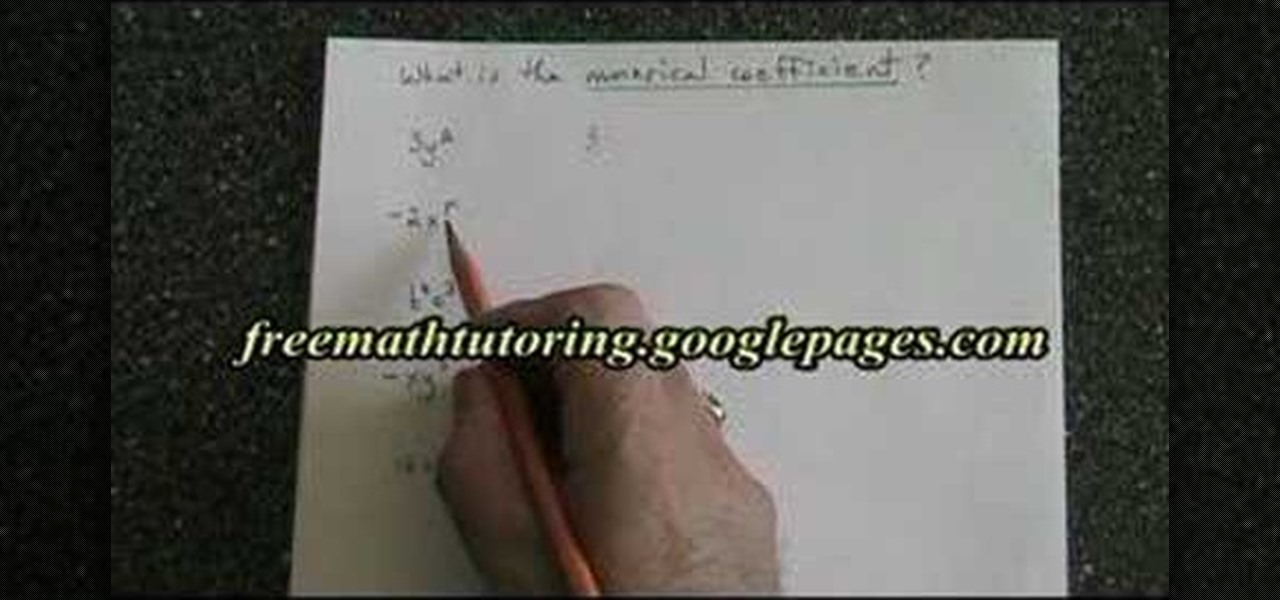
In this tutorial the instructor discusses about the numeric coefficients that we come across while we work with polynomials. He goes on to discuss the numerical coefficient of a monomial stating that it is the number that is present before the variable in the monomial. He states that the numerical coefficient can also be negative or if there is no number present in front of the variable, it indicates that the numerical coefficient is one. This video helps in understanding what the numerical c...

Make your own version of the $1500 Qlocktwo, a clock that literally spells out the time for you. Instructables member drj113 shares instructions for making a much cheaper alternative. Click through to do-it-yourself.

In this episode of Red Giant TV, Aharon Rabinowitz gives you some cool tips for working with Numeric Text, for things like video game scores and other digital readouts. No third-party Plug-ins are used in this tutorial. Whether you're new to Adobe's popular motion graphics and compositing software or a seasoned video professional just looking to better acquaint yourself with After Effects, you're sure to be well served by this video tutorial. For more information, including detailed, step-by-...

There are tens of thousands of iPhone applications out there. Some are fabulous. Some are stinkers. From boredom-busting games to truly useful utilities, Fox News Tapped-In tell you which are worth a place on your iPhone. Their concise video reviews and how-tos let you see the apps before you download. Plus, they show you tips and tricks you never knew were there. If you own an Apple iPhone or iPod, check this vodcast out.

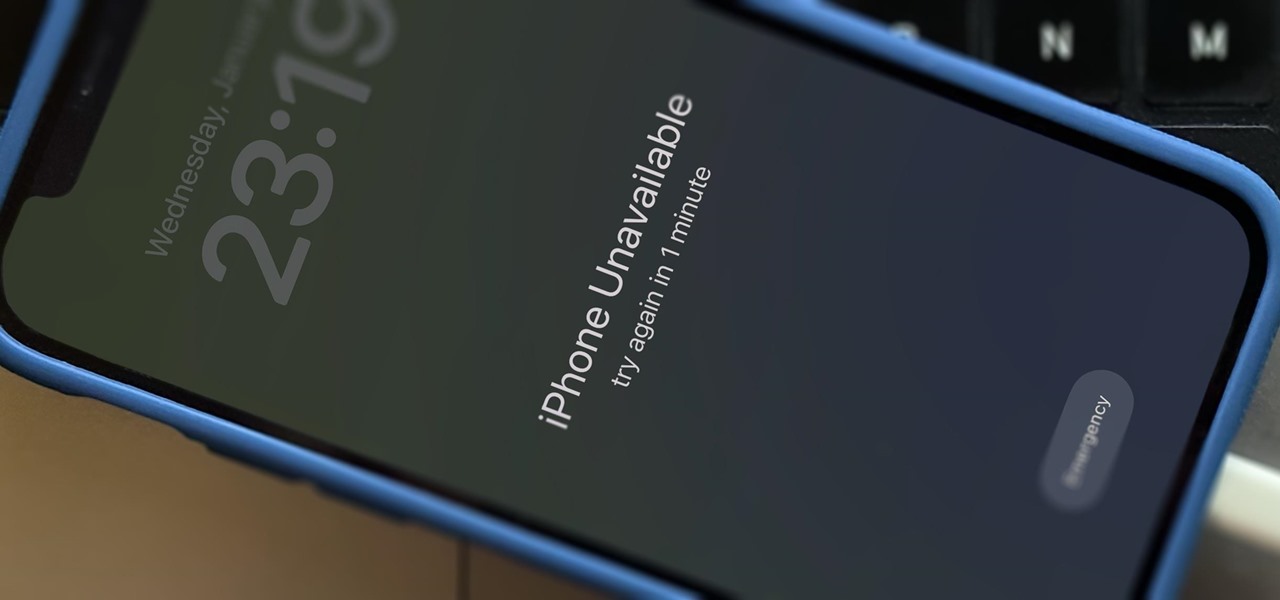
There has been significant debate over law enforcement's right to access our digital devices in recent years. New tools from Grayshift and Cellebrite are popping up faster than ever to help government agencies, as well as traditional hackers, break into iPhones. If you're concerned, you can take steps right now to beef up your passcode and prevent outsiders from gaining access to your device.

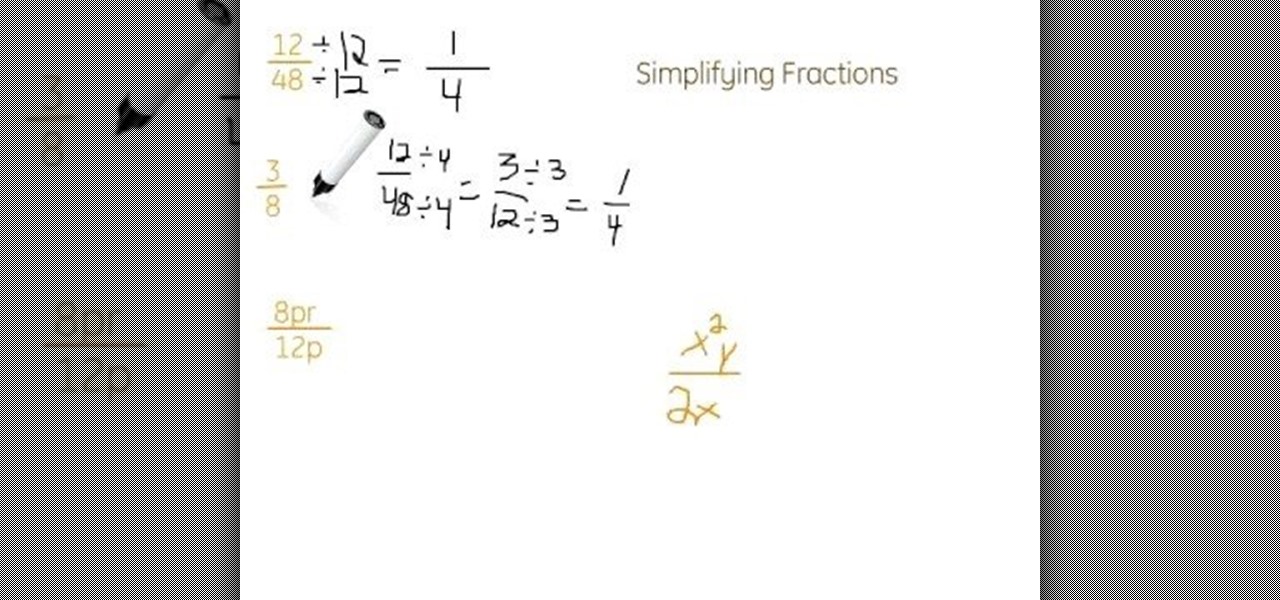
Need a little help figuring out how to reduce either numeric or algebraic fractions? Learn how with this free video lesson. From Ramanujan to calculus co-creator Gottfried Leibniz, many of the world's best and brightest mathematical minds have belonged to autodidacts. And, thanks to the Internet, it's easier than ever to follow in their footsteps (or just finish your homework or study for that next big test).

This software tutorial is on downloading and using Sizer to resize windows for exact screen grabs. Sizer is a free open source software that allows you to size a window to an exact numeric size instead of dragging the window around randomly. This is great for screen recordings with softwares like Camtasia, or for image screen grabs. See how to download and use Sizer in this tutorial.

Many of the modo tools have extra controls via Advanced Handles. Advanced handles have corner handles and numeric readouts. This quick clip reveals some hidden goodness in the Cube tool and shows you how to use the advanced handles in modo.

This 3D modeling software video covers multiple tools that will help you be more accurate and precise when building in SketchUp. SketchUp has many tools that make it easy to be creative when designing buildings or models, but it's just as important that they be accurate. Learn how to use numeric values and SketchUp tools to add accuracy and realism to your work.

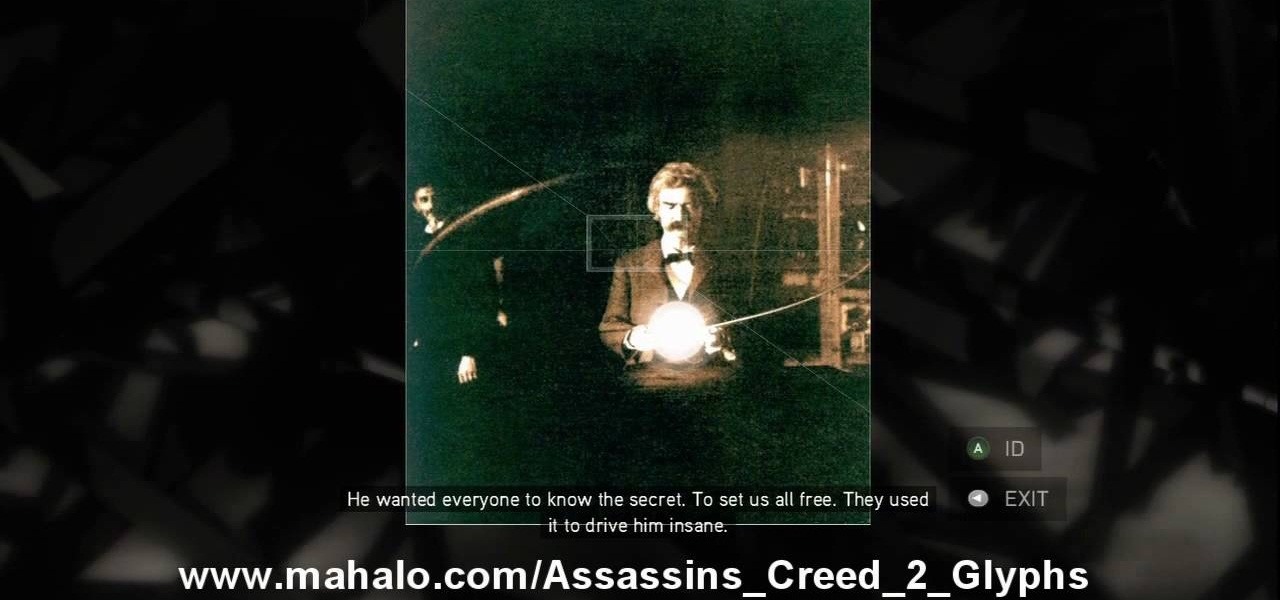
This is the 12th puzzle, entitled "Titans of Industry", in Assassin's Creed 2. Code wheel puzzle 1: The key here is in the “4=1” on the blueprint at the left of the screen. Line up the red 4 over the gray 1 and input the following code: 917240. Image 1: This one’s the opposite of the light-bulb “puzzle” from before – just move the dollar sign over the bulbs to extinguish them. Image 2: Highlight the glowing ball at the center of the image. Code wheel puzzle 2: Your hints here are the “2” on t...

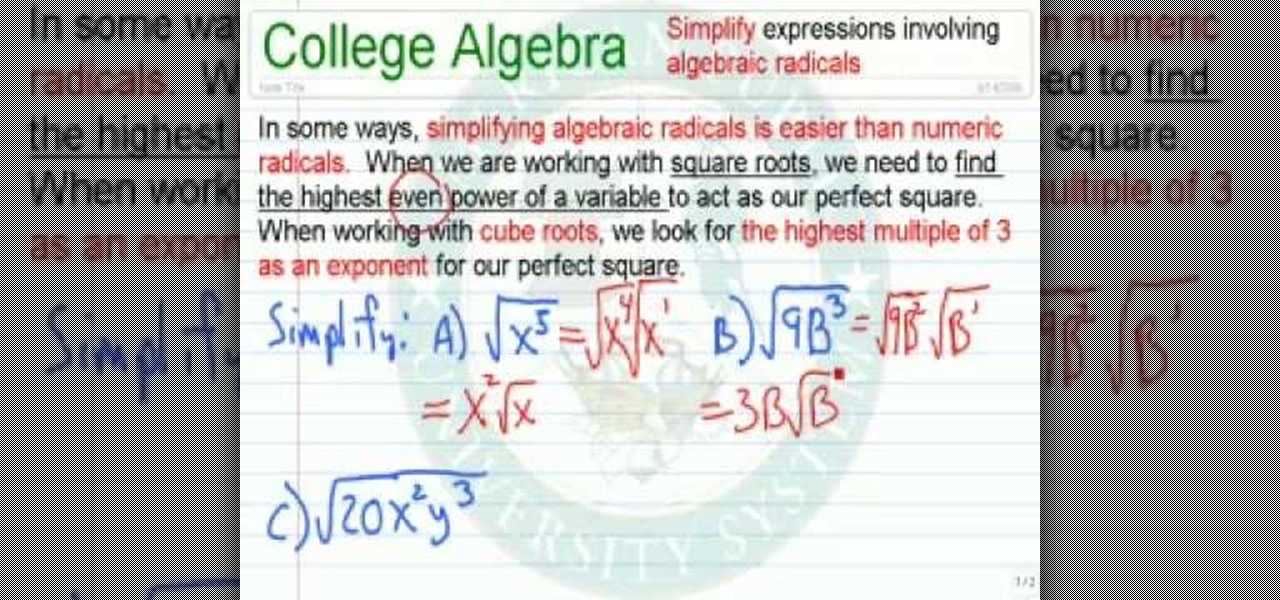
In this video tutorial, viewers learn how to simplify expressions involving algebraic ratios. In some ways, simplifying algebraic radicals is easier than numeric radicals. When we are working with square roots, we need to find the highest even power of a variable to act as out perfect square. When working with cube roots, we look for the highest multiple of 3 as an exponent for our perfect square. This video is very descriptive and clearly explains all the functions of the formula. This video...

In this video the instructor shows how to find the slope of an equation which is in the form Ax + By + C = 0. He says that the formula to find the slope of a line in the above form is slope m = -A/B, where A and B are the numeric constants of the variables x and y in the given equation. He goes on and further shows how to do this with a couple of examples. He shows how to reduce any equation into the general form and how to apply the slope formula then. This video shows how to find the slope ...

Feeling lost inside a library? The Dewey Decimal System is a logical and popular book classification system for libraries and schools helping you to easily locate any book or periodical you need. Fool these steps to better understand the Dewey Decimal System.

RIP Touch ID. Apple's fingerprint sensor on iPhone and iPad models with Home buttons is about to become phased out on Wednesday, Sept. 12. While Touch ID will remain an integral part of models from the iPhone 5S to the iPhone 8 Plus, as well as the iPad Air 2 through the sixth generation iPad, Face ID will completely take over as the default security method for unlocking future iOS devices.

The horizontal dotted icon in your iPhone's status bar serves as an indicator of your device's network strength. And while it does help provide an approximation of how strong your signal is, swapping it out to display an actual numeric value is a lot more precise and can change up the look of your iPhone (or at least the status bar). The process is quick, painless, and you don't even need to jailbreak your phone.

When you first set up an iPhone, you'll be prompted to create a six-digit passcode to unlock your screen and access certain system settings. If you skip this step, you can always go back and create one, which we highly recommend. Without a passcode, everything on your iPhone is accessible by anyone who gets their hands on it — nosey friends, hackers, thieves, local law enforcement, the FBI — and you don't want that, do you?

In After Effects 6.5, Adobe introduced Incremental saves. Rather than waiting for the auto-save to catch the latest revision to your project, incremental save allows you to manually save a new file, incrementing the name of your project in numeric integers. CINEMA 4D does the same. And with a little configuration, you can make it act exactly the same as in After Effects.

Welcome back, my budding hackers! In previous tutorials, we've looked at some of the basic commands and concepts for using Linux. Along the way, I realized that I've failed to provide you with some basic background material on the stdin, stdout, and stderror.

There's only one thing keeping hackers, thieves, law enforcement agencies, and maybe even the people you thought you could trust from breaking into your iPhone should they ever get possession of the device. Their odds of bypassing that thing are pretty good, but there's an easy way to make it an almost impossible feat.

If you're ever faced with a situation of handing over your iPhone to law enforcement (or getting it taken forcibly), whether by the police, feds, or court system, there are things you can do to prevent them from getting access to all that potentially self-incriminating data. And it takes less than a second.

There's always an iPhone in our list of top phones for privacy and security, due in large part to advanced security measures like Face ID, consistent iOS updates, and easy ways to prevent unwanted access and excessive data sharing. However, some of those options actually do the opposite and hinder security. It all depends on how you use your iPhone, but you should at least know everything available.

A rainbow table can be thought of like a dictionary, except instead of words and their definitions, it holds combinations of characters on one side and their hashed form on the other. What is a hash and why would you want to know what random combinations of characters are hashed into?

Welcome back, my hacker apprentices! Last week, I started off my password cracking series with an introduction on the principles and technologies involved in the art of cracking passwords. In past guides, I showed some specific tools and techniques for cracking Windows, online, Wi-Fi, Linux, and even SNMP passwords. This series is intended to help you hone your skills in each of these areas and expand into some, as yet, untouched areas.

This how-to video is about how to use command prompt to view the blocked websites at school. This step by step instruction will help one to open the blocked websites at school.

Working from home is going to be a reality for more people than ever. With Twitter CEO Jack Dorsey announcing that his employees will be working remotely for an extended period of time (and even permanently, in some cases), the workforce is rapidly changing. More companies are certain to follow suit.

If you've received a spam message in Signal Private Messenger, you know that anyone can contact you as long as they have your linked phone number. But when it comes to the people you're actually trying to have a private conversation with, how do you know it's really them?

With over 10,000 possible combinations, a four-digit passcode may seem secure, but it's fairly easy for someone to crack your code—no matter how clever you think it is. Luckily, there are many other options for securing your iPhone's lock screen—especially if your running iOS 9.

Welcome back, rookie hackers! We recently began an exploration of ways to hack using the Bluetooth protocol. As you know, Bluetooth is a protocol that connects near field devices such as headsets, speakers, and keyboards. Its minimum range is a 10-meter radius (~33 feet) and maximum is at 100 meters (~328 feet).

If running out of battery while out and about weren't bad enough, the experience is a lot more painful if your iPhone has a semi-untethered jailbreak. With that kind of jailbreak, when the iPhone dies, all of the mods will be disabled after the device powers back up. Fortunately, instead of restoring your jailbreak and tweaks manually after recovering from a critically low battery, you can avoid it altogether.

If you're interested in nabbing superhero memory strength, the secret behind training your brain is not necessarily what you might expect. Your standard G-rated brain strengthening exercises range from crossword puzzles to Sudoku to calculating fairly simple math problems to improve short term memory, but the real clincher used by some of the pros is essentially... porn. Yep, you read right.

For lack of a better word, a missing iPhone sucks. Not only do you lose a physical device that cost you a small fortune, but there's also the probability you'll never see your precious data again. Hackers and thieves might, just not you. To keep this from ever happening, there are preventative measures you should take, and the sooner you do them the better.

It's often the smallest details that determine your overall experience with a smartphone. Unlocking your device with a PIN is an example — and iPhones have had a leg up over Android thanks to their automatic unlocking. Thankfully, this era has finally come to an end with the arrival of the Galaxy S9.

Google's Gboard is by far the most popular keyboard available right now. Gboard lets you search almost anything—from regular Google searches, to emojis, and even GIFs—just by using your keyboard. The app even lets you share search results, saving you a great deal of time, which would've otherwise been spent juggling between apps and programs.

Your iPhone just went missing, and now you're panicking. You need it for work, to get around, to contact your friends and family, and pretty much everything else in your life. So, what are the chances you might get it back? The odds may be stacked against you unless it's just under a couch cushion, but you can improve your chances of recovering your iPhone by taking certain steps.

Samsung's new line of Galaxy S20 flagships have a water resistance rating of IP68. This means you don't have to worry as much about getting the phones wet, but there's a limit to that.

The top five apps of the 2010s were all social media apps of some kind, and the fact that's not surprising to you says a lot. We may use them for other reasons here and there, but our phones are social media machines at their cores. The thing is, some make better machines than others.