If you've already gotten your hands on Sony's Internet TV Blu-ray Disc Player, powered by Google TV, then you know how powerful this thing is. But if you're thinking of getting one soon, this video series will help you learn what you'll be getting yourself into.
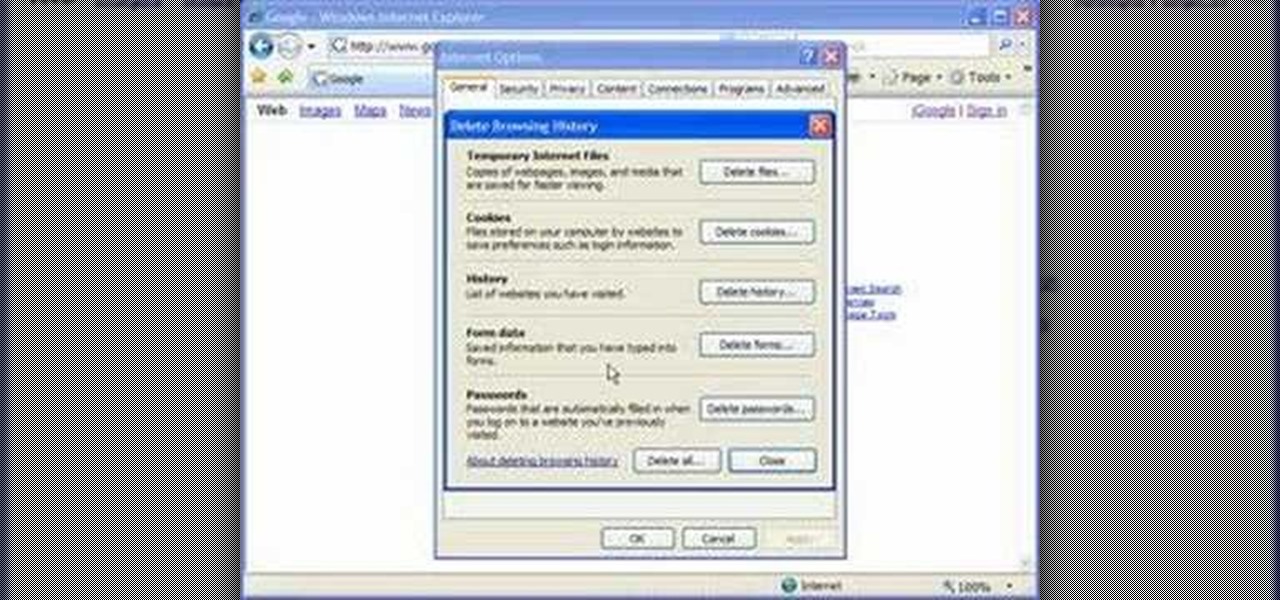
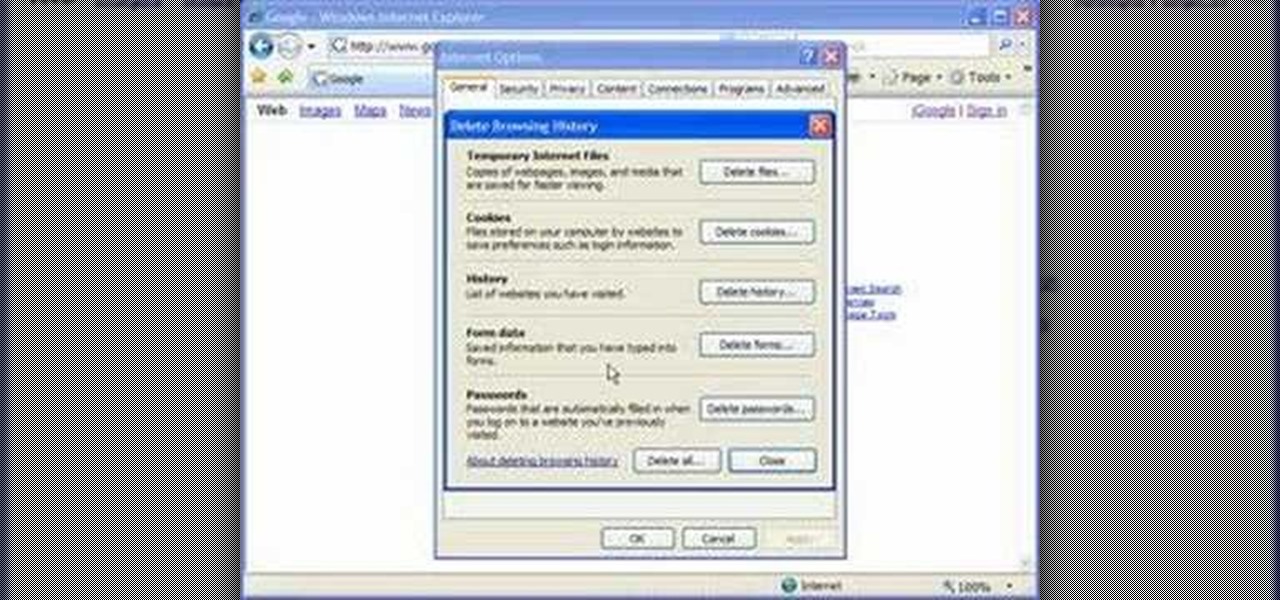
Cookies serve their purpose in Internet Explorer 7. They let the browser know which sites you have visited so you don't have to get security prompts every time you back to them. However, they can also slow down your browser, which can be frustrating. This video will show you how to delete cookies in Internet Explorer and browse faster.

Just because the internet renders you virtually anonymous does not mean social customs should be ignored. Just like in the outside world, there is etiquette that should be obeyed if you want to be treated as a friend rather than an annoyance online. In this how to video, Proper Ollie teaches you how you can have proper internet etiquette in social networking forums.

Have you maybe been eyeballing some things you'd rather other people didn't know about? Clear your Internet history and leave your anxiety behind.

This is the first of 3 steps that will show you how to juggle three balls. Jim the juggler demonstrates how to get them up and going. Step 1 begins with one ball, so be patient, you need to work your way up! (WMP files and smaller videos are available at the root directory)
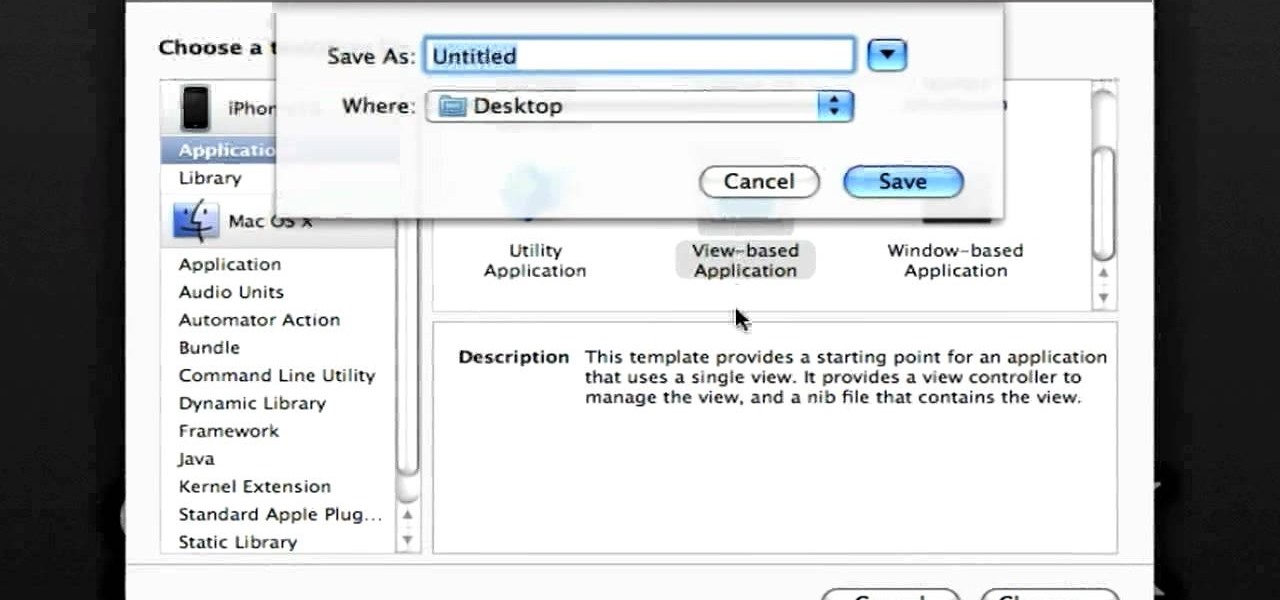
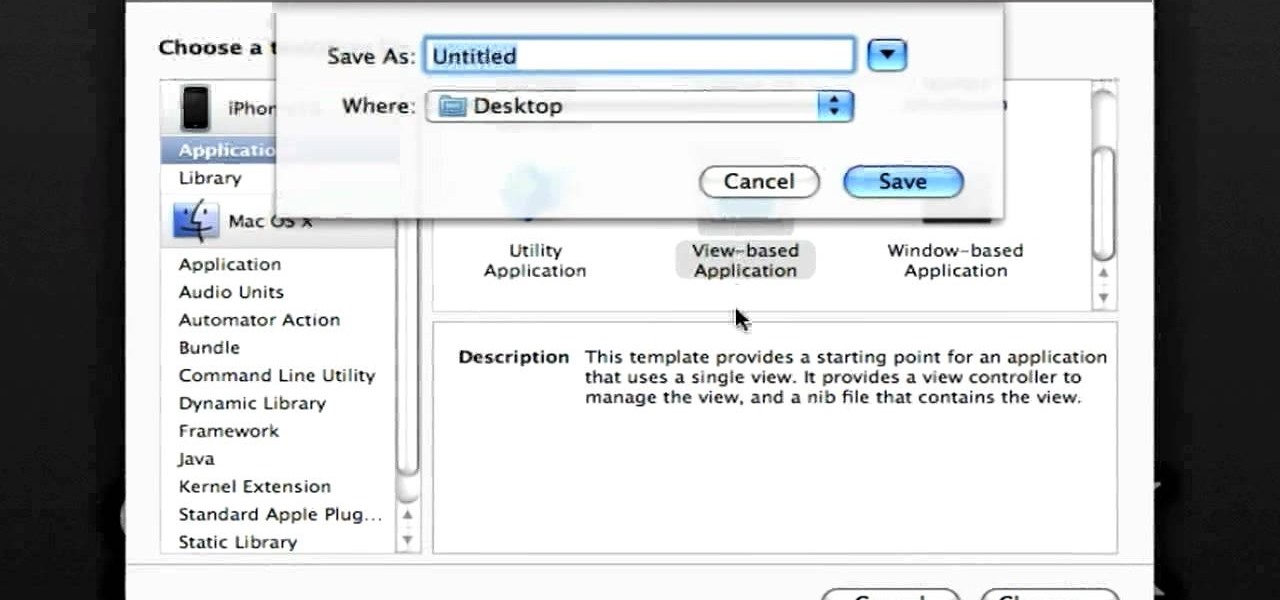
In this clip, you'll learn how to make recourse to the documents folder from within an iOS application. Whether you're new to the Objective-C operating language and Xcode IDE or are a seasoned developer merely looking to pick up a few new tips and tricks, you're certain to be well served by this tutorial. For more information, including a complete overview and detailed, step-by-step instructions, watch this free video Objective-C programming lesson for iPhone & iPod Touch developers.

This is a very basic introductory video that teaches you how to successfully install Quartz Composer on your MAC OSX 10.5 Leopard. Quartz Composer is a node-based graphical data software that uses visual programming language. Built exclusively for use on the MAC OSX, it's a handy software for graphic designers.

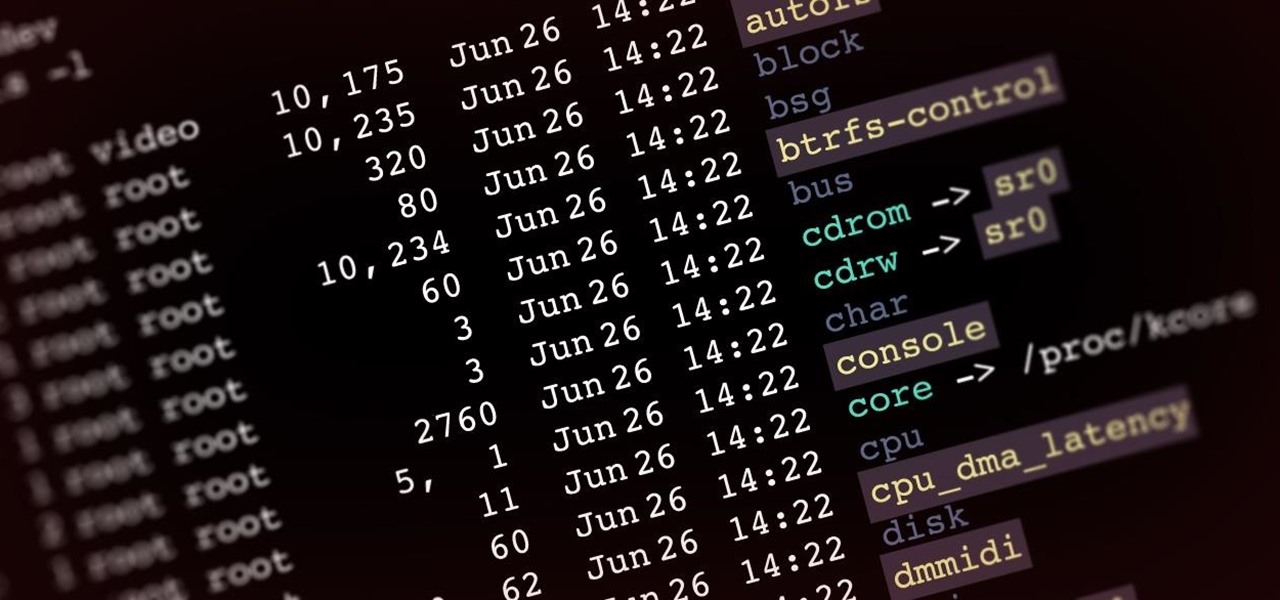
Post-exploitation is often not quite as exciting as popping the initial shell, but it's a crucial phase for gathering data and further privilege escalation. Once a target is compromised, there's a lot of information to find and sift through. Luckily, there are tools available that can make the process easy. One such tool is Postenum.

Without admin privileges, installing additional software, or modifying the Windows 10 firewall, an attacker can alter a router and perform a variety of exploits. It's accomplished by forwarding requests from Kali through a backdoored Windows computer to the router gateway with simple SSH tunnels.

Google, Amazon, and Facebook are always listening. But what's worse? Hackers are listening, too. Windows PCs are particularly vulnerable, but with a few simple commands, a remote attacker can even take over the microphone on someone's Mac computer, streaming audio and listening to private conversations in real time without the victim's knowledge, abusing an overlooked security consideration.

Screenshots taken from a compromised computer can provide hackers with access to private emails, photographs, and information found in sensitive documents. This data can be used by the attackers to build profiles of a target for social engineering attacks and blackmail or even just to release the information out in the wild.

Welcome back, my greenhorn hackers! Throughout this series on Metasploit, and in most of my hacking tutorials here on Null Byte that use Metasploit (there are many; type "metasploit" into the search bar and you will find dozens), I have focused primarily on just two types of modules: exploits and payloads. Remember, Metasploit has six types of modules:

Welcome back, my aspiring hackers! In recent tutorials, I have made reference to the name and location of the Linux devices in the file system, such as sda (first SATA or SCSI drive). Specifically, I have mentioned the way that Linux designates hard drives when making an image of a hard drive for forensic purposes.

In this video from FLPCNERDScom we learn how to clean your browser's cache and cookies on Internet Explorer 7. Click Start, right click on Internet Explorer, and choose Properties. Or go to Internet Explorer, go to Tools, and click Internet Options. Click delete in Browsing History, and then at the bottom click Delete all. Click the box that says Also delete files stored by add-ons. Then click Yes. This may take a few moments depending on your browser's history and cache. Once complete, click...

In this video, we learn how to set your home page as Google on Internet Explorer. First, open up Internet Explorer, then click on tools. Next, go to internet options and then look for where it says homepage. Now, type in the website name of what you want your home page to be. After you do this, click on the apply button on the bottom right of the window, then click on "ok". Once you do this, exit out of Internet Explorer, then go back into it. Your home page should start as what you set it on...

In this tutorial, we learn how to connect your PS3 to the internet. First, go to settings on the game console, then go to network settings. After this, go to internet connection settings and click on "custom". Now, go through all the different steps, then wait while the game finds your internet connection and save all your information. After the connection test is completed, you will be able to connect to the internet to play your games! You will have to have a wireless router to do this, as ...

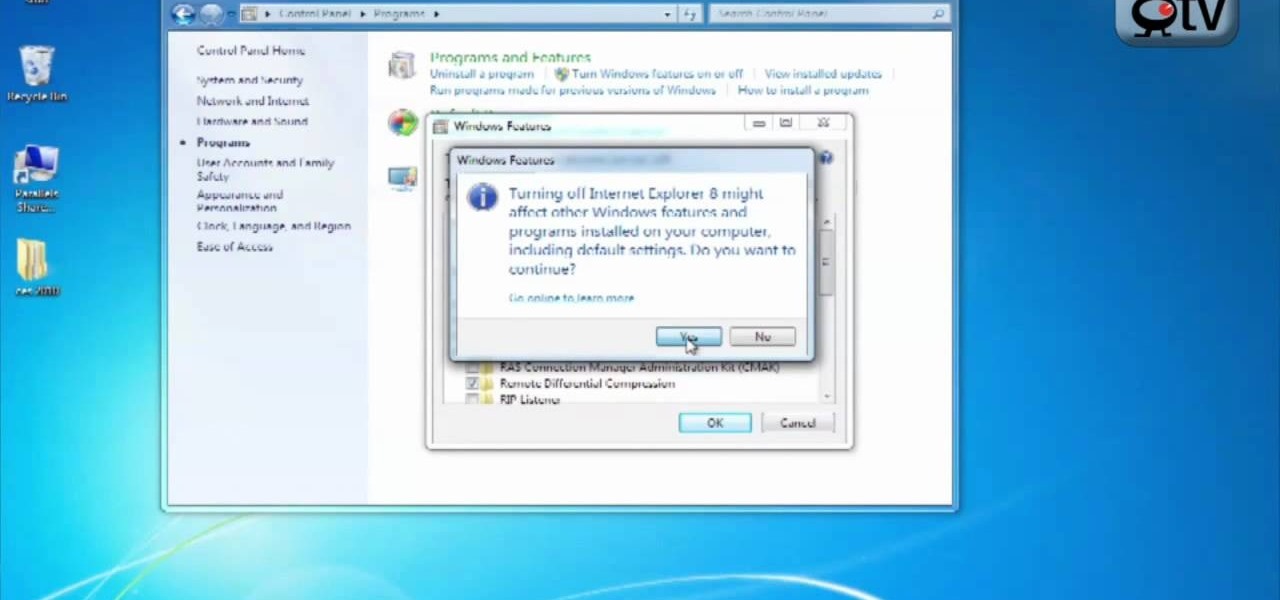
This video tutorial from TigerDirectBlog shows how to easily install or uninstall Internet Explorer in Windows 7 operating system.

In this Video Games video tutorial you will learn how to apply a wireless Internet connection to your Xbox 360. This can be done by what is called the ISC or internet shared connection. For this, plug in your Ethernet cord in to the Xbox and plug in the other end in to your computer. For the internet to work on Xbox, your computer must have Wi-Fi. Then on your computer go to control panel and then to network connections. Right click on ‘wireless network connection’ and select ‘properties’. Th...

Learn how to connect to the internet using your PS3 using an Ethernet cable. What you will need: 1. An internet modem or hub. 2. The details required to connect to the internet (password etc.). 3. A PS3 and an actual internet connection e. g. BT or AOL. Once you have those just follow these steps: 1. Take your Ethernet cable and plug it into the back of the PS3 into the socket labeled Ethernet. 2. Plug the other end into your internet modem. 3. Turn on your ps3 and go to "network settings" un...

The following are the steps to be followed to know the internet speed using CNET. 1. Go to google.com

This video is about understanding and deleting cookies in Internet Explorer. Cookies store bits and pieces of personal information concerning your web browsing habits. In essence, you can be spied on by others through cookies. Cookies should be deleted often - daily, weekly or twice weekly. Go to the Internet toolbar and select "Tools", "Internet Option". In this screen, you will see "Temporary Files". Choose delete cookies. Delete all cookies. Press "ok". All the cookies will be deleted. Rem...

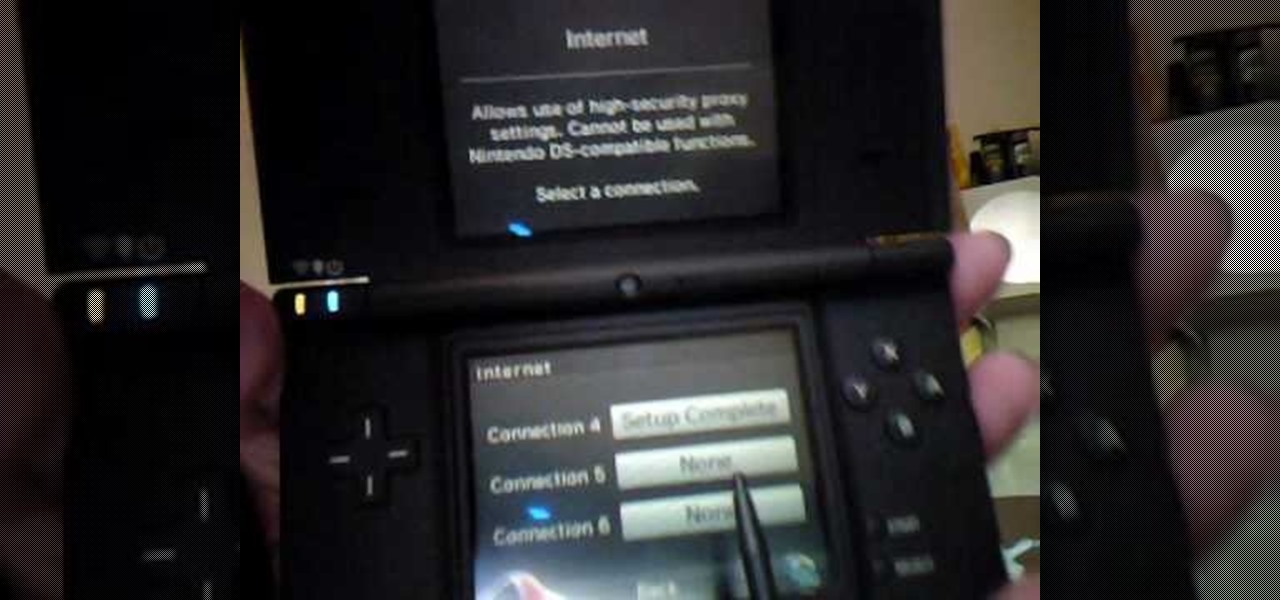
The big perk that comes along with purchasing a Nintendo DSi instead of a regular Nintendo DS is the Internet capability. With Nintendo's new DSi model you can go online and surf the web as well play other users over an Internet connection just like you would on an XBox or Nintendo Wii. Setting up and connecting the Internet on your DSi is quite easy to do and you will want to set this up right away to take advantage of all of the fun features.

In this two-part video tutorial, learn how to get the Internet on your Nintendo DSI. After these videos, you should be able to freely surf the Internet! However, it should be noted: This browser does not support flash or javascript, hence why you will notice certain things are unavailable, such as YouTube videos.

Web browsers such as Windows Internet Explorer 7 have become an important part of the computing experience for business and home users around the world. With the popularity of web browsers for accessing information, running programs, and even accessing corporate resources, the browser has become a target for viruses, malware, and phishing schemes that present real dangers to Internet users. Microsoft Internet Explorer 7 has several new features that make using the web easier and safer than ev...

Looking for an easy way to meter of your Internet bandwidth usage? This free video tutorial from the folks at CNET TV has got you covered. It details two freeware applications — one for Microsoft Windows, one for Mac OS X — that will help you keep track of your bandwidth usage. For the specifics, and to get started monitoring your own Internet usage, watch this helpful how-to.

Freelance web developer and Internet marketer David Frosdick offers some tips and tricks in this video tutorial on how to secure your Gmail account.

The internet has created amazing new standards for how closely information can be followed. If you want a portable analog unit that will monitor one important piece of online info continuously and have some DIY electrical knowhow, watch this video. It will show you how to use an Arduino Ethernet Shield to make an internet meter to monitor email, stocks, and other online info on a simple analog display. You will need to know some PHP to make this work.

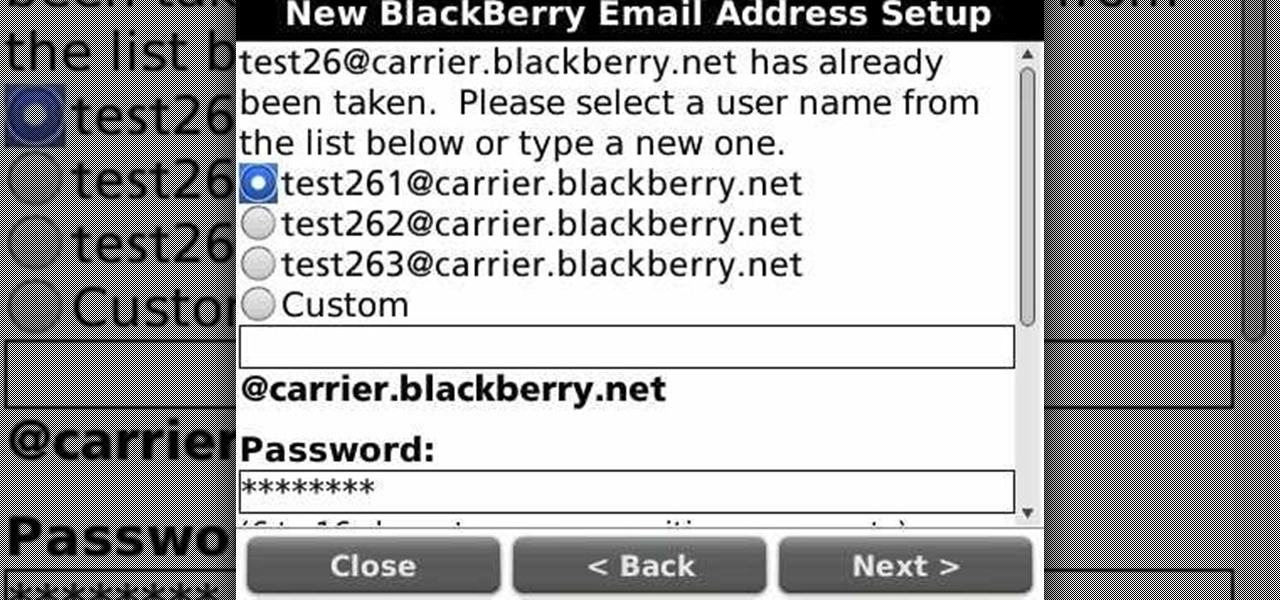
Learn how to create a new BlackBerry Internet service email account on a BlackBerry device running version 5 of the BlackBerry OS. This clip will show you how it's done. Whether you're the proud owner of a BlackBerry smartphone or are merely considering picking one up, you're sure to be well served by this video guide. For detailed information, including step-by-step instructions, take a look.

The internet has been a massive financial windfall for millions of people around the world, and it can be for you as well! There are a lot of ways to make money on your couch by using the internet, and this video will show you five great ways to do it! These include making websites and forums, advertising, and gambling. If you're hard up for cash, give it a whirl!

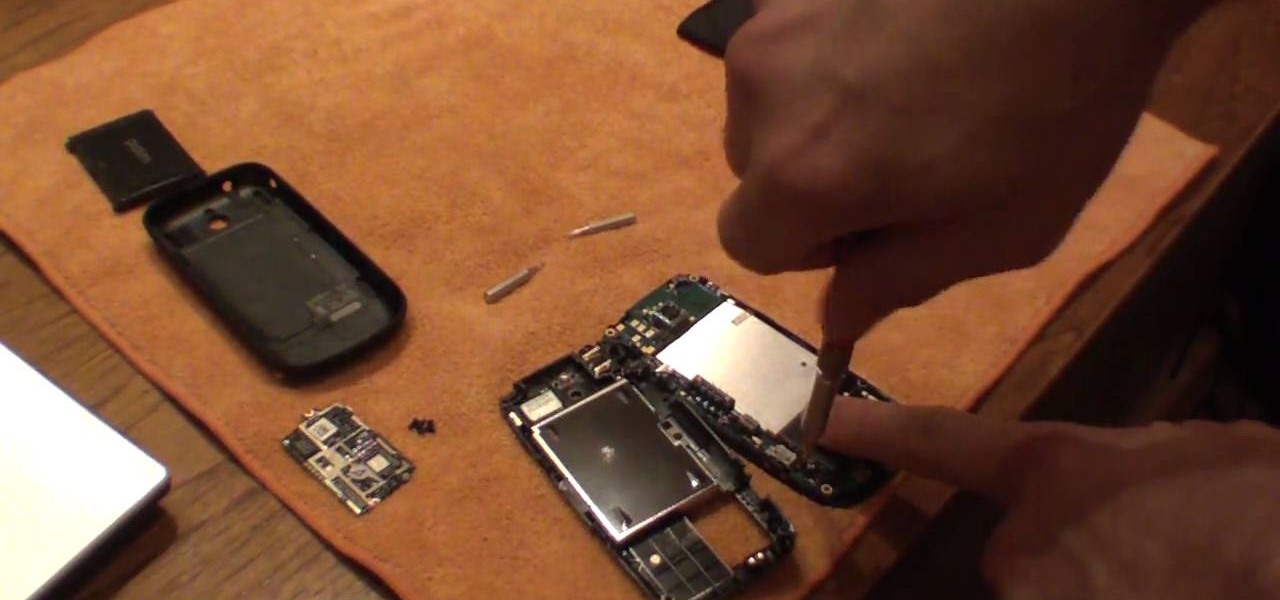
In this video tutorial, you'll learn how to add WiFi Internet connectivity to a normal Sprint Palm Pixi smartphone with a quick and easy radio board (radioboard) swap. For more information, including detailed, step-by-step instructions on how to add WiFi capabilities to your own Palm Pixi phone, watch this hacker's how to.

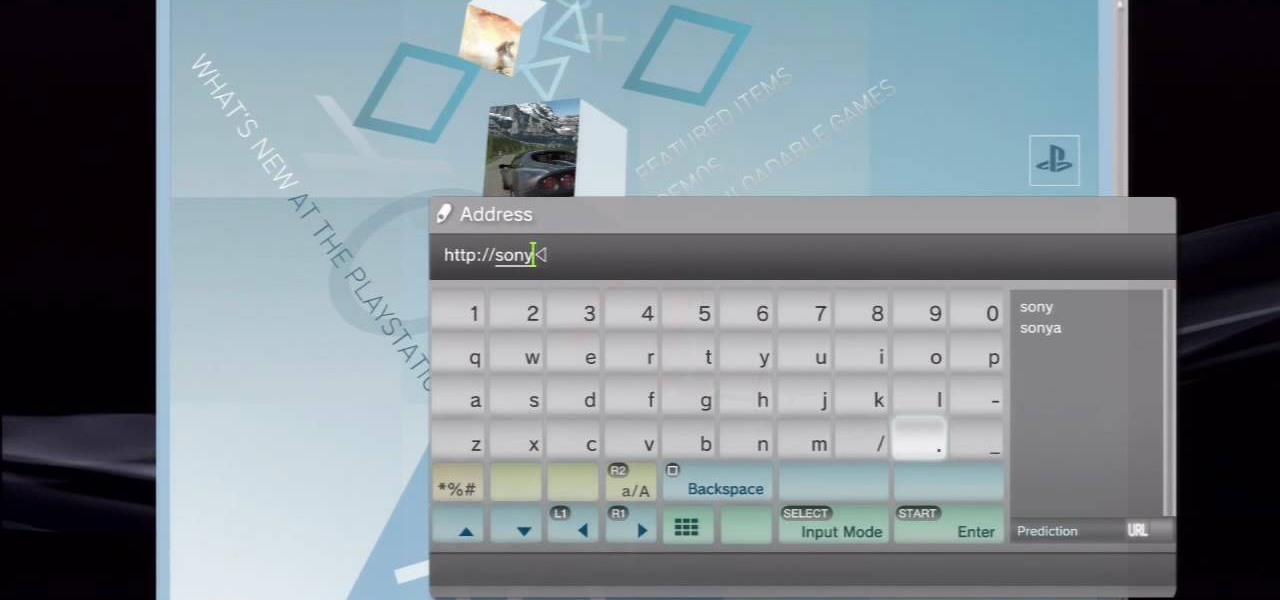
This video tutorial was created by SCEA for Sony PlayStation fans and readers on how to use their PS3. Learn how to surf the web on your PS3. Once you learn the ease of browsing the Internet on your PlayStation 3 with the Internet Browser, you won't be able to stop.

With an inconspicuous Android phone and USB flash drive, an attacker can compromise a Windows 10 computer in less than 15 seconds. Once a root shell has been established, long-term persistence to the backdoor can be configured with just two simple commands — all while bypassing antivirus software and Windows Defender.

After backdooring a MacBook not protected by FileVault or using a fake PDF to gain remote access, an attacker may wish to upgrade their Netcat shell to something more fully featured. While a root shell allows attackers to remotely modify most files on the MacBook, Empire features some useful post-exploitation modules which make hacking Macs very easy.

If you're completely new to Android, you're in for a treat with all of the software tweaks and customization options that your smartphone or tablet offers out of the box. But if you really want to take things to the next level, the ability to mod your device expands exponentially when you're rooted.

With the release of the Samsung Galaxy S5 right around the corner, the first full system dump has been released by Sammobile. As the inevitable ports of functioning apps slowly begin to leak, today we've got a non-app aspect of the system and the one that tends to leak first—ringtones.

If you hit the FN + F10 keys on your Nokia Booklet 3G, you'll see the available internet connections methods for your netbook including Bluetooth, wifi, and 3G.

A fast Internet connection means you can send and download files quickly. Modems, depending on if they are broadband or dialup, may have different speeds and run fast or slow. There are many free programs you can use to test out your PC computer's Internet connection!

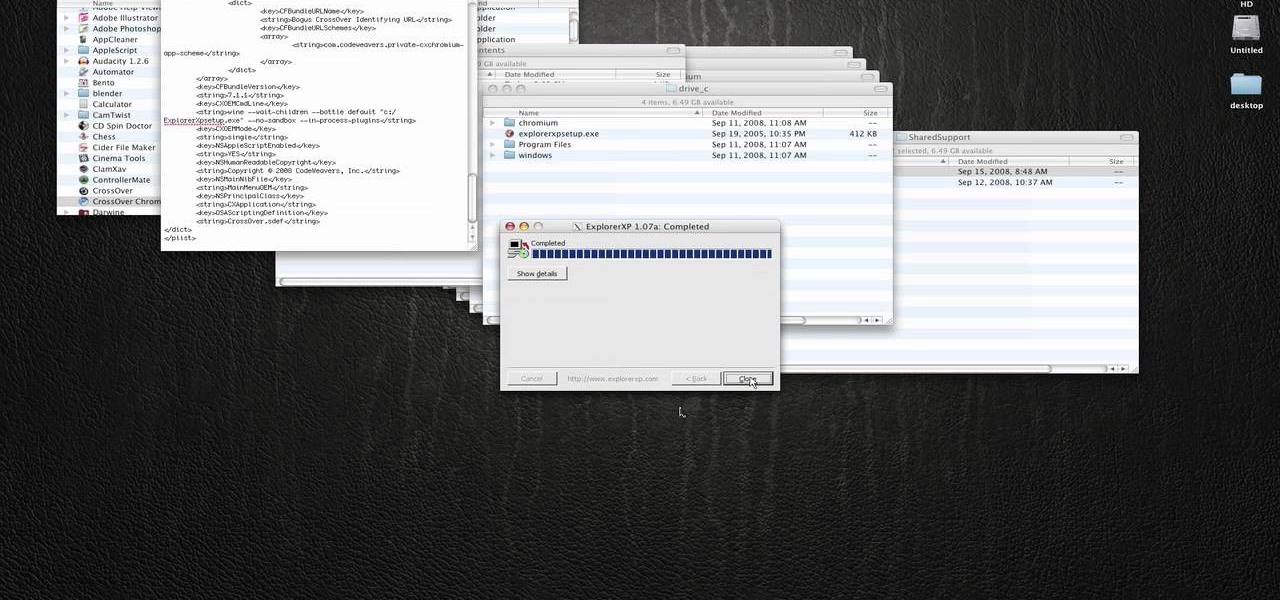
In this how to video, you will learn how to run Windows programs for free on a Mac using Crossover Chromium. You will need to download Crossover and install it by downloading it and dragging it into the applications folder. You will also need Explorer XP. Go to the applications folder and show the package content of Crossover. Go to shared support as you will need a file here later. Open Chromium, go to support, Chromium, and Drive, and then drop Explorer XP into the folder. Open the info fil...

Gaming consoles are capable of a lot more than power ups these days. Even a small console like a PSP can operate like a small computer, enabling you to browse the internet through WiFi connections. This video will give step-by-step instructions on how to get internet on your PSP.