When you use a scanner to look for error codes on a car, many can show up at once and confuse you as to the nature of the problem. Often, all of the codes are responses to the same problem. Watch this video for tips on interpreting multiple error codes.
This is the 12th puzzle, entitled "Titans of Industry", in Assassin's Creed 2. Code wheel puzzle 1: The key here is in the “4=1” on the blueprint at the left of the screen. Line up the red 4 over the gray 1 and input the following code: 917240. Image 1: This one’s the opposite of the light-bulb “puzzle” from before – just move the dollar sign over the bulbs to extinguish them. Image 2: Highlight the glowing ball at the center of the image. Code wheel puzzle 2: Your hints here are the “2” on t...

This is an instructional video to learn the line dance for Alan Jackson's new single, "Good Time." Alan Jackson is a star country singer and known for making great music to line dance to. He's a Grammy winning artist that inspires many to learn line dancing so that they may participate at his huge stadium concerts.

You've seen code blues called on TV, but how about in real life? If you are becoming a nurse it is important to know what goes on as part of a code blue situation. This nursing how-to video presents a mock code blue presentation with faculty. Follow along and learn what is involved in caring for a patient that has gone into code blue.

To program your DirecTV remote for your XBox you will need to find your programming codes. Press menu on your remote and scroll down to parental fav's and setups, then system setup, select remote control, and program remote. You can use either AV1 or AV2 both should work. Then you will choose DVD, and then select the brand for your 360 and your program codes will come up. Put your TV in AVI mode and press your menu and select button at the same time. The lights at the top of the remote should...

Foundstone Hacme Shipping is a web-based shipping application developed by Foundstone to demonstrate common web application hacking techniques such as SQL Injection, Cross Site Scripting and Escalation of Privileges as well as Authentication and Authorization flaws and how they are manifested in the code. Written in ColdFusion MX 7 using the Model-Glue framework and a MySQL database, the application emulates the on-line services provided by major shipping companies. This video will get you st...

Oh god, don't you break my heart, my achy breaky heart, I just can't take it anymore. Oh well, if you still need more achy breaky, check out this video and learn the line dance that years ago caused a nation to pause and reflect.

For a hacker, there are a lot of advantages to creating a fake network. One advantage forces nearby devices to use their real MAC address if you happen upon a network that's stored in their preferred network list.

No operating system is stricken with as many vulnerabilities as Windows, and it's often a race to release the latest patches to fix things. From an attacker's point of view, knowing which patches are present on a Windows machine can make or break successful exploitation. Today, we will be covering three methods of patch enumeration, using Metasploit, WMIC, and Windows Exploit Suggester.

QR codes are everywhere, from product packaging to airline boarding passes, making the scanners that read them a juicy target for hackers. Thanks to flaws in many of these proprietary scanning devices, it's possible to exploit common vulnerabilities using exploits packed into custom QR codes.

EternalBlue was a devastating exploit that targeted Microsoft's implementation of the SMB protocol. Metasploit contains a useful module that will automatically exploit a target, as long as it's vulnerable. But what if we wanted to exploit this vulnerability without Metasploit holding our hand? It can be done using a Python file to exploit EternalBlue manually.

Kali Linux, by default, probably doesn't have everything you need to get you through day-to-day penetration testing with ease. With a few tips, tricks, and applications, we can quickly get started using Kali like a professional white hat.

Have you ever seen pictures or videos of balloons being let go into the sky and randomly floating away in all directions? It's something you often see in classic posters or movies. Well, guess what? Now you'll be able to do that without having to buy hundreds of balloons, all you'll need is ARKit!

Using Hydra, Ncrack, and other brute-forcing tools to crack passwords for the first time can be frustrating and confusing. To ease into the process, let's discuss automating and optimizing brute-force attacks for potentially vulnerable services such as SMTP, SSH, IMAP, and FTP discovered by Nmap, a popular network scanning utility.

As we aim for a wireless world, technology's reliance on cloud computing services is becoming more apparent every day. As 5G begins rolling out later this year and network communications become even faster and more reliable, so grows our dependency on the services offered in the cloud.

As part of its ARCore push this week, Google has promoted Just a Line from one-time AR experiment to a full-fledged app.

Cross-compilation allows you to develop for one platform (like Kali) and compile to run on a different platform (such as Windows). For developers, it means that they can work on their platform of choice and compile their code for their target platform. For hackers, it means we can compile exploit code for Windows from Kali.

While attempting to hack a web app, there may come a point where the attacker may have to escape the default directory in order to access unauthorized files. This is known as a directory traversal attack. Much as the name implies, this attack involved traversing the servers directories. But in order to move to an unauthorized directory, we need to know where those directories are. Today we'll be building a tool to brute force these directory locations based on HTTP response codes. Before we g...

As many of you know, processor's clock frequency improvement got stuck in about 2003, causing the origin of multicore CPU (and other technologies). In this article I'll introduce you on how to run code simultaneously in various processors (I suppose that all of you have a multicore CPU). When you write code without any parallel directive, it only executes in one CPU at the same time (see it below). OpenMP make simple to work with various cores (if not with all of them) , without so much heada...

Ask around anywhere that Android users gather online, and you'll find that SwiftKey is almost unilaterally the most highly-recommended keyboard for our favorite mobile operating system. It's no surprise either—SwiftKey's combination of insanely accurate word predictions and rapid-fire gesture typing comprise a hard combination to beat.

Veering from common practice, XDA commenter, "the_commenter", discovered a changelog for the upcoming version of Android 4.4.3 tucked away on Google's servers.

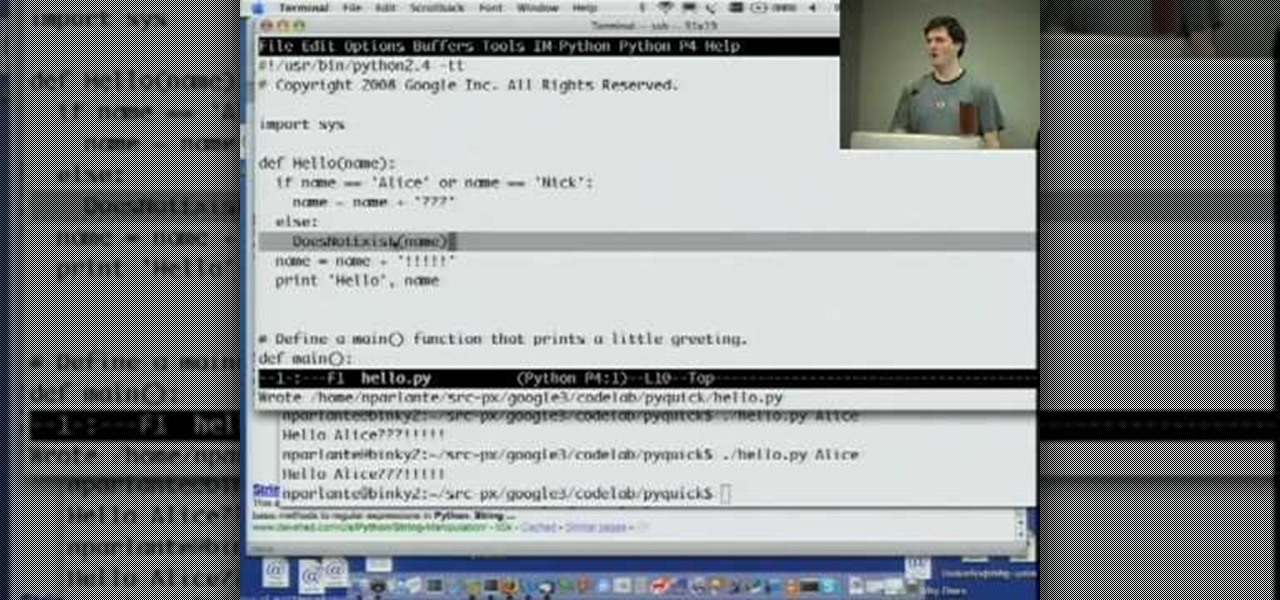
Welcome to Google's Python Class – a seven-segment, two-part free virtual class for people with a little bit of programming experience who want to learn Python. The class includes written materials, lecture videos, and lots of code exercises to practice Python coding. The first exercises work on basic Python concepts like strings and lists, building up to the later exercises which are full programs dealing with text files, processes, and http connections. The class is geared for people who ha...

Interested in learning how to code and create a modern website from scratch? Let this eight-part video tutorial series be your guide. It's easy and this series presents a complete, step-by-step overview of the process. For more information, including detailed instructions, and to get started creating and coding your own website groups, take a look.

In order to build a Spark Carousel in Adobe, you can get the source code first, which is available here.

This tutorial will show you how to hide your MySpace comments using the custom MySpace profiles website. All you have to do is visit the website mentioned in the video, and copy a simple code in the codes section. The code that you will be looking for in the list is the 'Hide MySpace comments' code. The code is then pasted in to your MySpace profile under the 'About Me' section. If you follow the directions entirely in this tutorial, your MySpace profile comments will be disabled until you re...

In this video tutorial, learn how to unlock (or jailbreak) your Blackberry, with these step-by-step instructions. This video also shows you how to get a IMEI Unlock Code from "Unlock To Talk", however, this code costs money. You can access a code here.

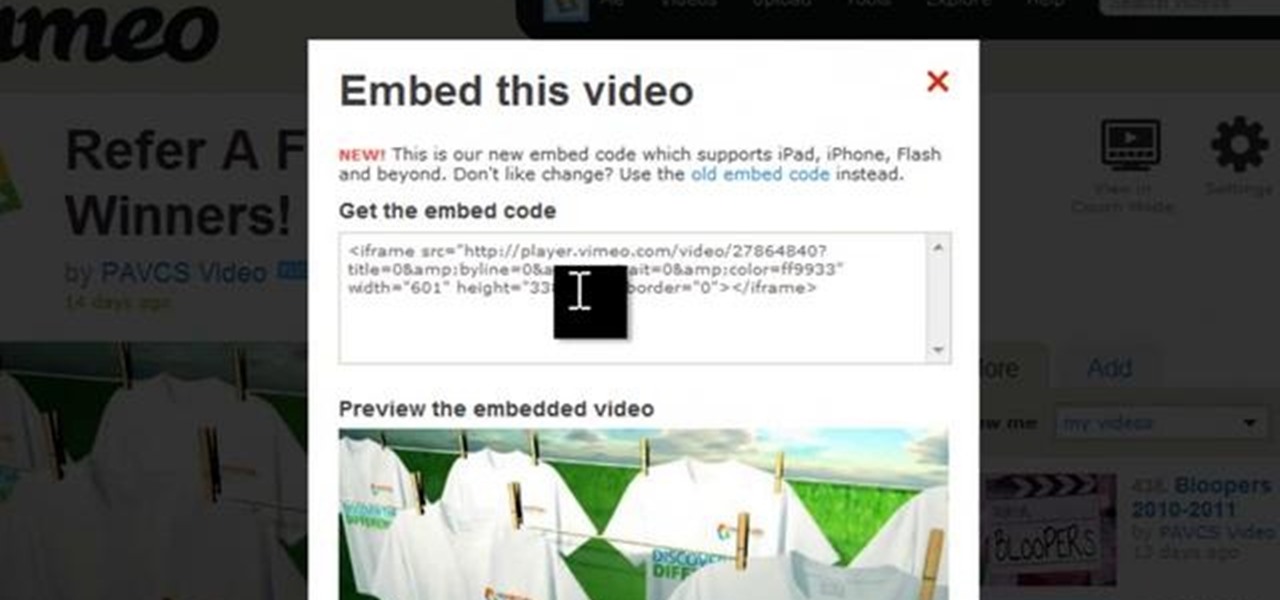
If you want to embed an iFrame into a Blackboard 9.1 page, you'll need to grab the code from whatever source you want (YouTube, Vimeo, Google Docs, etc.) and use the Build Content option in Blackboard. Select "Item" under the "Create" menu and turn off the Text Editor so that you can properly paste the code in. Take a look at this tutorial to see all the steps in action.

QR codes allow you to quickly and easily store and retrieve data within a single image. Much like barcodes at grocery stores, QR codes are images that can be scanned to discover data, such as an online website URL. Additionally, they can also be created by inputting text data into a QR code generator. Try scanning some of the QR codes in this video with an app on your phone or tablet to see how they work!

If the speedometer on your car isn't working and the check engine light is on, get your scanner out and look for code P0500. If you get that code, watch this video to learn a quick easy fix for the problem.

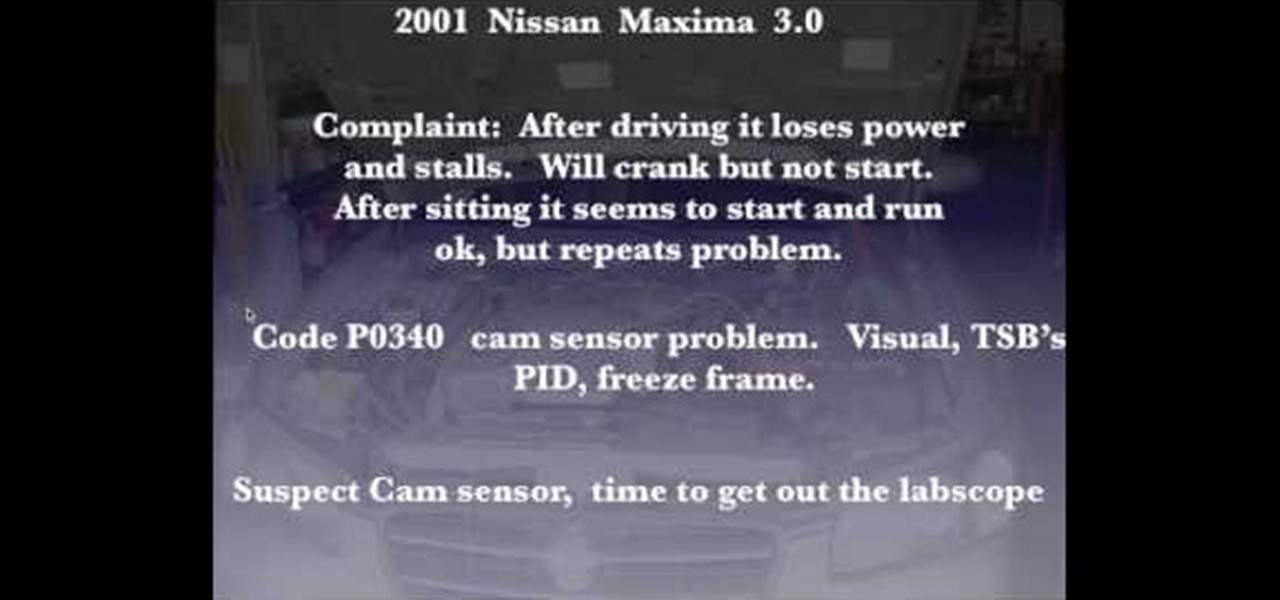
Just because your car shows an error code doesn't mean you should pull any parts. This video will show you how to confirm error code P 0340 on a Nissan (Bad Cam Sensor) by using a lab scope to check the cam sensor.

Add a chat program to your website and allow the logged in users to talk to each other! You can write this program using Adobe Flash CS3, PHP and MySQL. This tutorial shows you how to write your own Flash chat program incorporating all three systems.

Despite being on the Xbox Live Arcade and PlayStation Network, Scott Pilgrim vs. the World: The Game is actually a pretty hard video game. But, things get a whole lot easier with this cool play modes available with a few secret cheat codes. This video tells you those cheat codes to enable zombie mode, boss rush mode, and two others in the XBLA game.

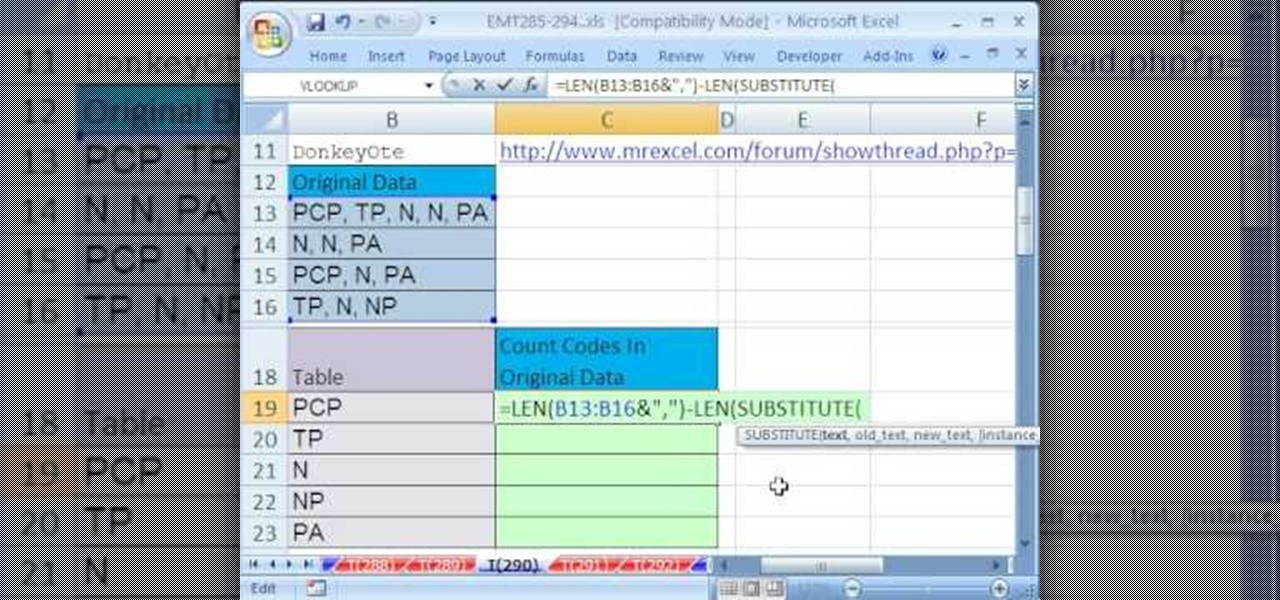
New to Microsoft Excel? Looking for a tip? How about a tip so mind-blowingly useful as to qualify as a magic trick? You're in luck. In this MS Excel tutorial from ExcelIsFun, the 290th installment in their series of digital spreadsheet magic tricks, you'll learn how to count codes from a column of text strings that have multiple codes.

This tutorial series shows you how to put up an Adobe Air Flex 3 Encryption System. One of the weak points of Adobe AIR and Flex is there is no encryption system built in, making your data and applications vulnerable. But that's ok, because this tutorial will show you how to remedy the problem by adding an AES encryption system.

This video describes Resistor Color Codes and how to read them. It relates Resistor Color Codes to scientific numbers and engineering notation.

Keeping secrets out of the wrong hands warrants desperate measures—or maybe just sensical. If you have a secret, the best way to protect it is with a code—and the best way to transfer that secret message is via an electronic telegraph system. This video will show you how to make your own homemade electronic telegraph machine, so that you can send those encrypted Morse code messages to your friends without fear of prosecution.

Check out this instructional dance video and learn how to line dance to the Allen Jackson song "God Bless Texas." Most clubs all do different line dances for this song. This tutorial provides instruction mainly for the North Carolina area, specifically the Cadillac Ranch club. This video also explains how to add your own flavor to a line dance. Practice your line dancing skills and just have fun with it.

The line dance is a dance with repeated sequence of steps in which a group of people dance in one or more lines, all facing the same direction, and executing the steps at the same time. Line dancing's popularity grew out of the 1970's, when the country-western dance continued to explore and develop this form of dancing.

The line dance is a dance with repeated sequence of steps in which a group of people dance in one or more lines, all facing the same direction, and executing the steps at the same time. Line dancing's popularity grew out of the 1970's, when the country-western dance continued to explore and develop this form of dancing.

The line dance is a dance with repeated sequence of steps in which a group of people dance in one or more lines, all facing the same direction, and executing the steps at the same time. Line dancing's popularity grew out of the 1970's, when the country-western dance continued to explore and develop this form of dancing.