While becoming the next Mark Zuckerberg may be out of reach for someone just getting introduced to code, the skill has never been more valuable. Just understanding basic programming language is a great thing to put on your resume, and if you know how to code, you’re golden. Software developers and programmers have been the most resistant to the recession, as jobs in the tech industry continue to grow.

You've probably heard about Rep. Greg Walden (R-WA) tweeting in Morse code back in December. .-- .. .-.. .-.. / -.-. .... .- .. .-. / -.-. --- -- -- / .- -. -.. / - . -.-. .... / ... ..- -... / --... ...-- ... / .-- --... . --.- ..

Your first, very basic web crawler. Hello again. Today I will show you how to code a web crawler, and only use up 12 lines of code (excluding whitespaces and comments).

Mike Lively of Northern Kentucky University shows you how to create a light switch in Second Life with scripting. Part 1 demonstrates how to create a prim switch which turns on (brightens) a prim in Second Life. Part 2 goes through the Light Switch code line-by-line and adds a rotor to the light switch. The code is provided for free distribution on Google Code at

This is a simple Adobe Flex Photo Viewer. It uses a number of techniques that are not found in any one place in the literature - data shorting, tile repeater, xml http services, inline mxml actionscripting, click on double functions, use of CDATA Tags, tooltip, glow and fade effects - all done in less than 100 lines of code (once you take out the blank lines). This was created by Mike Lively Director of Instructional Design at Northern Kentucky University for the Over The Rhine project.

This is a little c++ program that I thought would be handy in the future. Although, I apologize in advance for any errors in the code since I haven't had the chance to compile it yet. Anyway, please if you are a script kiddie please do me a favor and at least read this article fully. :)

This is my first ever how-to so I apologize in advance for any grammar mistakes or spelling errors. Introduction

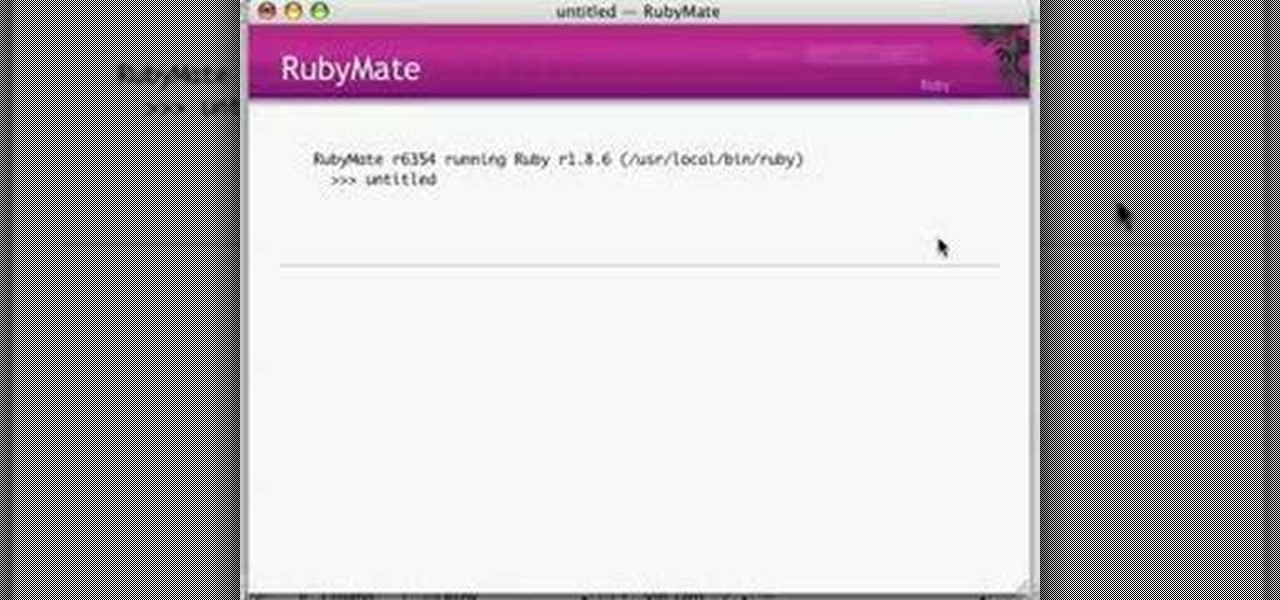
Recently, I've been learning Ruby as a second scripting language. But one topic I never covered with the many lessons online were sockets. So I did some research and came up with a very simple client/server connection that sends a string over the socket.

A stager is a small piece of software that's typically used by malware to hide what's happening in the early stages of infection and to download a larger payload later.

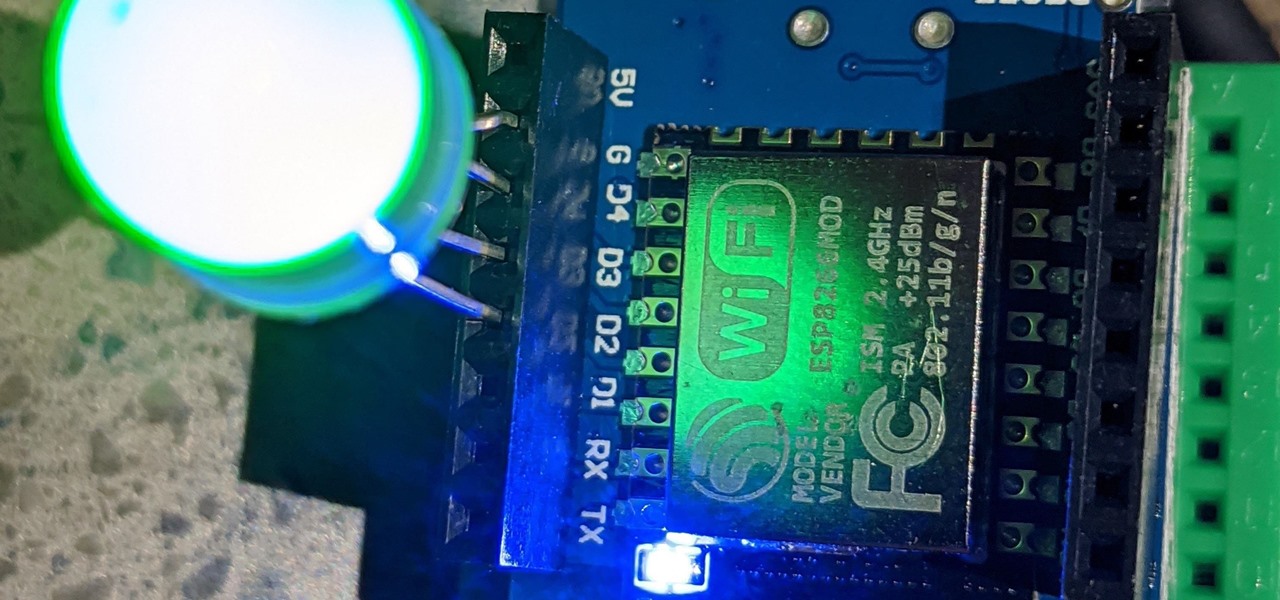
For anyone interested in using cheap, Wi-Fi-connected microcontrollers like the ESP8266, the Arduino programming language can be a barrier to entry. Based on C++, Arduino requires knowledge of more computer science than languages like Python. Fortunately for beginners, setting up MicroPython on an ESP8266 allows anyone to write Python on affordable microcontrollers in a matter of minutes.

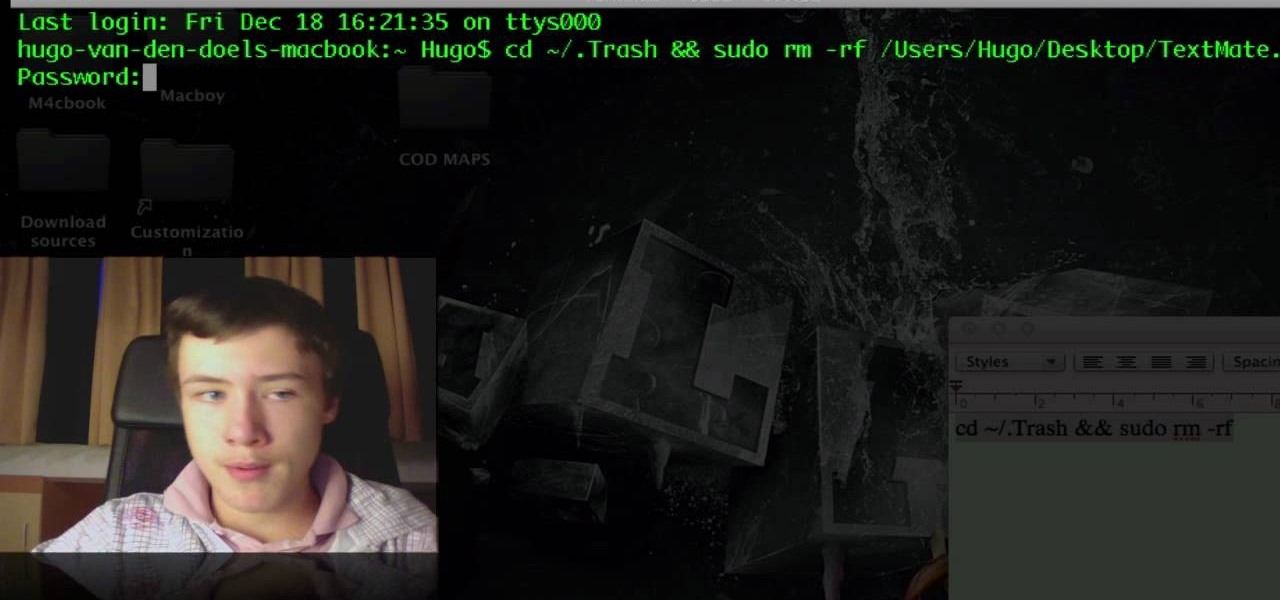
If you have trouble emptying your trash on your Mac computer, you will need to launch the Terminal first, in order to begin troubleshooting the issue. The trash will often fail to accept items, if it believes that a program or object is in use. Move the application that you can't delete onto your desktop. Add a line of code to the terminal. Add the application to the code, by dragging it to the code. It will ask for your code. Enter your password. Press enter. You will need to use a Sudo code...

It's exciting to get that reverse shell or execute a payload, but sometimes these things don't work as expected when there are certain defenses in play. One way to get around that issue is by obfuscating the payload, and encoding it using different techniques will usually bring varying degrees of success. Graffiti can make that happen.

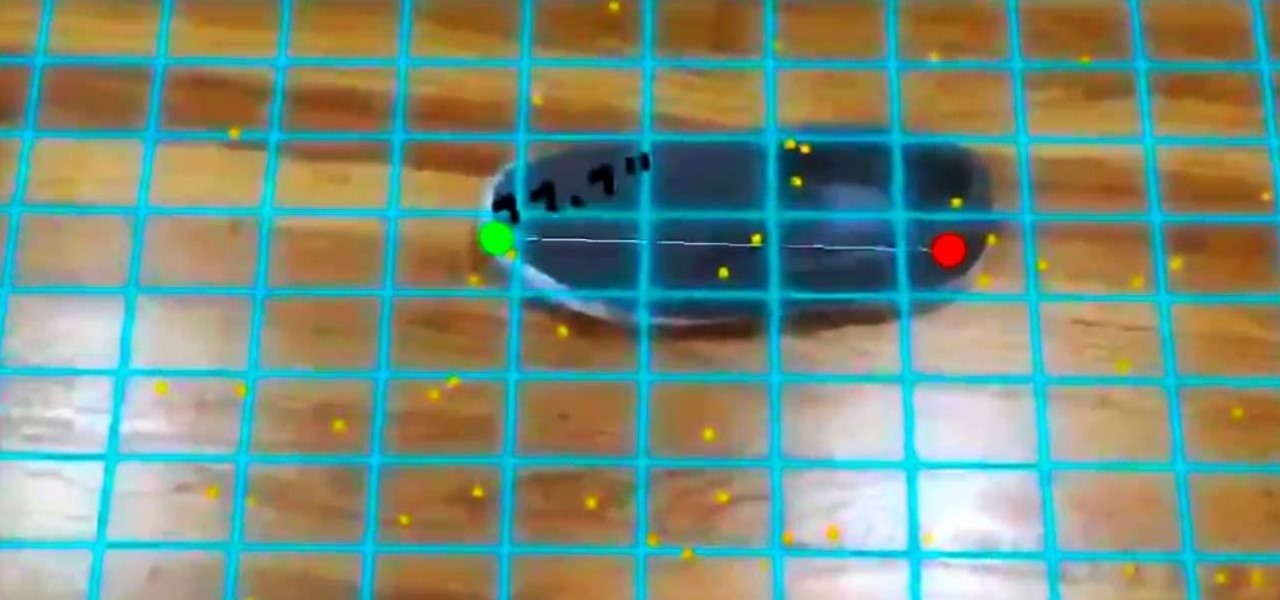
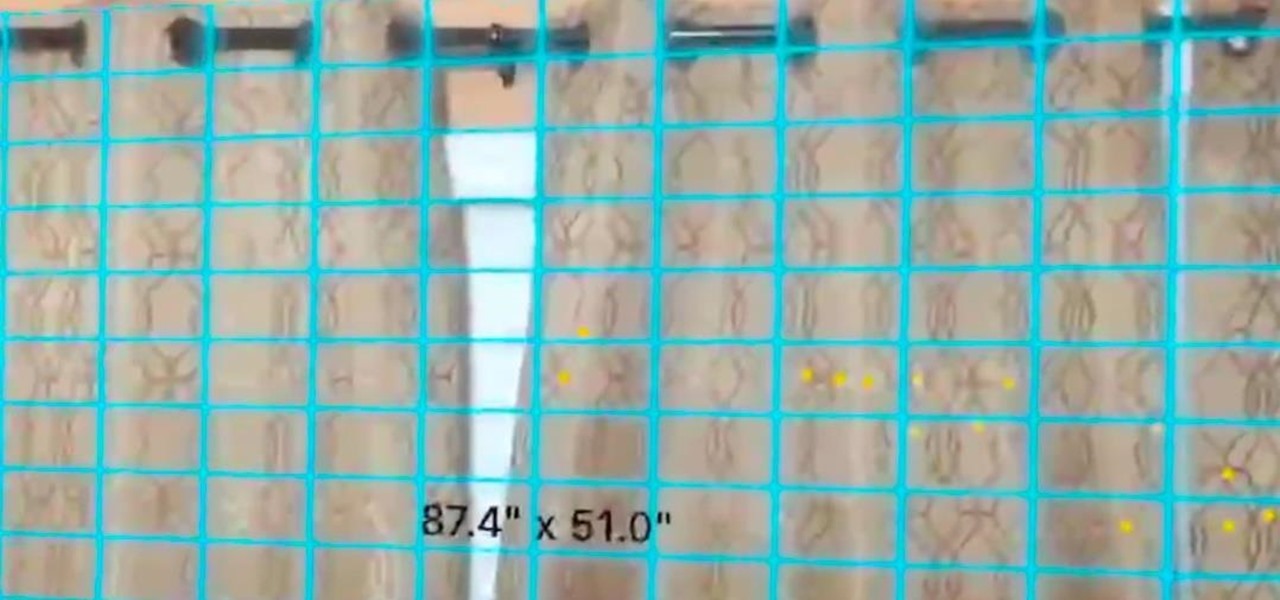
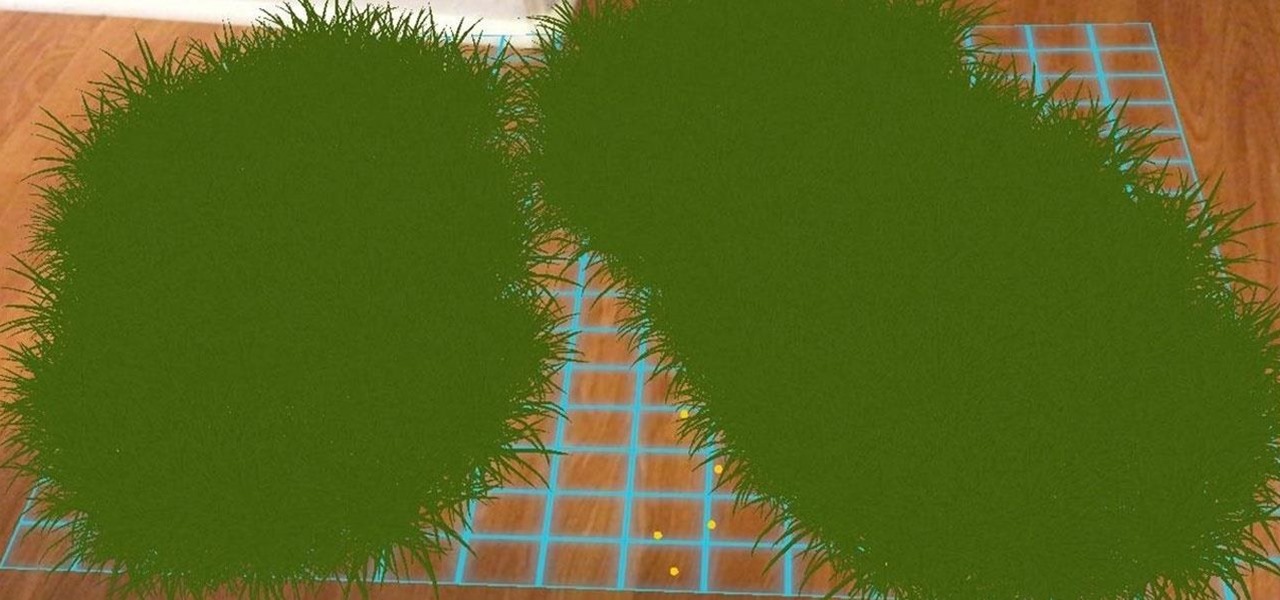
In our last ARKit tutorial, we learned how to measure the sizes of horizontal planes. It was a helpful entryway into the arena of determining spatial relationships with real world spaces versus virtual objects and experiences.

You may have all the tools and people needed for putting up a fence, but something that should not be skipped is coding. Checking the coding and property lines to your place is important for making sure you don't cross into a place that you aren't supposed to be. This can result in bad blood forming and the removal of your hard work. So check out what you'll need to do in order to prevent that, in this tutorial. Enjoy!

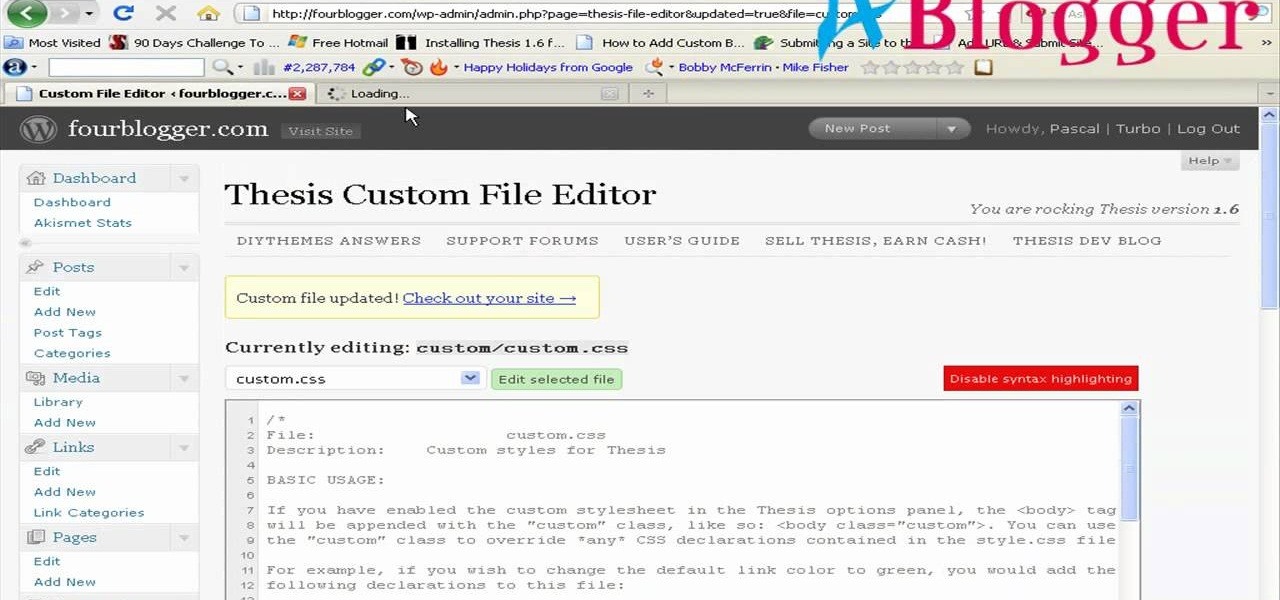
First you need to go to your site and click any post you want and see the simple heading and now you want to change the background. To do this, first you need to go to your word press admin and then click custom file editor in thesis options it will open your code window and here you will have to paste the code which is showing in the video. you will have to paste it in custom.css. After pasting the code you have to click the green save button.

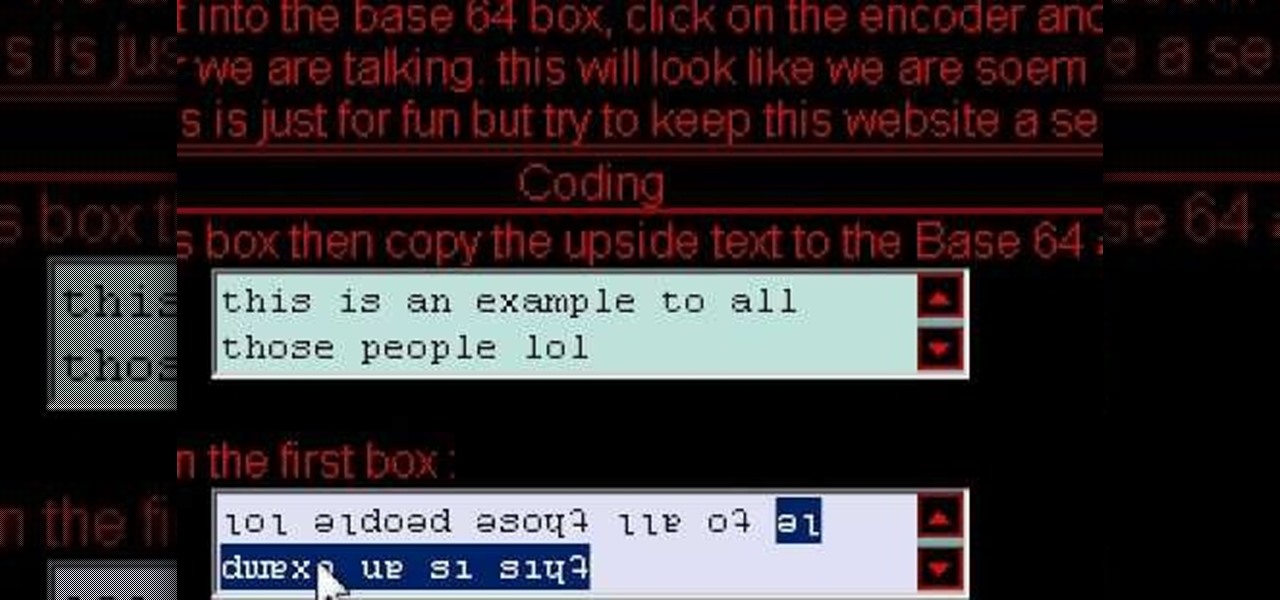
Cool tips and tricks on Facebook give you some extra edge on others. This trick will demonstrate that how to talk to your special loved ones that no one else can understand.

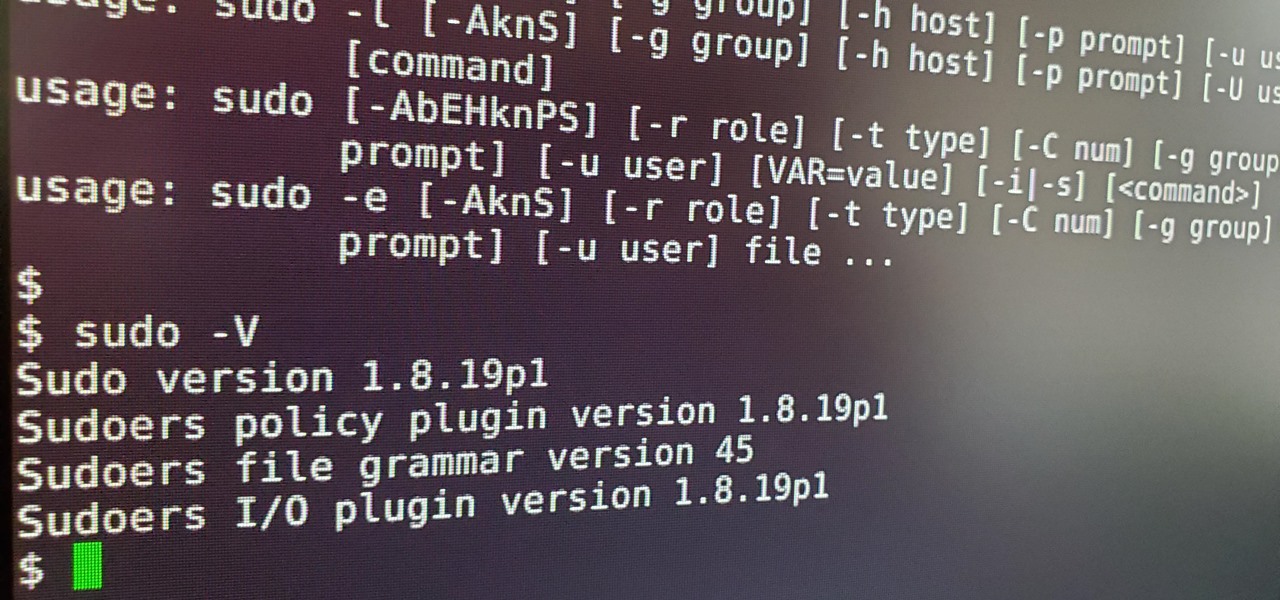
Anyone who has used Linux long enough is familiar with sudo. Short for superuser do (or substitute user do, depending on who you ask), it allows users to run commands as either root or another user on the system. From a hacker's point of view, sudo is often all that stands between them and root access. We'll be exploring an older vulnerability in sudo that allows a user to run commands as root.

UnrealIRCd is an open-source IRC server that has been around since 1999 and is perhaps the most widely used one today. Version 3.2.8.1 was vulnerable to remote code execution due to a backdoor in the software. Today, we will be exploiting the vulnerability with Metasploit, examining the underlying code to understand it, and creating our own version of the exploit in Python.

Before SOAP and REST, there were Remote Procedure Calls. Ruby on Rails ships with native RPC support and this screencast programming tutorial will show you how to build powerful remote API queries with 3 lines of Ruby on Rails code!

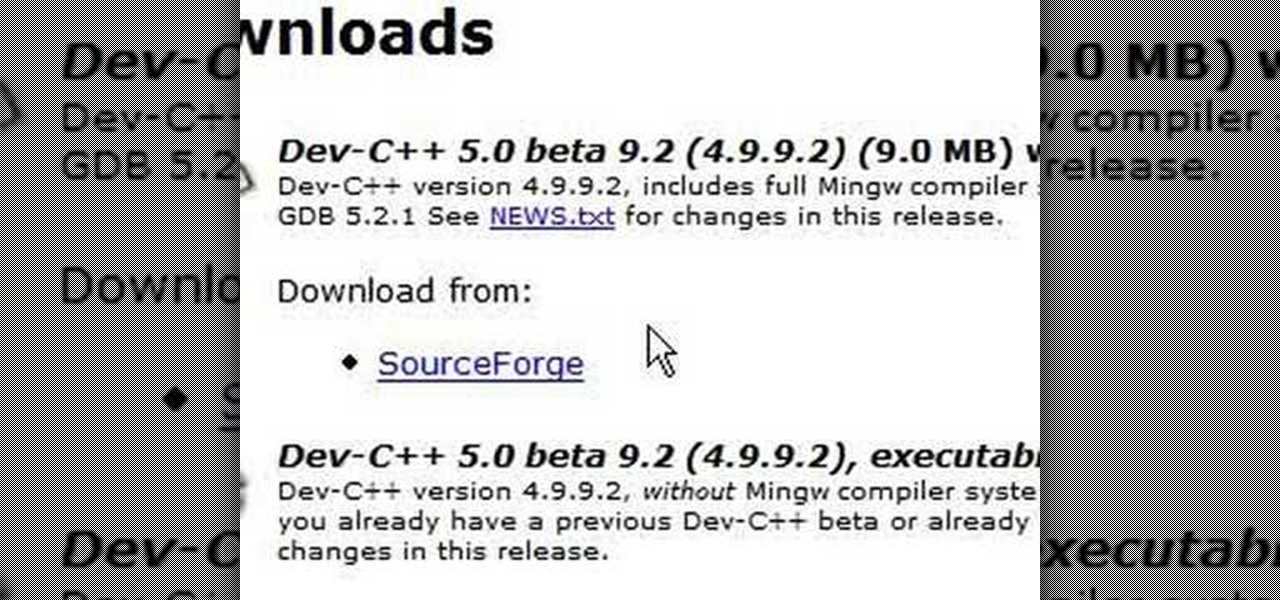
C++ is one the most powerful and fundamental languages commonly used to computer programming. If you've ever wanted to get started using, then please watch this video series. It's 29 parts will teach you everything you need to know about coding in this magnificent language, allowing you to create your own fairly full-featured computer programs. Honestly, if you have any questions about C++ at all, or want to learn it and don't think that you can because you've tried programming before and fai...

Developers creating login systems know better than to store passwords in plain text, usually storing hashes of a password to prevent storing the credentials in a way a hacker could steal. Due to the way hashes work, not all are created equal. Some are more vulnerable than others, and a little Python could be used to brute-force any weak hashes to get the passwords they were created from.

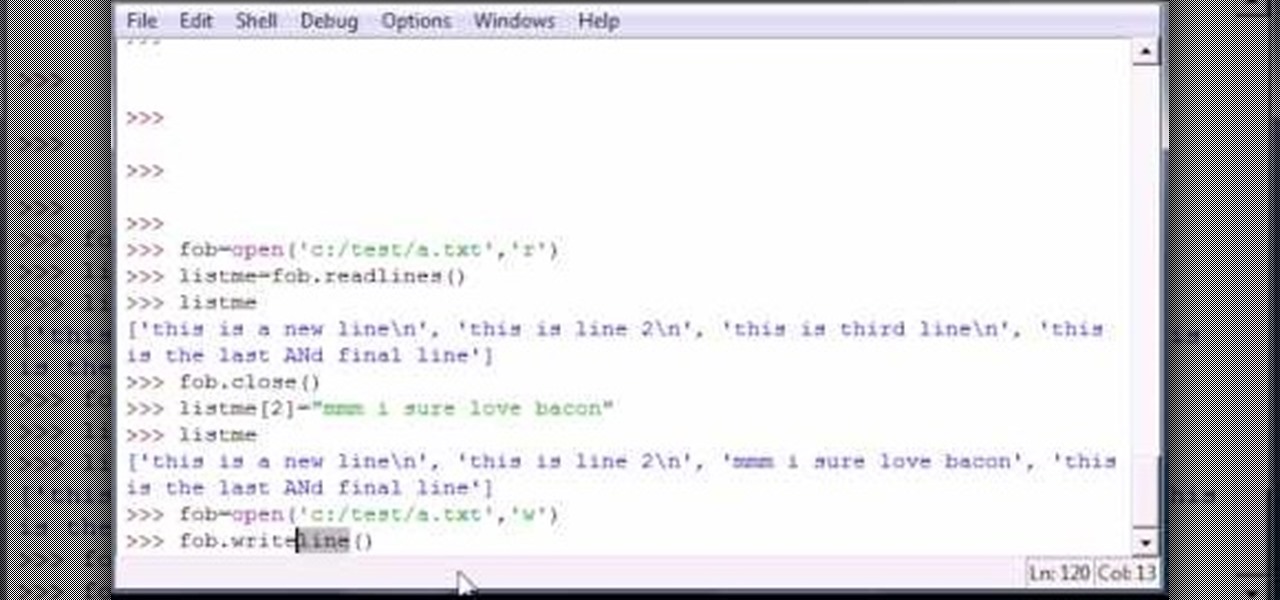
Bucky from The New Boston serves up this Python video tutorial on how to read and write lines in files in Python. This is the program you use to write all of your Python code down. Fun with reading and writing lines into a file!

Bucky from The New Boston serves up this Python video tutorial on how to program and write lines in files in Python. This is the program you use to write all of your Python code down. Fun with writing lines into a file!

Would you like to have news read to you? Or simply wish you could have a podcast that covered whatever you please? In this video tutorial, you'll learn how to use the Apple OS X Automator and RSS to create your own podcasts, automatically, without writing a line of code. For step-by-step instructions, take a look at this great how-to.

Correctly identifying the underlying technologies that run on a website gives pentesters a considerable advantage when preparing an attack. Whether you're testing out the defenses of a large corporation or playing the latest CTF, figuring out what technologies a site uses is a crucial pen-tester skill.

One of the first steps in attacking a web application is enumerating hidden directories and files. Doing so can often yield valuable information that makes it easier to execute a precise attack, leaving less room for errors and wasted time. There are many tools available to do this, but not all of them are created equally. Gobuster, a directory scanner written in Go, is definitely worth exploring.

In a previous tutorial, we were able to measure horizontal surfaces such as the ground, tables, etc., all using ARKit. With ARKit 1.5, we're now able to measure vertical surfaces like walls!

Have you noticed the many utility ARKit apps on the App Store that allow you to measure the sizes of horizontal planes in the world? Guess what? After this tutorial, you'll be able to do this yourself!

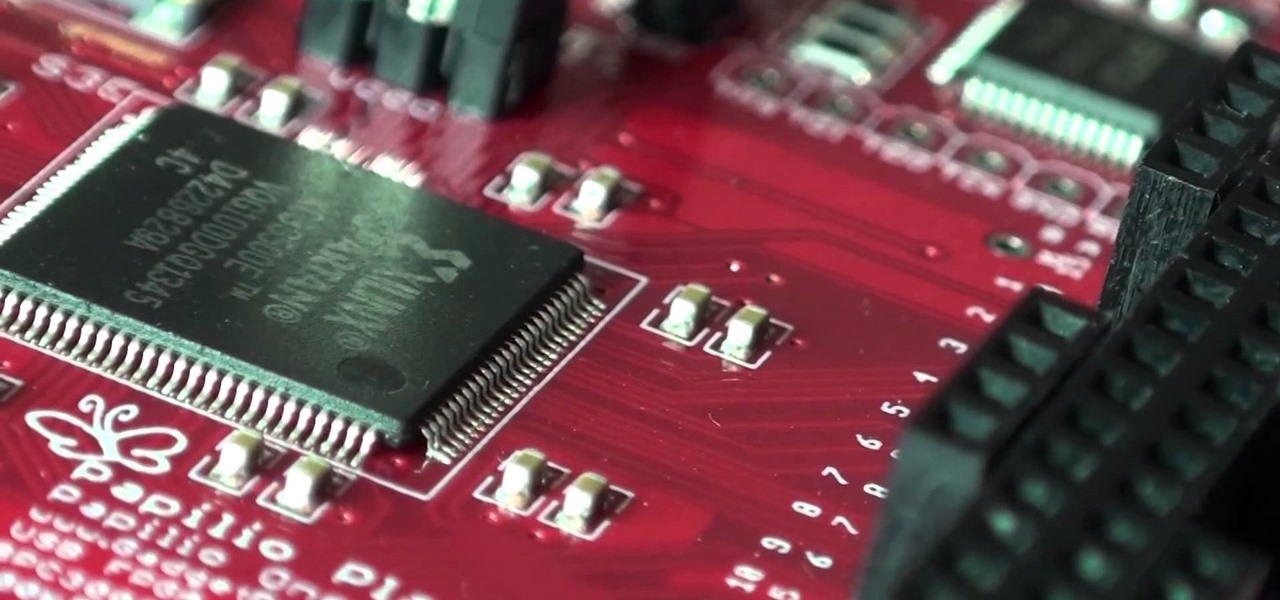
A FGPA is chip that is programmable with the computer to create circuit. It is a totally different type of programmable board compared to an Arduino for example. The Arduino will follow lines of codes to generate the necessary outputs. A FPGA won't however read lines of code, but it is a circuit itself. When the chip is programmed, a series of AND-ports, OR-ports and many others ports are linked together. The FGPA will increase the speed and the possibilities of your designs! I assume that by...

Both the Gears of War 3 Limited and Epic Editions contain a DLC code that allows you to unlock and play the Adam Phoenix character. The code is a little hidden, and unlike most DLC codes, isn't printed on the back of the manual. This guide from IGN will show you where to find the Adam Phoenix DLC code.

Ever notice how some augmented reality apps can pin specific 3D objects on the ground? Many AR games and apps can accurately plant various 3D characters and objects on the ground in such a way that, when we look down upon them, the objects appear to be entirely pinned to the ground in the real world. If we move our smartphone around and come back to those spots, they're still there.

Shodan calls itself "the search engine for internet-connected devices." With so many devices connected to the internet featuring varying levels of security, the special capabilities of this search engine mean it can provide a list of devices to test and attack. In this tutorial, we'll use Python to target specific software vulnerabilities and extract vulnerable target IP addresses from Shodan.

Developing GUI apps in python is really cool. I ask those who understand the language to help convert some of the command-line or console programs or apps ( I mean programs that are useful to a hacker ) to GUI. I know GUI makes us lazy and not wanna learn but we should all know its fast. Today's tutorial is on p2p chat app I developed last week and decided to share it with the community since its kinda cool.

All of the new iPhones from 2018 were released with dual-SIM support, but none of them were capable of actually using the eSIM in iOS 12, only the physical nano-SIM. But on iOS 12.1 and later, you can finally take advantage of eSIM so you can have, say, a business and personal plan on your iPhone XS, XS Max, or XR at the same time.

If you're a developer looking to get some exposure for your high-quality app, or if you're a user hunting for new apps and would like a chance to win a paid app at no cost, then Jack Underwood's new Promo Codes app may get you there, which you can install for free from the Google Play Store.

Welcome back, my amateur hackers! Over the course of the next year, we will be developing our own zero-day exploits. In my first article in this series, I introduced you to buffer overflows, which are the source of some of the most lethal exploits, particularly the "remote code execution," so we are focusing our exploit development here on a buffer overflow.

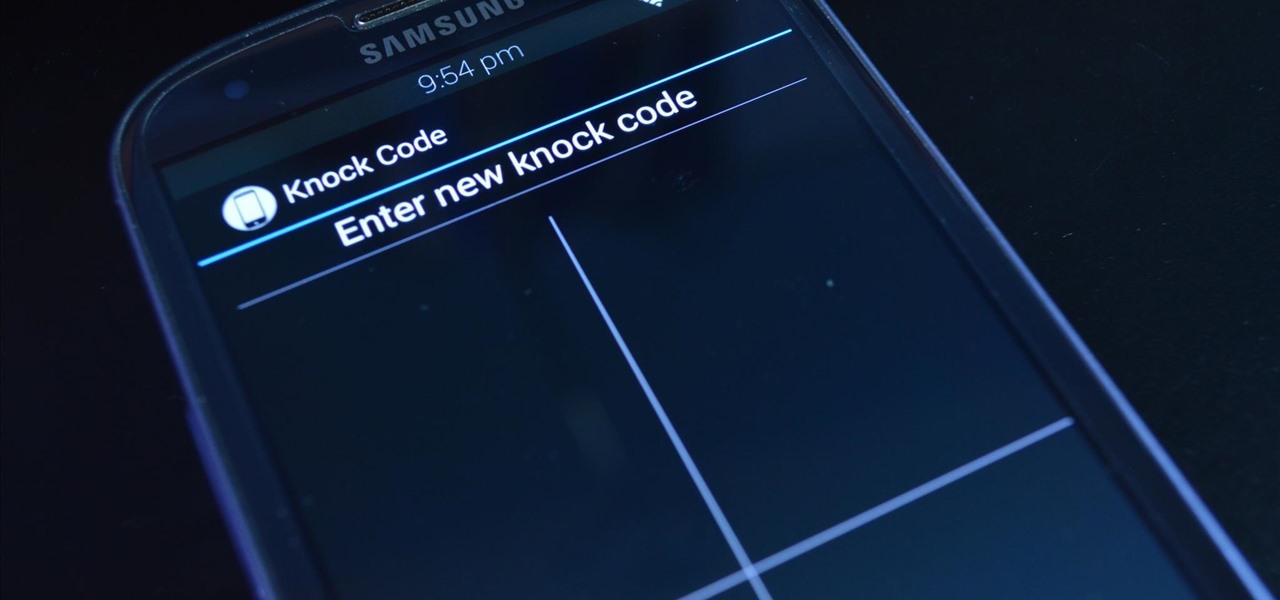
LG's arsenal of screen-off and screen-on tap gestures recently expanded into lock screen territory. Dubbed "Knock Code", this feature allows owners of various LG phones, like the G2 and upcoming G3 to unlock their phone with a series of taps on the screen. The most impressive part is that the screen doesn't even need to be on!

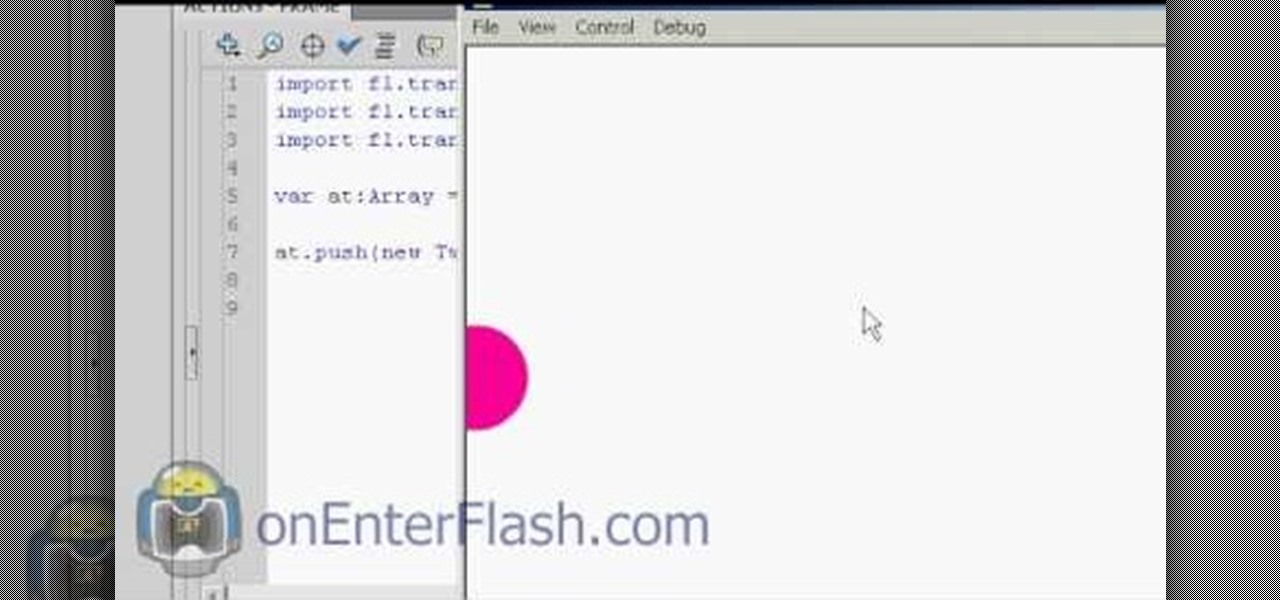
Most of you viewers out there who are familiar with Flash, After Effects, or other creative software know what a tween is. But can you write the code for them? This video will teach you how to code different classes of tweens using Actionscript 3 in Flash CS4.

One of the first steps when pentesting a website should be scanning for hidden directories. It is essential for finding valuable information or potential attack vectors that might otherwise be unseen on the public-facing site. There are many tools out there that will perform the brute-forcing process, but not all are created equally.

KeePassX, 1Password, and LastPass are effective against keyloggers, phishing, and database breaches, but passwords managers rely on the operating system's clipboard to securely move credentials from the password vault to the web browser. It's within these few seconds that an attacker can dump the clipboard contents and exfiltrate passwords.