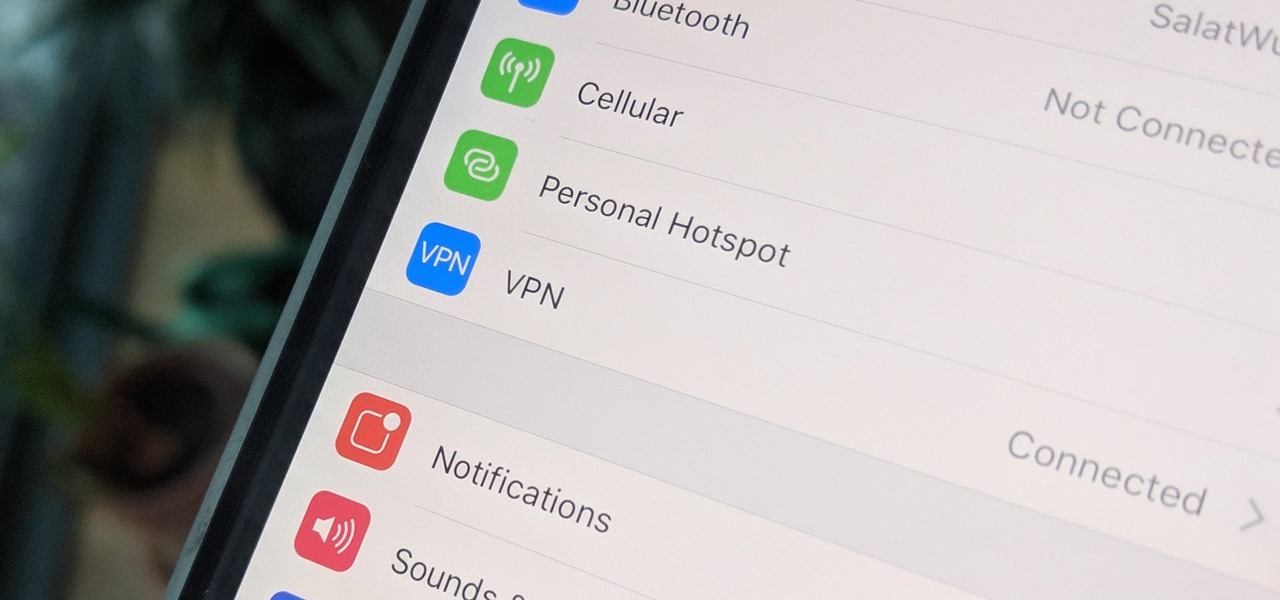
A virtual private network is a necessary part of your arsenal if you're insistent on surfing the web privately and securely on your iPhone. The App Store is littered with hundreds of different VPN services that encrypt traffic and mask your IP address, but what they all have in common are connectivity issues.

Conducting phishing campaigns and hosting Metasploit sessions from a trusted VPS is important to any professional security researcher, pentester, or white hat hacker. However, the options are quite limited since most providers have zero-tolerance policies for any kind of hacking, good or bad. After researching dozens of products, we came out with 5 potentials that are ideal for Null Byte readers.

Transferring hundreds of screenshots, webcam recordings, keystroke logs, and audio recordings between your VPS and a local Kali machine can be tricky. Services like Dropbox don't always have the best privacy policies and suffer data breaches just like any other website. To mitigate these risks, we'll use a secure, open source, and decentralized alternative.

Backdooring a powered-off MacBook is easy when a few minutes of physical access is allowed. That attack works well if the hacker also shares a Wi-Fi network with the victim, but this time, I'll show how to remotely establish a connection to the backdoored MacBook as it moves between different Wi-Fi networks.

If you've been watching the latest USA TV Series Mr Robot, you will have seen the Raspberry Pi used by Fsoeciety to control the HVAC system. OTW covers this very well here with his take on setup they may of used.

In the previous article in this short series, we learned how to find our neighbor's name using publicly accessible information and how to monitor device activity on their home network. With this information at our disposal, it's time to get into installing and configuring the necessary tools to begin our attack on John Smith's computer.

At the Google I/O keynote presentation today, Clay Bavor, Vice President of Virtual Reality for Google, shared a number of new initiatives in virtual and augmented reality. This included new services for the Tango platform called visual positioning service, or VPS.

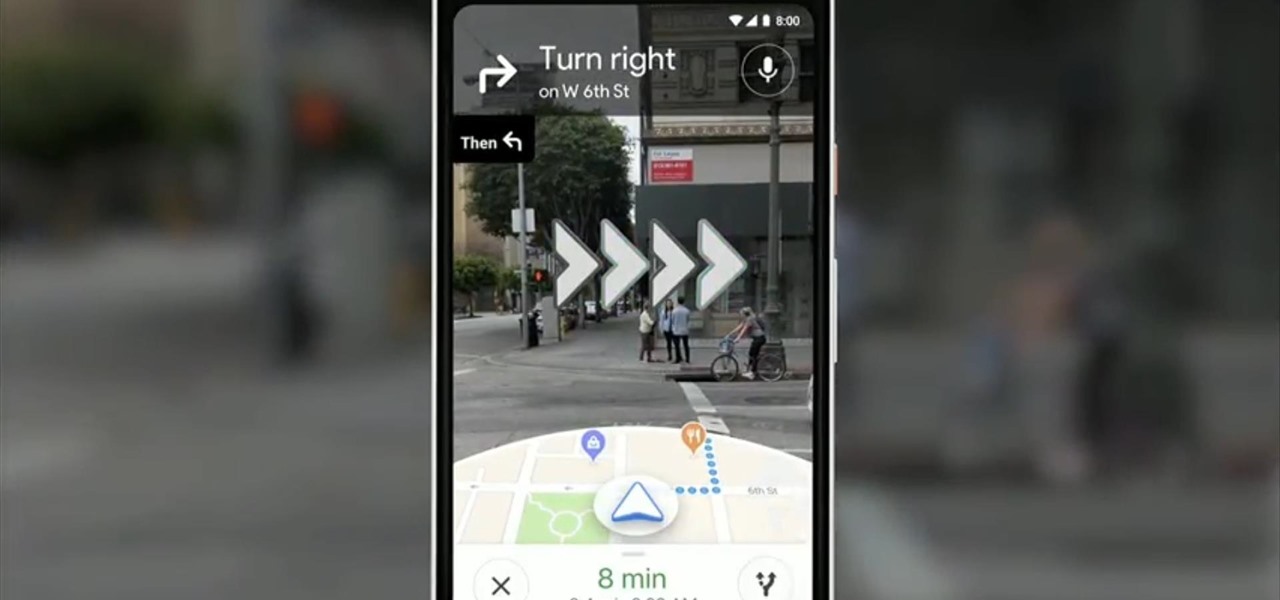
At Google's I/O developer conference keynote on Tuesday, ARCore may have been absent, but Google did preview a potentially trailblazing augmented reality feature for Google Maps.

Screenshots taken from a compromised computer can provide hackers with access to private emails, photographs, and information found in sensitive documents. This data can be used by the attackers to build profiles of a target for social engineering attacks and blackmail or even just to release the information out in the wild.

proxyFinderEnterprise is a tools for find proxylist . in this topic you learn how to use this tools for find a proxy list .

With an ordinary birthday card, we can introduce a physical device which contains malicious files into someone's home and deceive them into inserting the device into a computer.

A powered-off Windows 10 laptop can be compromised in less than three minutes. With just a few keystrokes, it's possible for a hacker to remove all antivirus software, create a backdoor, and capture webcam images and passwords, among other highly sensitive personal data.

Sherif Marakby has returned to Ford as the VP of AVs & Electrification after a brief stint with Uber. Marakby's VP title will be effective June 12.

Kings Dominion, an amusement park located in Doswell, Virginia, just announced a mobile augmented reality game for park visitors. Gameplay in The Battle for Kings Dominion — available on May 19 for iOS and Android devices — follows the playbook designed by Niantic through Ingress and Pokémon GO.

Apple announced upcoming changes today to prevent third-party tracking of users and prevent autoplay, on Safari. Safari will prevent the recording (by anyone other than Apple) of users' browsing behavior, and by doing so prevent advertisers from targeting ads based on individuals' history.

Flickr is the most known and dependable photo sharing website to date, so if you haven't made an account yet, you better now, if you want to share your precious photos with family, friends, and even the whole world! Flickr allows you to store digital photographs online and share them with other people.

The internet is constantly under siege by bots searching for vulnerabilities to attack and exploit. While conventional wisdom is to prevent these attacks, there are ways to deliberately lure hackers into a trap in order to spy on them, study their behavior, and capture samples of malware. In this tutorial, we'll be creating a Cowrie honeypot, an alluring target to attract and trap hackers.

The latest Star Wars movie, Solo: A Star Wars Story, has grossed almost $350 million worldwide during its first month in theaters. This is a good opportunity to discuss how hackers can use media hype (in this case, Hollywood movie hype) to disarm an unsuspecting Windows user into inserting an evil USB stick into their computer.

The microphone in a Windows computer is accessible to most applications running on the device at all times and completely without security limitations. Information gathered from recorded audio conversations taking place in the surrounding area of a compromised computer can be used for social engineering, blackmail, or any number of other reasons.

This video will show you how to tether your Samsung Messager 2, (the MetroPCS phone) to your PC to use as a modem for internet access. This will allow you to use your cell phone as your internet connection point, meaning you'll connect to the net for the cost of your cell phone's data plan. You will need your Samsung USB cable, a PC with Windows 2000 or higher, all current drivers for your phone and PC, and you will also need to head here to get the Samsung PC Studio program. This is part 1 o...

Systm is the Do-It-Yourself show designed for the common geek who wants to quickly and easily learn how to dive into the latest and hottest tech projects. They will help you avoid pitfalls and get your project up and running fast. In this DIY episode, see how to create an Internet enabled claw game.

This tutorial demonstrates how to use Microsoft Internet Explorer and Mozilla Firefox. Learn more about web browsers in this free instructional video series.

This week, Dr. Sung-Hoon Hong, Vice President of Samsung Electronics, announced at the Virtual Reality Summit in San Diego that not only does Samsung have a new virtual reality headset coming, but that Samsung intends to enter the field of augmented reality, too. In fact, Hong talked very little about virtual reality and instead spoke at length about Samsung's move into augmented reality.

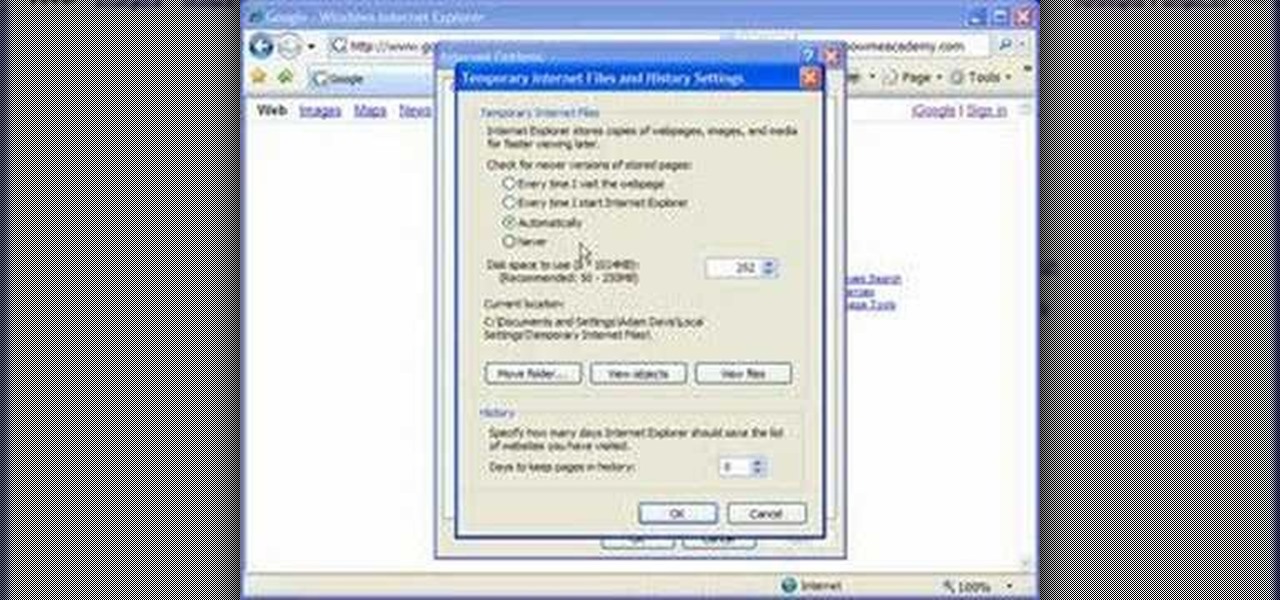
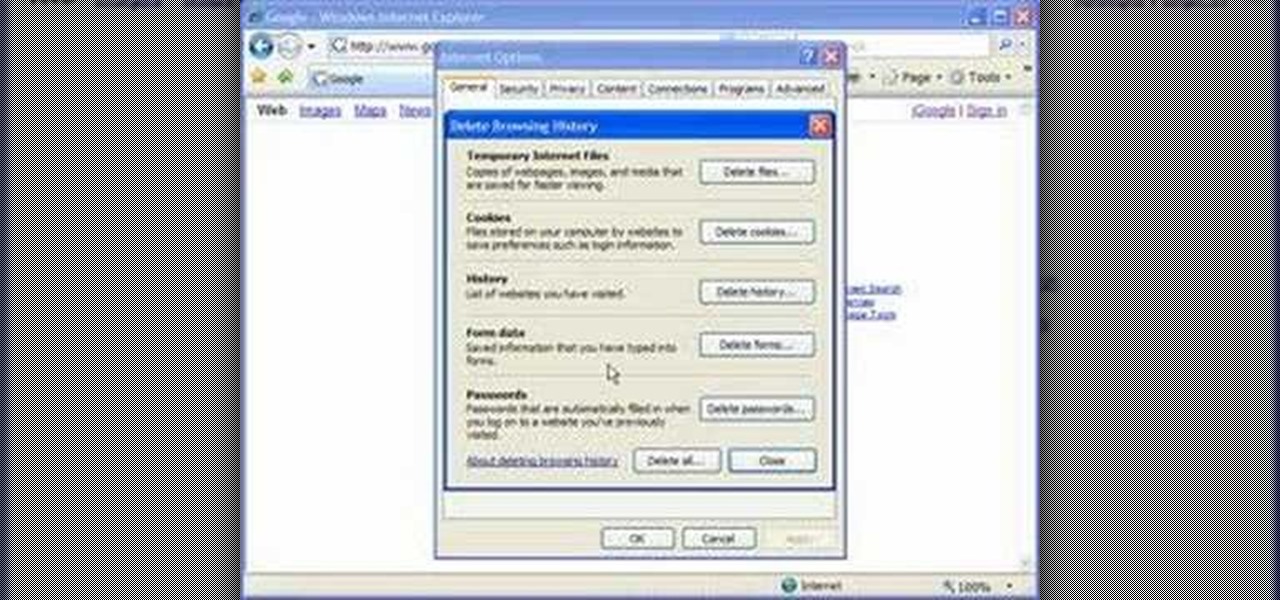
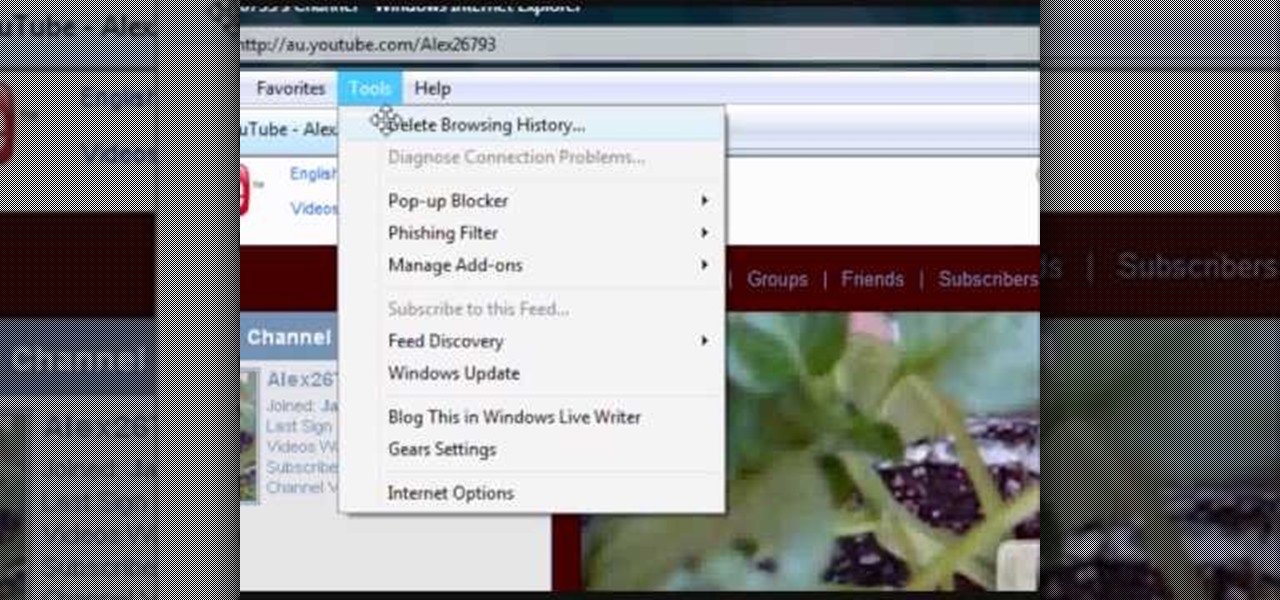
In this Computers and Programming video tutorial you will learn how to delete temporary internet files in Internet Explorer 8. The video is from FreeComputerRepair. Click on Start -> control panel ->network and internet connections -> internet options. Now the internet properties dialog box opens up. Here you go down to browsing history and click ‘Delete’ button. This will open up the Delete Browsing History window. Here you check all the data that you want to delete. If you don’t want to del...

With iTunes, you can listen to the radio over the internet and hear broadcasts from around the world. Make sure your computer is connected through the internet, then click "Radio" in the source list to see the internet radio stations available through iTunes.

In this video, we learn how to automatically clear browser cache in Internet Explorer. This will help your internet run faster and it will also help protect your computer from your personal information being store. First, open up Internet Explorer, then click on the tools drop down menu and go to internet options. From here, go to temporary internet files and click on the button that says "automatically", then adjust the disk space to use to what you prefer. After you have changed the setting...

Play remotely with all your friends, stream videos and music from the Internet or even check your Facebook and email - all with your PSP. The PSP has Internet capability, but not every network will be available to you at all times. Here is how you can hack any wifi connection with your PSP.

If you've already gotten your hands on Sony's Internet TV Blu-ray Disc Player, powered by Google TV, then you know how powerful this thing is. But if you're thinking of getting one soon, this video series will help you learn what you'll be getting yourself into.

Cookies serve their purpose in Internet Explorer 7. They let the browser know which sites you have visited so you don't have to get security prompts every time you back to them. However, they can also slow down your browser, which can be frustrating. This video will show you how to delete cookies in Internet Explorer and browse faster.

Just because the internet renders you virtually anonymous does not mean social customs should be ignored. Just like in the outside world, there is etiquette that should be obeyed if you want to be treated as a friend rather than an annoyance online. In this how to video, Proper Ollie teaches you how you can have proper internet etiquette in social networking forums.

Have you maybe been eyeballing some things you'd rather other people didn't know about? Clear your Internet history and leave your anxiety behind.

There are many different applications and games on the Nintendo 3DS that can take advantage of an active internet connection over Wi-Fi such as Netflix or the eStore. Unfortunately, since the 3DS is a mobile device, you won't always have access to the internet. If you have a mobile hotspot on a smartphone or tablet, you can share the internet connection over wireless with the gaming handheld.

If your computer or web browser is running slowly, a good place to start clearing space is in your Temporary Internet Files. Temporary Internet files, as well as cookies, are collected every time you visit a site online. These files make it easier for your PC to remember your browsing history, and your log in information for various websites. However, sometimes all of these little files can add up into one big clog on your machine. If your computer isn't running up to par, follow along with t...

In this video, we learn how to remove our browsing history on Internet Explorer. First, click on "tools", then click on "delete browsing history". If you want to delete all of your browsing history, then click on that option. Most people are content with only deleting temporary internet files as well as browsing history. Getting rid of these will speed up your internet a bit. Another way is to go into "internet options", click under the "general" tab and choose which files you'd like to delet...

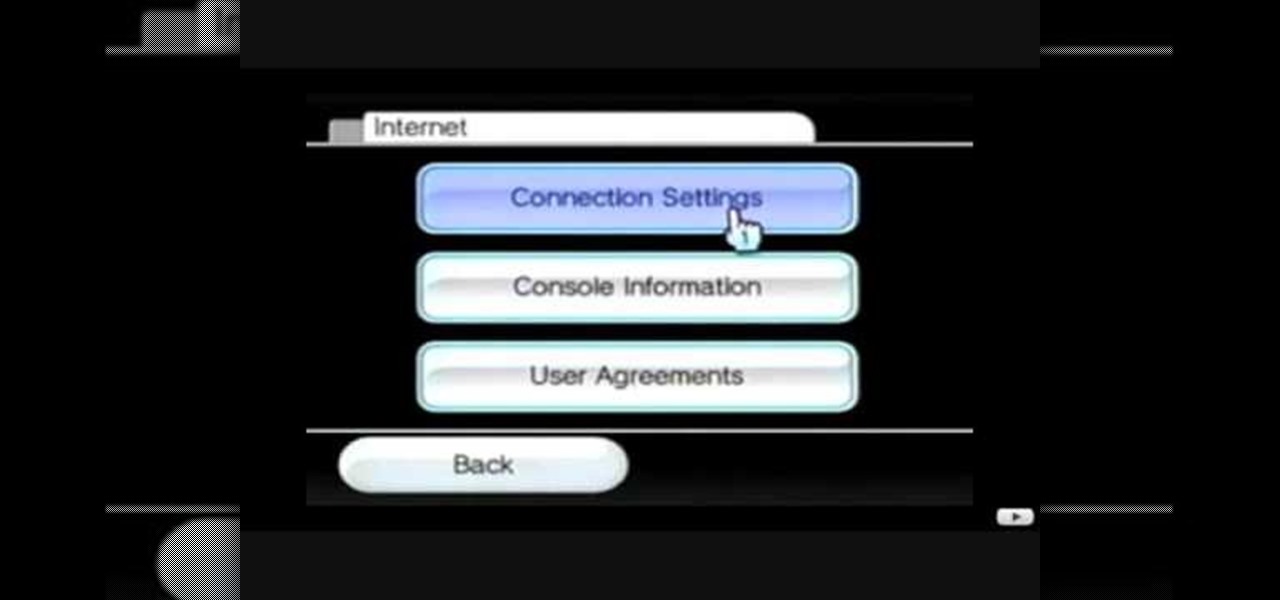
This video tutorial shows how to connect to the Internet using the Wii video game system. The advantage of connecting to the Internet with your gaming system is to play games, such as Animal Crossing or Call of Duty, with other players. You can also get the Internet Channel which allows you to watch YouTube videos and do other tasks you would normally do on the internet. You will need a wireless router to do this. On the Wii home menu, click on Options, Wii Settings, and scroll once to the ri...

Learn how to connect to the internet using your PS3 using an Ethernet cable. What you will need: 1. An internet modem or hub. 2. The details required to connect to the internet (password etc.). 3. A PS3 and an actual internet connection e. g. BT or AOL. Once you have those just follow these steps: 1. Take your Ethernet cable and plug it into the back of the PS3 into the socket labeled Ethernet. 2. Plug the other end into your internet modem. 3. Turn on your ps3 and go to "network settings" un...

To delete Internet Explorer 7 or 8 from you computer, search for "unlocker" in the Google search engine. Click on the first search result to go to the unlocker site. Click download to access the unlocker application. Click the save me option when prompted. Next, find the downloaded files and install the unlocker application on your computer. Go to the local disk C, open the program files and find Internet Explorer. Right click on Internet Explorer and then click on the unlocker. Select the ap...

This video is a step by step guide to clear cache for Internet Explorer version 7.0. On your Internet Explorer browser version 7.0, go to tools. Click Internet options. Go to general tab, then click browsing history and hit delete. Window will pop up. Click delete on temporary files and click yes to confirm. Click delete on cookies and click yes to confirm. Click delete on history and click yes to confirm. Click x to close the window and the current Internet Explorer window. Pull up a new Int...

Looking for an easy way to meter of your Internet bandwidth usage? This free video tutorial from the folks at CNET TV has got you covered. It details two freeware applications — one for Microsoft Windows, one for Mac OS X — that will help you keep track of your bandwidth usage. For the specifics, and to get started monitoring your own Internet usage, watch this helpful how-to.

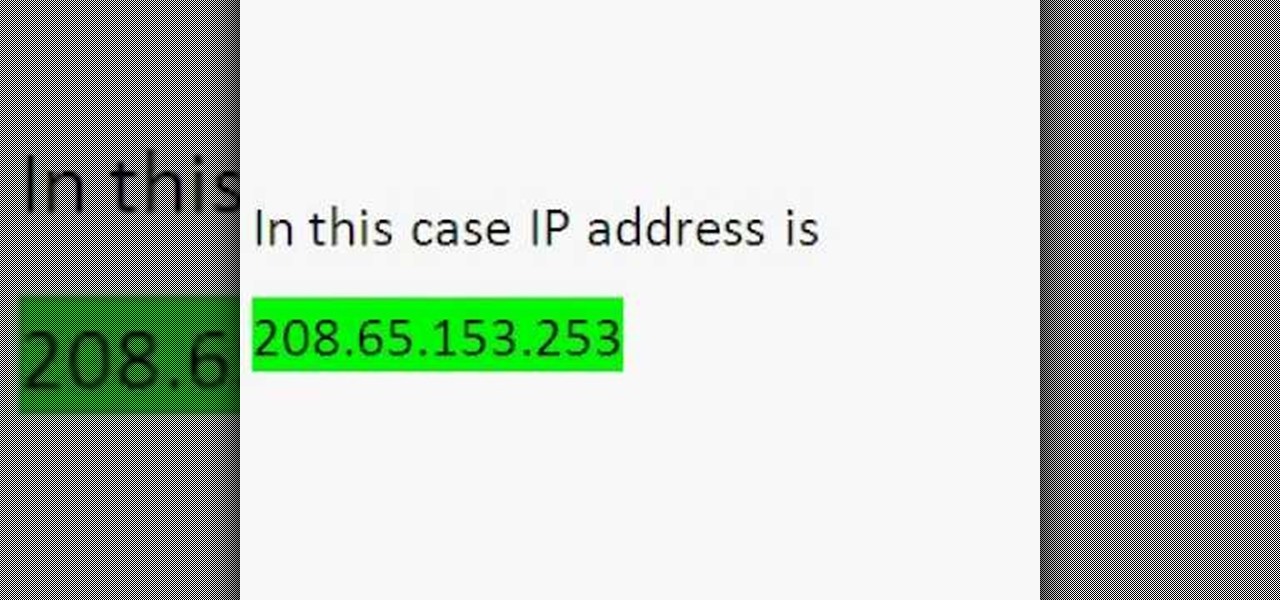
Wondering how to find the Internet Protocol address of a website?