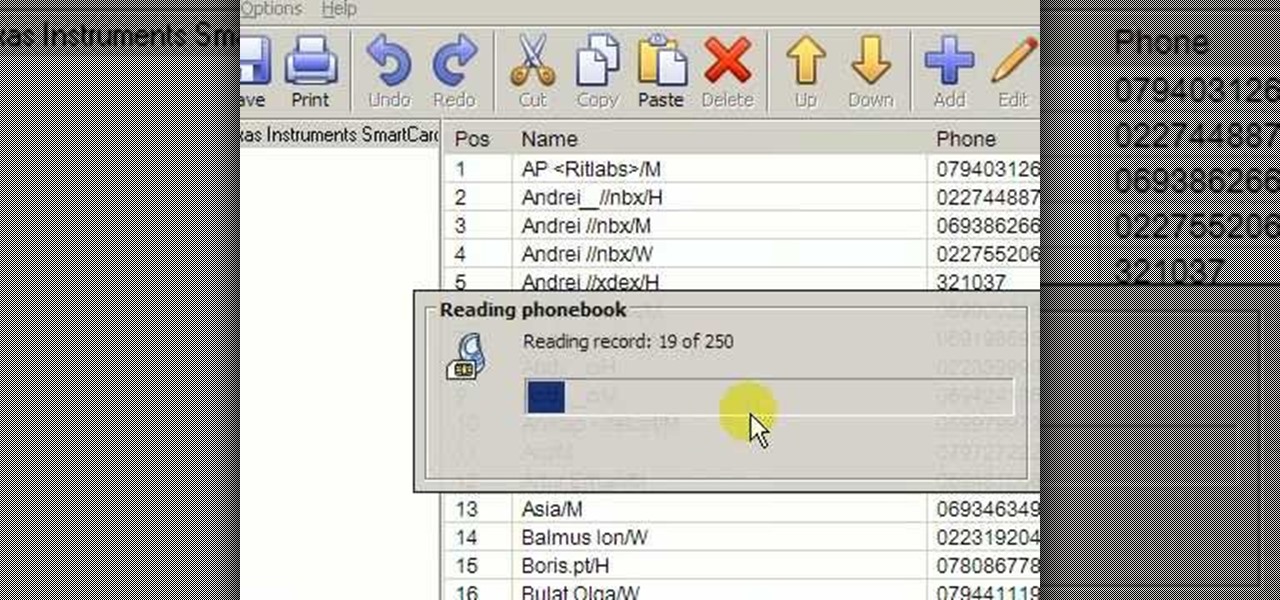
Accidentally deleted your address book? Got some sneaking suspicions you want to clear up? Got something to hide - permanently? In this video you'll learn what hardware and software you need and how to use it to recover deleted text messages, or, conversely, how to delete data permanently from your SIM card. Don't worry - we won't judge.

Welcome back, my neophyte hackers! Have you ever had a neighbor that you're certain is up to no good? Maybe you've seen him moving packages in and out at all hours of the night? Maybe you've seen people go into his home and never come out? He seems like a creep and sometimes you hear strange sounds coming from his home? You know he's up to no good, but you aren't sure what it is exactly.

I know I can't be the only person whose socks go missing in a shroud of mystery, but I'm determined to catch the sock-thieving gnomes in the act. While I have my suspicions, I can't quite prove it. Sure, I could drink a load of Red Bulls and never sleep, guarding my socks—but that's just crazy right? Luckily, I've found a way to set up my phone to catch the culprits.

Three variants of the Pixel 2 have appeared in Google's Android Open Source Project (AOSP) code, confirming various suspicions about which processor will power the Pixel 2.

Earlier last week, there were a number of fake five-star WhatsApp reviews to be found on the Google Play Store. Now, Gmail, Chrome, Messenger, and Firefox are all the latest victims to be saturated in five-star spam that wrongly refers to the word "game" in reference to non-game apps.

Waymo claims in court documents filed yesterday in its lawsuit against Uber that ex-Uber CEO Travis Kalanick knew that former Google engineer Anthony Levandowski was in the possession of stolen documents while employed at the troubled ride-sharing firm.

NOTICE: Ciuffy will be answering questions related to my articles on my behalf as I am very busy. Hope You Have Fun !!!

Developing an imperceptible lie is difficult, especially when you're lying right to someone's face. Thanks to smartphones, getting people to trust you is now easier than ever. You can craft a lie in seconds and hit send, all without ever seeing their untrusting faces.

One thing I absolutely cannot stand is lag when I'm gaming. Every time I'm about to beat my killstreak record on Call of Duty, my internet connection drops and I'm a goner. It never fails. This usually happens because someone else on my Wi-Fi is streaming a movie or downloading a huge file.

Repetitive use of apps over time will eat up your storage space with by caching data on your device. This can be useful at first, speeding up your apps by not requiring them to re-download frequently used data, but as a cache grows, even the initial performance improvements can be outweighed by the unwelcomed loss of storage space. And if a cache grows too large, the time it takes an app to access the cached data can be even slower than the time it would've taken to re-download the data in th...

For all the benefits 5G brings to cellular data, it isn't without weaknesses, the biggest being privacy. Yes, the latest standard comes with breakneck downloads speeds up to 4.3 Gbps, but at what cost? Like with all things on the internet, 5G devices open opportunities for both good and bad actors.

In my last tutorial, I talked about creating a virus inside of a Word Document in the scenario of a mass-mailer attack. In this post, however, I'm going to be covering creating a fake image or screenshot with a meterpreter backdoor hidden inside to be used in a similar scenario. Step 1: Creating the Virus

Welcome back, my novice hackers! Previously in my "Spy on Anyone" series, we used our hacking skills to turn a target's computer system into a bug to record conversations and found and downloaded confidential documents on someone's computer. In this tutorial, I will show you how to spy on somebody's Internet traffic.

Tony Parisi, the global head of VR/AR at Unity Technologies, has been passionately working with virtual and immersive spaces for a long time. And while the internet world we live in now is very different than when Parisi was co-authoring VRML (Virtual Reality Modeling Language) — an early attempt at creating 3D environments that would work in a web browser — some of the questions that were assumed answered are being asked again.

Does your network begin to crawl right around the time your sinister-looking next-door neighbors get home from work? Do you harbor suspicions that one or more of them may be stealing your Wi-Fi? It's easy to find out. And equally easy to give freeloaders the boot. In the guide below, we'll show you how to secure your wireless connection in three easy steps.
Ron Paul Republicans take over Nevada GOP

Fatherhood is difficult, especially when you're an octopus. That is the moral of the 2011 IGF Student Showcase winner Octodad, available for free from its website. This hilarious little title was created by a team of interactive media students at DePaul University in Chicago, and is the latest in a stream of successful indie games to come out of collegiate video game design programs. In fact, it's so successful that a sequel is in the works.

Are you prone to crusades of the overambitious? Well, here's one for you: try to find and identify every animal on earth. You may think scientists have a handle on this, having pinned down 1.4 million animal species so far, but there are millions more are out there, waiting to be found. Brazilian scientists have put the cost of finding the rest at a decisive $263 billion.

L.A. Noire is the newest Rockstar (GTA4, Red Dead Redemption) game created by Team Bondi ( The Getaway). The game is set in the late 1940’s in Los Angeles. The main character, Phelps, is a war veteran rising through the ranks from police officer to detective. The game is presented in mini episodes (one case per episode) and flashbacks. Once you finish a case, you go straight to the next one. Having played four cases where the character moves from police officer to detective, here are my initi...

It seems even Al-Qaeda is not immune to World Cup hysteria. The international terror network issued the following demented statement, early in the pre-season: