Some cops already have the ability to extract data from your cell phone using handheld forensic devices, but soon police officers will have a new mobile data collection toy to play with—an Apple iPhone. Actually, it's an iPhone-based device that connects directly to the back of an iPhone, which is designed to give law enforcement an accurate and immediate identification of a suspect based on their facial features, fingerprints and even their eyes.

In this how to video, you will learn how to break up with your girlfriend. First, you should make sure that problems have been building up. This is the initial part that should make you decide whether or not you want to go through with it. This includes your girlfriend nagging and complaining at you. If you are prepared to do this, the next part is the actually break up. You can approach your girlfriend in person and tell her it is over. Tell her why you are breaking up. Another method is bre...

This is a cool little trap that me and some friends came up with while messing around with TNT and redstone on a big platform in the sky. The reason we called it the 'Roof Lever Trap' is because it utilizes the ability to place levers on the bottom side of blocks, which was introduced in Minecraft 1.3.1.

One of the most anticipated new Maps features in iOS 11 for iPhones is live and ready to keep you safe on the road. Right now, Do Not Disturb While Driving is opt-in, but if you missed Apple's on-screen prompt to enable it and want to turn it on, or if you accidentally enabled it but want it turned off, we're here to help.
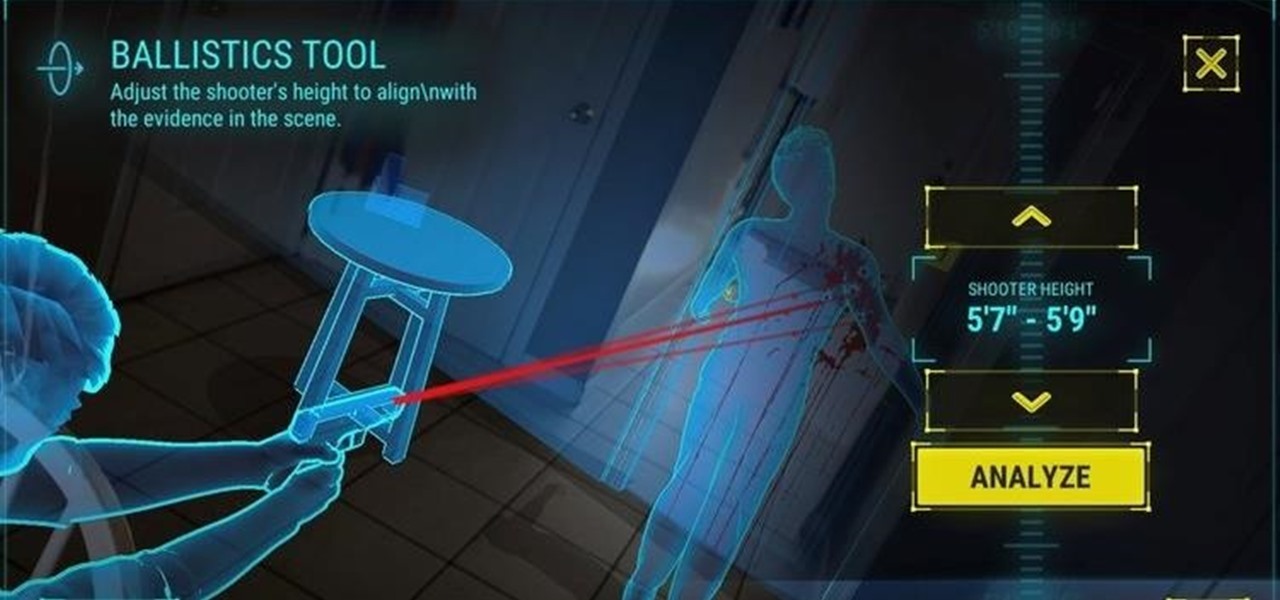
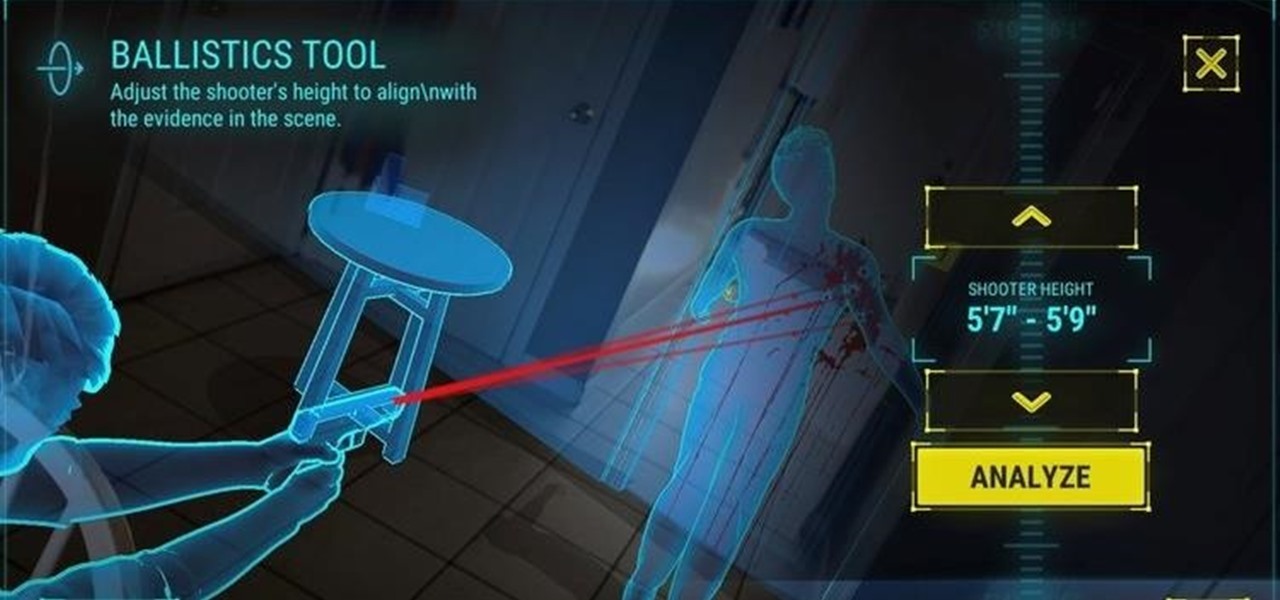
The crime procedural show is the perhaps the most direct path to the average TV viewer's heart. Could the same hold true for augmented reality games?

You know that feeling when your cell phone gets stolen and you figure it is pretty much lost forever. You could've used one of the millions of device managers and trackers, but ya didn't. And the Good Samaritan is not coming to your rescue.

Since The Guardian published leaked documents exposing the depth of the NSA's spying powers, many people who've never put much effort into protecting their privacy are finally starting to pay attention. Evidence of public opinion concerning PRISM can be seen from the rise in traffic for pro-privacy sites like DuckDuckGo to the petitions demanding that the program be scaled back or done away with altogether. Some would argue that you waive your right to privacy by signing the terms of agreemen...

Apple revealed three new iPhone models on Wednesday, Sept. 12, at its "Gather Round" event in Cupertino, as well as announced the official release date of iOS 12, its newest mobile operating system. If you missed it and want to watch the full event, here's how to do it on your computer, smartphone, or Apple TV.

The next big event Apple is holding is WWDC 2018, its Worldwide Developers Conference, is about to happen. If you want to see the first glimpse of iOS 12 for yourself, as well ARKit improvements, Apple Watch news, and maybe even some macOS announcements, here's how you can tune into the event right at home from your computer or mobile device.

Augmented reality is expected to eventually change everything, and the prevailing view is that those changes will be for the better. The converse view, however, is that the technology will further erode privacy.

Uber's driverless car program lead has quit after just one year working for the ride-hailing company.

Although the Magic Leap One: Creators Edition is currently officially available in only six US cities, those living outside of Magic Leap's designed US cities now have a roundabout way to order the device.

For many of us, pets are important family members. They give us loyalty, companionship, and comfort. Now, researchers have given us another reason to welcome them into the family: Babies from families with furry pets — the majority of which were dogs — had higher levels of two types of beneficial gut bacteria.

Store-bought marinades and sauces have an ability to jazz up the simplest items. But after a while, those favorite tastes seem a bit repetitive and mundane, and that got us to experimenting with different add-ins to make our marinades stand out. Fruits, herbs, spices—all of the usual suspects were delicious, but not spectacular.

Whether you call them chickpeas, garbanzo beans, or Egyptian peas, these little morsels are one of my favorite snacks—when properly seasoned, that is. Being mild in flavor on their own, they're incredibly versatile and fun to experiment with. (They're also incredibly healthy.)

If you've ever received an email from a sketchy address purporting to be Uber, asking you to sign in with your credentials, you might be a phishing target. Hackers use a fake login page from real-looking domains to trick you into giving up your account information, and while it's been an issue in the past, Uber is making it more difficult on cyber thieves with the addition of two-step verification.

Food is both a necessity and a joy. Many people enjoy exploring, cooking, eating, and learning about foods from around the world. But the picture isn't always rosy. A new report from the Centers for Disease Control and Prevention (CDC), highlights the ways and whereabouts of food that make us sick.

Hello friends. This is actually my first how to.

Barbecue season: it's the perfect time to play with fire, produce your best burger ever (until next year, that is), and find even more ways to make beer a part of your daily life. However, even a grilling badass occasionally gets stumped by minor BBQ problems. No worries: We've got solutions!

It's that time of the year, y'all—when the air becomes crisp, the nights grow long, and people crave hearty, warm soups and stews. And of all the season's offerings, my hands-down favorite has to be chili: It's versatile, meaty, and above all else, it's damn easy to make. (Thank you, Lord, for the slow cooker. Amen.)

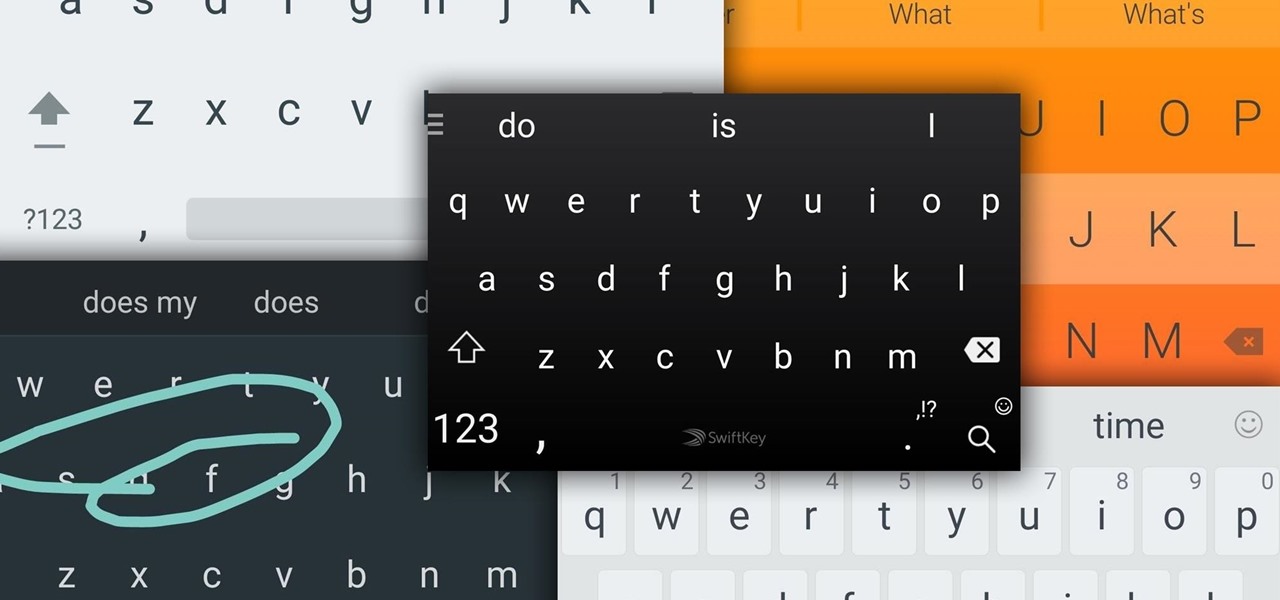
Google Now, Siri, and Cortana aside, the main way you interact with your smartphone is through the keyboard. Every app you use, every search you perform, every message you send—the most fundamental interface between you and your device is that handful of characters and those 26 letters on the bottom half of your screen.

Checking the weather ranks among the most mundane but essential tasks you can do on your smartphone. Thankfully, both the iOS App Store and Google Play are loaded with weather apps that add some much needed spice to this daily routine, giving you less of a reason to be caught unaware.

Many of us choose to use an iPhone — as well as other devices in the Apple ecosystem — because of the company's dedication to user privacy and security. If you need more proof of that commitment, look no further than iOS 14.5, released April 26, which adds new tools to protect our data while browsing the web and more control over the data installed apps collect on us.

At launch, Chromecast with Google TV is fairly limited in the number of compatible apps. Many of the usual suspects are there, but there are some interesting omissions, like Google Stadia (though support is coming). However, at its core, the device runs on Android 10, which means you can sideload apps, including those that don't officially support Chromecast with Google TV.

In the aftermath of the unindicted police killings of Michael Brown and Eric Garner, we've been told that the system worked as intended. When our legal system's outcome is at conflict with what a majority of Americans believe is just, it's clear that some changes are needed. But what specifically needs to change? And what can an average citizen with a moral and just cause do to prevent these kinds of tragedies from repeating themselves again and again?

Samsung's lineup of Galaxy Note devices for 2020 include the specs-behemoth Galaxy Note 20 Ultra and the slightly more cost-effective Galaxy Note 20. Excuse the pun, but there's a lot to unpack here in terms of unique features and hardware.

In the case of Apple Watch v. Fitbit, the winner comes down to the judge at hand. Apple currently offers two smartwatches — the Series 5 and the Series 3 — while Fitbit offers three models — the Fitbit Versa 2, Fitbit Ionic, and Fitbit Versa Lite. Whatever your assumptions about these devices are, throw them out the window, as each has something unique to bring to the table.

WikiLeaks. In recent weeks, it's been the hottest topic on the web. It's been attacked on a multinational level by political influence peddling.

In this video, Sky Van Iderstine will tell you how to get your IP address e-mailed to you every time it changes by using a freeware program, Wimp. With this information, you can then track your stolen Mac laptop or even desktop's location using www.ip-adress.com (the "adress" is not a typo.) Imagine the look of the police officers when you show them the satellite picture of your suspects location! Locate your stolen Mac laptop using Wimp.
In case you haven't figured out already, our government is always on the move to figure out new ways to extend their control. The CISPA, for one, is one of the best examples, along with "re-education" programs, and racial divide (Trayvon). What I've noticed in the past few months is that their new "ideas" are coming out at an increasingly alarming rate.

Amazing actor who you know his face but most likely don't know his name. His latest role was the really mean boss man in THE TOWN.

“Of drones I think two words” Khan said. “It’s immoral and it’s insane. Immoral because you cannot justify eliminating suspects and insane because it’s counterproductive. All it does is it turns more people against the US, hatred grows and the beneficiaries of this insanity are the militants.” » Top Pakistani Politician Calls Drone Strikes “Insane, Immoral, War Crimes”.

Wiretaps, which have increased almost tenfold since data was first reported in 1969, are only the tip of the surveillance iceberg. In 2011 federal and state courts approved a total of 2,732 wiretaps; but government agencies made over 1.3m requests for data to mobile-phone companies. That figure includes wiretaps and pen/traps, but it also includes requests for stored text messages, device locations and tower dumps, which reveal the presence of everyone—suspects and not—within range of a parti...

Giveaway Tuesdays has officially ended! But don't sweat it, WonderHowTo has another World that's taken its place. Every Tuesday, Phone Snap! invites you to show off your cell phone photography skills.

The Writers at io9.com have been running through a fantastic series of blog posts, in which they're teaching their readers about the history of great 80s sci-fi and fantasy. Because so much of this is right up my alley, I though I'd aggregate their aggregations, so to speak, and write a little retrospective of my own.

Your constitutional right to privacy cannot be violated by police, so ruled the United States Supreme Court in a unanimous decision on two cases from California and Massachusetts—a major ruling for privacy advocates worldwide.

Well, The Prophet Blog and Chart Rigger must be squirming in their matching trash bag onesies right now, because their stinky princess K$UX‘s new track is a proper T-U-N-E.