
How To: Play "MakeDamnSure" by Taking Back Sunday on guitar
Learn how to play "MakeDamnSure" by Taking Back Sunday, an acoustic guitar tutorial. Follow along with this demonstration, tabs and lyrics here:


Learn how to play "MakeDamnSure" by Taking Back Sunday, an acoustic guitar tutorial. Follow along with this demonstration, tabs and lyrics here:

In this video, we learn how to play "Detroit Rock City" by KISS on electric guitar. Start out with Eb, Bb, Gb, Db, Ab, and Eb. Pull of the first fret and go to the second, then do this over four times. Once you have finished this, do it over three more times until you reach the end. Now, you will place your fingers on the fourth string fourth fret, then do these chords over again three more times. There will be another guitar playing Eb, Bb, Gb, Db, Ab, and Eb as you continue on playing this,...

Although the Health app mostly focuses on fitness, Apple has slowly added features to help with other aspects of well-being, including hearing. In iOS 13, there's now a headphones volume tracker in Health that monitors audio levels and lets you know when your music, podcast, movie, or whatever else is too loud.

Hello my fellow hackers, it's been a while since my last post, I can't get the time now-a-days for the posts but can manage to tend to comments.
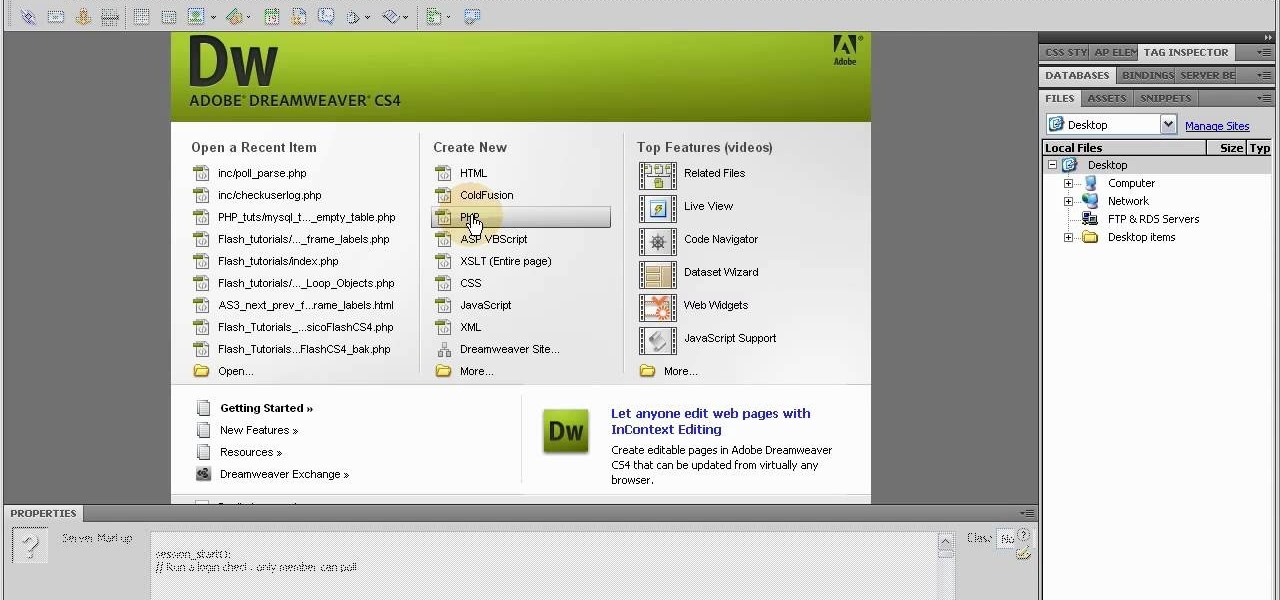
In this clip, you'll learn how to reset or truncate a MySQL DB table directly with script or indirectly through PHPMyAdmin. Whether you're new to the PHP scripting language or a seasoned developer mereley looking to pick up a few new tips and tricks, you're sure to benefit from this video tutorial. Take a look.

The tutor suggests that you do 87% to 93% of your maximum on this drill. Take deep breaths while doing these exercises. You have to do five sets followed by rest for one and half minutes for each exercises.1. First of all you have to start with the first overload drill which is the heavy DB chest press. You have to lie down on your back on the bench and hold the drills in your hands and then bring these two drills up. You have to do the repeats of four to seven only for this exercise.2. Now d...

Learn how to play "Goodbye" by Secondhand Serenade, an acoustic guitar tutorial. Follow along with this demonstration, tabs and lyrics here:
Jay-Z's Tidal streaming service provides Hi-Fi music to a mainstream audience. Even better, Tidal can do this without blowing out your eardrums, because it's easy to enable volume normalization so that one track isn't louder than the next.
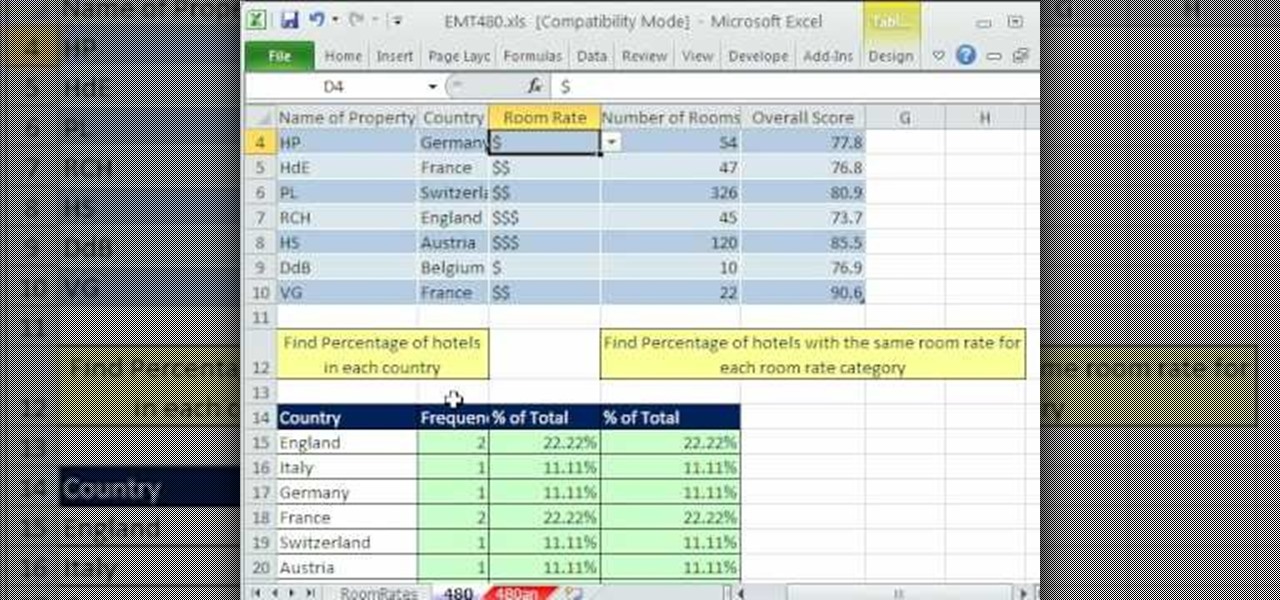
New to Excel? Looking for a tip? How about a tip so mind-blowingly advanced as to qualify as a magic trick? You're in luck. In this Excel tutorial from ExcelIsFun, the 480th installment in their series of digital spreadsheet magic tricks, you'll learn how to calculate a percentage of total from a database data set when the variable of interest is text (word). This is accomplished with recourse to the COUNTIF, SUM & COUNTA functions.
In this video tutorial, learn how to get auto tune, or the t-pain vocal effect, in Audacity using gsnap. To get the GSNAP (GSnap/Grymmjack skin), go here.

Plug this baby into your FiOS-powered computer and simulate the real-time climate of any location in the country -- rain, lightning, fog, sunshine.
In this video, we learn how to start doing pull-ups. First, stand up while you pull down on the machine at a weight you can handle. After this, do wide lat pulls using a weight that is heavy for you, but you can still handle. Next, do seated row exercises in sets to where you can't do anymore of them. Low cable rows are your next exercise, making sure you have the right form while doing them. Start to do W's next, while sitting down on your knees and using control with your arms. After this, ...

In the driverless race, technological advances can sometimes just add more tension to an already heated competition, if Waymo suing Uber over their allegedly stolen LiDAR technology is any indication. Now, Sony is offering a new camera sensor, one that should help self-driving cars "see" the road with much more accuracy than any other camera sensors available for vehicles currently.

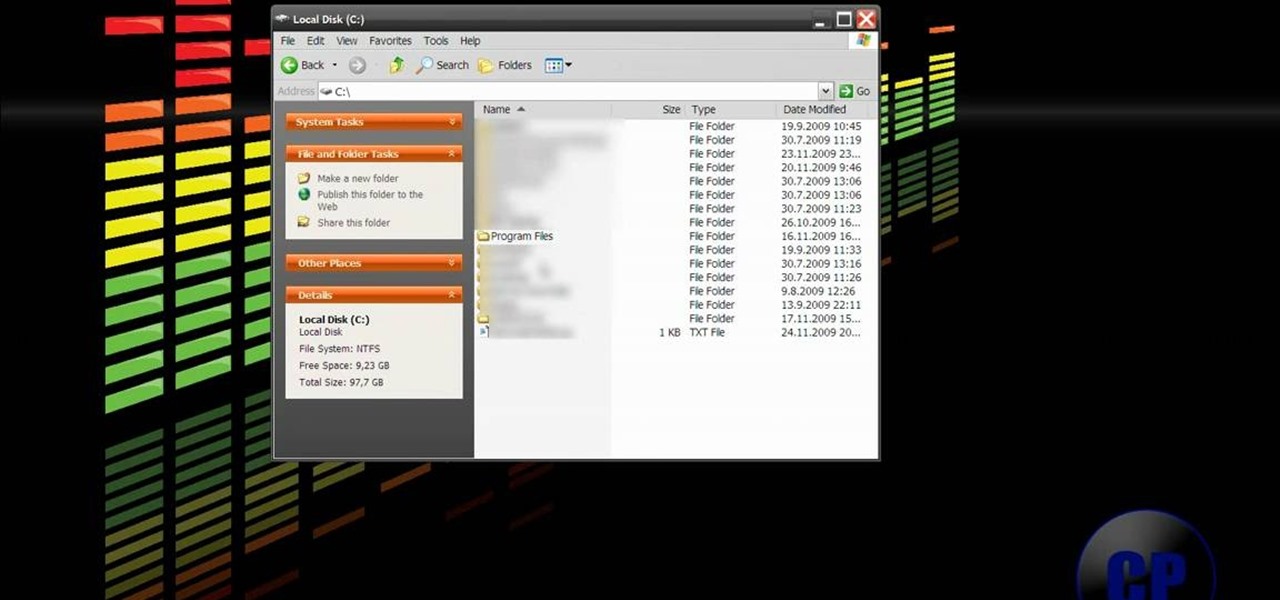
Today I will show you how to make a metasploit exploit really quickly. This tutorial is mainly applied to stack based buffer overflows and seh buffer overflows exploits .There is a simple way for rop exploits too but I will dedicate a special tutorial on this subject.

If you have a Mac running Mountain Lion, I'm sorry to tell you that all it takes to crash almost any app on it is eight little characters. This strange bug seems to only affect Mountain Lion and doesn't cause your computer any harm. Apparently, it even crashes the error reporter. On its own, the bug doesn't really pose a threat—just don't type it.

A member of the woodwind family, the flute is a reedless instrument that plays music when air is blown over the opening or an edge. Early flutes were made of bone and date back 30,000 to 50,000 years in certain parts of the world. In this series of videos, learn more about playing the flute in the key of Db from our expert.

In this great video series our expert Ryan Larson, a great accordion player, shows us not only how to play in the key of Db and all the notes in that key but also how to instantly better our improvisational skills.

Passwords stored in web browsers like Google Chrome and Mozilla Firefox are a gold mine for hackers. An attacker with backdoor access to a compromised computer can easily dump and decrypt data stored in web browsers. So, you'll want to think twice before hitting "Save" next time you enter a new password.

Welcome back, my tenderfoot hackers! One of the issues we often encounter with Metasploit is how to add new modules. Although Rapid7 (Metasploit's owner and developer) periodically updates Metasploit with new exploits, payloads, and other modules, at times, new modules appear that are not added to the Metasploit repository.
This is for those using Kali Linux 2.0 that need to edit the CRDA values to get the increase in Txpower

It used to be easy to hack tethering—root your device and install a third-party or modded tethering app. But snuck in amongst the changes in Android 4.3, a new data-monitoring service of sorts made its debut. There used to be a time when your data connection was yours. You paid for it, so you were free to use it for whatever you wanted. Unfortunately, those days are long gone.

Learn how to play "The Truth" by Daniel D on the piano.

Making a NANDroid backup can save you from all sorts of flashing-related mishaps and accidents. Bootloops, SystemUI crashes, accidental wipes, bad ZIPs, or a dozen other possibilities—there's almost no condition in which a NANDroid is unable to correct problems with your device. However, recent changes to Android have created an almost paradoxical situation where restoring a NANDroid can actually lock you out of your phone.

This is a short explanation and tutorial on how to grab saved passwords from Google Chrome, ideally from a meterpreter session. The idea behind this is to understand how saved passwords work and how to keep them safe. Let's have some fun :D Understanding Google Chrome Saved Passwords

Welcome back, my budding hackers! When we are looking for ways to hack a system, we need a specific exploit to take advantage of a certain vulnerability in the operating system, service, or application. Although I have shown you multiple ways to exploit systems here in Null Byte, there are still many more exploits available that I have not yet shown you.
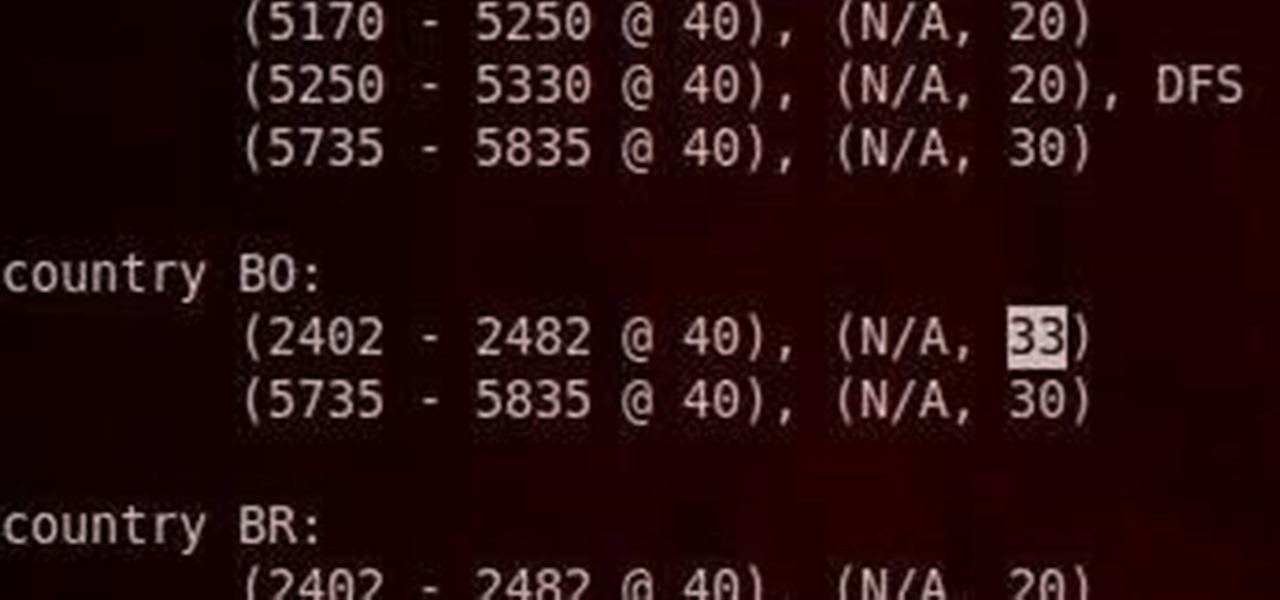
Do you have an Alfa AWUS036NH Wi-Fi adapter that claims it can go to 2000 mWs, or some card that can supposedly transmit power over 1000 mW? If so, you may have run into problems setting your card's TXPOWER higher than 30 dBm, which is about 1000 mW. Well, I will show you how to break that barrier and go as high as you want!
Yes, I understand some people may consider this a repost. However, I have been searching for this answer for 3 weeks and after reading numerous reddit post, Kali Forums post and Null byte post I finally have gotten it to work for me. I would like to compile and share this information with you guys.

In this how to video, you will learn how to master and mix a rap song using Cool Edit Pro 2. First, download the program and open the vocal track in the program. Double click the vocals to highlight it all. Next go to effects and pick amplitude and amplify. Choose center wave and click okay. Go to amplitude again and choose dynamic processing. Choose very fast processing. Go to delay effects and type in 250, 10, 1812, 20, 100%, and 30% in the window. Next, go to filters and pick FTT filters. ...
Welcome hackers. Hackacademic.RTB1 is vulnerable machine for training our skills.This machine can be download from free from here. There is many tutorial how to hack these machine but i did always be my self.

Hello everyone! Hope everyone having good day!! I wanted to share an easy way to locate an appropriate exploit from the EDB, get it compiled, and run it all from inside the terminal.
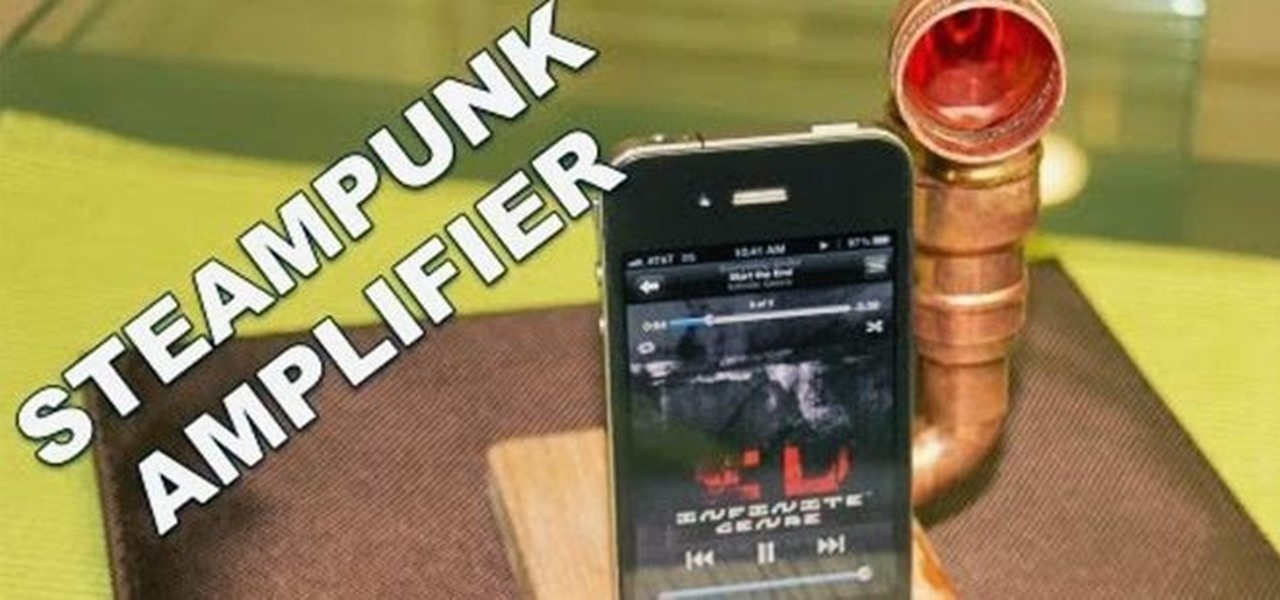
Do you listen to a lot of music on your smartphone or MP3 player? Ever wished the built-in speaker was louder? You're in luck, because this simple amplifier can increase your volume by 14 decibels and make your device look totally steampunk while you're at it. What You'll Need

Welcome back, my amateur hackers!

Learn how to play Shout it out loud by Kiss on electric guitar. The guitar is tuned down 1/2 step for this song (Eb, Bb, Gb, Db, Ab, Eb). First riff: Two lead guitars are playing together. 2nd string, 16th fret, twice. Bend up and back down. 14th fret. Second guitar is playing 2nd string 12th fret twice. Repeat twice. Bend it up and down. 10th fret.
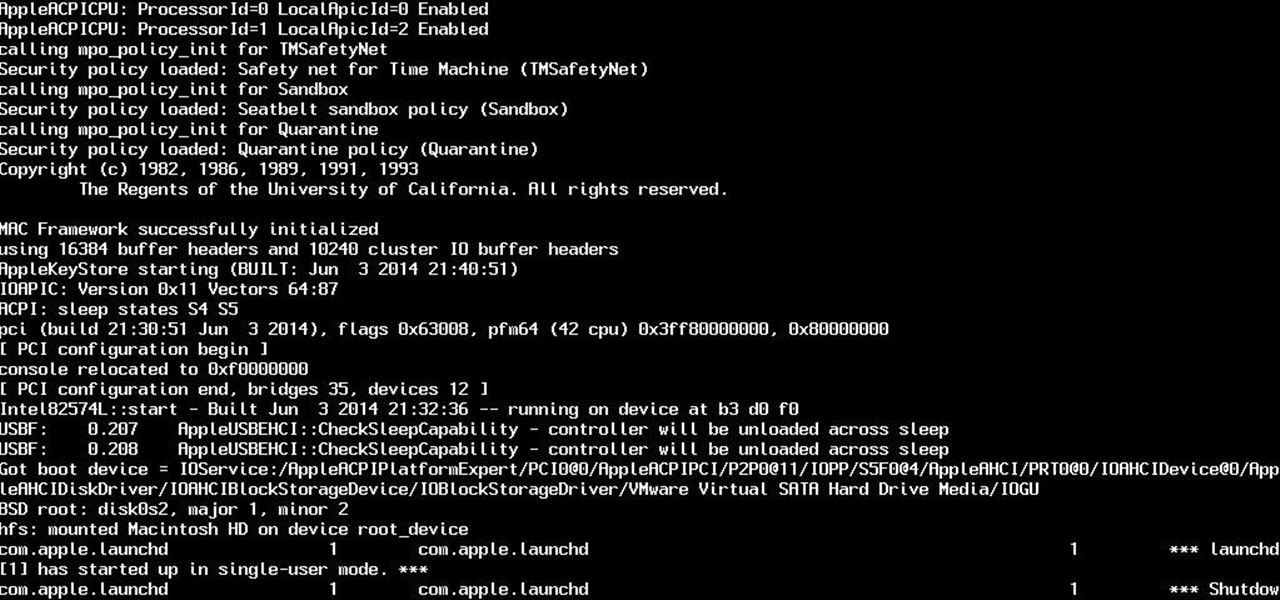
So yeah. Its AugustFackYou and I felt like posting today and being an active member of the community. After reading this please tell me if you have any comments on what I can do better or if this method is bad. Anyway today I will be showing you how to get root on a mac. I managed to become an administrator at my school with this and one other method.

Welcome back, my tenderfoot hackers! Recently, Microsoft released a new patch (September 8, 2015) to close another vulnerability in their Windows Vista, 7, 8, and 8.1 operating systems. The vulnerability in question (MS15-100) enabled an attacker to gain remote access to any of these systems using a well-crafted Media Center link (MCL) file.

Hello Elite Hackers! Welcome to my 3rd Post, which explains how to hack any account like G-mail, Facebook, etc.
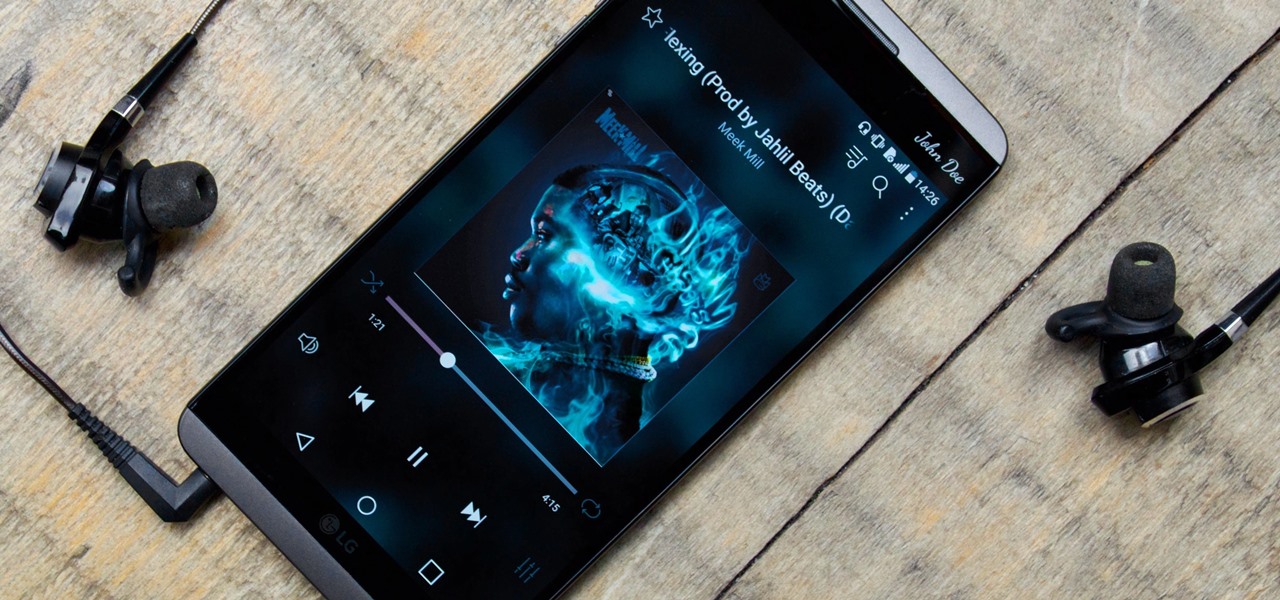
While music may not technically be a "universe language," it is the one language listened to by all. There are over 1,500 music genres today—rap, classical, rock, jazz, trap, hip-hop, house, new wave, vaperwave, charred death, nintendocore... and the list goes on. And if you're like most people, you now probably listen to the majority of your music on your phone.

In this series of instructional music videos you'll learn how to play the blues piano in the key of D Flat (Db). Expert Ryan Larson shows you his special 12 key method to help you understand the techniques used by blues musicians through the ages, including the music theory behind 12 chord blues song structure, walking bass & rhythm lines, as well as 7th chords.

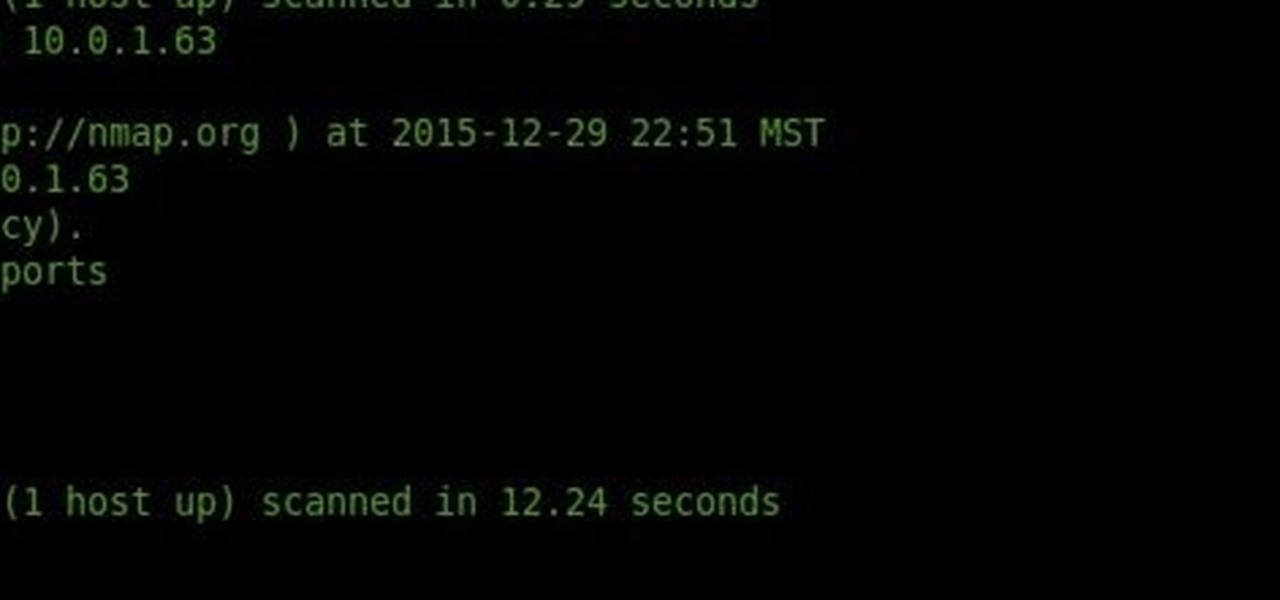
Nmap is possibly the most widely used security scanner of its kind, in part because of its appearances in films such as The Matrix Reloaded and Live Free or Die Hard. Still, most of Nmap's best features are under-appreciated by hackers and pentesters, one of which will improve one's abilities to quickly identify exploits and vulnerabilities when scanning servers.

Welcome back, my hacker novitiates! Often, to hack a website, we need to connect to and exploit a particular object within said website. It might be an admin panel or a subdirectory that is vulnerable to attack. The key, of course, is to find these objects, as they may be hidden.