New weapons are needed to combat antibiotic-resistant bacteria. Instead of drugs, scientists have discovered in an animal study that they may be able to harness vampire bacteria to vanquish pneumonia.

Practically every smartphone comes with a built-in camera app, but these apps are generally created by the device's manufacturer. And let's face it, manufacturers are hardware companies first and foremost, so they don't always produce the best software.

If your Android device wasn't manufactured by Samsung, chances are it uses on-screen navigation buttons. Colloquially referred to as "Soft keys," these have become commonplace due to their flexibility, as well as the fact that manufacturers don't have to include extra hardware buttons with a propensity to fail.
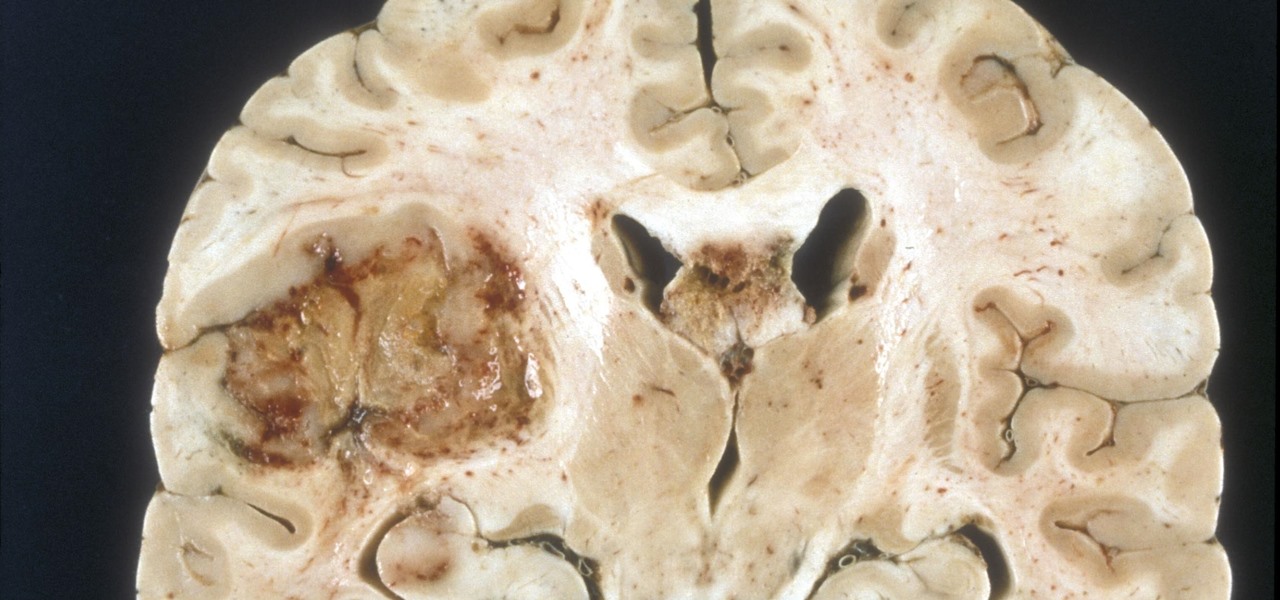
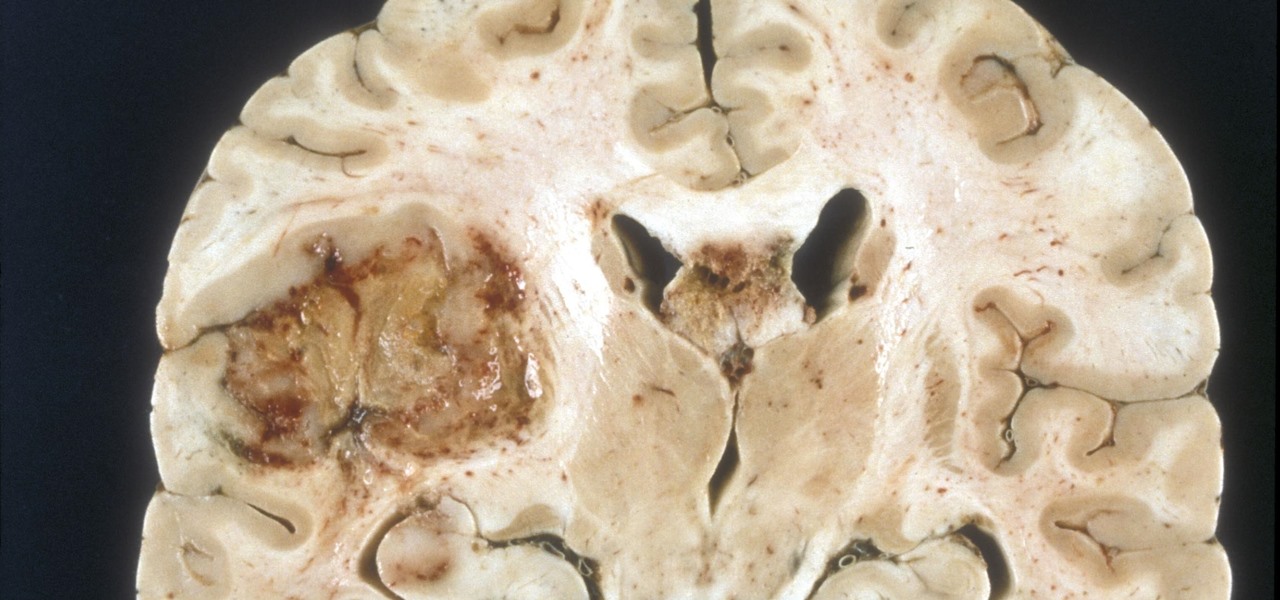
A deadly type of brain tumor and Zika-related brain damage in developing fetuses are devastating brain conditions that, at first glance, may seem unrelated. However, thanks to new research, their paths seem to cross in a way that could benefit patients. A new study has shown that Zika kills brain cancer stem cells, the kind of cells most resistant to treatment in patients with glioblastoma, a deadly brain tumor diagnosed in about 12,000 people in the US each year.

An average user's smartphone tinkering doesn't go much further than taking their phones out of the box, signing into their account, and installing apps. But some of us want more functionality and customizability than the basic experience provided by Android and iOS.

In this day and age, maintaining your privacy is a perpetual battle, and doing so with an internet-connected device like your smartphone is even more of a struggle. Every website you visit, every app you install, every message you send, and every call you make is a potential vulnerability that could expose you to prying eyes.

Though many students spend four years of high school learning a foreign language, most of us probably retained very little. Chalk it up to the carelessness of youth, but chances are you've since been in situations or places that left you wishing you paid more attention in class or had continued practicing long after you graduated.

Cold brewing tea and coffee are all the rage, and for good reason: they're idiot-proof. I, personally, am a total dunce at brewing coffee. It either ends up strong enough to peel paint from a car or so weak that you can see through it. Meanwhile, I have friends who inevitably brew green tea to the point where it's painful to drink it.

Electronic warfare tactics work by jamming, disrupting, or disabling the technology a target uses to perform a critical function, and IoT devices are especially vulnerable to attacks. Wireless security cameras like the Nest Cam are frequently used to secure critical locations, but a hacker can surgically disable a webcam or other Wi-Fi connected device without disturbing the rest of the network.

Canvas fingerprinting is the web's trickiest privacy threat, but it's not impossible to stop. With all the media attention it's gotten lately, it's time we lay out exactly how to detect and prevent this invasive tracking technique.

With warm weather comes bugs, and with bugs come bites, and with bites come itches. From ticks and spiders to mosquitoes and bees, insect bites come in sundry shapes and sizes, but they all commonly pull an itchy, red reaction out of our bodies.

Smartphones are more like computers than actual telephones. Unfortunately, thieves, hackers, and other bad actors know this and are always looking to make money off your personal data. Thankfully, your Galaxy S20, S20+, or S20 Ultra has tools to combat these threats — as long as you know where to look.

When joining a new network, computers use the Address Resolution Protocol to discover the MAC address of other devices on the same network. A hacker can take advantage of ARP messages to silently discover the MAC and IP address of network devices or actively scan the network with spoofed ARP requests.

If maintaining privacy is an ongoing battle, the front line is your smartphone. Apple included several new security features in iOS 10, but at the same time, some of the best new functionality comes with potential privacy trade-offs that everyone needs to understand.

It hasn't been long since Apple released iOS 16.0 with over 350 new features, but iOS 16.1 just came out with even more cool updates for your iPhone. While some of the recent upgrades were expected, others are somewhat surprising — and there's even one that you may not even think was possible.

Once you've installed Ubuntu with security in mind and reduced the possibility of network attacks on your system, you can start thinking about security on an application level. If a malicious file is opened on your system, will an attacker be able to access every file on the computer? The chances are much slimmer if you put the proper defenses in place.

In this video tutorial, viewers learn how to install and use Ad Block Plus in Mozilla Firefox. Begin by clicking on Tools and select Add-on. Then click on Get Add on and search for the extension in the search box. Now install the add on and restart the browser. Users will be able to selectively block out text ads or even just elements of web page that is not wanted to be seen. This video will benefit those viewers who use the Mozilla Firefox web browser, and would like to learn how to install...

In this Microsoft Outlook video tutorial, learn how to use Microsoft Outlook from systems administrator and MS Outlook expert Gary Zier. Gary will teach you Microsoft Outlook techniques such as how to permanently delete items in MS Outlook, how to selectively send read receipts in Outlook, how to prevent multiple prefixes in emails, how to create and save searches in Microsoft Outlook, how to configure the desktop alert in Outlook, how to print select pages from an email, and how to create cu...

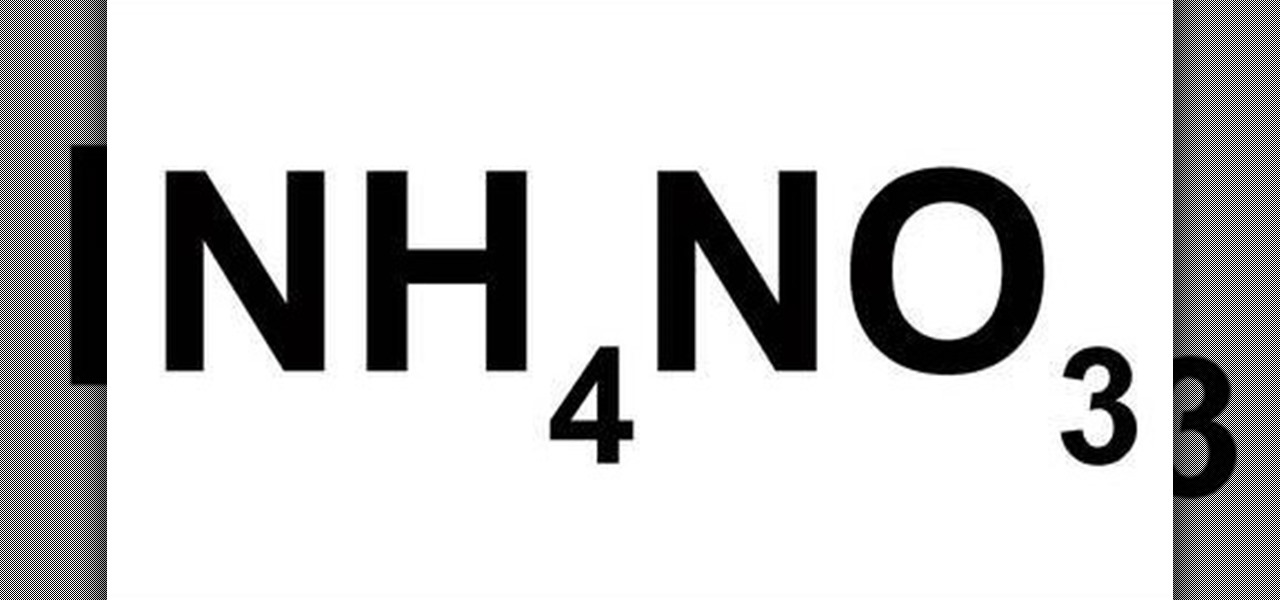
OK, so you don't necessarily have to make ammonium nitrate to have ammonium nitrate — ammonium nitrate can simply be obtained from fertilizers and instant cold packs. Making homemade NH4NO3 can be much more expensive then buying it, but this method is not meant to be a viable route, it's an exploration of science and chemistry.

In this Photoshop tutorial you will see how to use layer masks to selectively blend the results from FocalPoint with your original image. FocalPoint 1.0 is a plug-in for Photoshop and has it's own layer masks that allow you to choose a focal point and blur around it with the layer masks. See how to use these layer masks within Photoshop and the FocalPoint plug-in. Work with layer masks in FocalPoint Photoshop plugin.

This PhotoTools tutorial will teach you how to use presets in your studio to automate frequently used effects. See how to create presets for senior portraits in the PhotoTools plug-in for Photoshop. You will also learn how to selectively paint in a PhotoTools effect on senior portraits brought into Photoshop. Retouch senior portraits in PhotoTools for Photoshop.
NBC News has fired the producer it deemed most responsible for the airing of a selectively edited 911 call placed by George Zimmerman the night he killed Trayvon Martin.

The newest fuel alternative on the horizon? Pee. U.S. researchers have been experimenting with using urine as a method of producing hydrogen. Not only could this virtually free and readily available resource possibly power automobiles, but it could also aid in the clean up of municipal wastewater.

Google recently unveiled the start of their new social network Google+, which is set to compete with Facebook and fix the awkward, broken aspects on online sharing they claim exist. It's currently only open to a limited number of Googlers during its "field trial," and if you weren't one of the lucky ones given an invitation, you can still sign up to be notified when Google+ is available in your area. You can also stay up to date on its Twitter page, GooglePlus.

XSS stands for cross-site scripting, which is a form of web-based exploitation that uses client-side vulnerabilities in a web page to execute malicious JavaScript codes. JavaScript is referred to as "cross-site" because it usually involves an external website containing the malicious code. That code is most commonly used to steal cookies with a website that the attacker created and hosted on another server. The cookies can then be used to escalate privileges and gain root access to someone's ...

There are a few different types of Apple iPhone and iPad users: general household users who largely consume media—e.g. surfing the web, watching movies, listening to music. Other iPhone and iPad owners use their device(s) to produce stuff—written documents, edited movies, blog posts, music tracks, and the like. And then there are those who are very mobile with their devices. They commute to and from work on a regular basis with their iPhone or iPad. Some users may travel a lot on business, or...

With so many wireless iOS networking apps for the iPhone, iPad, and iPod touch available, there’s very little reason to connect any of these devices to iTunes, except to update the software. Besides, importing and exporting photos using iTunes has never been one of the best features of Apple‘s mobile device process. Let me introduce you to 5 useful apps for importing and exporting photos to and from your iOS device(s).

For our final part of recognizing crowd control, we shall look at the mind. It's the most complicated thing in the universe, but also the most easily influenced. What makes us to gullible? What methods to commercials, companies and the media use to influence our position on things? These are just a few of the questions we will answer.

Everybody has them. You can say you don't, but it's probably a lie. There's at least one person on your mobile phone that you never, ever want to pick up the phone for. When they call, you cringe and immediately hit the silent button. They're annoying. Overbearing. You hate them, but yet you love them enough to not delete them entirely from your contact list. Maybe if they called just once a week, but once a day is just too much for you to handle. What do you do?

This week, Apple announced the beta version of its new wireless, cloud-based service, iCloud. I wrote a summary of it here. The iCloud service includes some new features in the latest version of the iTunes Store, which allows you to access all your iTunes songs, mobile apps, and eBooks purchased in their respective iTunes stores and download that media to up to 10 of your devices—your iTunes supported Macs and PCs and mobile devices. This downloading can all be done wirelessly without you hav...

Thanks to the advent of smartphones and mobile apps, Scrabble has spread like wildfire across the globe, whether it be Scrabble or one of its many popular word game spinoffs, such as Words with Friends, WordWise and Kalimat.