Have a file or a number of files too sensitive to be stored on your desktop hard drive? Thwart would-be snoopers with an encrypted USB flash drive. This free video tutorial from the folks at CNET TV will show you everything you'll need to know to create your own password-protected thumb drive directories.

Password protect your files and folders in Mac OS X. This free video tutorial from CNET TV will show you how. Thwart would-be snoopers with this home cryptography guide, which presents easy-to-follow, step-by-step instructions on how to protect your privacy by encrypting your sensitive data.

Password protect your files and folders in Microsoft Windows XP or Vista. This free video tutorial from CNET TV will show you how. Thwart would-be snoopers with this home cryptography guide, which presents easy-to-follow, step-by-step instructions on how to protect your privacy by encrypting your sensitive data.

There are 10 major ways to protect your PC. Disable Autorun, in Windows. Make sure that your system is up to date, by setting automatic updates. Always use a log on for your computer that does not have administrative privileges. Use different passwords, and change your passwords on a regular basis. Don't use simple passwords. Be careful of using links sent to you via email. Never disclose your sensitive information in public forums: e.g. social networks. Encrypt sensitive data on your compute...

This video speaks about removing sensitive information in Adobe Acrobat 9. The viewer might get a very obvious idea of removing sensitive information by redaction. Redaction is the process of permanently removing sensitive information from a PDF file. This is done by opening the Advanced menu, clicking "Redaction" and then clicking "Show redaction tools", which can be in any format, images or text. The viewers will definitely get a clear idea of removing such sensitive information by redactio...
When you need a website to showcase your product or service, it can be quite confusing. Follow these easy steps to gather everything you need to have a successful website. Start your search for a domain name in the domain name registrar. (Example: www.companyname.com) Rent space from a hosting company to hold the files for your website. Set up an email account for your company. Create the content for your website (example: products, prices, services, etc). Get internet security to protect sen...

Data thieves don't have to be programming wizards to get their hands on your personal information. They often find hard drives that contain financial and other sensitive data at flea markets, charity shops, the city dump—even on eBay. In this video tutorial, PC World explains how to completely erase sensitive data from old drives before recycling or discarding them. Wipe your old hard drives with this how-to.

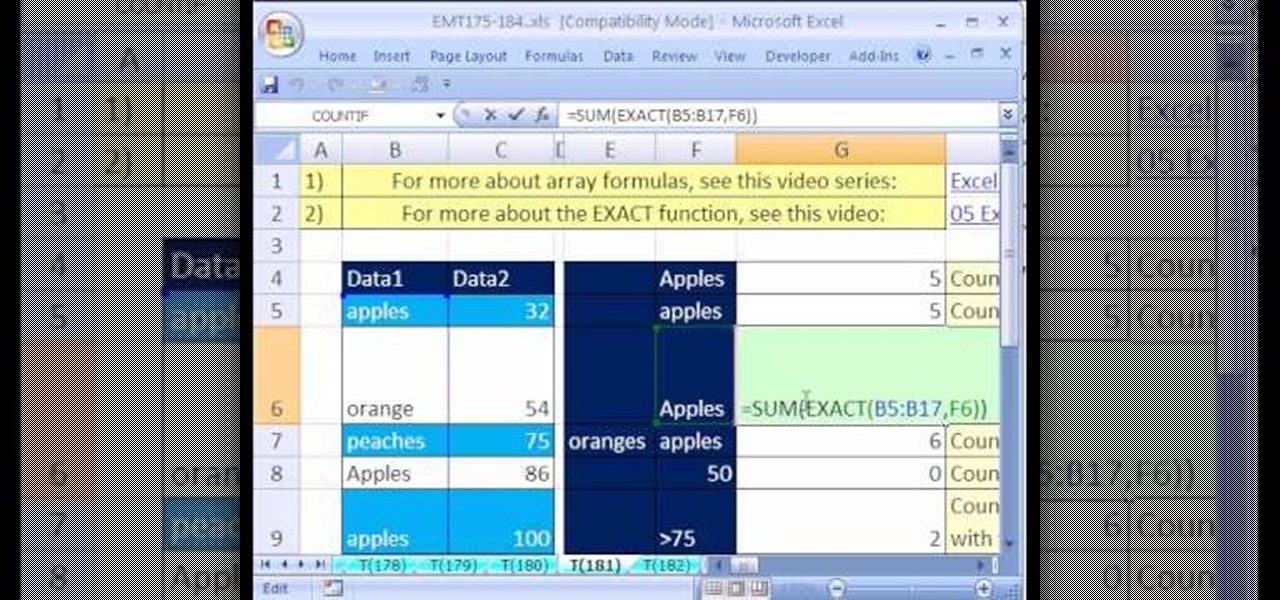
New to Microsoft Excel? Looking for a tip? How about a tip so mind-blowingly useful as to qualify as a magic trick? You're in luck. In this MS Excel tutorial from ExcelIsFun, the 181st installment in their series of digital spreadsheet magic tricks, you'll learn how to count words (case sensitive) using the SUM and EXACT functions in an array formula.

TrueCrypt is a free application that lets you encrypt designated programs on your Ubuntu system to prevent unwanted access. Provided you select a strong password, intruders will not be able to open your personal files and documents. This instructional video walks you through the process of installing TrueCrypt on your Ubuntu operated machine and demonstrates an example on how to create an encrypted volume within a select partition.

Watch Bill Myers show you an easy way to quickly hide sensitive screen capture text or images using Camtasia Studio.

If you're concerned about someone accessing your OneDrive files, you may want to upgrade your protection by enabling fingerprint or Face ID unlocking. Your sensitive information deserves to be protected, and now you can do so easily. Worry no longer — if you need to let someone else use your phone, with a password-protected OneDrive, sneaky file grabbers will be out of luck.

When BlackBerry made the move to Android OS, they were aware of the limitations it presented. Unlike with BB10, they didn't create the operating system and would have to deal with the vulnerabilities already included. As a result, they added numerous security enhancements, and at the heart of this is DTEK.

Reading people's minds is something that most inquisitive and sensitive people have wished that they could do at some point. Well, what if you could? This video will show you a great multipurpose bar trick that will allow you to appear to read the mind or body of people in a variety of situations. It's really remarkable how easy this is and how well it works.

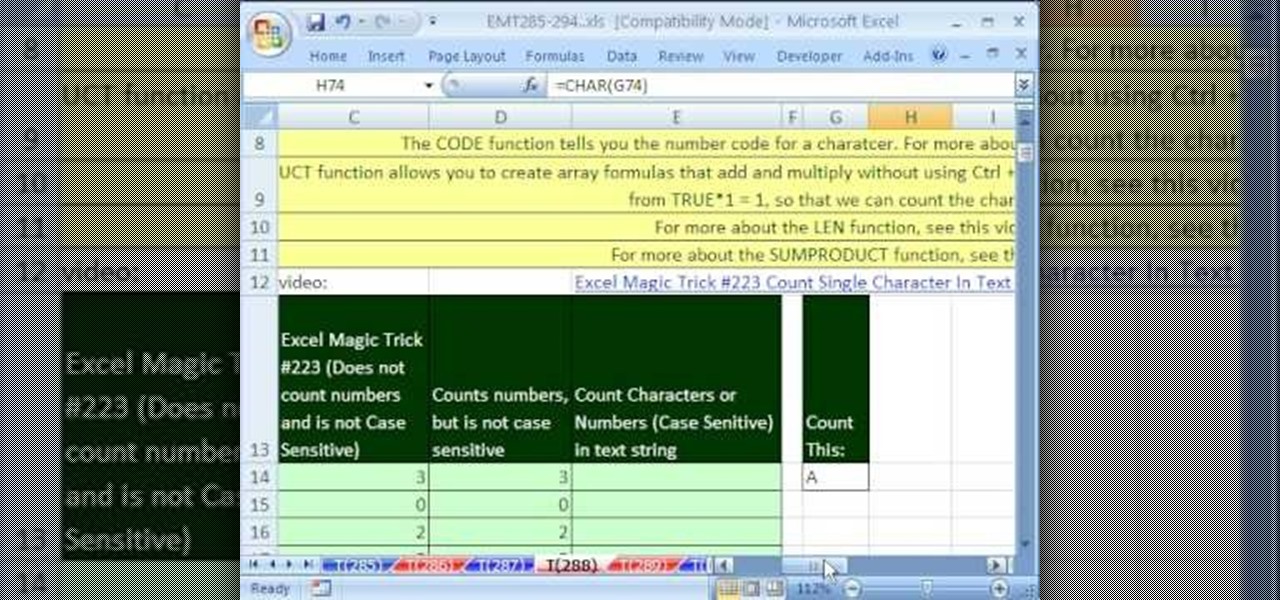
New to Microsoft Excel? Looking for a tip? How about a tip so mind-blowingly useful as to qualify as a magic trick? You're in luck. In this MS Excel tutorial from ExcelIsFun, the 288th installment in their series of digital spreadsheet magic tricks, you'll learn how to count the number of characters or numbers in a text string with a formula that is case sensitive.

Any electronic equipment is bound to accumulate dust, slight moisture, dirt or any combination of the above on its sensitive parts over time. The delicate nature of items also means further care is required.

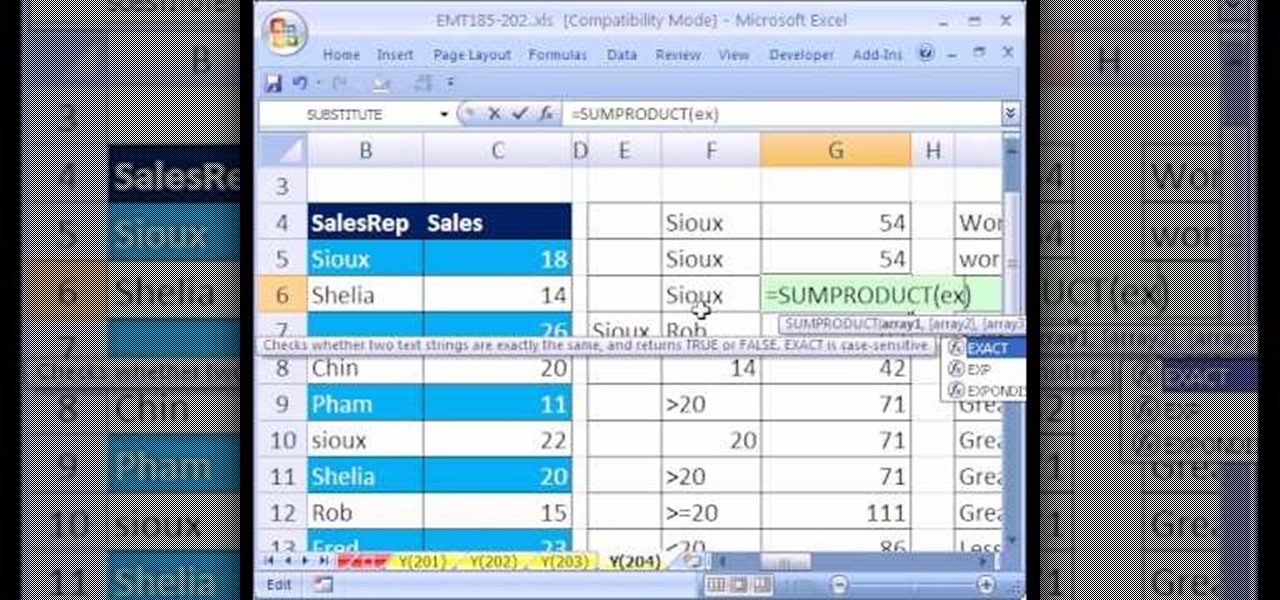
New to Microsoft Excel? Looking for a tip? How about a tip so mind-blowingly useful as to qualify as a magic trick? You're in luck. In this MS Excel tutorial from ExcelIsFun, the 204th installment in their series of digital spreadsheet magic tricks, you'll learn how to use the SUMPRODUCT and EXACT functions in an array formula to add the sales for a sales representative where lower and upper letters matter (i.e., are case sensitive) in the criteria (conditions).

This video shows how to use a special tool to redact or remove sensitive information from Adobe Acrobat 9. This includes hidden metadata, file attachments, comments, hidden text and layer elements within a PDF file. You can also set it up when you're emailing. The Examine Document function highlights information that you may want to remove. You can then select the different types of data and choose which things you want to remove.

When the climate changes, so do all the things that rely on the climate, including people, plants, and pathogens. A European study recently took a broad look at what kind of microorganisms are most likely to be affected as climate change heats, cools, dries, and wets the world around us.

Adding to the recent recent slew of bugs and issues within iOS 7, it now seems that emails sent with attachments are not encrypted, despite Apple's claims that they are.

We share links on an almost daily basis, usually not even thinking twice about it. Whether you're sending a funny cat video to your sister, or letting your coworker know where to go to download relevant files, there are plenty of reasons you might be giving someone a URL.

You keep all kinds of important and sensitive information and data on your computer, and if your hard drives crashes, you're done for… unless you've backed it up. CNET has some "Insider Secrets" on how you can backup your system with an external hard drive, network-attached storage, and online services.

If your iPod is broken, don't worry! In this tutorial, learn how to remove and replace the screen on your iPod Touch so that it looks brand new again. This fix will not destroy your iPod if you do it properly and will still function as a heat sensitive touchscreen. Follow along and be careful!

Cooking Light food editors show you what to do -- and what not to do -- to create the perfect caramel. There are certain do's and don'ts to making caramel. It involves sensitive heat and making sure not to burn the sugar.

Like the crab that symbolizes them, Cancers can be a little soft-shelled at times, so woo these sensitive souls cautiously. Learn how to use astrology advice in dating, by watching this how-to dating video. Pick up tips on making a relationship with a Cancer work. Here a hint, do something nice for a Cancer when you suggest an activity for the both of you to do.

With all the web applications out on the internet today, and especially the ones built and configured by novices, it's easy to find vulnerabilities. Some are more perilous than others, but the consequences of even the slightest breach can be tremendous in the hands of a skilled hacker. Directory traversal is a relatively simple attack but can be used to expose sensitive information on a server.

Malware attacks on mobile phones are reaching an all-time high and it looks like companies like Samsung are doing all that they can to prevent any unwanted hackers from accessing its sensitive user data.

The Nessus vulnerability scanner, is the world-leader in active scanners, featuring high speed discovery, configuration auditing, asset profiling, sensitive data discovery and vulnerability analysis of your security posture. Nessus scanners can be distributed throughout an entire enterprise, inside DMZs, and across physically separate networks. In this network security video tutorial, you'll learn how to hack a network using Nessus 3.

Have sensitive data that you want to make sure you securely delete? Or maybe you're getting an external drive ready to recycle or to give to a colleague. In this video tutorial, you'll find instructions for securely emptying your trash and also securely delete the contents of an external hard drive. For more, and to learn how to remove data from your Mac computer securely, watch this video tutorial from Apple.

Onion water makes invisible ink. The drawing becomes visible when it is heated. Use this as inspiration for one of your April Fools Day pranks!

Open up your mobile phone and solder on a light sensing resistor to make an alarm go off when the phone is in the light. Possible uses?

If you had to answer the following statement, which answer would you choose? Water is:

Eczema sucks. It's a skin condition characterized by dryness, redness, and itching. Often this dryness leads to patches of dry skin that, if bothered excessively, can lead to pus. Those who suffer from eczema have extremely sensitive skin that needs to be treated professionally.

Baby hair can usually be extra fine, and baby skin is also sensitive to harsh shampoo. Detangling can also be a challenging. This tutorial shows you how to take care of your child's hair, and still let them express themselves.

Bathing a baby means not only keeping them clean, but also taking care of their skin. This video shows you how to keep your child's skin soft and well moisturized. Make sure your baby doesn't continually suffer from dry skin, and always moisturize after a bath.

Need a hand figuring out how to care for the sensitive skin of an infant? This video guide from Health Guru will teach you everything you'll need to know. For all of the details, watch this video guide for new parents.

If you have a friend or loved one with bad breath, handling the situation in a sensitive way is crucial to solving the problem and saving your relationship. This video will give you good ideas for having that conversation successfully and nicely.

Giving advice to a friend in a problem relationship in a sensitive, effective fashion is hard. If you are looking for some tips on how to do so, watch this video. It is loaded with ideas for having insightful, helpful relationship talks.

Looking for an easy way to make certain that your sensitive personal information is secure? With Identity Finder, it's easy! So easy, in fact, that this home-computing how-to from the folks at TekZilla can present a complete overview of the process in just over three minutes. For more information, including step-by-step instructions, take a look.

Without washing your makeup brushes, you're just spreading dirt and bacteria, aggravating your skin, and causing makeup to look worse than it should. This how-to video offers some tips for getting those brushes clean. Good brushes are very sensitive, so they require special handling. Learn how to clean makeup brushes by watching this video makeup lesson.

Here is a demonstration of a custom designed brush for the TVPaint software. This pen is sensitive to a realistic method of gestural drawing. Watch this instructional video to use this software brush to make several types of digital drawing strokes.