Sharing your Wi-Fi password is like giving an unlimited pass to snoop around your network, allowing direct access even to LAN-connected devices like printers, routers, and security cameras. Most networks allow users to scan and attempt to log in to these connected devices. And if you haven't changed the default password on these devices, an attacker can simply try plugging them in.
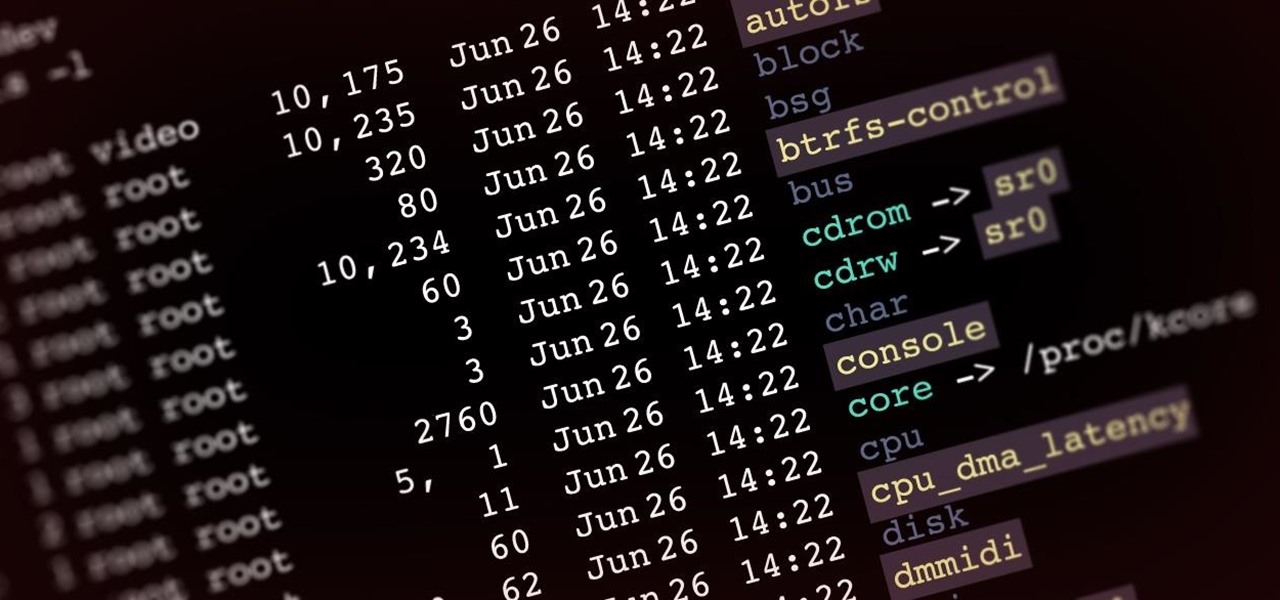
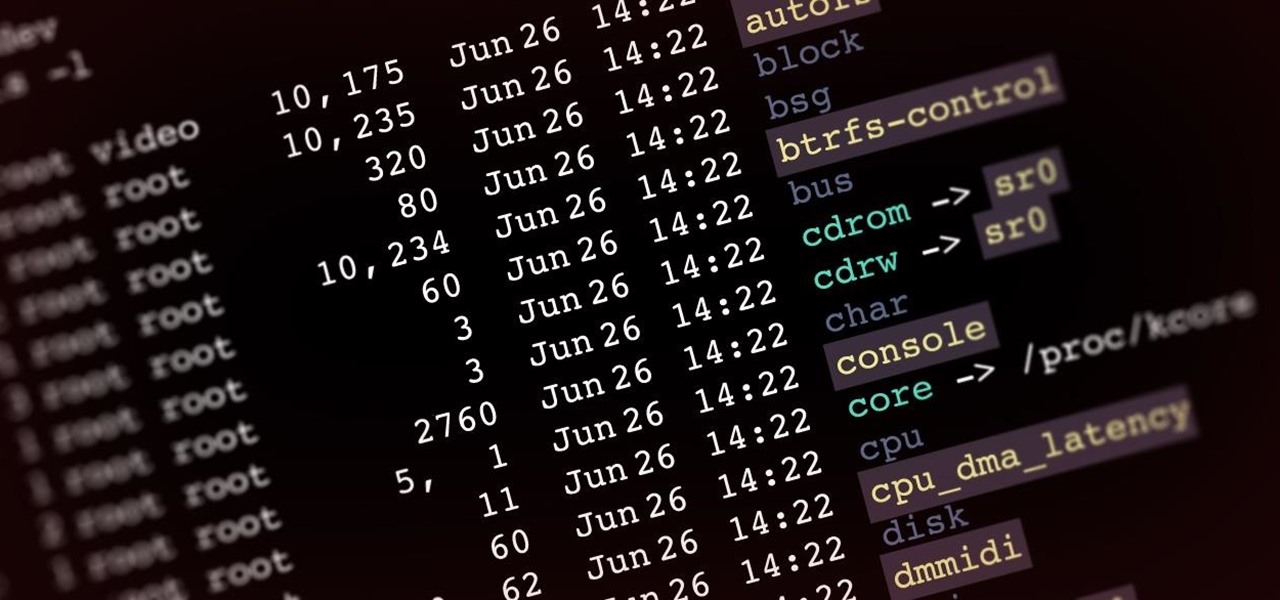
Welcome back, my aspiring hackers! In recent tutorials, I have made reference to the name and location of the Linux devices in the file system, such as sda (first SATA or SCSI drive). Specifically, I have mentioned the way that Linux designates hard drives when making an image of a hard drive for forensic purposes.

There's something special about Laika Inc.'s Paranorman... Hey! Did you love Coraline? Are you interested at all in stop-motion animation? Well, watch this feature on Laika Inc.’s new film, Paranorman.
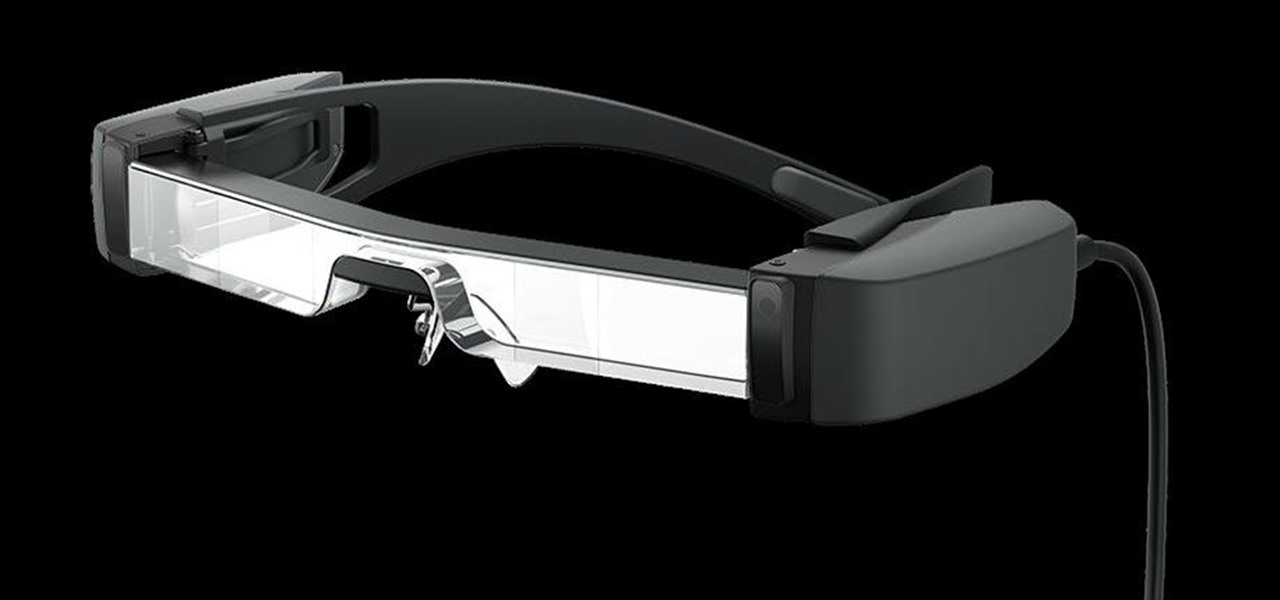
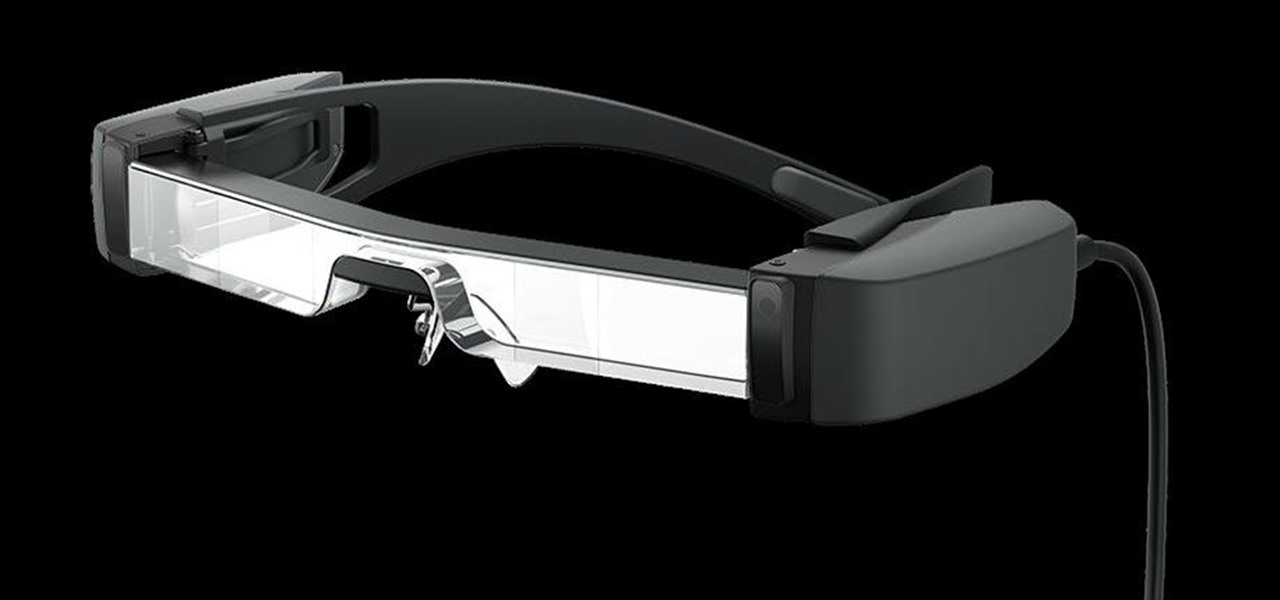
The average business person likely recognizes Epson for its printers or even its projectors, not the futuristic AR wearables.

Search engines index websites on the web so you can find them more efficiently, and the same is true for internet-connected devices. Shodan indexes devices like webcams, printers, and even industrial controls into one easy-to-search database, giving hackers access to vulnerable devices online across the globe. And you can search its database via its website or command-line library.

Before attacking any website, a hacker or penetration tester will first compile a list of target surfaces. After they've used some good recon and found the right places to point their scope at, they'll use a web server scanning tool such as Nikto for hunting down vulnerabilities that could be potential attack vectors.

Electronic warfare tactics work by jamming, disrupting, or disabling the technology a target uses to perform a critical function, and IoT devices are especially vulnerable to attacks. Wireless security cameras like the Nest Cam are frequently used to secure critical locations, but a hacker can surgically disable a webcam or other Wi-Fi connected device without disturbing the rest of the network.

In October of 2017, Mathy Vanhoef released "Key Reinstallation Attacks: Forcing Nonce Reuse in WPA2." This paper demonstrates a way to decrypt traffic on practically any WPA2 network, the most commonly used form of wireless security (seeing as all other forms of Wi-Fi encryption have already been broken). Practically all of the network-connected devices we use will need to be updated in some way in order to protect against this vulnerability, each of them in a different way.

Walsh, a new community under construction on 7,200 acres of former ranch land near Fort Worth, Texas, will one day contain 15,000 homes.

Hello ladies and gentlemen, PySec here coming at you with another informative(hopefully) article for you all. In the last tutorial, we finally finished our discussion about IP Addressing and I intentionally didn't mention a really important concept with which IP Addressing wouldn't be feasible without it. What I'm talking about is how our network device gets the IP Address in order to communicate with other devices on the network/Internet. There are many different ways for that to be accompli...

One of Android's biggest strengths, when compared to other mobile operating systems is its open file structure. Google introduced a built-in file manager with Marshmallow that provides basic file management, but like with most apps on Android, there are alternatives. Third-party file managers are readily available, providing deeper access and control of all your files.

You may be familiar with image-based or audio-based steganography, the art of hiding messages or code inside of pictures, but that's not the only way to conceal secret communications. With zero-width characters, we can use text-based steganography to stash hidden information inside of plain text, and we can even figure out who's leaking documents online.

The Windows 10 desktop and microphone can be livestreamed without using Remote Desktop Protocol (RDP) software and without opening any ports on the target computer. A hacker with low user privileges can monitor and exfiltrate a target's every move and private conversation in real time no matter where they are. Hackers are watching and listening, and there are few ways to protect yourself.

If you've grown bored of day-to-day hacking and need a new toy to experiment with, we've compiled a list of gadgets to help you take password cracking and wireless hacking to the next level. If you're not a white hat or pentester yourself but have one to shop for, whether for a birthday, Christmas present, or other gift-giving reason, these also make great gift ideas.

Wi-Fi devices are continually emitting "probe frames," calling out for nearby Wi-Fi networks to connect to. Beyond being a privacy risk, probe frames can also be used to track or take over the data connection of nearby devices. We'll explain how to see nearby devices emitting probe frames using Probequest and what can be done with this information.

Your home has walls for privacy, but Wi-Fi signals passing through them and can be detected up to a mile away with a directional Wi-Fi antenna and a direct line of sight. An amazing amount of information can be learned from this data, including when residents come and go, the manufacturer of all nearby wireless devices, and what on the network is in use at any given time.

NOTICE: Ciuffy will be answering questions related to my articles on my behalf as I am very busy. Hope You Have Fun !!!

Microsoft believes its Mesh platform can help developers build immersive AR apps more easily. We spoke with a member of the Microsoft team to learn more about the platform.

In this simple video tutorial, you'll be learning how to change a label's font and text style using the Brother P-Touch Editor software (this applies to higher-end P-Touch Labellers and the QL series of label printers).

Take a look at this instructional video and learn how to build your own miniature computer numerical control (CNC) machine. A CNC machine acts as a controller that reads G Code instructions for machine tools such as drills and printers. To perform this task, you'll need some geared motors you can find in old analog camcorders with optical zoom.

See how you can make your mouse cursor leave a trail behind it. First, go to "Start" and then "Control Panel". Then go to "Printers" and "Other Hardware" and then "Mouse". A new window should pop up and you should go click on the "Pointer Options" and then select the length of the trail you want your cursor to leave behind. It's easy to set your mouse cursor to leave a trail on your computer screen.

In this tutorial, AJ Wood shows you how to use InDesign CS4 to design a photobook that can be exported in JPEG format and sent to the printers.

Is your love of race cars exceeded only by your love of elaborate papercraft? Do you have easy access to industrial-size printers and a surfeit of clean cardboard? If you answered yes to all of the above, odds are you're the Seiko Epson printer corporation, who recently set about assembling an impressive 1:1-scale 3D cardboard replica of a Honda/Acura NSX Super GT race car for the 2010 Tokyo Auto Salon:

Bakerella offers a trove of fun recipes for dessert-on-a-stick. Cupcakes, cakes, pies, cookies, even macaroons, all bite-size, all lollipop-style. My favorites below.

In this Illustrator CS2 video tutorial you will learn to use PMS Colours. Learn how to open and choose swatches from a PMS color set. PMS is a worldwide color matching system for printers. Make sure to hit "play tutorial" in the top left corner of the video to start the video. There is no sound, so you'll need to watch the pop-up directions. Use PMS Colours in Illustrator CS2.

It’s that time of year (in the U.S. anyway) when people are focused on getting organized -- or rather wishing they were organized. Being organized is great, it affords physical space, mental space and all but insures higher efficiency. But wishing and doing are two entirely different things. Wondering how to achieve the bliss of knowing where your stuff is? It’s easy... if you start small and don’t waste your valuable time watching TV shows or reading magazine articles on “how to” do it.

Before you start snapping away and submitting your photos, please take some time to read the official rules below!

Giveaway Tuesdays has officially ended! But don't sweat it, WonderHowTo has another World that's taken its place. Every Tuesday, Phone Snap! invites you to show off your cell phone photography skills.