Organizations Search Results

Recon: How to Research a Person or Organization Using the Operative Framework
The Operative Framework is a powerful Python-based open-source intelligence (OSINT) tool that can be used to find domains registered by the same email address, as well as many other investigative functions. This reconnaissance tool provides insight about your target through examining relationships in the domains they own.

How To: Become a Master Sommelier
The Court of Master Sommeliers is one of the most exclusive organizations on Earth, having only inducted 158 Masters since it's inception in 1969. They are the kings of the wine-tasting world, and their wine knowledge and tasting abilities are unmatched. Does being an internationally recognized wine snob sound good to you? It does to us. This video features Master Sommelier Cameron Douglas giving a talk at Google about his life and how he came to be where he is, offering many tips and lessons...

How To: Circumvent an internet proxy or browser filters
Some governments and organizations employ proxy servers to filter web content, permitting access to some web sites while blocking others. Here are several ways to get around these censorship policies. This is employed in China with YouTube and many other voices of anti-goverment ideas.

How To: Walkthrough SEGA's Alpha Protocol on the Xbox 360
Find out how you can kick butt in Obsidian Entertainment and SEGA's video game Alpha Protocol. The RPG and action hybrid came out on June 1st, 2010, and is available on the PlayStation 3 (PS3), Microsoft Windows (PC), and the Xbox 360. This video game walkthrough series from Mahalo focuses on Alpha Protocol for the Xbox 360.

How To: Become a professional Call of Duty gamer
Let's face it, pro gamers make a ton of money, and that money is only increasing every year. If you're fairly good at Call of Duty: Black Ops and want to try your hand at the tournament scene, find out how to connect with other professional gamers and organizations and land become a pro Call of Duty player.

How To: Fight with a sword and shield according to the SCA rules
Just starting to get into the Society for Creative Anachronism? This tutorial shows you some basic footwork and few useful strategies when you're fighting with just a basic buckler (punch shield) and a sword. Though aimed at the SCA, this tutorial will work for anyone into theatre combat, boffer larps or other reenactment organizations.
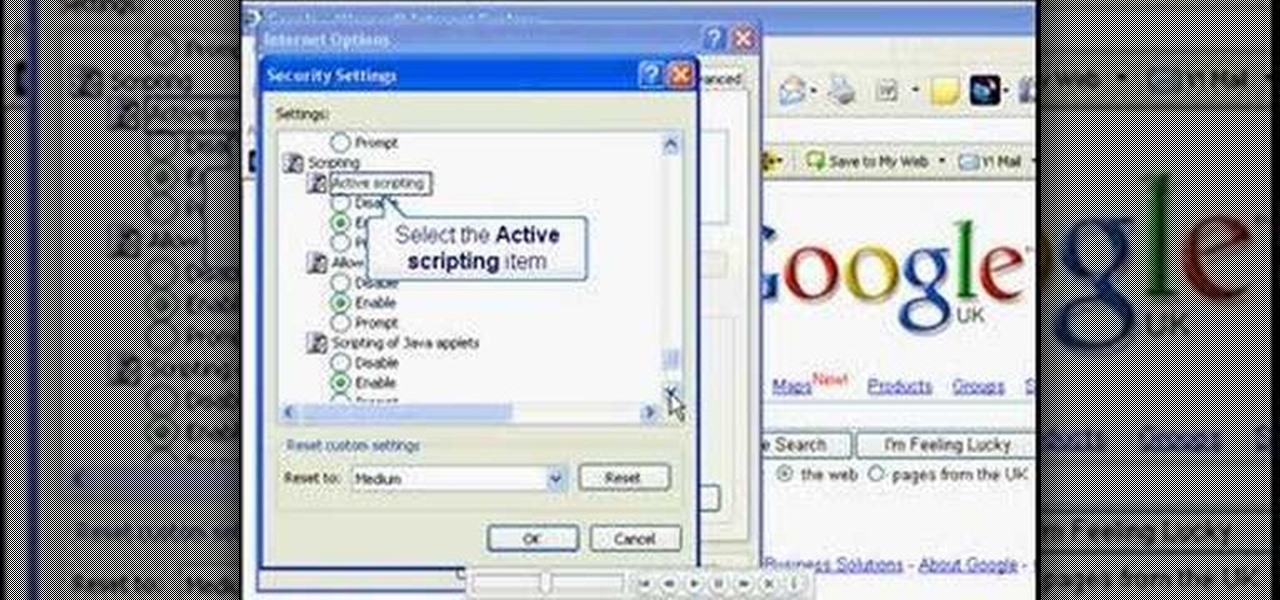
How To: Turn JavaScript on in Internet Explorer
In this video, you will learn the steps to take to enable JavaScript in Microsoft's Internet Explorer (IE) web browser. Although JavaScript support is typically enabled by default in most modern browsers and many web applications depend on JavaScript being enabled to function properly, some persons and organizations may occasionally disable JavaScript to negate the effects of annoying or insecure implementation of JavaScripts on some web pages (such as pop-ups, hidden tracking links, unwanted...

How To: Pronounce the English word "hierarchy"
Today's word is "hierarchy". This is a noun which means a system of people, organizations, or things that have ranks.

How To: Use Maltego to Fingerprint an Entire Network Using Only a Domain Name
Hackers rely on good data to be able to pull off an attack, and reconnaissance is the stage of the hack in which they must learn as much as they can to devise a plan of action. Technical details are a critical component of this picture, and with OSINT tools like Maltego, a single domain name is everything you need to fingerprint the tech details of an organization from IP address to AS number.

How To: Meet men if you're over 60
You are never too old to meet a mate! Never! In this video, learn some great tips on how to socialize your life to meet men when over 60.

How To: Break a lease
Breaking a lease is almost always considered a legal breach of contract, even if a tenant has a good excuse. Here are some exceptions to the rule

How To: Officiate at your friend’s wedding
Your friends want you to marry them! Before you can officiate their big day, you'll need to jump through some legal hoops. Learn how to officiate at a wedding.

How To: Use LinkedIn to find a new job
Step1. Determine the type of job you want. Make sure that you have a detailed and complete profile on ‘linkedin’. You must also have a number of connections. Then decide which job you are looking for and the typical functions and titles. Also choose which type of industry you would like to work in and also choose what locations. You also need to write down specific names of organizations that you want to work for and who are they.

How To: Book the best hotel room for your money
Watch this video tutorial to learn how to book the best hotel room for your money. You've spent all year saving up for your dream vacation. The last thing you want is to end up in a hotel room that ruins the whole trip.

How to Beat a Telemarketer: 8 Surefire Ways to Keep Them from Calling You Back
Telemarketers can be as terrifying as a villain from a horror film. Your phone rings with an unknown 800 number, and you immediately fill with a sense of dread. There's no way to get them to stop calling; you imagine the number appearing on your phone at all hours of the day and night, haunting you.

How To: The Top 80+ Websites Available in the Tor Network
There are nearly 100,000 unique onion service addresses online with over two million people using Tor every single day. Join me as I explore a small fraction of what the Tor network has to offer.

How To: Turn Your Smartphone Pics into Extra Cash with These Android and iPhone Apps
Everything is documented these days, thanks to the Internet and mobile devices. Most people who own a smartphone use it to take lots of pictures. If you're one of those people, an app called Scoopshot can help you turn some of those photos into extra cash. Scoopshots lets you post your pics so that news organizations can pay you to use them. Companies can also post tasks, so if someone is looking for a particular photo in your area, you can accept the task, go take the photo, and earn money f...

News: This Is How Big Business, Cities & Native American Tribes Are Leveraging the Power of AR via DAQRI Headsets
While the mainstream consumer market waits for cool augmented glasses to arrive from Magic Leap, or maybe even Snap Inc. (Spectacles 2.0??), AR headset maker DAQRI and its business customers are finding new, money-saving and time-saving use cases for the technology today.

News: HoloGroup Is Trying to Crowdfund Their Holographic Learning App HoloStudy
When the HoloStudy Demo app for HoloLens came out in September, it was a pretty impressive start to what could be a very valuable science tool for education. Now, Moscow-based HoloGroup, makers of HoloStudy, started an Indiegogo campaign to improve their modular teaching app.

How To: Find Out If Facebook Owes You Ten Bucks
For the most part, nobody makes money off of Facebook. Sure, some people make a living by updating pages for businesses and celebrities, but hardly anyone gets a dime from the site itself.

How To: Become a certified aerobics instructor
Aerobics are a super fun way to get rid of some calories and lose weight. If you really enjoy your classes, maybe you should consider taking up a healthy career as an instructor! This video will give you the steps you need to make your new job happen!

How To: Help your child stop stuttering
Stuttering is a communication disorder affecting over 3 million Americans. Stuttering can make school and other social interactions difficult. Although there are no instant cures, these tips will help your progression toward speech fluency.
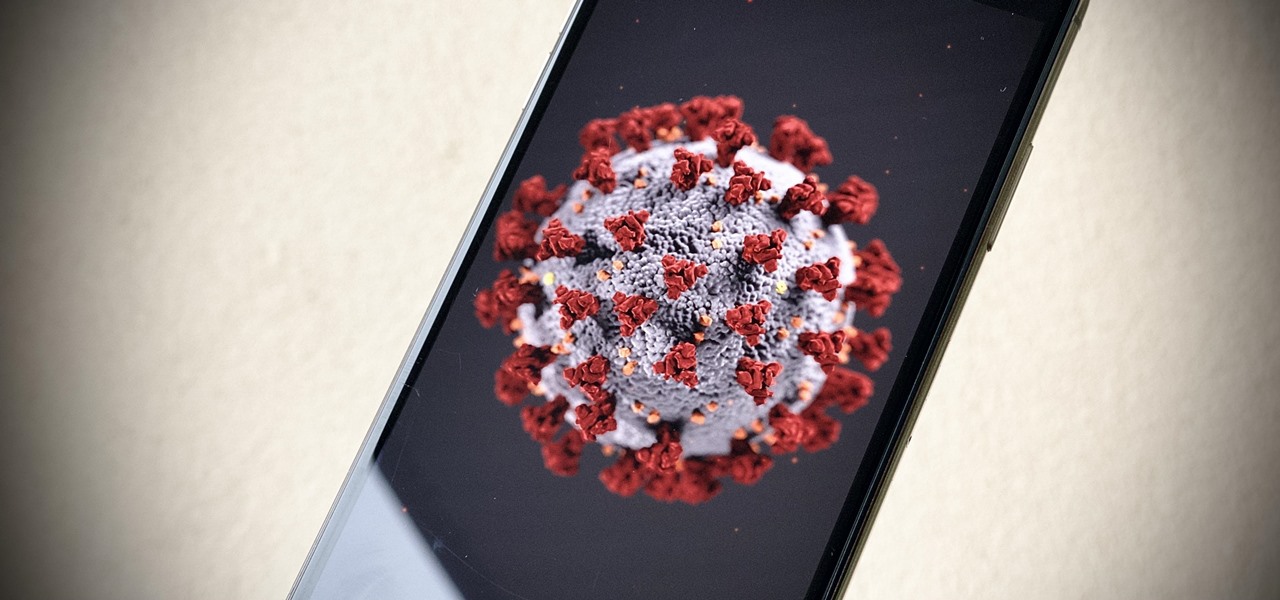
News: Apps & Resources to Follow for Coronavirus News Updates
With the whirlwind of noise surrounding the COVID-19 virus sweeping the nation, it's not hard to default to panic mode. One of the best ways to avoid panicking, however, is to follow trusted sources of information and avoid all of the opinions and trolls that don't reflect reality.

How To: Secure Your Identity & Become Anonymous Online in 2019
Your social security number, credit card information, and medical history can fall into the wrong hands if you're not careful about how and where you share your data online. If you really care about your data, there are tools and techniques you can utilize to protect yourself from cyberstalkers, advertisers, and hackers in a time when digital lives are a high commodity.

News: ODG's Newest Wearable Allows FedEx Pilots to Use Augmented Reality to Navigate Emergency Situations
On Thursday, Osterhout Design Group (ODG) revealed a new, specially-crafted oxygen mask that uses the same augmented reality technology from its smartglasses to assist FedEx Express pilots navigating dangerous conditions.

How To: Set Up SoftEther VPN on Windows to Keep Your Data Secure
Imagine for a moment that a VPN is like putting on a disguise for your computer. This disguise works to change your IP address, secure your traffic with encryption, and mask your location to bypass regional restrictions. This makes it a helpful tool for both whistleblowers and journalists. VPNs are also built into the well-known Tor Browser.

How To: Scrape Target Email Addresses with TheHarvester
Open-source data scraping is an essential reconnaissance tool for government agencies and hackers alike, with big data turning our digital fingerprints into giant neon signs. The problem is no longer whether the right data exists, it's filtering it down to the exact answer you want. TheHarvester is a Python email scraper which does just that by searching open-source data for target email addresses.

Social Engineering: How to Use Persuasion to Compromise a Human Target
Social engineering makes headlines because human behavior is often the weakest link of even well-defended targets. Automated social engineering tools can help reclusive hackers touch these techniques, but the study of how to hack human interactions in person is often ignored. Today, we will examine how to use subtle, hard to detect persuasion techniques to compromise a human target.

News: How Governments Around the World Are Undermining Citizens' Privacy & Security to Stockpile Cyberweapons
In a world increasingly regulated by computers, bugs are like real-life cheat codes. They give you the power to break the rules and do good or bad without ever leaving your seat. And government agencies around the world are discovering and stockpiling unreported bugs as cyberweapons to use against anybody they see fit.

News: Predictions for the New Year
infosecinstitute posted a handy article about what to expect in the new year for cyber security, along with highlighting major game changers from 2015; 2016 Cyber Security Predictions: From Extortion to Nation-state Attacks - InfoSec Resources.

How To: Become a Hacker
Many of our members here at Null Byte are aspiring hackers looking to gain skills and credentials to enter the most-valued profession of the 21st century. Hackers are being hired by IT security firms, antivirus developers, national military and espionage organizations, private detectives, and many other organizations.

CES 2015: Linx Headbands Can Keep You Safe from Permanent Head Injuries
Wearables were everywhere at CES 2015... you literally couldn't walk 10 feet without seeing some new and innovative device. Among the sleep, fitness, dog, and baby wearables, we came across one with a different, more important purpose—the Linx IAS injury prevention headband.

How To: Use Google's Advanced Protection Program to Secure Your Account from Phishing
It's easy to have your password stolen. Important people like executives, government workers, journalists, and activists face sophisticated phishing attacks to compromise their online accounts, often targeting Google account credentials. To reduce this risk, Google created the Advanced Protection Program, which uses U2F security keys to control account access and make stolen passwords worthless.

News: Sea Shepherd's Web-Based Augmented Reality Experience Spotlights the Damage Done by the Fishing Industry
Augmented reality's status as a new storytelling medium has already led to the reinvention of filmmaking and journalism.

News: After Nearly a Decade of AWE, Founder Ori Inbar Unpacks the Past, Present, & Future of Augmented Reality
In just a few weeks, on May 29, the annual AWE (Augmented World Expo) conference will take place once again in Silicon Valley (Santa Clara, California, to be exact).

News: Microsoft Fuels Efficiency at Chevron with Remote Assist App for HoloLens
Four months after unveiling the latest productivity apps for the HoloLens, Microsoft now has a series of compelling real-world use case videos showing how the augmented reality device and its apps are helping oil giant Chevron.

How To: Disable the 'Unlock iPhone to Use Accessories' Notification in iOS 11.4.1 & Higher
If you're on iOS 11.4.1 or iOS 12 and go more than an hour without unlocking your iPhone, an "Unlock iPhone to Use Accessories" message will appear whenever you connect your iPhone to a computer or other device that tries to use the Lightning cable's data lines. This is to protect you, but it can be annoying if you have no reason to believe that law enforcement or criminals will have access to your iPhone.

News: This Augmented Reality Panda App Uses the Voice of Kristen Bell to Teach Kids About Nature
What's black and white, sounds like actress Kristen Bell, and is standing in your living room talking to your kids right now? Don't worry, that's just Genius the Panda, an augmented reality character from the Yakables app for iPhones and iPads.
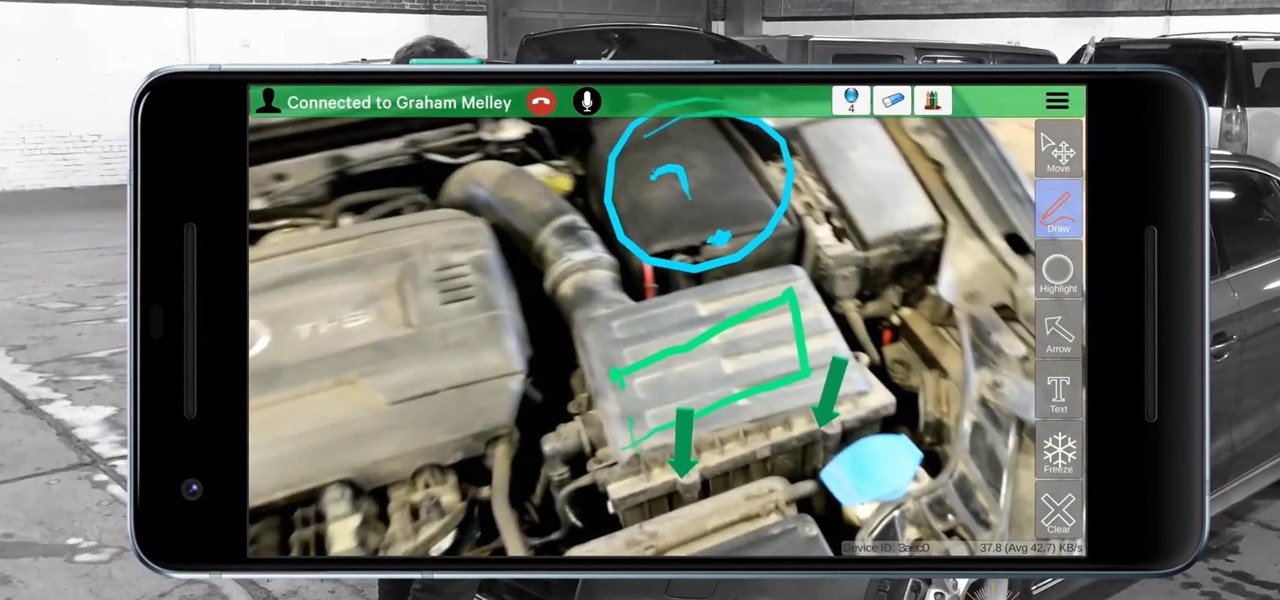
News: Scope AR Adds ARCore Support to Live Remote Assistance App
Scope AR has decided to take its live remote assistance enterprise application, Remote AR, further into the mobile augmented reality realm by harnessing the powers of Google's recently released ARCore.

