Eric Mayo teaches us how to put together a resume as an ex-offender. Your resume should be a one page paper of all your skills and work experiences. If you don't have a lot of experience writing resumes, get help from friends who have experience. When you write it, add your name, address and telephone number onto it so you can be contacted. After this, you will want to list: objective, work experience, education/training, skills/strengths, and references. Remember not to list your references ...

MSG is scary. MSG is often used as a flavor enhancer and is put into your foods to trick your brain into thinking you're happier while you eat them. MSG is very controversial and while it is still FDA approved, is not recommended for consumption. If you would like to get all the facts on MSG and know exactly which foods to look out for, watch this tutorial from Food Facts. You will learn all the secret names that MSG hides under and how to keep your kids away from this evil offender.

This video is a useful ex-offender resource that will help people with felony convictions get employment by teaching them to properly put together a resume. A poorly written resume can hinder your employment.
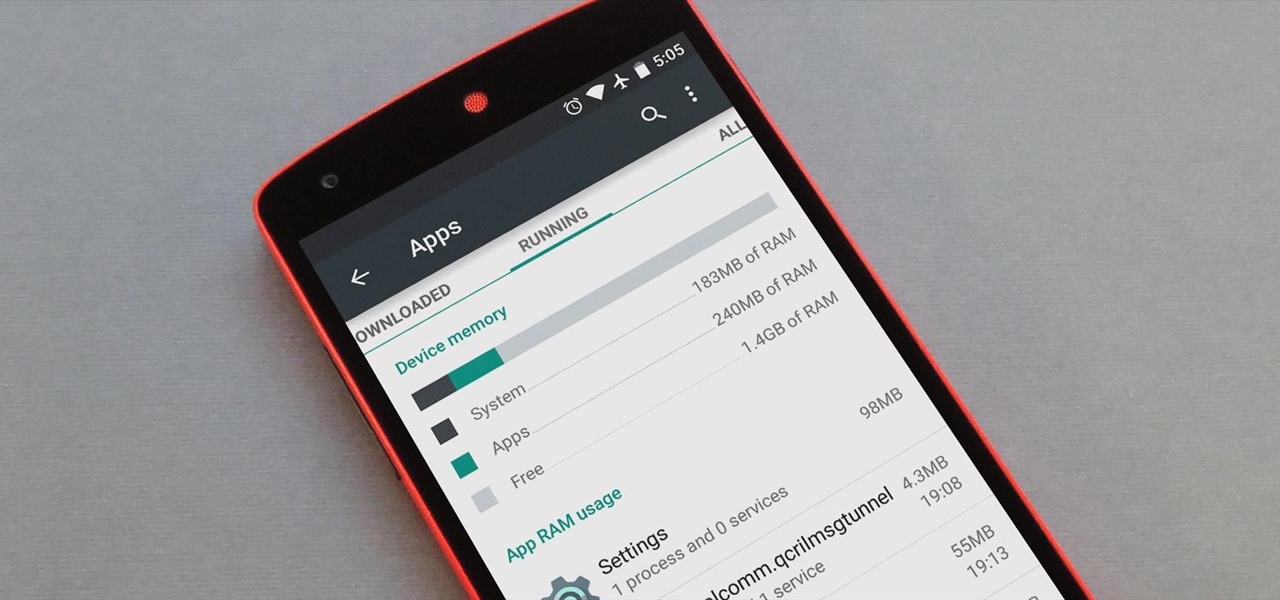
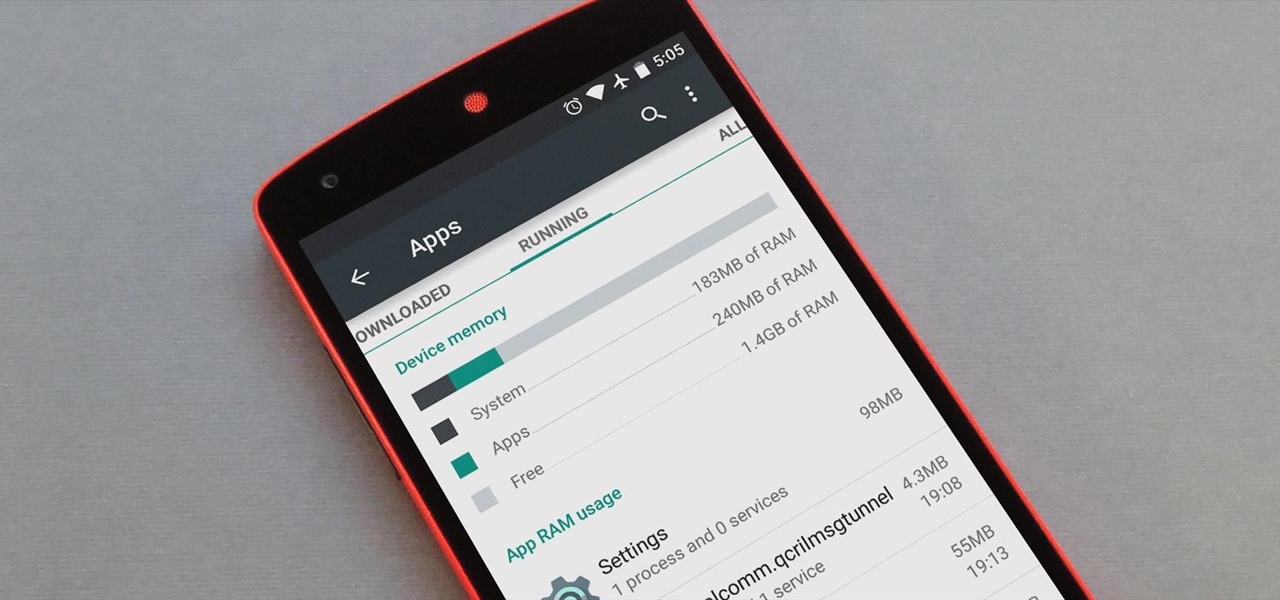
Android version 5.0 Lollipop introduced a ton of changes to the OS—and of course with new features, there's always a new set of bugs. One of the biggest bugs of all was a massive memory leak caused by the new screen-off animation, which loaded its assets into memory but never cleared them away.

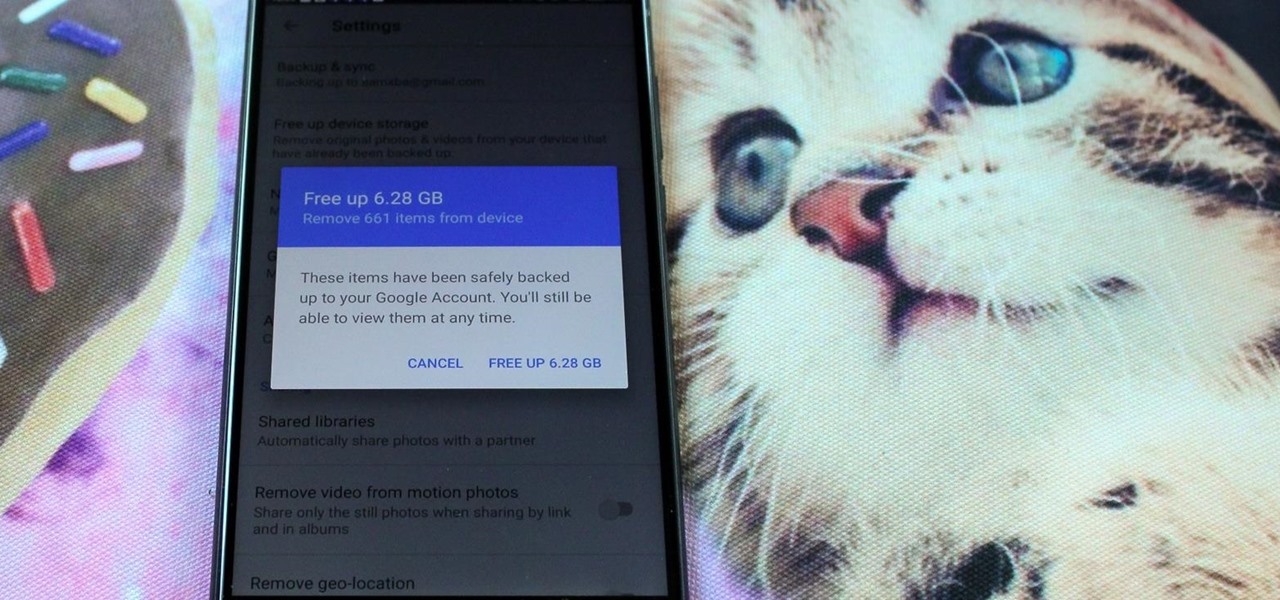
Every time Apple releases a new version of their mobile operating system, it comes packed with an assortment of bugs, issues, and other hindrances.
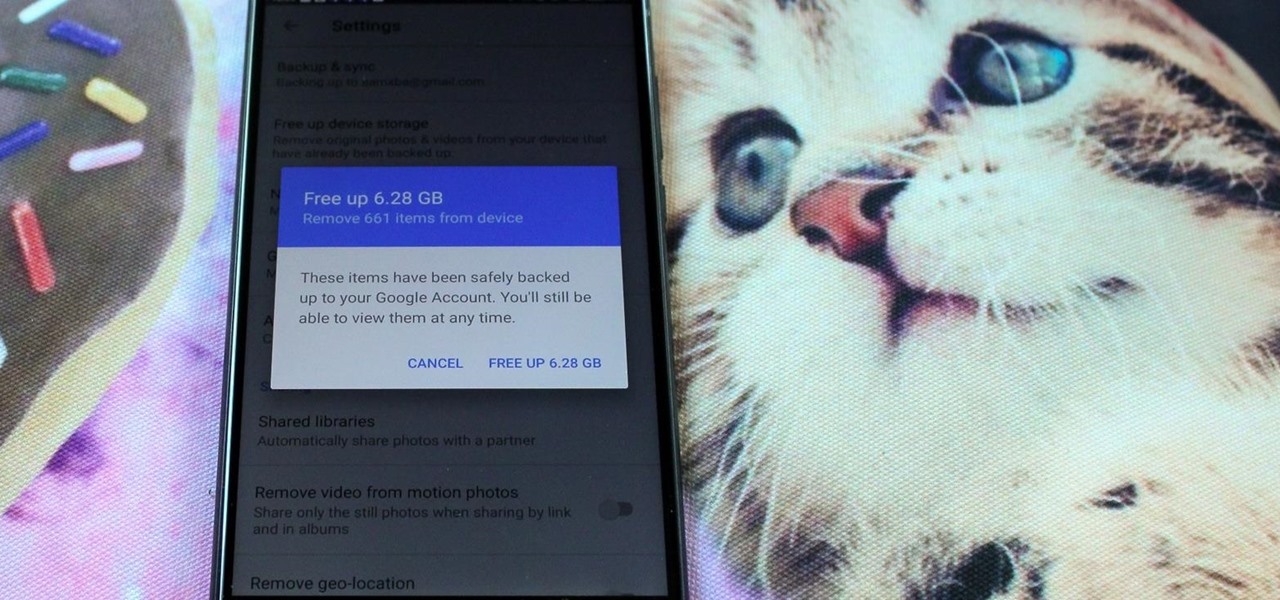
All phones (yes, iPhones too) slow down over time. As your device gets bogged down by various apps and you begin to run out of storage, it's just an inevitability. That doesn't make it any less frustrating ... I mean, is there anything more annoying than a slow phone? My answer: No. Of course not. It's the single most annoying thing ever.

It has been a long while since I last came here to write an article. Graduate school keeps you busy. After I looked over what I had written previously, I decided that I should introduce another fun topic from cryptography. In this case, steganography.

Open-source intelligence researchers and hackers alike love social media for reconnaissance. Websites like Twitter offer vast, searchable databases updated in real time by millions of users, but it can be incredibly time-consuming to sift through manually. Thankfully, tools like Twint can crawl through years of Twitter data to dig up any information with a single terminal command.

The latest film addition in the American-produced Millennium series, The Girl in the Spider's Web, was just released on Blu-ray a few days ago. As you could expect, the movie has many hacking scenes throughout, just like the previous English and Swedish language movies centered around hacker Lisbeth Salander. Of course, with the quick pace of some scenes, the hacks can be hard to follow.

Introduction Halo: Reach is Bungie's latest and final addition to the franchise. Microsoft has claimed the title and from now on 343 Industries will be working on the Halo franchise. In my opinion, Bungie's last game is the best out of all of them. These are some tactics and bits of advice that I've picked up.

Acclaimed Cinematographer Adam Kimmel Arrested:

Honestly, I have no clue. I think it was one of the smartest plays in WC history. Game on the line. If that ball goes in, you're going home. You sacrifice yourself to a red card (and the next game against Holland), but you give your goalie and the Fates an opportunity. So, is he another Henry who gave his country an opportunity or a FairPlay offender to its very definition? Uruguay - Ghana

Some cops already have the ability to extract data from your cell phone using handheld forensic devices, but soon police officers will have a new mobile data collection toy to play with—an Apple iPhone. Actually, it's an iPhone-based device that connects directly to the back of an iPhone, which is designed to give law enforcement an accurate and immediate identification of a suspect based on their facial features, fingerprints and even their eyes.