Not sure what to do when you get a security warning about a macro? What are macro security settings, the Trust Center, and Trusted Locations anyway? Watch this instructional video to learn how to enable macros and make informed security decisions that can help you keep your computer safer while you work in Microsoft Office Excel, Outlook, Word, Publisher, PowerPoint, and Visio 2007.

Want to play old school Nintendo on your Windows Mobile devices, such as smartphones? Well, this video tutorial will show you how to install the NES emulator on that Windows Mobile electronic touchscreen device. Just sync up your cell phone, and download the software off of the Internet. Just think, you could be playing Mario in the palm of your hand, on your mobile phone.

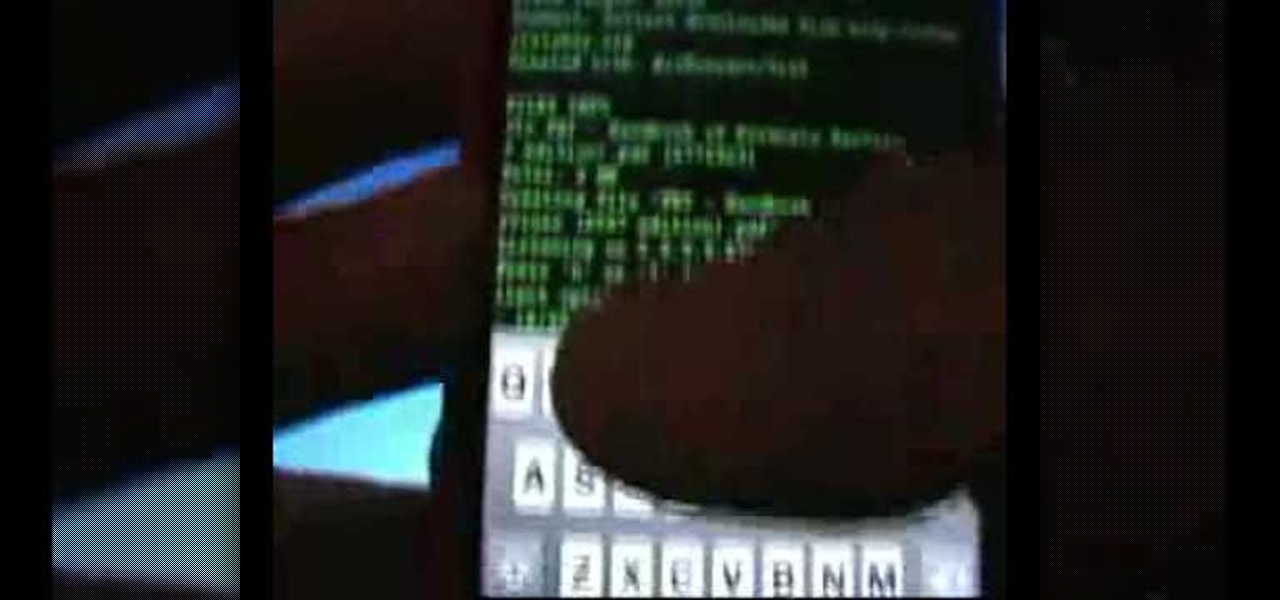
A basic tutorial from InfinityExists.com on using Backtrack - the Linux-based security software package. This tutorial covers: Where to get Backtrack 2, How to burn an .ISO file, How to boot Backtrack 2, How to login, and start the GUI interface. It also illustrates basic Linux commands, and how to set up your Network Interfaces.

Learn how to set up the lighting rig of your mobile DJ set up - including proper light placement. Part 1 of 2 - How to Set up the lighting in your mobile DJ set up.

A look at how to set up your pa, mixer, turntables and amp in your mobile DJ setup. Part 1 of 2 - How to Set up the audio and PA in your mobile DJ set up.

This two part segment will show you how to use the Wi-Fi tethering mobile hotspot functionality on your Motorola Droid Bionic smartphone for free after rooting it. Segment 2 of the guide will walk you through using Radiocomm to hide your tethering usage from Verizon Wireless so you're less likely to get caught.

There are so many different devices today that have Wi-Fi capabilities--notebooks, handheld gaming devices, tablets, and more. Why not share some of the 3G and 4G internet that streams into your Motorola Droid 3 with the other electronics you carry with you? You can turn your Verizon Wireless Droid 3 smartphone into a mobile Wi-Fi hotspot using the mobile hotspot menu on the android phone.

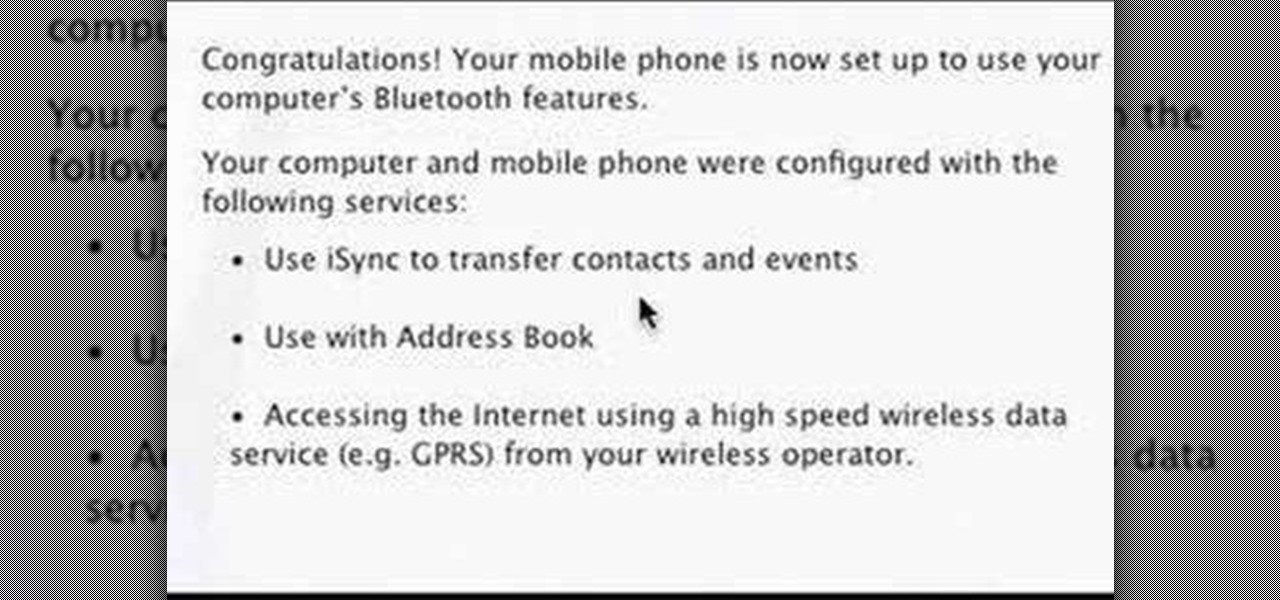
In this video you will learn how to setup a Bluetooth mobile phone in OS X. To do this go at system preferences select Bluetooth click on Discoverable, Open Bluetooth Setup Assistance and Show Bluetooth Status in the menu. Then click Sharing and mark all the options. Now go at devices, select set up new device, mark mobile phone, click continue, wait until the device will find your mobile device, click continue and you will get a pass key. Enter that passkey. A window will pop-up where you ca...

During the recent Augmented World Expo (AWE), we had a chance to try out the Lenovo ThinkReality A6 AR headset. Unfortunately, the experience was all downhill from there.

Just weeks after revealing plans to port one of its most vital augmented reality products from HoloLens to the smartphone world, Microsoft has finally opened the mobile software floodgates to the public.

While iOS 12 is arguably the best iteration of Apple's mobile operating system yet, one major fault so far is security. On Sept. 26, Videosdebarraquito discovered a passcode bypass that gave access to contacts and photos from the lock screen. Apple has since patched that security flaw, but Videosdebarraquito has discovered a new one that affects all iPhones running iOS 12.1 and 12.1.1 beta.

These days, it seems new phones get announced every other week. We've grown accustomed to glossing over the specs, looking at some press renders, then moving on to check out the next phone. If you had done this in September 2008, you might have overlooked what would become one of the most important phones of all time.

As the level of data being generated grows exponentially, past the Information Age and into the coming Hyper-Information Age of immersive computing — as resistant as many of us are to the idea — personal data security is becoming a necessary consideration in our everyday lives. Recognizing this, Mastercard, Qualcomm, and Osterhout Design Group have teamed up to show what secure shopping could look like in the very near future with iris authentication.

Hackers are claiming money for a security flaw in Apple's new update. Quick Summary:

T-Mobile continues to make waves in the U.S. wireless market behind CEO John Legere's UnCarrier program. At the latest installment in a series of industry-challenging announcements, Uncarrier 5.0 unveiled Test Drive. The new program is set to allow would-be customers to try out the "latest generation" iPhone for seven days on T-Mobile's network without any financial commitments.

How much privacy are you getting as an AT&T customer? With the recent leaks confirming the National Security Agency's surveillance on AT&T users, and the ongoing trial of Jewel v. NSA, it seems not much at all.

There are many different applications and games on the Nintendo 3DS that can take advantage of an active internet connection over Wi-Fi such as Netflix or the eStore. Unfortunately, since the 3DS is a mobile device, you won't always have access to the internet. If you have a mobile hotspot on a smartphone or tablet, you can share the internet connection over wireless with the gaming handheld.

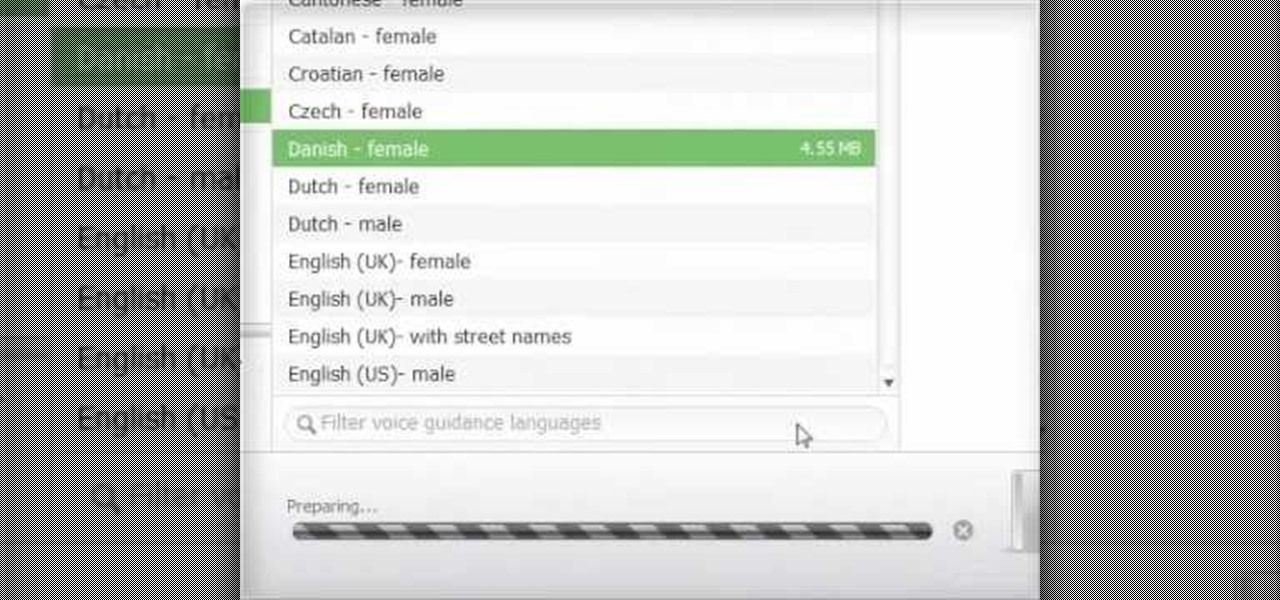
In this clip, we learn how to create Ovi Maps routes with your PC when using a Nokia C5 mobile. The C5 is the first offering in Nokia's new "C" series of mobile phones. It runs on Nokia's Symbian OS and features a 2.2-inch screen and 3.2-megapixel camera. Want more? Search WonderHowTo's sizable collection of C5 video tutorials.

In this clip, we learn how to download additional Ovi Maps-compatible maps when using a Nokia C5 mobile phone. The C5 is the first offering in Nokia's new "C" series of mobile phones. It runs on Nokia's Symbian OS and features a 2.2-inch screen and 3.2-megapixel camera. Want more? Search WonderHowTo's sizable collection of C5 video tutorials.

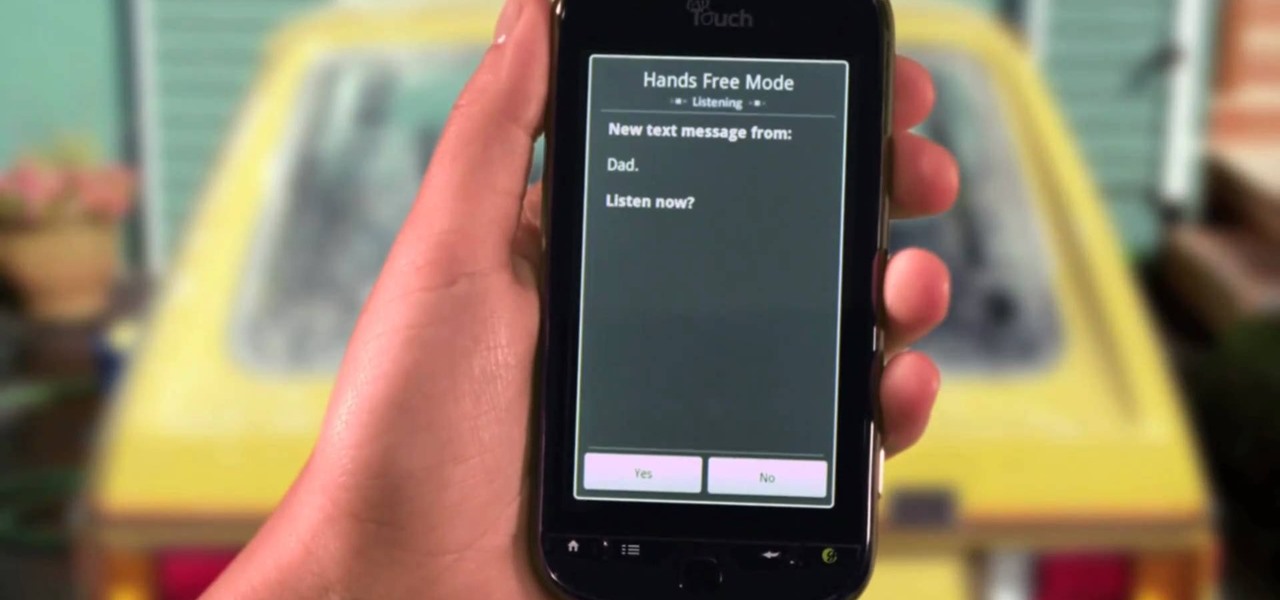
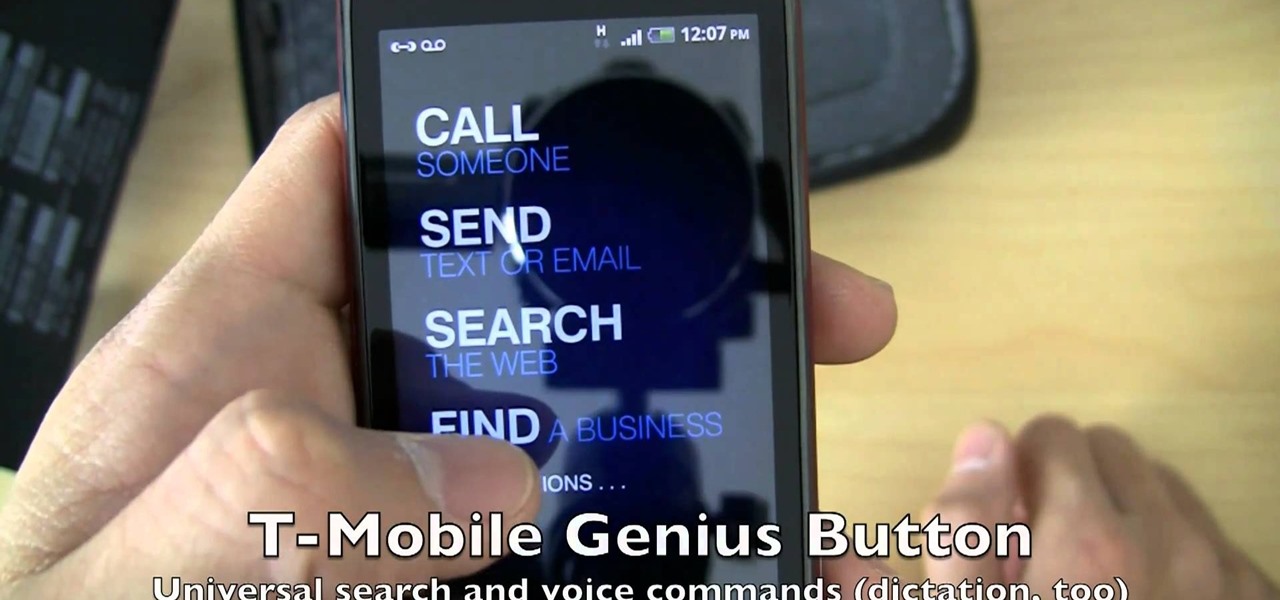
Control your myTouch 4G with your voice! This clip will teach you how to use the myTouch 4G's Genius Button. Whether you're the proud owner of a T-Mobile myTouch 4G Google Android smartphone or are merely toying with the idea of picking one up sometime in the near future, you're sure to be well served by this brief, official video tutorial from the folks at T-Mobile. For complete instructions, watch the video!

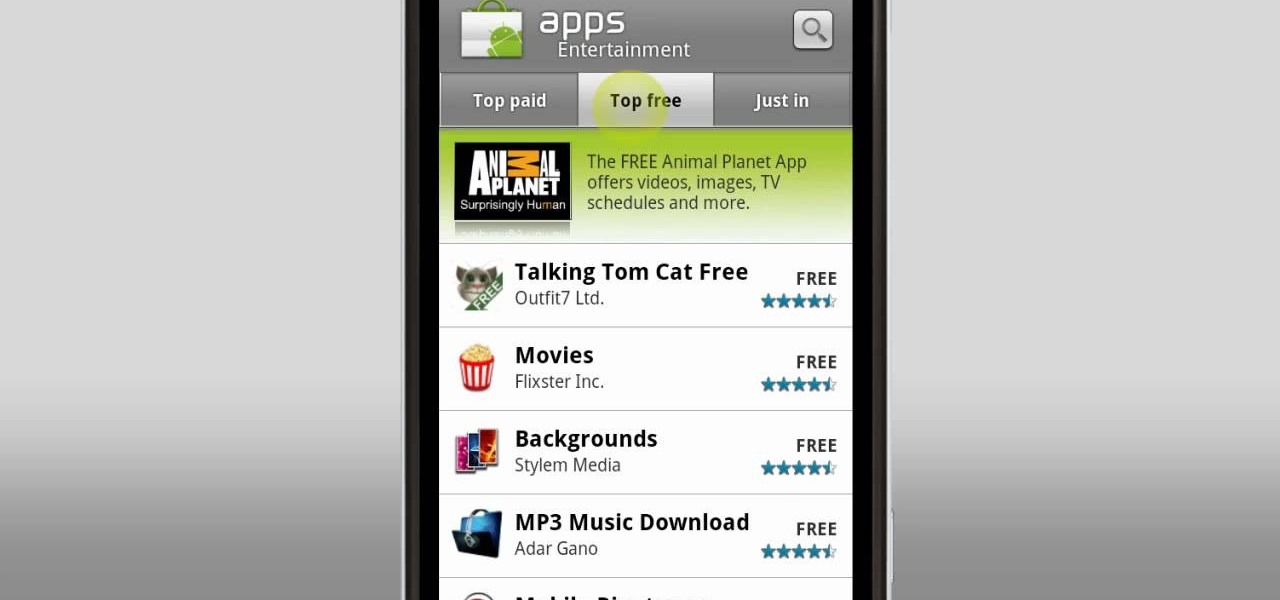
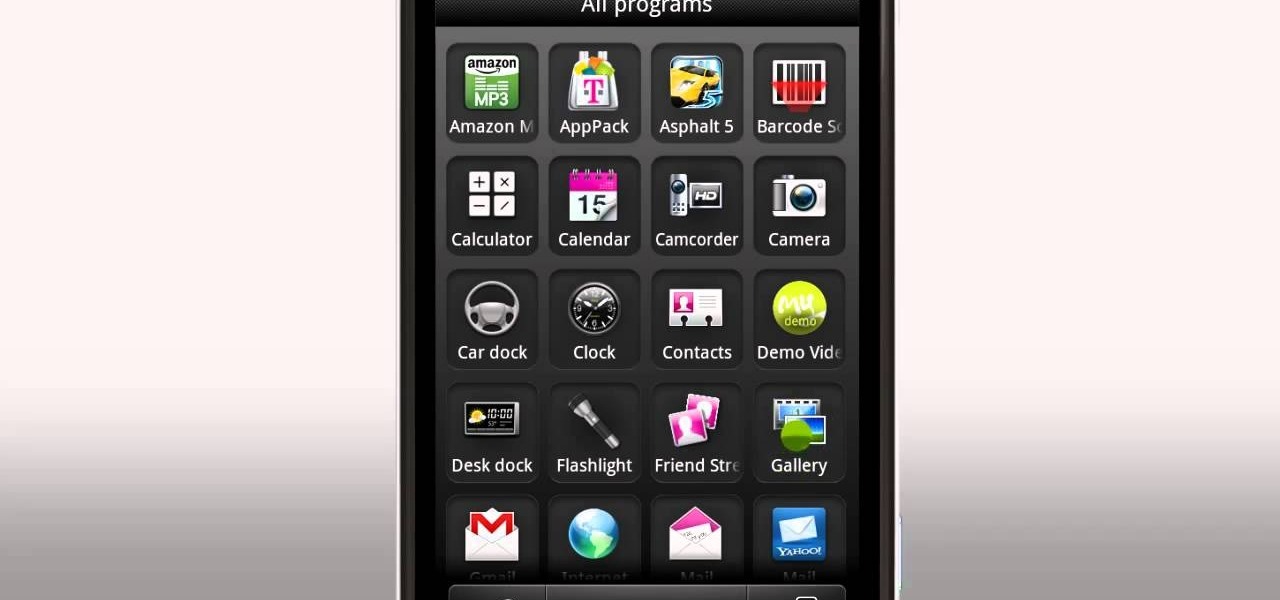
Find and download new apps to a myTouch 4G with the Android Market! This clip will teach you how. Whether you're the proud owner of a T-Mobile myTouch 4G Google Android smartphone or are merely toying with the idea of picking one up sometime in the near future, you're sure to be well served by this brief, official video tutorial from the folks at T-Mobile. For complete instructions, watch the video!

Use the myTouch 4G's Gallery app to browse between captured pictures and videos! Whether you're the proud owner of a T-Mobile myTouch 4G Google Android smartphone or are merely toying with the idea of picking one up sometime in the near future, you're sure to be well served by this brief, official video tutorial from the folks at T-Mobile. For complete instructions, watch the video!

Learn everything you need to know about using a T-Mobile myTouch 4G Google Android smartphone. This video guide presents a general overview of the phone's hardware and software. For all of the details, and to get started using your own myTouch 4G, watch this video guide.

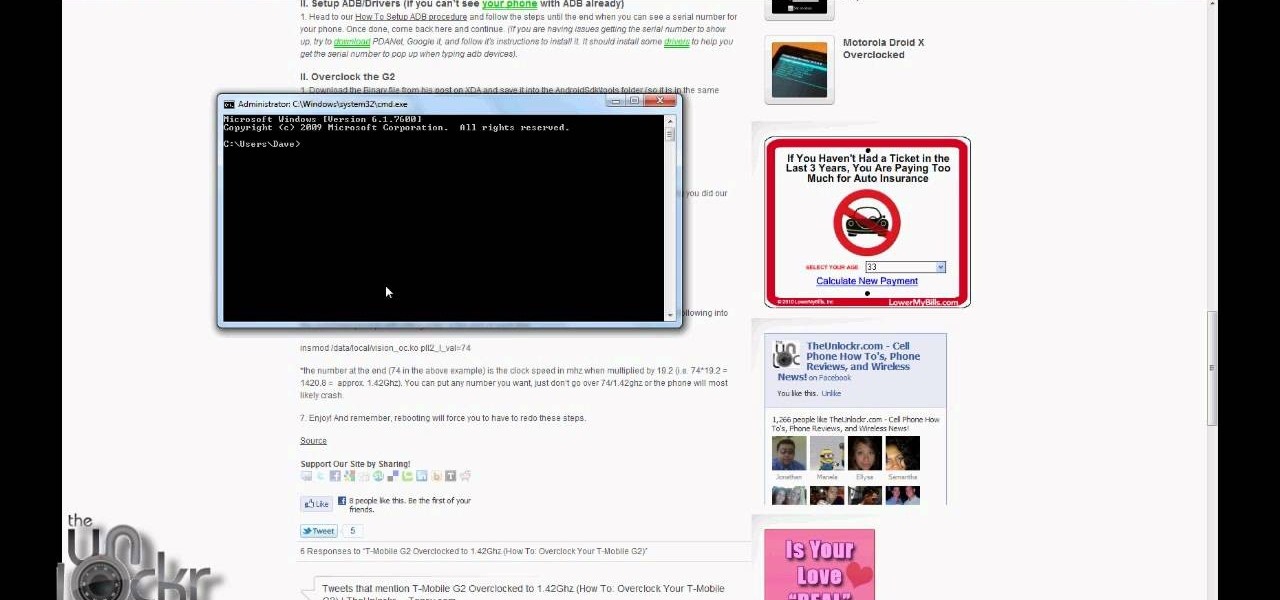
Get more power out of your T-Mobile G2 Google Android cell phone by overclocking it's CPU! It's easy! So easy, in fact, that this mobile phone hacker's guide can present a complete overview of the process in about four minutes. For more information, including detailed, step-by-step instructions, take a look!

Learn how to install a custom ROM on a rooted T-Mobile G2 Google Android tablet. Whether you want to learn how load a custom ROM on your own T-Mobile G2 or just want to see how it's done, you're sure to be well-served by this seven-minute hacker's how-to. For detailed, step-by-step instructions, take a look.

Learn how to load a cracked Hero ROM onto a rooted T-Mobile G1 Google Android smartphone! Custom ROMs help you to unlock your phone's hidden potential and allow you to, among other things, turn your mobile phone into a 3G wireless modem with free WiFi tethering. For all of the details, and to get started running custom ROMs on your own rooted G1, watch this three-minute hacker's how-to.

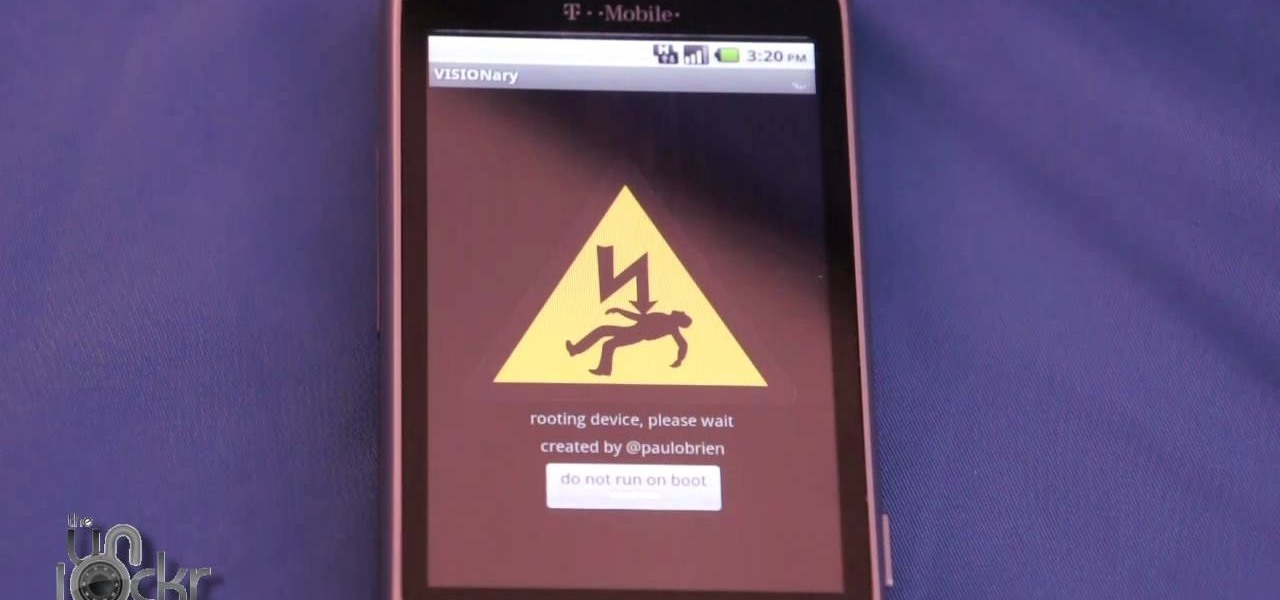
Root your G2 the easy way with an app you can download directly from the Android market! Unlock your mobile phone's hidden potential by running custom ROMs, overclocking it, and even turning it into a wireless hotspot with WiFI tethering. For all of the details, and to get started rooting your own G2 cell phone, take a look.

Much like Mac OS X computers, Apple iOS mobile devices like the iPhone and iPad support VoiceOver, Apple's text-to-speech module. In this video clip, you'll learn how to turn it on and use it on your own iOS mobile device.

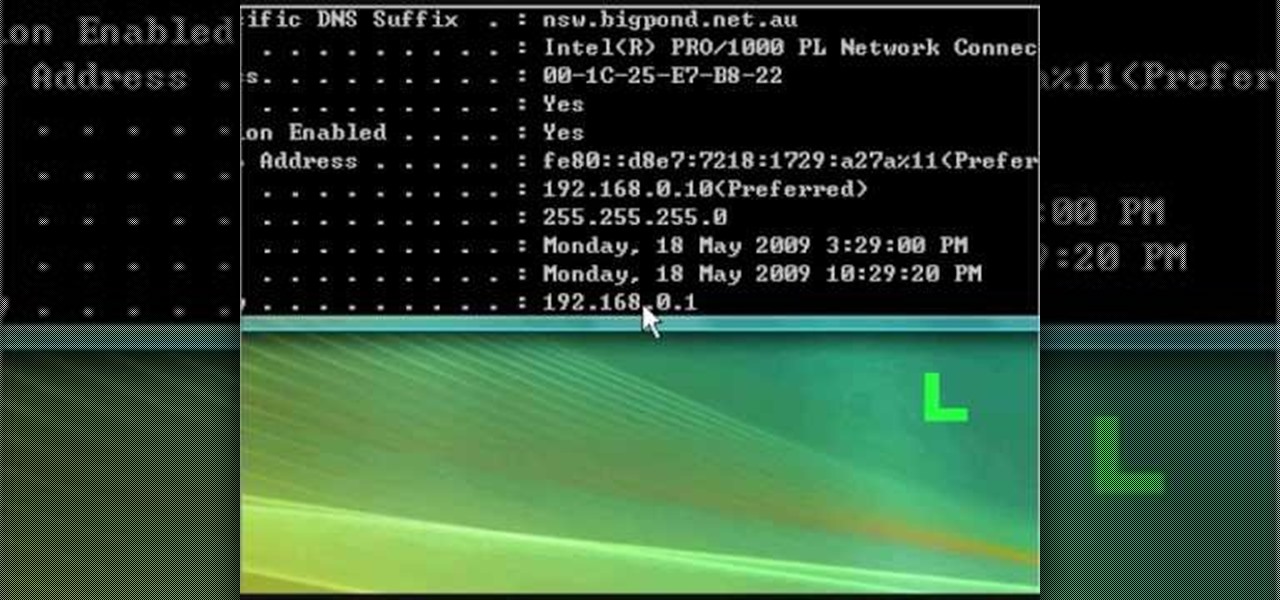
In this tutorial, we learn how to fix security mode for nds Wi-Fi. First, open the command prompt in Windows. Next, type in "ipconfig/all" in the black window that appears. After this, copy your default IP the screen just gave you, then type it into your address bar online. After this, you will be able to log into your security account and make default changes you prefer. Change different station accesses and any other security preferences you want to change. After this, you can change your p...

Root your T-Mobile MyTouch 3G or G1 Android smartphone using the flashrec.apk method, which will permit you to replace your recovery image in a single click. For detailed, step-by-step instructions, and to get started rooting your own T-Mobile Android MyTouch 3G or G1 phone, watch this free video tutorial.

Having security setting on your web browser is a pretty important tool. It keeps you safe from potential hackers and makes sure you don't visit unsafe sites that could lead to a virus. But sometimes the security settings on a web browser can be a pain and the best choice would be to turn it off. So in this tutorial, you will learn how to easily change the security settings to INternet Explorer 8. So sit back and enjoy!

Going mobile? While the ASUS Eee PC is undeniably one of the most portable travel laptops available, it's by no means the the most mobile, because mobility also implies mobile connectivity. In this video tutorial, you'll learn how to install a 3G HSPDA modem in an Asus Eee PC. This mod will work on any Eee PC without the extra PCIE slot. For step-by-step instructions, watch this how-to.

In this video, we learn how to download torrents on the iPhone 2.0 or 2.1. Before you do this, you will need: Cydia, Mobile Terminal, C Torrent, Safari Download Plug-in, and Mobile Finder. to start, you will first go to a torrent site and find the torrent that you want to download. Then, click on the download torrent button. From here, you will see a warning appear on the screen. Choose to download this and then go to your Mobile Finder. Find where you saved the torrent to. Then, hit the home...

Tetiana from Best Buy Tips and Tricks shows you how to upload a photo on your mobile phone to your Facebook account directly from your mobile phone. For this you need to select the photo from your media, choose the option "upload to Facebook" and insert a suitable caption as shown in the video. The photo will be uploaded to your Facebook account for all your friends to see. Now you can share photos with your friends via Facebook on the go, using your mobile phone.

This is a video guide to mobile broadband from Top10.co.uk. Find out what mobile broadband is in this informative video. This "how to" mobile broadband video will explore how and where mobile broadband works, what the advantages of using mobile broadband are, who offers it and how to set it up on your laptop -- from dongles to USB modem sticks.

Cyber Security is a horrible computer virus. It mimics a virus protection program and invades your system, making it nearly impossible to remove. In this tutorial, learn how to remove this annoying trojan horse from your PC and save your computer.

Video tutorial showing how to make your own solar-powered wireless security camera using an off-the-shelf solar panel and any wireless webcam. See creator site for more detailed graphics.

Smartphones are inherently bad for privacy. You've basically got a tracking device in your pocket, pinging off cell towers and locking onto GPS satellites. All the while, tracking cookies, advertising IDs, and usage stats follow you around the internet.

If you've ever received an email from a sketchy address purporting to be Uber, asking you to sign in with your credentials, you might be a phishing target. Hackers use a fake login page from real-looking domains to trick you into giving up your account information, and while it's been an issue in the past, Uber is making it more difficult on cyber thieves with the addition of two-step verification.

In the business world, it's sometimes said that "where there's smoke, there's fire." At Snapchat parent company Snap, Inc., it appears the equivalent of smoke is executive turnover.