It's 2017 and finally ordering "fries with that" at McDonald's is an even easier prospect for all you lovers out there ball and chained to the fast food game. The great big golden arches are moving one step closer to making your order as golden as it ought to be through a mobile ordering app using geofencing technology to track your location.

As great as the Internet is, it is not without its dangers. Hackers at any time may be breaking into your online accounts and compromising your sensitive information. Last year, hackers broke into Facebook, Gmail, and Twitter and made off with 2 million stolen passwords.

Windows Vista is jam-packed full of new security features, which could be a good thing, but they're just so obtrusive it's not really worth it. If you want to learn how to stop all of the annoying security alerts, this video will walk you through the process of disabling these security notifications in Windows Vista.

In recent years, unwanted calls have become a top priority for the FCC. In 2016, analysts estimated that US customers received over 2.4 billion robocalls per month. As a result, the FCC has provided carriers new tools to combat this problem.

Perhaps it's a coincidence that the Vuzix Blade smartglasses look like the sunglasses that a police officer would wear, but a new partnership with an AI software company makes the wearable a perfect fit for law enforcement.

A pair of organizations recognized companies working in augmented reality for their innovative technologies over the past week. Meanwhile, another company used augmented reality for a sector that is overdue for a technology makeover, while another company has developed new camera modules that could usher in the next evolution of mobile AR.

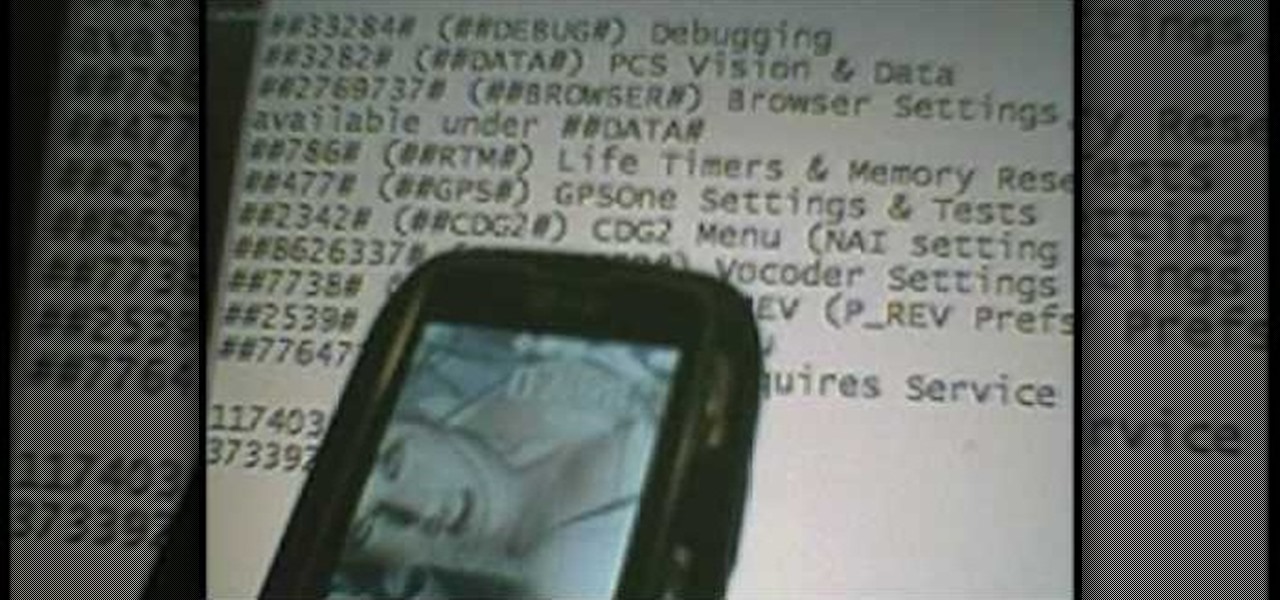
Cellular carriers like to nickel-and-dime us out of every bit of money they can feasibly justify, so as consumers, we owe it to ourselves to make sure that we're getting our money's worth.

I think it's safe to assume that most of us appreciate a little privacy and security when it comes to our mobile devices, which is exactly why we have lock screens that require unique passwords, patterns, or PINs. Although someone can discretely peer over your shoulder to see what your password is, it's much more difficult for them to duplicate your face to unlock the device.

Every day it seems like new information comes to light about how the National Security Agency creeps into our lives. Knowing that they can backdoor into our seemingly private devices is a scary thought, whether you have information to hide or not.

Former Vice President Dick Cheney was so fearful of attacks, he had his heart defibrillator re-calibrated to block incoming wireless signals so that highly skilled hackers couldn't send him into cardiac arrest.

Depending on what mobile device you own, you'll see something that says "via device name" next to the date of your post on Facebook. If you're device is not recognized, you'll simply see a "via Mobile" note, which is what happens when I post from my phone. If you allowed your iPhone to be called iPhone when you logged into the app, it'll show up as a recognized device on Facebook, and will post "via iPhone." Same thing goes if you have a Samsung Galaxy S3 or Nexus 7 or iPad. It could also jus...

You don't want anybody to have access to your cell phone. Nobody. Well, instead of the standard unlock mechanism, the one anybody can unlock your cell phone with, the Motorola DROID, and Android enable mobile device, allows you to create your own unlock pattern, secret to anyone else, which wakes it from sleep mode. Best Buy has answers. The Best Buy Mobile team explains how simple it is to set up a secure lock on a Motorola DROID cell phone.

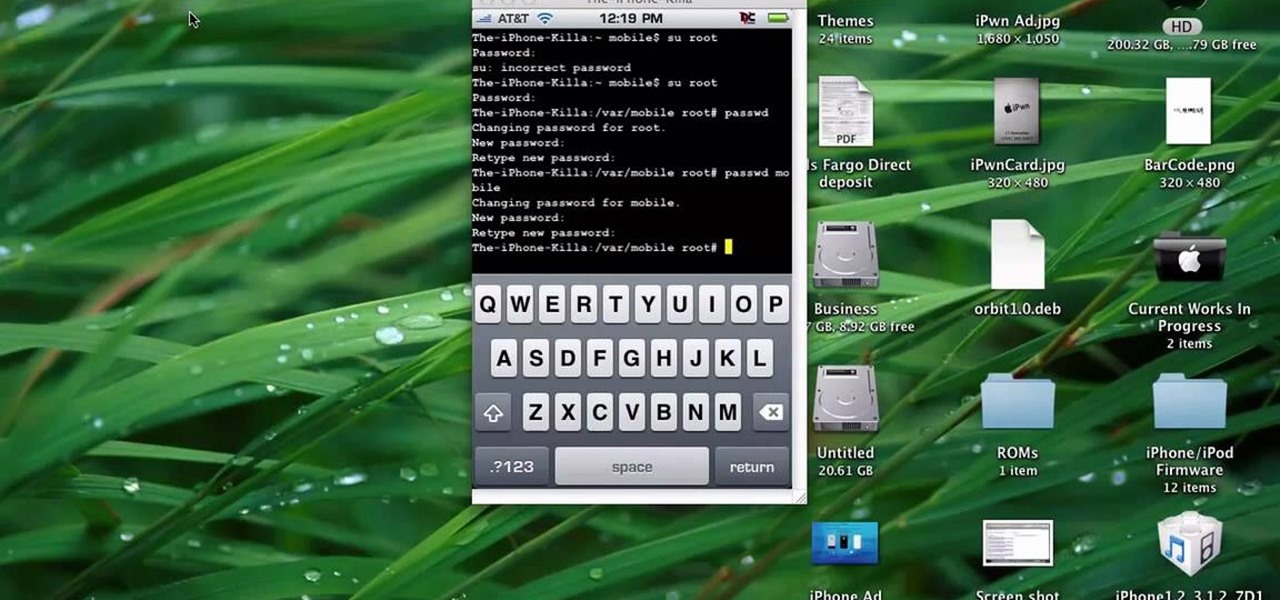
This quick tutorial runs you through a fast and easy way to make your iPhone or iPod Touch more secure. However the best security is abstinence. Just don't run the programs that leave your devices vulnerable unless you need them.

Lock picking can be difficult with some security features. This instructional video shows you what happens when you encounter them and what to do. Break into a lock when you've forgotten your keys, but please don't sneak in anywhere you don't belong. Watch this video lock-picking tutorial and learn how to detect security pins.

With the new screening protocols and their full body x-ray scanners, the TSA is taking constant criticism from unhappy travelers. Between the nude images the scanner produces and the awkward pat downs, air travel will never be the same. That's why it's important to make sure you're prepared for your flight and the TSA security checkpoints.

Kryptowire, a company specializing in mobile security solutions, released a report on Tuesday, November 15 that exposed firmware in a number of Android devices that was collecting personally identifying information (PII) and uploading it to third-party servers without users' knowledge.

Installing security lights outside of your home can make for a great addition, but they also create new problems with regards to maintenance and cleaning. Having lights outside exposes them to all of the elements that mother nature can throw at them. This video will show not only how to install security lights, it will also show the proper measures to take so they will keep working with minimal maintenance and care.

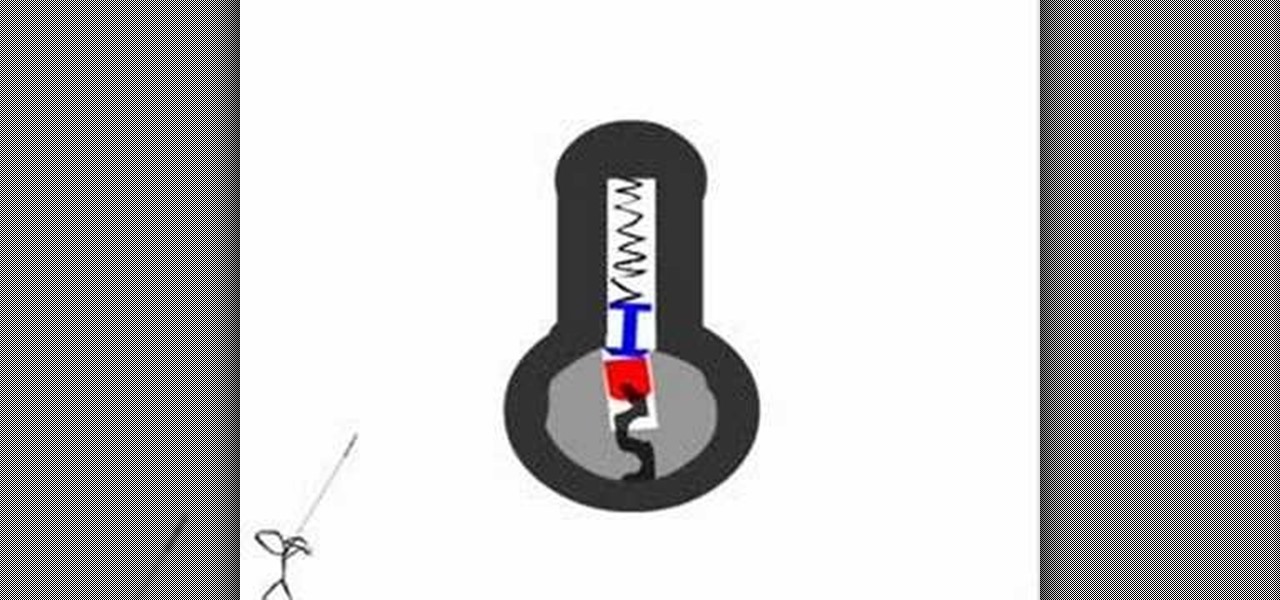
This is a lock picking video which demonstrates how to pick a tumbler lock. Of course the only way to really open locks is to practice. But this is the basic info to picking locks. This lock picking tutorial also covers security pins and clear instructional animations to demonstrate. Learn how to pick a lock and use this video to understand lockpicking, security pins, skill tension, and bump keys. See all about how to pick a tumble lock & understand lock security pins.

Make calls and send text messages and emails with voice commands on your T-Mobile G2! This clip will teach you how. Whether you're the proud owner of a a T-Mobile G2 Google Android smartphone or are merely toying with the idea of picking one up in the near future, you're sure to be well served by this official video guide from the folks at T-Mobile.

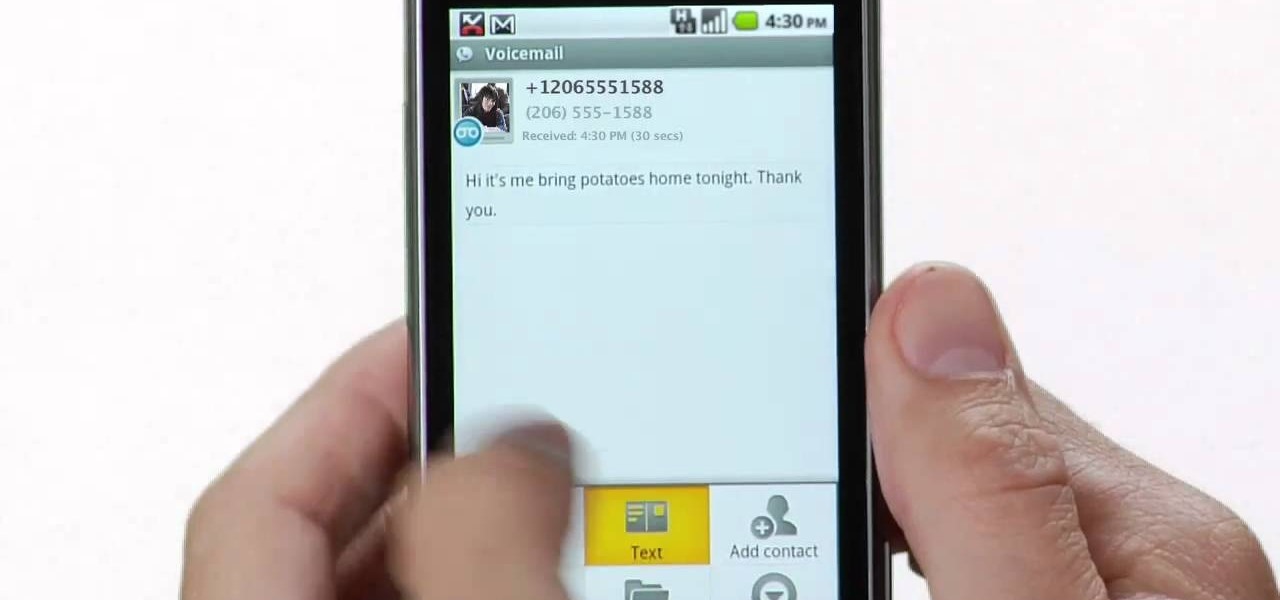
Use Google Voice to transcribe voicemails received on your T-Mobile G2! This clip will teach you how. Whether you're the proud owner of a a T-Mobile G2 Google Android smartphone or are merely toying with the idea of picking one up in the near future, you're sure to be well served by this official video guide from the folks at T-Mobile.

Use all of your web apps on your T-Mobile G2! This clip will teach you how. Whether you're the proud owner of a a T-Mobile G2 Google Android smartphone or are merely toying with the idea of picking one up in the near future, you're sure to be well served by this official video guide from the folks at T-Mobile.

Use all of your favorite Google apps on your T-Mobile G2! This clip will teach you how. Whether you're the proud owner of a a T-Mobile G2 Google Android smartphone or are merely toying with the idea of picking one up in the near future, you're sure to be well served by this official video guide from the folks at T-Mobile.

Interested in loading a custom ROM onto a Windows Mobile Device running Windows Mobile 6? This clip will teach you everything you need to know. It's easy! So easy, in fact, that this mobile phone hacker's guide can present a complete overview of the process in about seven minutes. For more information, including detailed, step-by-step instructions, take a look!

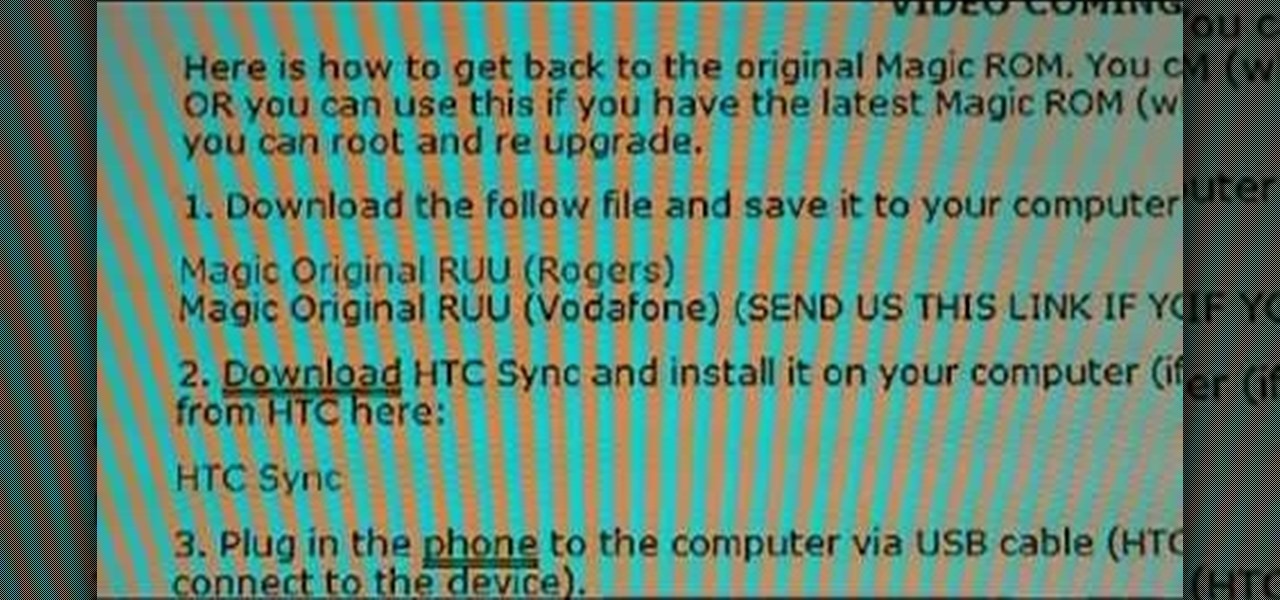
Have rooter's remorse? Want to restore and reset your HTC Magic or T-Mobile MyTouch 3G's factory firmware and put your cell phone back as it was? Here's how you do it!

In this clip, you'll learn how to quickly set a security pattern on an LG Droid Ally Google Android smartphone. For more information, including a complete demonstration and detailed, step-by-step instructions, and to get started setting up your own security secreen, watch this helpful video guide.

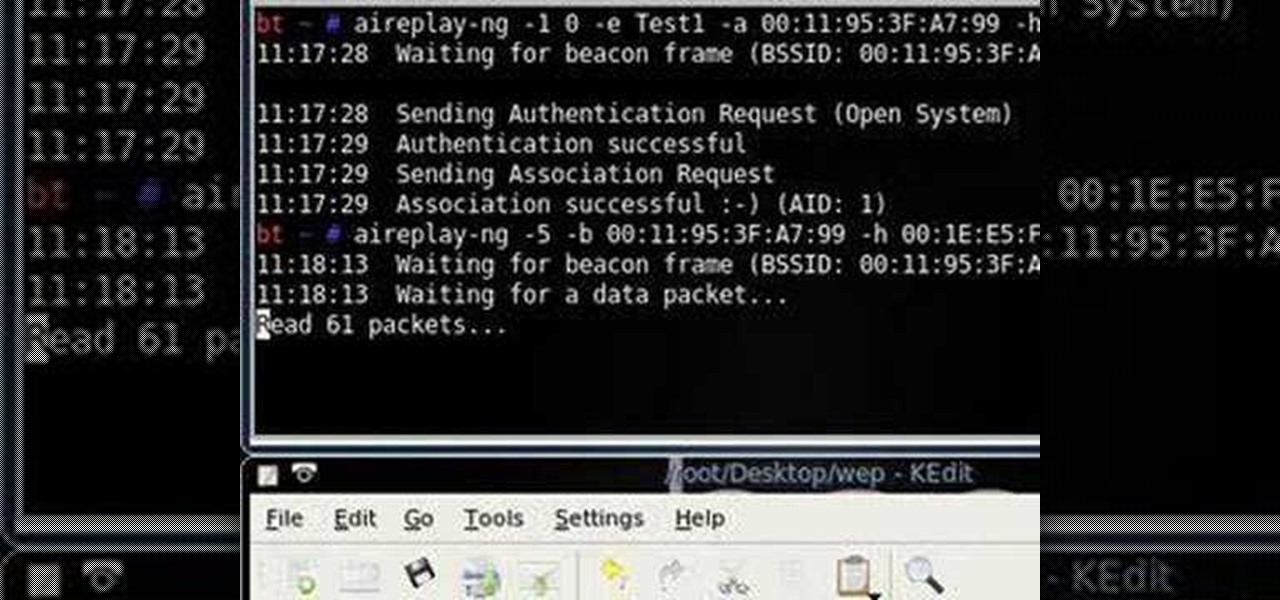
Want to test the security of your WEP WiFi wireless network? In this clip, you'll learn how to use the Backtrack Linux distro and the Aircrack-ng WiFi security app to crack a WEP key. The process is simple. For more information, including step-by-step instructions, and to get started testing the security of your own WiFi networks, watch this hacker's how-to.

Learn how to configure the features in F5's FirePass v7 SSL VPN Endpoint Security. Peter Silva shows some of the new Endpoint Security features in the recent FirePass v7 release. Watch how to create policies, enforce host checks and other protective measures for your Remote Access deployments. For more information, and to get started configuring your own installation of FirePass v7, take a look.

If you live in a hurricane prone area, it is a good idea to protect your windows with security film. This video will teach you how to install hurricane security window film on your own and protect your home and assets.

In this video tutorial, viewers learn how to tune their ukulele or guitar with a Windows mobile. Begin by going to the link in the video description and download the Audio Tuner Mobile program. Connect the mobile your PC and install the Audio Tuner program. Open the Audio Tuner program in your mobile phone. Users are able to choose from a variety of instruments such as: the banjo, bass guitar, guitar, mandolin, piano, ukulele and violin. The users are able to choose which note they want to tu...

In this four part video series, learn how to "hack" the LG Rumor/Rumour. In part one, learn the codes you can do, without using the USB cable. Part two and three goes over hooking the phone up to bitpim. Lastly, part four sums up what you will have learned. Again, by hacking your phone there is a chance you can damage your phone, so proceed with caution!

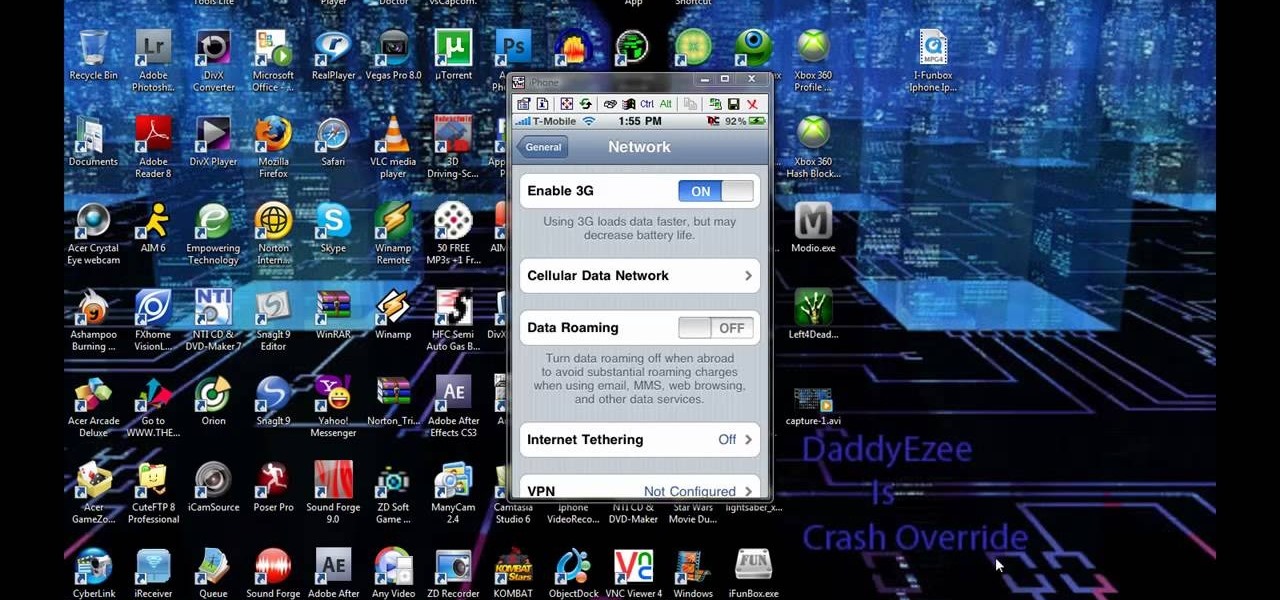
Check out this video to learn how to get MMS on iPhone 3G for T-Mobile on 3.0 firmware. This works on T-Mobile's Network only!

Ever wanted to learn how to pick a lock? Well, there's no better time than now to start learning the craft of so many locksmiths out there... lock picking. Just watch this video tutorial to see how to bypass security wafers when lock picking.

Want to mix and scratch like a professional DJ? To be a good DJ you need to understand the concepts of mixing tracks, adding cool effects, and of course you need a good sense of rhythm to line up the beats. This how to video explains how to be a professional mobile DJ. This video explains a few points on how to approach the Mobile DJ industry in a more professional manner. Watch this DJ tutorial so you can learn how to be a professional mobile DJ.

Not sure what to do when you get a security warning about a macro? What are macro security settings, the Trust Center, and Trusted Locations anyway? Watch this instructional video to learn how to enable macros and make informed security decisions that can help you keep your computer safer while you work in Microsoft Office Excel, Outlook, Word, Publisher, PowerPoint, and Visio 2007.

Want to play old school Nintendo on your Windows Mobile devices, such as smartphones? Well, this video tutorial will show you how to install the NES emulator on that Windows Mobile electronic touchscreen device. Just sync up your cell phone, and download the software off of the Internet. Just think, you could be playing Mario in the palm of your hand, on your mobile phone.

A basic tutorial from InfinityExists.com on using Backtrack - the Linux-based security software package. This tutorial covers: Where to get Backtrack 2, How to burn an .ISO file, How to boot Backtrack 2, How to login, and start the GUI interface. It also illustrates basic Linux commands, and how to set up your Network Interfaces.

Learn how to set up the lighting rig of your mobile DJ set up - including proper light placement. Part 1 of 2 - How to Set up the lighting in your mobile DJ set up.

A look at how to set up your pa, mixer, turntables and amp in your mobile DJ setup. Part 1 of 2 - How to Set up the audio and PA in your mobile DJ set up.

During the recent Augmented World Expo (AWE), we had a chance to try out the Lenovo ThinkReality A6 AR headset. Unfortunately, the experience was all downhill from there.

While iOS 12 is arguably the best iteration of Apple's mobile operating system yet, one major fault so far is security. On Sept. 26, Videosdebarraquito discovered a passcode bypass that gave access to contacts and photos from the lock screen. Apple has since patched that security flaw, but Videosdebarraquito has discovered a new one that affects all iPhones running iOS 12.1 and 12.1.1 beta.