Welcome back, my neophyte hackers! Many newbie hackers seem to be confused regarding the process or methodology to employ a successful hack. Most want to simply go straight to the exploit without doing the due diligence to make certain that the hack will work and you won't get caught.
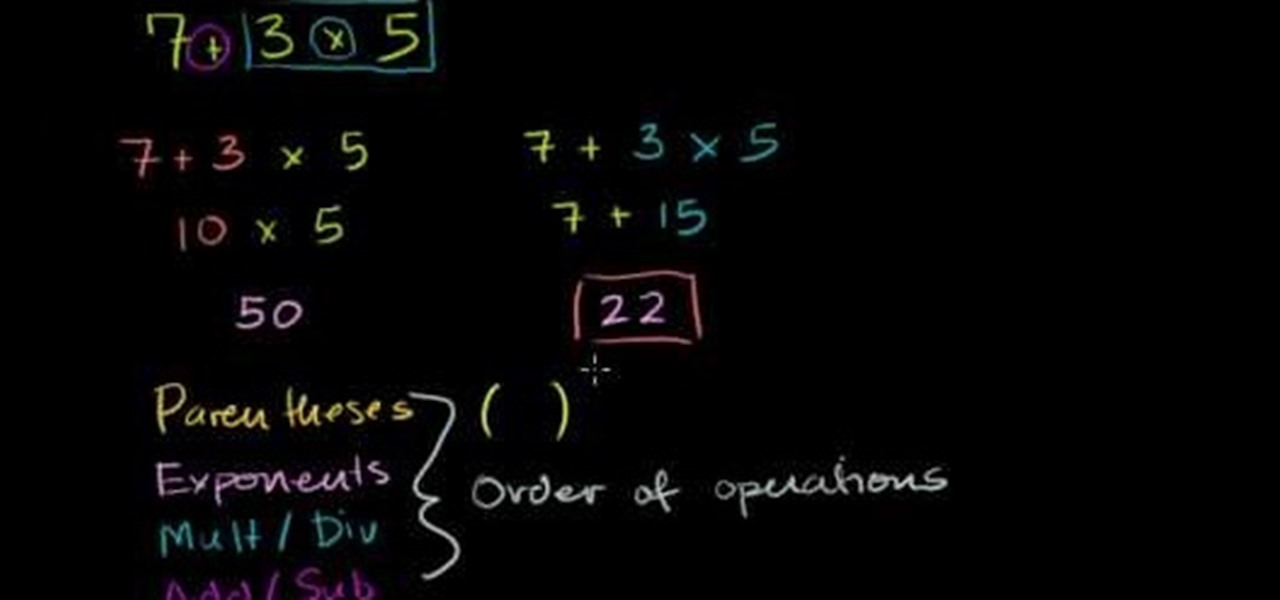
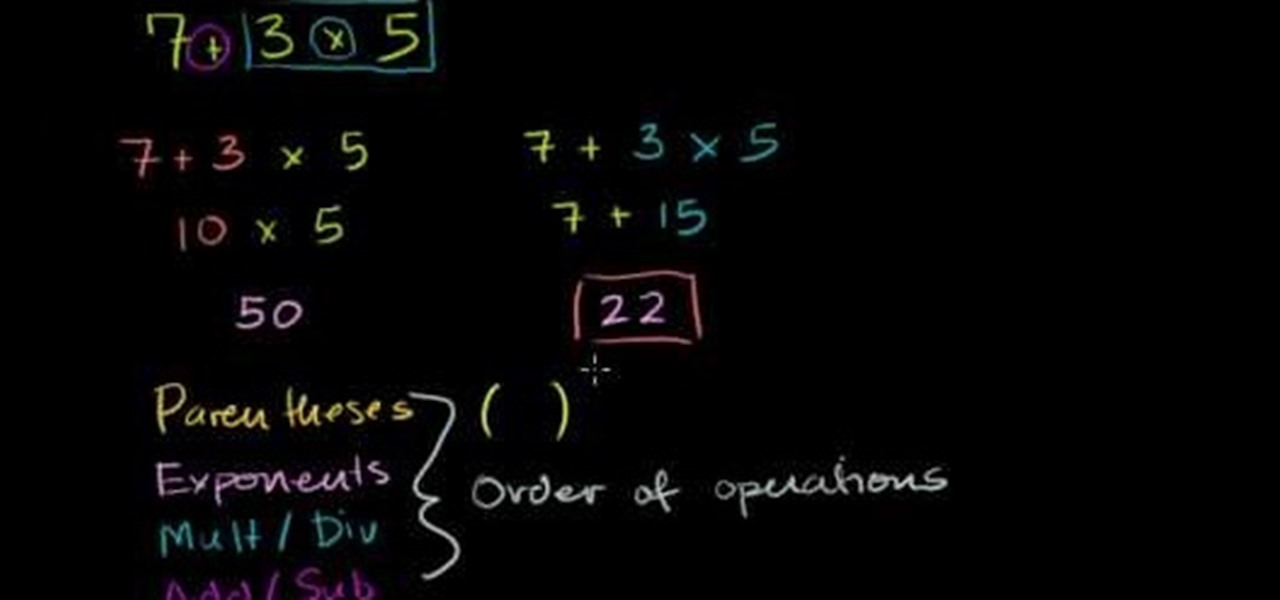
In mathematics, the order of operations define the priority in which complex equations are solved. The top priority is your parenthesis, then exponents, followed by multiplication and division, and finally addition and subtraction (PEMDAS). This video tutorial demonstrates the order of operation with various examples and explains the associated methodology. From Ramanujan to calculus co-creator Gottfried Leibniz, many of the world's best and brightest mathematical minds have belonged to autod...

Excerpts from a presentation by Dr. Simeon Hein at the International UFO Congress, 2005. Dr. Hein is the director of the Institute for Resonance in Boulder, Colorado. The Institute is devoted to the study of subtle-energy sciences including remote viewing, crop circles and related subjects. Dr. Hein has a Ph.D. in sociology and has previously taught research methodology and statistic courses. Dr. Hein first learned remote viewing in 1996 and subsequently became involved in crop circle researc...
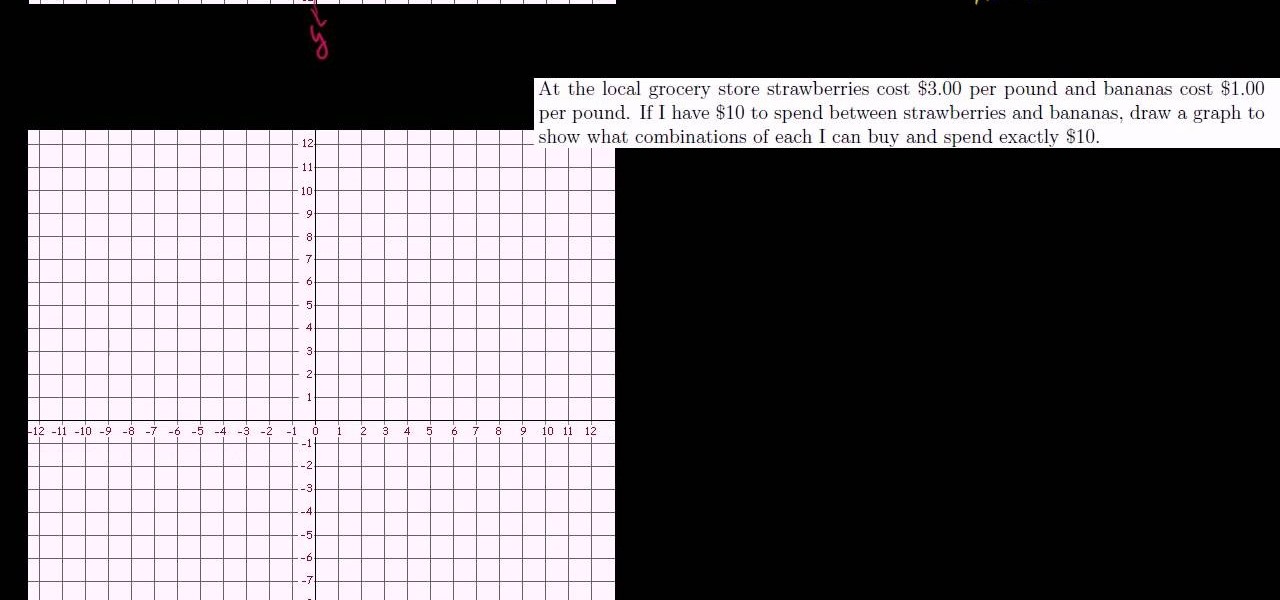
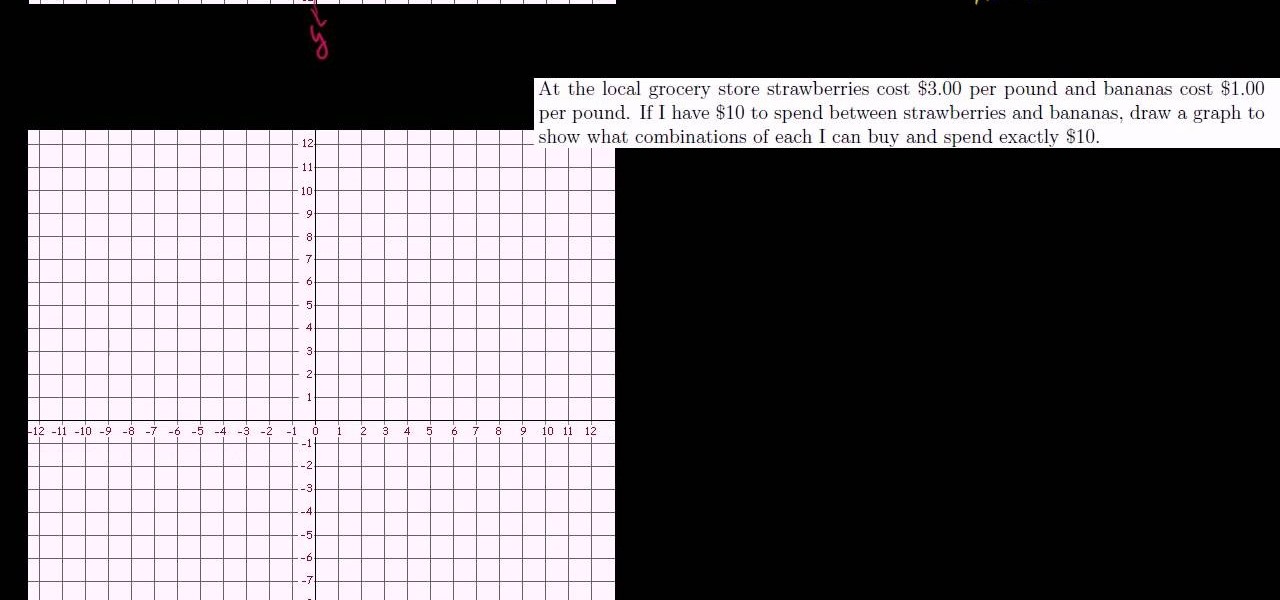
A line is defined by two connecting points on a graph, and intercepts are the points on both the x- and y-axis, where the line intersects. This video tutorial demonstrates how to graph lines using x and y intercepts in a given area. This instructional video also graphs various examples of equations and explains the associated methodology.
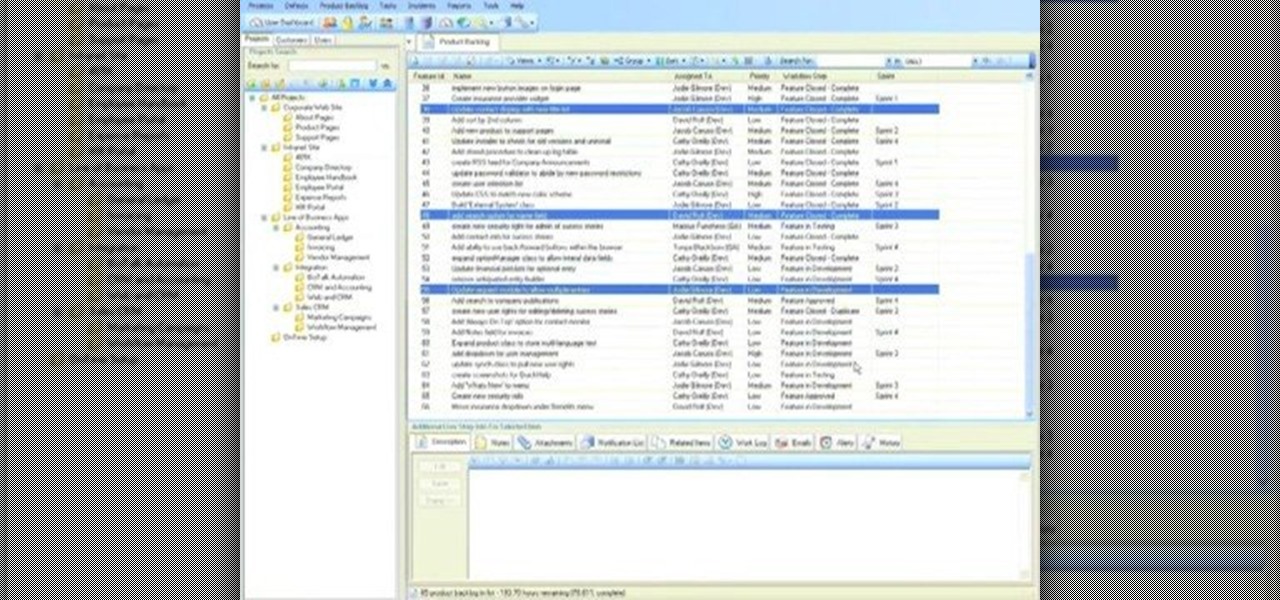
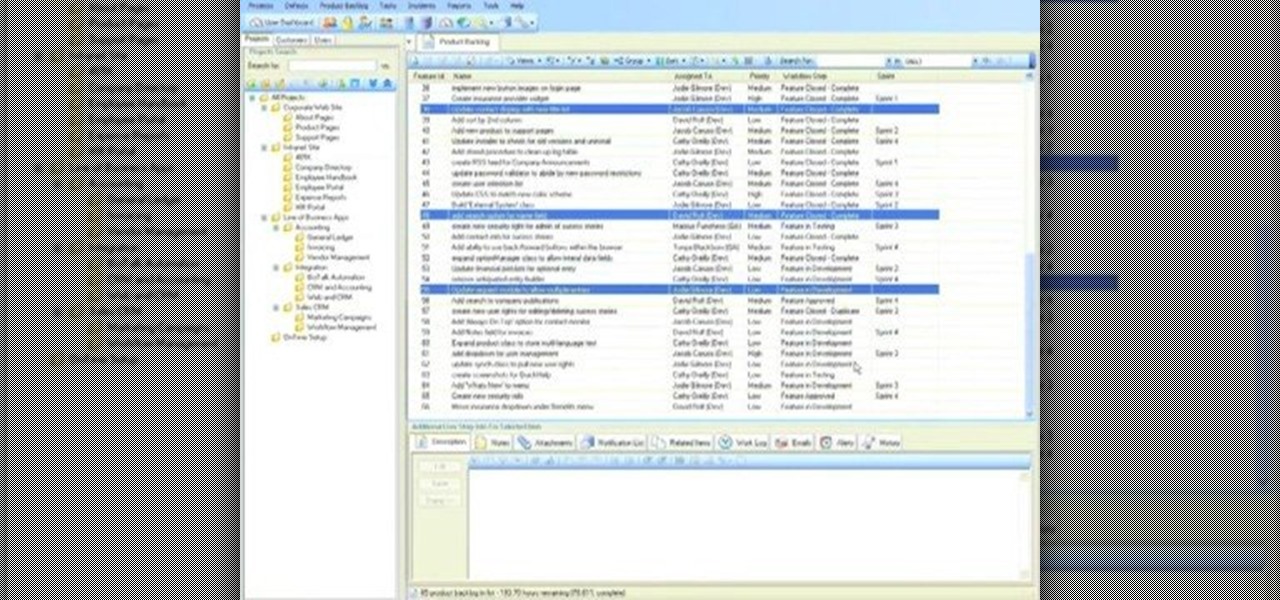
OnTime is such a flexible tool and it can be used in a variety of ways, with completely different methodologies. One of the methodologies that works well with OnTime is Scrum. This week we walk through a quick demonstration of setting up a new OnTime database for use with a Scrum methodology.
In this video series, you will take a look a the new Houdini 9 interface and learn how it will make your work faster and easier.

This is video footage of one step in the process of dressing a loom. This includes threading heddles and sleying reed. For a first-time weaver, setting up the loom can be 80% of the job. Many beginners actually enjoy dressing the loom more than weaving off the web. This comes about by careful work, techniques that have built-in double-checks, and efficient methodology.

A great technique for tempering chocolate on one you can do in the same bag you use for piping. Ideal to be used with a Water bath or Circulator but there are plenty of ways you can replicate this without those items.

Invented by Motorola engineer Bill Smith in 1986, Six Sigma's methodology defines a series of steps with specific value targets. These targets can be used, for example, to eliminate costs and process cycle time while increasing profits and customer satisfaction.

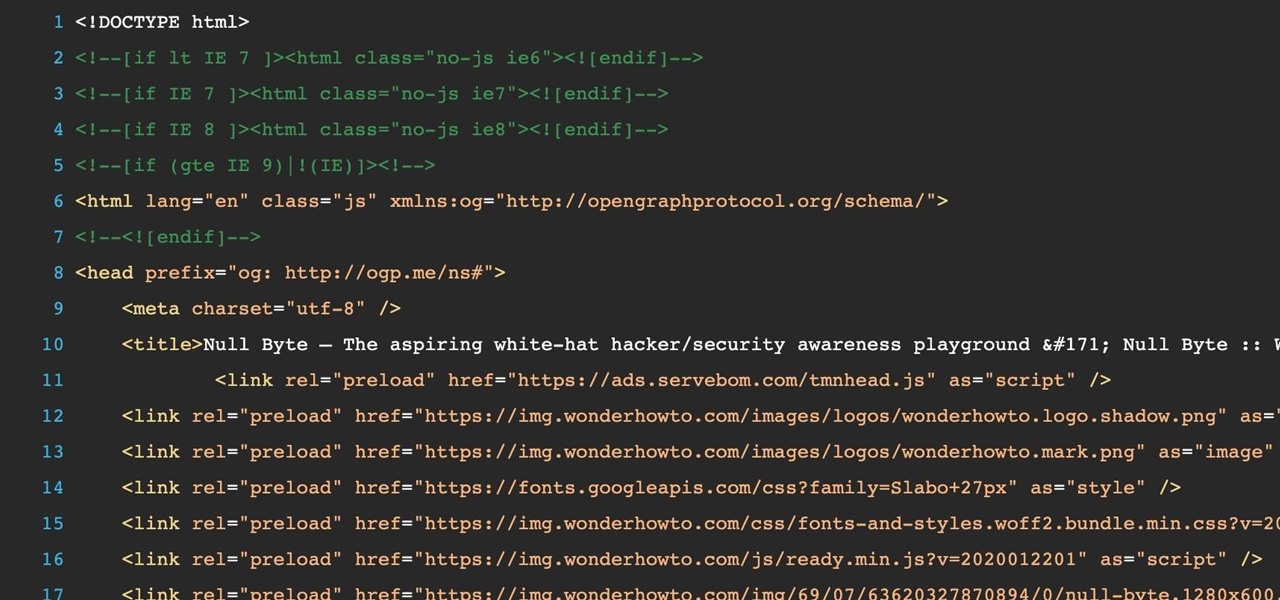
Since I first announced the new Null Byte recognition for excellence a few weeks ago, several of you have written me asking, "How can I study for this certification exam, and what material will be covered on the exam?" Now I have an answer for you. The White Hat Hacker Associate (CWA) will cover 14 domains or areas. Everything you need to know is here on Null Byte. There will be no questions that are not covered here on this site, guaranteed.

More and more tech-savvy leaders are flocking to the lucrative and exciting world of project management thanks to the high-pay, analytical environment, and nearly unparalleled flexibility. But this means that competition for the best positions in this dynamic field is fierce. If you want to stand out from the crowd, you're going to need to have more than a few base-level certifications on your résumé.

Facebook may have shamelessly copied Snapchat and its camera effects for faces (as well as its World Lenses), but it might beat its social media competitor to virtual body augmentation.

Smoked foods are popular all over the world, but most of us don't have smokers at home. If you want smoked salmon, brisket or Gouda, you usually have to go out and buy it. Outdoor smokers aren't usually an option for city-dwellers, and the indoor versions can be pricey.

The public leaks of NSA tools and information have led to the release of previously secret zero-day exploits such as EternalBlue, which was used in the notorious WannaCry ransomware attack. Despite multiple patches being released, many users have failed to update their systems, so many devices are still vulnerable to these now-public attacks.

New documents reveal that electric car company Tesla has filed a surprising new patent that has nothing to do with batteries or autonomous driving and everything to do with augmented reality.

Think back to when you last wanted to transfer some music or videos to your friend's smartphone and how difficult and slow it was. As powerful as our phones are, the default file sharing options are limited. There are, fortunately, some better options which make moving files easy, secure, and painless.

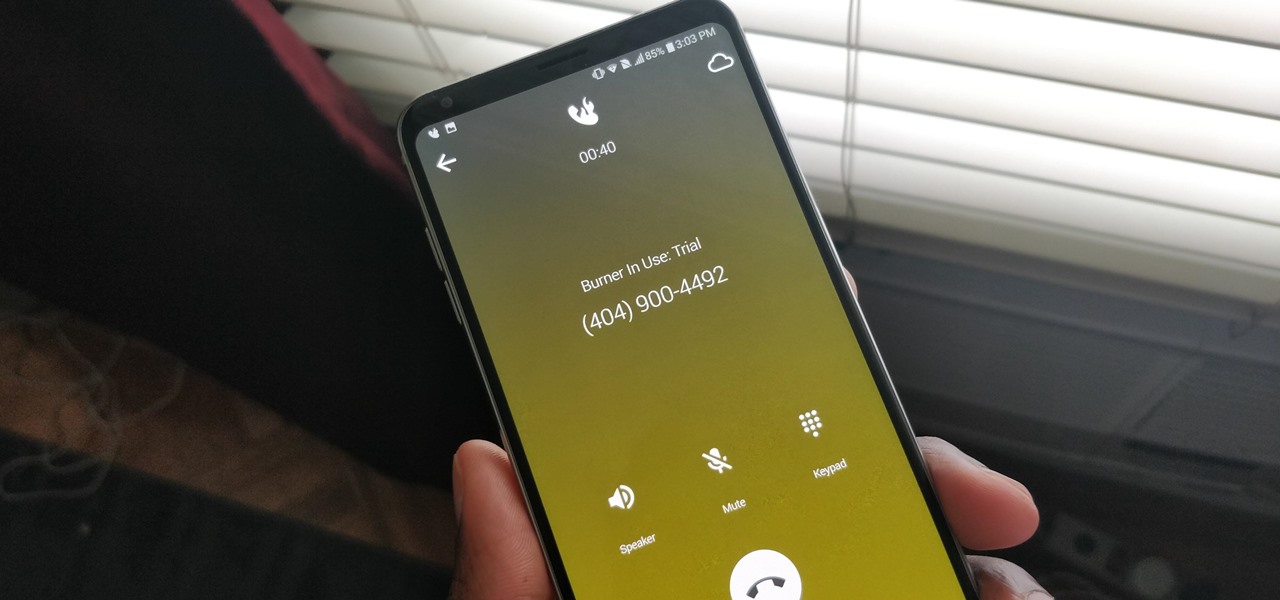
A burner number isn't just for criminals and cheating spouses. In this digital world, with many of our interactions being conducted online, a throwaway phone number acts as a buffer — it lets you enjoy the web without having to give out your personal information, such as real name or phone number.

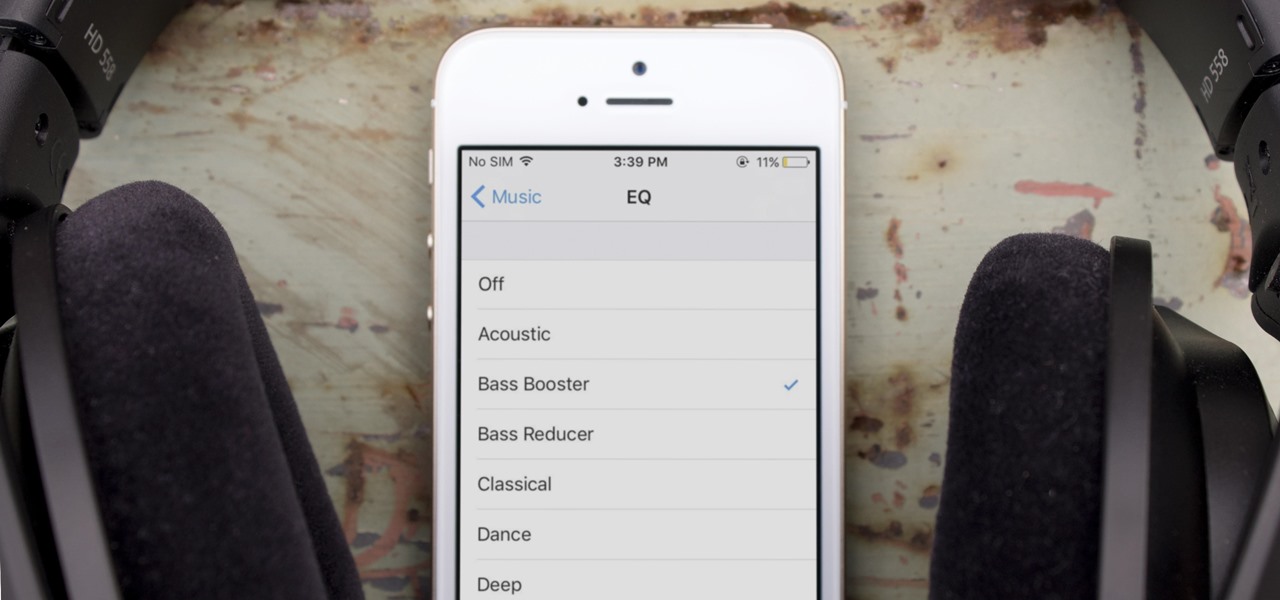
One of the most popular usages of modern-day smartphones is listening to music. It doesn't matter if you download or stream your tunes, you are part of a massive group of users who do exactly the same. While statistics are a bit foggy on how many smartphones users download music, we do know that over 68% of American smartphone owners stream music on a daily basis.

A few months ago, my friend Sarah appeared at a party bearing homemade liqueurs—amaretto, hazelnut (e.g. Frangelico), and vanilla liqueurs, to be exact. Her cool factor, which was already quite high, jumped up a few more notches—as did the overall energy of the party. (And that's why we call her 'Game Time.')

Penetration testing, or pentesting, is the process of probing a network or system by simulating an attack, which is used to find vulnerabilities that could be exploited by a malicious actor. The main goal of a pentest is to identify security holes and weaknesses so that the organization being tested can fix any potential issues. In a professional penetration test, there are six phases you should know.

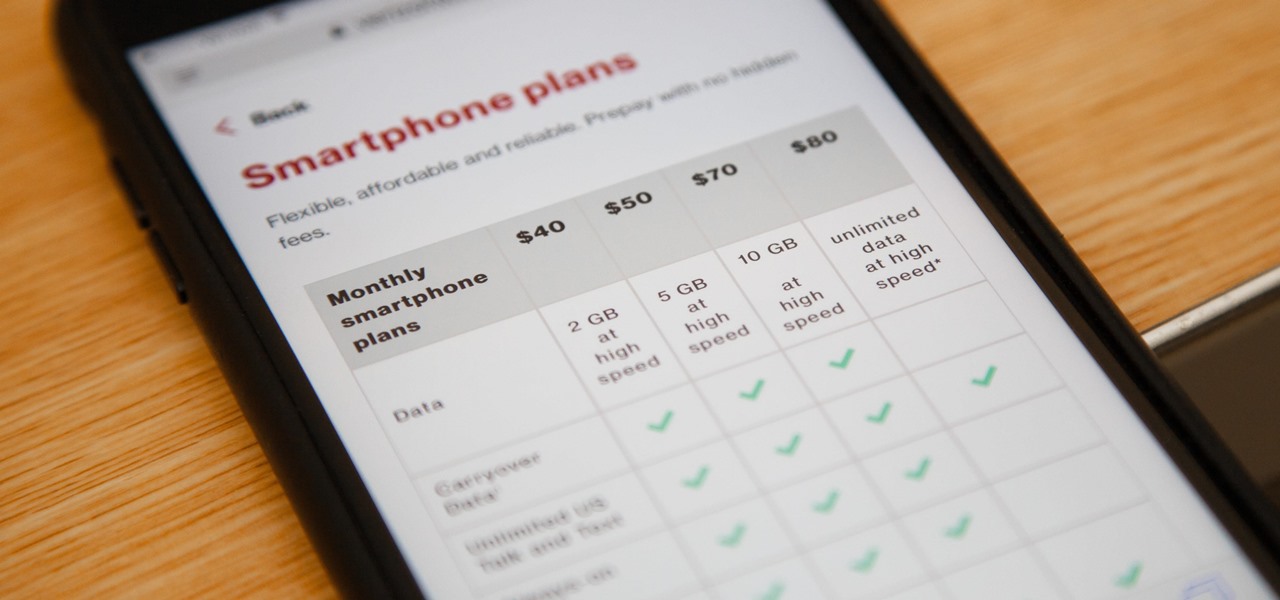
Verizon launched the $80 unlimited prepaid plan this week and we've found that it actually isn't as limitless as they would have you believe.

The web development landscape has changed dramatically over the past ten years. Both aspiring and seasoned developers now need to know a wide range of programming languages and platforms to create truly pro-level sites from scratch, and continuing education is vital if you want to stay ahead of the curve and be competitive in this increasingly popular and lucrative field.

It's no secret that learning how to code is one of the best things you can do if you want to land a high-paying career in a world that's heavily reliant on web and app development.

In 2018, Niantic unveiled its in-development augmented reality cloud platform for smartphones, the Niantic Real World Platform. A demo showed Pikachu and Eevee cavorting in a courtyard, darting in front of and behind potted plants and people's legs as they walked through the scene. This would be the future of Pokémon GO.

Privilege escalation is one of the essential skills a hacker can have and often separates the newbies from the pros. With a continually changing landscape and a plethora of exploits out there, it can be a problematic aspect of any attack. Luckily, some tools can help expedite the process. Linux Exploit Suggester is just one of many to help you get root.

There are two kinds of people standing in the international section of the grocery store: the kind who love Pocky and the kind who don't yet know that they love Pocky because they've never had it.

Social engineering is a pretty important item in a hacker's toolkit. In Mr robot there was a time, we saw Elliot using social engineering to gain access to his therapist's boyfriend's email and bank accounts by calling him and pretending to be someone from his bank, then Elliot asked him for some info that were really useful to gain access to his account, the target believed to be someone from the bank and gave him the info Elliot was looking for. But How Is It in the Real World?

So this is my methodology for this project of writing a rootkit. Please leave feedback on what is right/wrong. I tried to simplify concepts the best I could however...

Hi nullbytes! I've been recently reading the whole Linux Basics for the Aspiring Hacker series and felt like it was missing some stuff I know, so I felt like sharing it with anyone who might find it useful too.

The experience of actually using the HoloLens 2 can be difficult to describe to anyone who hasn't had a chance to directly interact with the device in person and be blown away by its immersive capabilities.

The development of virtual reality at Facebook has been evolving lightspeed in the last few years. But while a relatively small group of VR enthusiasts and gamers are enjoying the social media giant's dedication to immersive headsets, it is the augmented reality space and its potential scale that truly has the tech market enthralled.

If you need to scan a large number of domains for a specific web app vulnerability, Dorkbot may be the tool for you. Dorkbot uses search engines to locate dorks and then scan potentially vulnerable apps with a scanner module.

In my previous article, we learned how to generate a vulnerable virtual machine using SecGen to safely and legally practice hacking. In this tutorial, we will put it all together, and learn how to actually hack our practice VM. This will provide some insight into the methodology behind an actual attack and demonstrate the proper way to practice on a VM.

Welcome back, my tenderfoot hackers! As hackers, we often are required to get past antivirus (AV) software or other security measures. To do so effectively, we need to have some understanding of how AV software works. In this tutorial, we will take a cursory view of how AV software works so that you can better strategize on how to evade detection by it.

Hello readers, and welcome to Null Byte. Before we start, for those of you who may not know me, my name is ghost_; I'm a relatively active member of our community and have been around for a while.

In a way, Twitter is the town square of our era, where people can share and discuss ideas on a wide variety of topics. While the tech giant has its own app for Android, it's pretty bare-bones when it comes to features. This has paved the way for third-party clients that are rich with customization options.

The transcribing app can be an invaluable tool, especially if you're a student or are in a profession that relies on audio journals or interviews. These apps can convert important recordings like lectures and meetings into text for you to carefully read through to better comprehend.

Shodan calls itself "the search engine for internet-connected devices." With so many devices connected to the internet featuring varying levels of security, the special capabilities of this search engine mean it can provide a list of devices to test and attack. In this tutorial, we'll use Python to target specific software vulnerabilities and extract vulnerable target IP addresses from Shodan.

Back in the Nexus days, Google's approach to hardware was very different from most OEMs. You could say OnePlus swooped in with a similar mantra a few years later, focusing on great hardware at an affordable price tag. There were compromises, of course, but even then, it resulted in true treasures such as the Galaxy Nexus and Nexus 5.

Smartphones are inherently bad for privacy. You've basically got a tracking device in your pocket, pinging off cell towers and locking onto GPS satellites. All the while, tracking cookies, advertising IDs, and usage stats follow you around the internet.