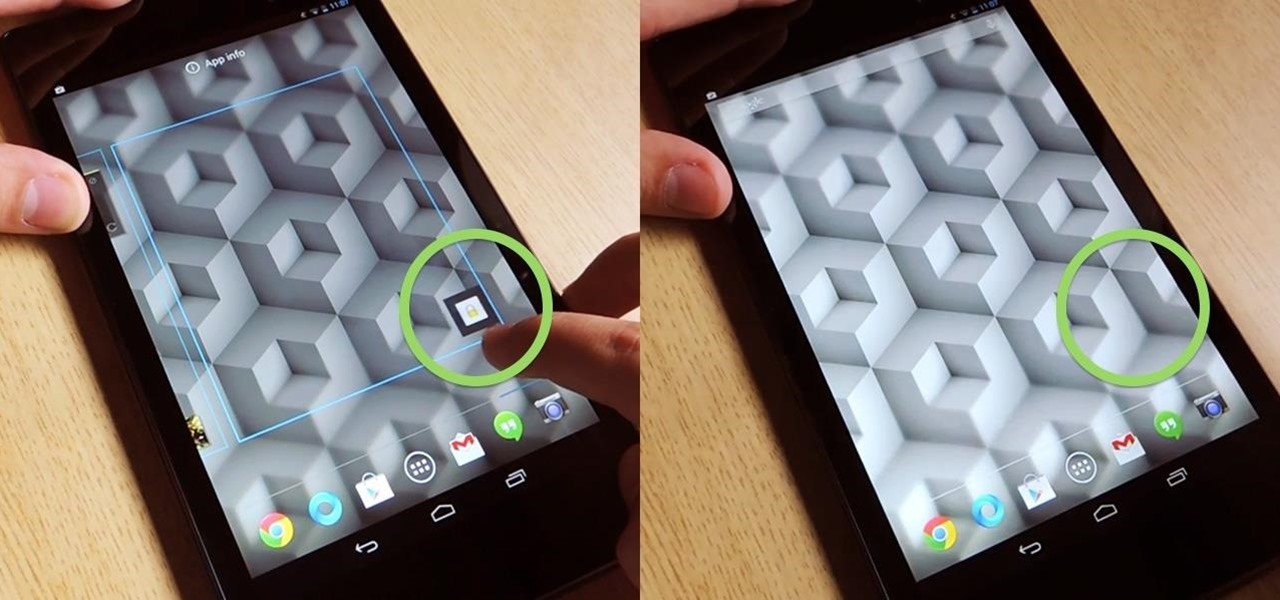
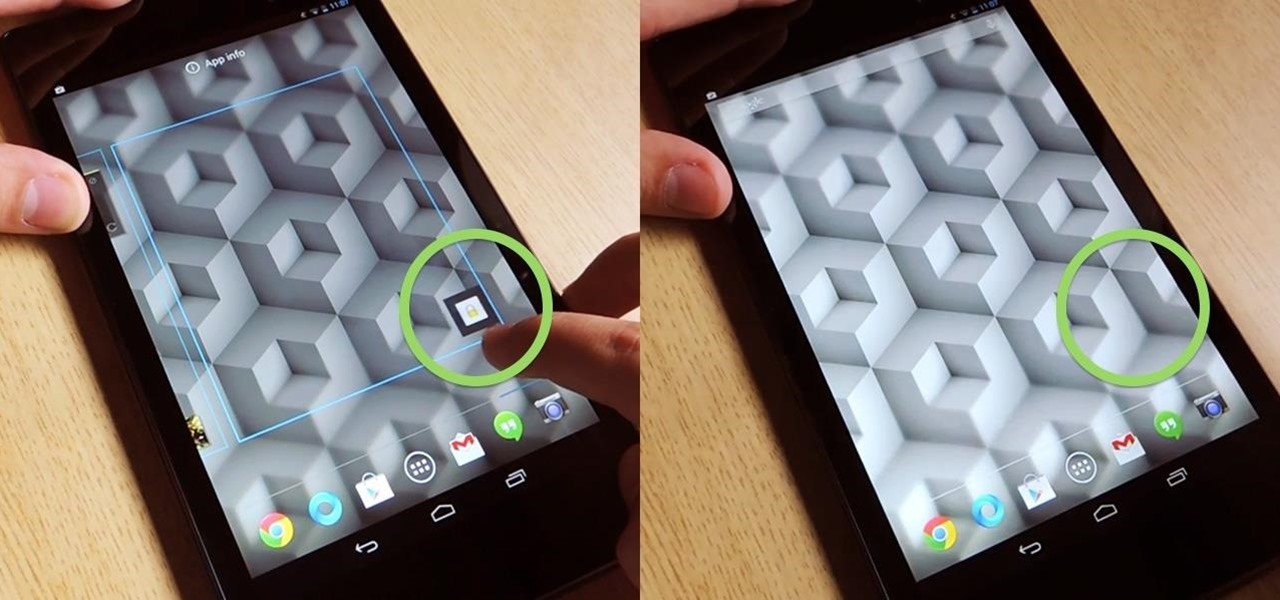
How To: Lock Your Nexus 7 Directly from the Home Screen with an Invisible Locking Shortcut
Overall, I love the Nexus 7 tablet, but one thing that I truly dislike about it is having to press the Power/Lock key to lock my screen.

Overall, I love the Nexus 7 tablet, but one thing that I truly dislike about it is having to press the Power/Lock key to lock my screen.

In this web design tutorial you will learn how to manage web design layers efficiently by using solo mode, hiding layers and locking layers. This Xara Web Designer tutorial will show you the importance of using these features to manage your website design.

Yep, Google just put in place a new thing called the dun dun duuuun .... "Device Catalog!" No, not like the Macy's catalog of your smartphone dreams. This is quite the opposite.

You've protected your Ubuntu system from physical attacks, annoyed network hackers, and sandboxed potentially malicious applications. Great! Now, the next logical steps to locking down your OS include thoroughly auditing Ubuntu for weak points, using antivirus software that respects your privacy, and monitoring system logs like a boss.

Once you've installed Ubuntu with security in mind and reduced the possibility of network attacks on your system, you can start thinking about security on an application level. If a malicious file is opened on your system, will an attacker be able to access every file on the computer? The chances are much slimmer if you put the proper defenses in place.

Hacker's are always looking for new ways to exploit systems and exfiltrate passwords, even in hashed form. Sophisticated brute-force attacks powered by high-end GPUs can perform millions of password attempts per second. But Ubuntu and Debian users aren't completely helpless. There are ways to harden the hashed password to better defend against Hashcat attacks.

Windows 10 and macOS have poor reputations when it comes to customer privacy and user policies. Our hacking Windows 10 and hacking macOS articles might make it seem like a reasonably secure operating system doesn't exist. But I'm here to tell you that there is a viable alternative that could provide some sense of security and trust.

After installing Ubuntu as your primary OS, you should have protected against USB Rubber Ducky payloads, defended against hard drive forensics, and reduced the overall attack surface against physical strikes. When defending against network-based attacks, you'll want to minimize hardware disclosures, prevent packet sniffers, harden firewall rules, and much more.

In this video, we learn how to install a locking hardwood floor with Lowe's. First, prepare the sub floor before you begin installing the floors. After this, grab all of the tools you need to install the flooring properly. Place spacers between the flooring and the walls and start to lay it down. Lock the planks together on the first row. Then, lock the sides to the next row and use weights to keep the floors from moving. The ends must be 6 inches apart on each row. For a locking floor, cut o...
As a follow-up video to inference locking, this Google SketchUp tutorial shows how to combine a series of roof forms together using inference locking. You will also use arrays and copying to create dormers. Please keep in mind, this isn't a video on roofs, but an example of various inference locking techniques and how they work in Google SketchUp.

Locking tuners make guitar playing much easier. Essentially, locking tuners keep you from having to constantly tune and retune your instrument by keeping the chords locked in place.
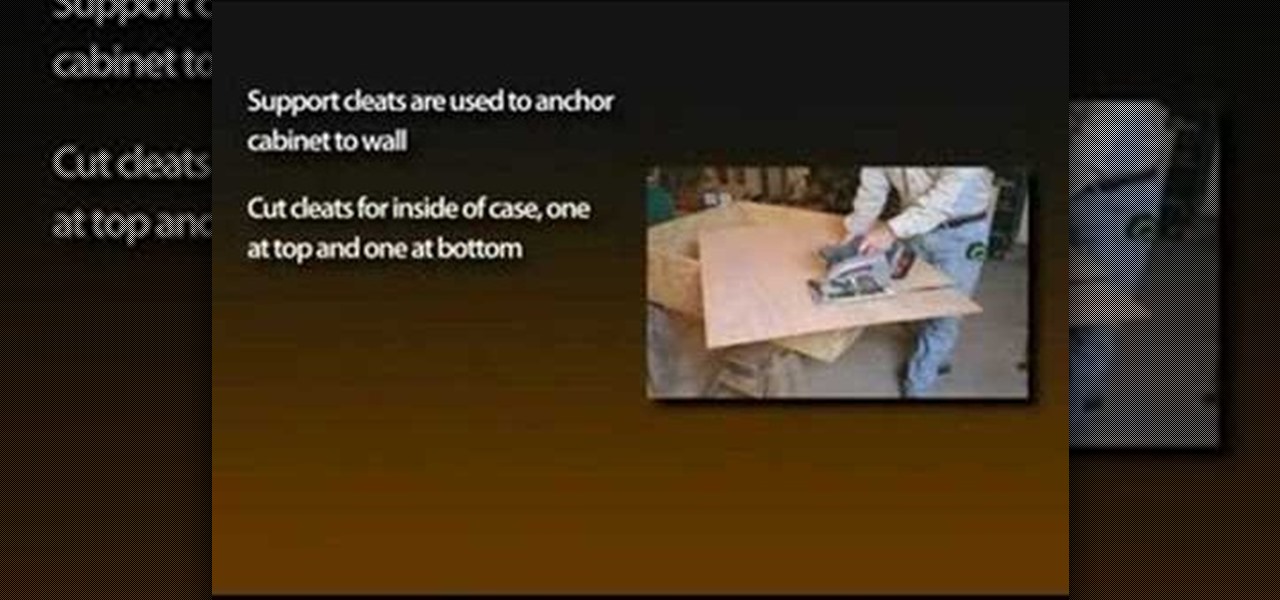
With the growing popularity of cordless power tools, it's extremely easy these days to accumulate a lot of portable tools, and when you add in quality corded tools, such as circular saws, routers, planers and air nailers, you can end up with a pretty hefty investment. These same tools are the first to “walk away” in a theft. Left lying around a shop or garage, they can also be somewhat dangerous for youngsters. A locking cabinet not only provides a secure place, but protects the tools as well...

This locking tutorial teach you about some dancing movements by Shawn Phan in his own style. He describes some small things while dancing a few basic movements that are missed during dance steps. At first he gives a short description of dancing steps that he is going to describe through this locking video tutorial. He gives a simple idea to dance better and easy steps to do to make the dance more funky. Those who watch dancing and those who dance always expect something amazing in the perform...

Creepers and zombies aren't very smart, but if you're on a multiplayer server for Minecraft, you're going to want to be able to protect your stuff! Here is how you can construct a locking door using cobblestones, an iron door and redstone.

What are the names of basic picks? How do you use them? Check out this instructional con video that provides an overview of the basic pins used in lock picking. All picks can be put into two basic categories, raking picks and single pin picking picks. Learn the names of the various picks and how to use them with this tutorial video. Learn the basics and start lock picking like a pro!

The SportRack bike rack lock kit can be easily added to many of the SportRack model racks. It includes two locks, one that secures the bikes to the rack and another that locks the rack to your trailer hitch. It only takes a minute to install and is dead simple to use, as this video demonstrates.

Did you buy a car and find out the wheels are held on with wheel locks and you don't have the key? Or perhaps you lost the key to your own wheel locks? This tutorial shows you how to use the Dynomec locking wheel nut remover to remove wheel locks without damaging the wheel or the nut. The Dynomec locking wheel nut remover should be used for removing your vehicle's wheel locks and NOT to steal others. Use the Dynomec locking wheel nut remover.

Getting locked out of a bedroom or bathroom can be a real bummer. Fortunately, these locks are easy to "pick" and get yourself in. This how to shows you clearly what to do to get yourself back inside so you don't feel frustrated all day long. This excellent video takes you step by step through the process. This video talks about 2 different types of locks and the two different types of tools you'll need.

When picking a padlock, the only part you need to worry about is the part where the key goes into the lock. The locking mechanism has pins attached to springs. The key pins are on the bottom and the driver pins are on the top. The key turns when the pins of different heights are separated, flush and aligned. Stick a tension wrench into the keyway and put pressure on it. Take a pick to push the rest of the pins up until they are flush with the shear line. Stick the tension wrench into the bott...

Many have tried to prove (or disprove) that tennis ball lock picking really works, but it still seems up for debate. Mythbusters have supposedly debunked this technique (watch the video). Someone over at the Auto Blog also has tested this car lock method with failed results (watch the video).

In this tutorial, learn how to get a little bit of Droid on your iPhone. You will get a step by step on how to install the Android locking screen on your iPhone 3G or 3GS. This requires a jailbroken, Cydia-enabled phone and a little work, but the cool effect is totally worth it. Check it out!

If you want to lock your iPhone's screen position in one place to make it easier to read when laying down or whatever you're doing, you can actually do it. This video will show you the steps to locking your Apple iPhone's screen in place. You need to open up Cydia and search for "Rotation Inhibitor". Simply install Rotation Inhibitor, restart the SpringBoard, then open up Cydia again and click on "Future Packages" and install "SBSettings". Then re-Spring again.

Looking to enter the world of the pop & lock? Learn the difference between the two with help from this free lesson. In dance, popping is all about popping the body by flexing muscles and grinding shoulders, while locking is a way to cut off flowing movements.

Ever wanted to learn how to pick a lock? Well, there's no better time than now to start learning the craft of so many locksmiths out there... lock picking. Just watch this video tutorial to see how to bypass security wafers when lock picking.

The Next Three Days is the new film by Paul Haggis (Crash), which stars Russell Crowe and Elizabeth Banks. Laura (Banks) is accused of murder and sent to prison, and her husband John (Crowe) struggles to prove her innocence while taking care of their only child. But the system does not work for John, and he's forced to take extreme actions and attempt a prison break.
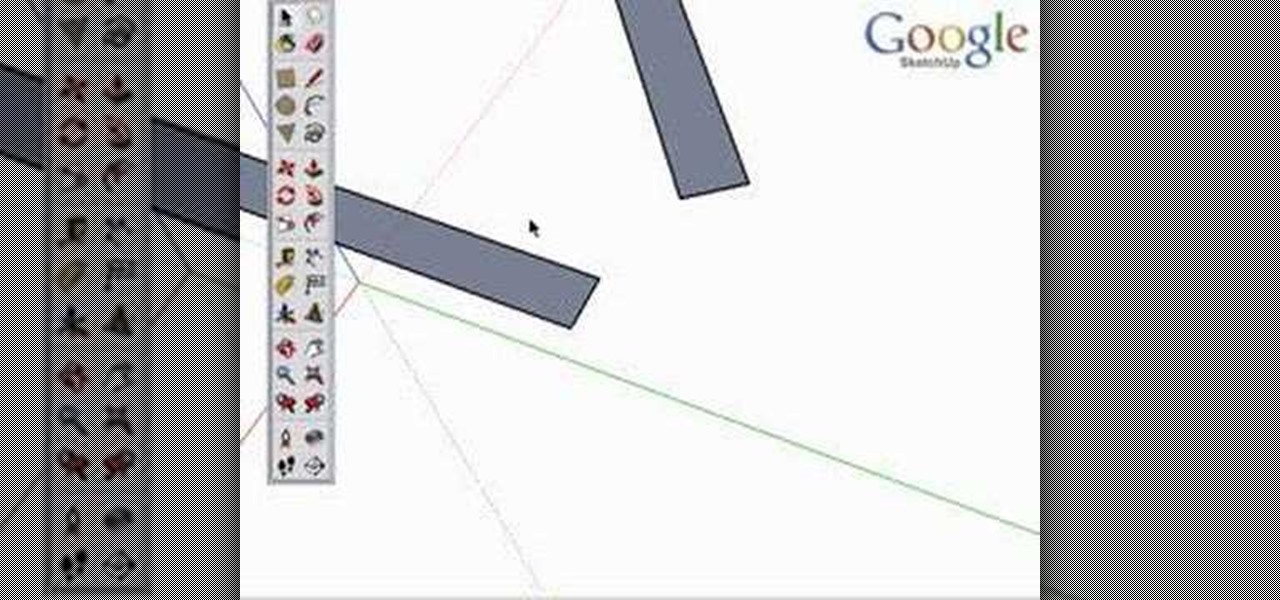
Inference locking is the ability to draw or move in only one locked direction in SketchUp. This SketchUp tutorial will teach you how to use the inference lock technique and show a few examples of inference locking in use and the advantages it has for modeling and navigating the SketchUp viewport.

Nothing can ruin a nice bike ride like getting your bike stolen. Improperly locking your bike or just leaving it unattended is a sure way for it to be stolen.

We now officially have a new use for Coke cans that has out-cooled Lady Gaga's Coke can curls from her video for "Telephone."

Want to make sure that a document isn't accidentally edited or overwritten? It's easy; you just need to lock the file. All you need to do is right-click on the file, expand its general information, and check the Locked box. For a video walkthrough of the file locking process in Mac OS X, watch this video lesson from Apple.
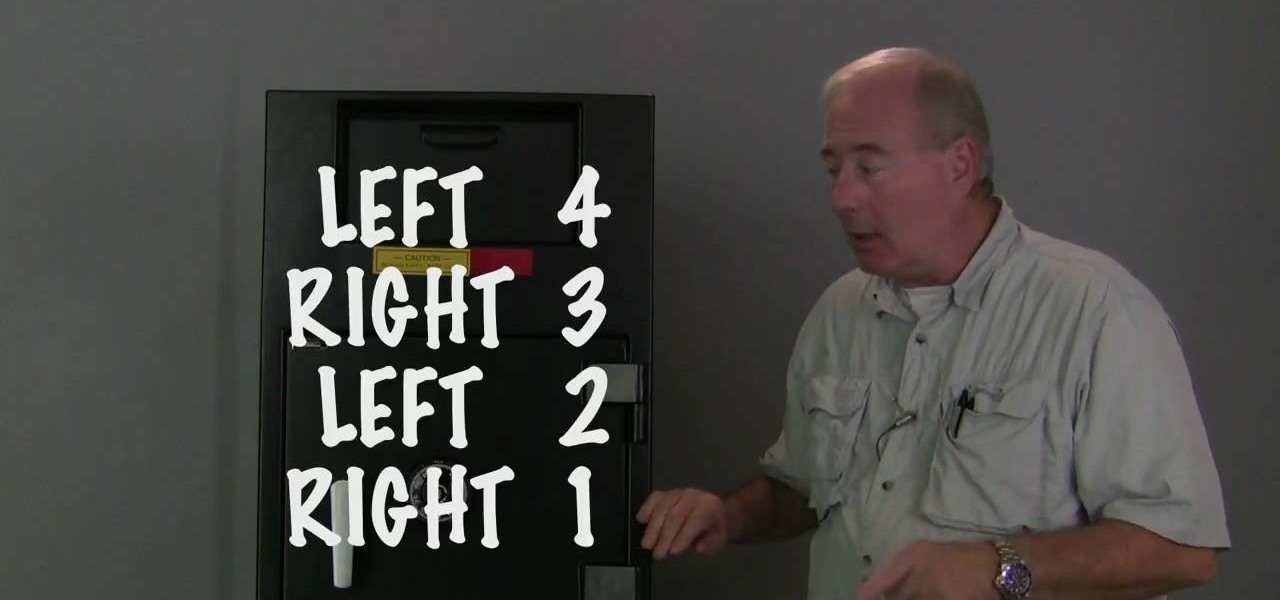
In this video tutorial, viewers learn how to dial open a combination safe lock. Begin by turning the lock 4 times to the left. Then turn the lock 3 times to the right. Now turn the lock 2 times to the left and finish by turning it one more time to the right. Users should hear and feel a click when they finish turning the lock. When locking the safe, turn the lock 4 or more times to the left. to ensure security. This video will benefit those viewers who have a safe lock and would like to learn...

Check out this instructional con video that demonstrates how to bypass a master lock number 17 in this locking picking tutorial. This technique will work on both old and new combination locks. They all use the same mechanism. Learn how to bypass a master lock number 175 with this tutorial con video. Start picking locks like a pro!

Want to show a friend something on your iPhone but don't want them messing up your Angry Birds game or peeking at your private emails? Enter Locktopus, the perfect solution to locking your iOS apps from prying eyes. The only catch—you need to jailbreak your iPhone.

A spare key is one of those things that never seems like a huge deal until you need it. If you've ever lost your keys, had them stolen, or locked yourself out of your house or car, you know how difficult and embarrassing it can be trying to get your door open.

Locking individual apps on your Android device gives you an added layer of security by safeguarding app data from unwanted attention. I personally prefer using an app locker over a standard lock screen because my kids play with my phone, and they've completely disabled it after inputting the wrong PIN. So app lockers give me the right balance between giving my children access to my device, and the security of locking down my data from would-be intruders.

By Zech Browning Shihan of Gyodokan Martial Arts. Step 1: "Storm Within the Calm - Putting It All Together - Part 1"

Locking your keys inside of your car is frustrating, to say the least, especially if you're in a hurry to get somewhere. You can always call AAA roadside assistance or a locksmith, but you'll probably have to fork over some money, as well as wait for them to get to you. You might even get towed.

There is no default option on iOS 16 or iOS 17 to lock your apps behind Face ID, Touch ID, or passcode authentication. However, a clever, easy-to-implement workaround will protect your sensitive apps from nosy friends and family temporarily using or looking at something on your iPhone.

Keeping prying eyes off your device isn't always the easiest thing to do, especially once you lend somebody your phone to make a call. Seems that whenever someone is scrolling through your pictures or checking out your new phone, they always end up somewhere you don't want them be. You could always hover over their shoulder to make sure they're not getting into your texts or photos, but that isn't always possible.
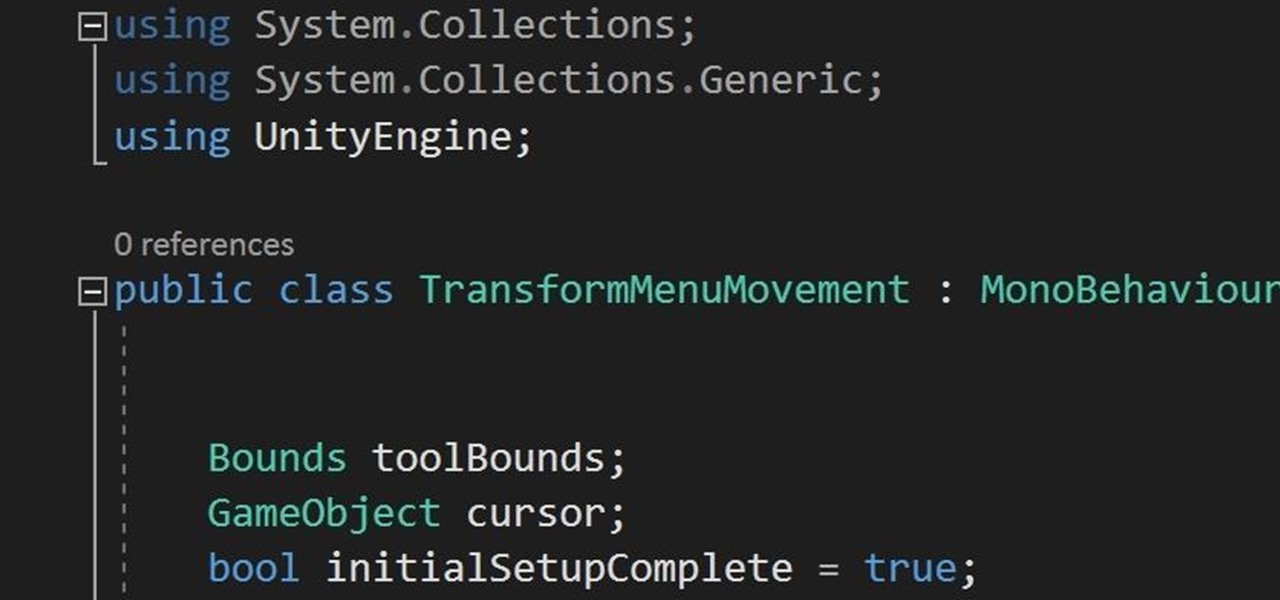
In the previous section of this series on dynamic user interfaces for HoloLens, we learned about delegates and events. At the same time we used those delegates and events to not only attach our menu system to the users gaze, but also to enable and disable the menu based on certain conditions. Now let's take that knowledge and build on it to make our menu system a bit more comfortable.
There are those who hold their phone or set it down when they're not using it, and others, like myself, who pocket it. If you're like me and are rocking the pants pocket fade, then you'll love the new Android app I found.