Rope seizing is a technique that is used when two things need to be held together with rope, like two pieces of timber for example. This video from ITS Tactical demonstrates how to use some cord to perform rope seizing on a big, heavy rope so that you can use it to suspend an object or perform other heavy rope-using tasks.

In this keyboard tutorial, you'll learn how to play LL Cool J & Boyz II Men's "Hey Lover" on the piano. While this tutorial is best suited for intermediate or advanced piano players, players of all skill levels can play along. Watch this tutorial to get started playing "Hey Lover"!

Killzone 3 is the biggest shooter to hit the PS3 in quite some time, and one of it's few awesome unique IPs. This video will teach you how to not be a n00b in this awesome game while using the Marksman (hint: spawn trapping), Infiltrator (stabby stab), Engineer (helps Marksman with ammo for more spawntrapping), Medic (revives Marksman for more spawntrapping), Tactician (spawn-point seizing) classes. Spawn

Need to know how to tie a Bowline with a few ways of securing it? This way shows you how to secure it with a seizing so that it won't accidentally come undone. Included is a little variation of the bowline with a built-in seizing. If you don't have electrical tape to secure the bowline feed the bitter end back through the hole. It also makes it so you don't have a tail line dangling if you're towing something.

Making chocolate covered pretzels can be a snap. The main ingredients needed include: pretzels, chocolate ganache, heavy cream, and a little bit of butter. Those ingredients ll come together to help make a delicious snack perfect for any tailgating party, baby shower, or just because. So sit back and enjoy this easy tutorial on how to make delicious chocolate pretzels.

Watch to learn how to say the numbers from ninety to one hundred in French. quatre-vingt-dix - ninety

Watch to learn how to say the numbers from seventy to eighty in French. soixante-dix - seventy

Watch to learn how to say the numbers from one to twenty in French. un - one

By slow cooking all your ingredients in a crockpot, you can have a complete pot roast dinner ready to eat in no time. Learn how to season the pot roast in a crockpot and make a simple gravy to top off this hearty meal. You"ll need boneless beef, top round, olive oil, potatoes, baby carrots, beef broth, worcestershire sauce and cornstarch.

Layering becomes a necessary skill to know during the fall and winter, when it's nigh impossible to get away with wearing just your favorite dress or t-shirt and nothing else.

This project may be more for you than your kids, but that doesn't mean your children won't have fun constructing this awesome crafts project! You can teach your kids about recycling, and build something wonderful and useful. A notes organizer is also a great idea for getting organized in life. To make this, you"ll need:

This video details how to survive a knife threat from behind. When threatened from behind with a knife, do not attempt to move the body first, this will result in the attacker maintaining the capability to thrust the knife into the body. When threatened, place arms out and low in a submissive position, this is to be followed by moving the left arm backward in a sweeping motion to push aside the arm which is holding the knife. Once the arm is moved, turn the body and bring the elbow up into an...

In this next tutorial, you're going to want to make sure you have plenty of time on your hands. That's because this boss battle is pretty long. You'll be going one on one with the sand boss Stygian. He's a giant, ugly worm that takes some time to defeat. On top of him, you;ll have to battle a bunch of enemies who are on foot.

Nothing is more frustrating that finding yourself out on the open sea and having to manuever around a bunch of stuff lying around in your boat. Not only can it be hazerdous, but also very annoying. So what do you do? Install a storage bag or course! In this tutorial, you;ll find out how to easily install a CE Smith t-top storage bag on your boat in little to no time. Now all your stuff can be easily put away and easily accessible. Enjoy!

This tutorial is for those who own an iPod Touch 3G. In this video, find out how to unlock it with a 3.1.2 firmware. This is a tethered jailbreak and means you;ll have to run the program back rain everytime you turn your device on, off, or reset it. Be aware, that whenever you do something that messes with the software in a device, there is always the potential of dying or breaking so be careful Enjoy!

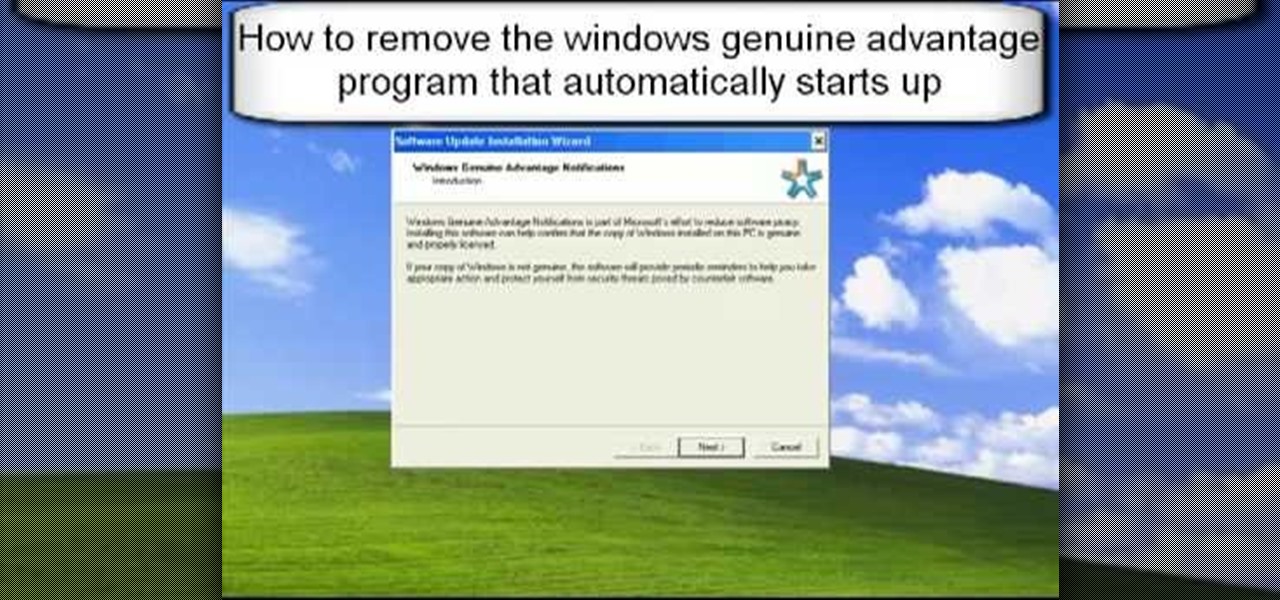
1. First go to START -> ALL PROGRAMS -> ACCESSORIES -> SYSTEM TOOLS -> SCHEDULED TASKS.2. Right click on WGA setup icon and select PROPERTIES. Find where the WGA files are located.3. Copy the location form the window appears in the previous step and paste it in the address bar of MYCOMPUTER.4. Delete the files found in the respective location.5. After deleting the files, now delete the WGA found in the scheduled task.6. RESTART the windows and windows genuine advantage ll not disturb again.

It's a timeless doggie no-no, and one that has been paradied in numerous dog scenes in movies: A plate of delicious fried, steaming food is left by the owner on the table. The owner then leaves for a brief moment. His dog, smelling the delicious goodness, seizes the moment and quickly jumps up, snatches a piece of chicken, and devours it under the table.

English can be difficult because few words are spelled phonetically, and every rule has exceptions. But you can become a champ in no time by memorizing a few basic rules.

One day, your car may break down and you won't be able to afford to hire a mechanic, so what do you do... you look on the web for some how-to vehicle repair videos and become your own car mechanic, that's what. You don't need any advanced training to perform repairs and simple maintenance on your automobile, but you may need a few tools. Invest in the basic tools and you'll be prepared for just about any car malfunction you can think of. These tutorials will help get you on your way, as long ...

Crostini is the Italian word for toast and is basically a fantastic canvases to put almost anything on top of to make easy and tasty hors d’oeuvres. This video will show you some crositini using Italian ingredients or other flavorful combinations. Watch this video to learn how to make a simple crostini. Great for picnics and parties! 12 slices firm white bread 5 tbsp. (75 ml) butter 2 tbsp. (30 lL) all-purpose flour 1/2 c. (125 ml) milk 3 oz. fresh mushrooms (about 9 med.), finely chopped 6 t...

The Cloud Security Alliance (CSA), a leading IT trade association, has published its first report on risks and recommendations for connected-vehicle security, ahead of when driverless cars are about to see volume production in the near future.

The increasingly important world of white hat or "ethical" hacking is getting competitive. Thanks to growing salaries and opportunities for talented and trained coding pros who can infiltrate servers and safeguard networks against digital threats, demand for intrepid cyber warriors is through the roof, and it shows no signs of slowing down any time soon.

There are all kinds of theories—many supported by science—about what causes Alzheimer's disease. Tangles of protein called ß-amyloid (pronounced beta amyloid) plaques are prominently on the list of possible causes or, at least, contributors. An emerging theory of the disease suggests that those plaques aren't the problem, but are actually our brains' defenders. They show up to help fight an infection, and decades later, they become the problem.

Welcome back, my aspiring hackers! In this series, we continue to examine digital forensics, both to develop your skills as a forensic investigator and to avoid the pitfalls of being tracked by a forensic investigator.

We use smartphones for just about everything, and while that may be beneficial to us in our day-to-day lives, it can also be used against us in the court of law.

Cruise Automation, General Motors' (GM) driverless car arm, has hired two hackers who were once seen by many as a safety threat to help find vulnerabilities in its self-drive car network.

How to Concrete in a Post: Step 1:

This truck repair video shows you how to remove the bed from a Chevrolet C1500 W/T truck. This needs to be done to fix certain problems, in this case the fuel lines. Whatever reason you need to remove the bed from your Chevy, this video shows you how to do it properly.

The camera system on the iPhone has never been better. Apple's iPhone 11, 11 Pro, and 11 Pro Max sport some of the best shooters on the market. But no level of quality makes up for the fact that shady apps can access your cameras for nefarious reasons. You can take control of the situation, however, and block any app you want from using your rear and front-facing cameras.

The Unity 3D engine is not only responsible for facilitating the creation of 60% of AR and VR content but it also plays a significant role in producing the immersive stories that increasingly push the boundaries of cinema.

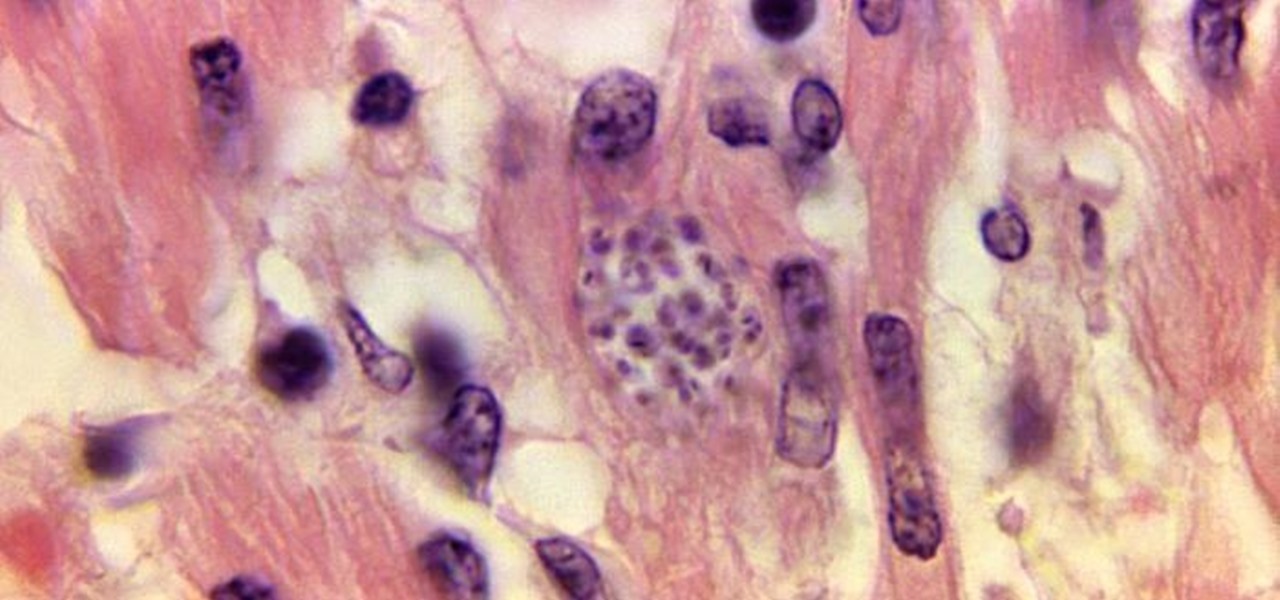
For the first time, the US Food and Drug Administration (FDA) has approved medication to treat children with a serious infection called Chagas disease, which stealthily infects and damages the hearts of millions of victims a year.

Tesla founder and CEO Elon Musk offered some insight into how hackers might seek to turn driverless cars into zombie fleets, but remained upbeat about what can be done about it.

There are a few key ingredients that you always need on hand when baking cookies and other desserts, but when you run out, you run out. You either have to stop what you're doing and go to the grocery store, find a good substitute, or scrap the project entirely. Chances are, you'll never accept defeat, and why go to the store if there's a good substitute on hand?

This week, Silk Road was shut down for good when the FBI seized the anonymous online marketplace after Ross Ulbricht, aka Dread Pirate Roberts, was arrested. This comes just two weeks after another illegal marketplace called Atlantis shutdown. However, there are plenty of other black markets hiding within the Deep Web, freely and anonymously accessible using the Tor browser.

A vulnerability in the design of LiDAR components in driverless cars is far worse than anything we've seen yet outside of the CAN bus sphere — with a potentially deadly consequence if exploited.

A man-in-the-middle attack places you between your target and the internet, pretending to be a Wi-Fi network while secretly inspecting every packet that flows through the connection. The WiFi-Pumpkin is a rogue AP framework to easily create these fake networks, all while forwarding legitimate traffic to and from the unsuspecting target.

The next-generation Audi A8 to launch in July is expected to be the world's first Level 3-capable production car to go on sale in retail channels.

Welcome back, my greenhorn hackers! In many cases when a computer, phone, or mobile device is seized for evidence, the system will have graphic images that might be used as evidence. Obviously, in some cases these graphic images may be the evidence such as in child pornography cases. In other situations, the graphic images may tell us something about where and when the suspect was somewhere specific.

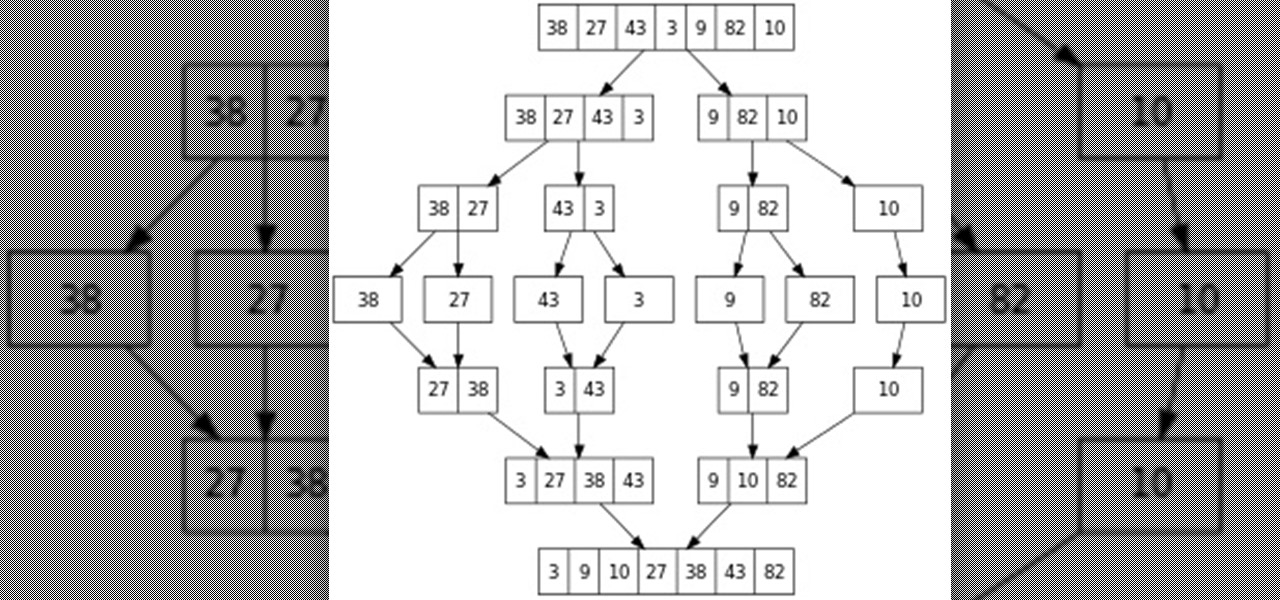
Hello everyone! This is part 7.0 of my Sorting series. I know, I said last time that there would be a 6.1, but not just yet!

Fall is the time for comfort foods—and what is more comforting than crusty bread slathered in melted cheese? Owning a fondue pot is both convenient and wonderful, but not all of us have the luxury of space for nonessential kitchen appliances. However, there are plenty of ways to make an absolutely delicious, lump-free fondue without the traditional equipment.