Beauty is pain, and there's no better proof of this aphorism than high heels. Whether they're a measly two inches or a whopping six inches, high heels are undeniably the most fabulous and effective way to visually lengthen your legs and make your calf muscles look slim. They come in gorgeous designs and colors and are many gals' favorite fashion accessories. But oh yeah, there's one snatch: they're a pain in the ass to wear for longer than half an hour.

In this tutorial, you will learn how to turn gracefully in heels. This lesson is taught Lady Ellen of Le Femme Finishing School in NJ for transgendered individuals. Watch this how to video and you can walk and turn gracefully in heels.

Handstands are hard to do in general, whether you're a yoga veteran or a little tyke trying to impress his friends in P.E. Yoga junkies, however, possess a much butter control of the muscles that hold a handstand in place, including the core and arms.

Learn how to do the kip up to get to your feet easily under you. It is a move from gymnastics, parkour, and breakdancing that artists use to leap gracefully to their feet.

Have you ever tried to play lothario to a girl at a club and turned her ever so gracefully, only to misjudge her height and clotheslining her in the face? With minimal lighting and swarming, uncomfortable crowds of people, it's no surprise that any sort of graceful dancing at all is difficult in a club, but it's possible to avoid lawsuits if you learn the dance move presented in this video.

Everyone loves a party—until the host’s pooch starts giving your leg a little bit of his doggie style. Show that canine he’s not humping any old bitch.

Watch and learn a basic tutorial on how to make a card vanish, using a back palm. Follow along with an aspiring young magician as he gracefully shows the technique. Hint: It's all about the hands.

In this video, Becca explains and demonstrates how to walk in high heels. Becca is neither a model nor has been professionally trained. The tips and tricks shown in the video are her own techniques after rigorous practice and experience. She suggests to start with a very short pair of heels. She explains about the weight factor when walking on heels, which can affect the posture. She says that a lot of women go wrong when they try to walk on heels as if they were walking flat footed. She also...

Watch this instructional poi video tutorial to leran how to spin the Low Same-Direction Reels trick. This video is for beginners who have conquered basic spinning techniques.

How to get your hula hoop from your waist up above your head, relatively gracefully, and then to "lasso" the hoop above you.

As many of you may have heard, Apple's new iOS 9 is "rootless", which supposedly would make jailbreaking much more difficult. However, it has been shown to be possible. ih8sn0w posted a youtube video of his jailbroken iphone running iOS 9 and even gave some hints about it in the video description section. However, he also stated that he will NOT be releasing it to the public. So it would be quite the feat and adventure to take his hints and comments and use that to figure out how to jailbreak...

I have a lot of favorite kitchen tools. My seven-inch Global chef's knife is my baby. My pasta maker is my dance partner on any given Friday night. My girlfriend's stand mixer is my favorite toy in the apartment.

Easter may have come and gone, but my love of hard-boiled eggs sure hasn't. Yet as much as I love hard-boiled eggs, I hate making them; I have to work in small batches to have consistent results, and they're always a little overdone, crumbly, and sometimes even green.

Greasy fast food. Snacks. Candy. Empty stomachs. What do these all have in common? They're all things that people commonly have for lunch during the week, because it beats the hassle of having to plan, make, and pack lunches before their workday.

If you're a developer in the augmented and mixed reality space, there's a high probability that you're intimately familiar with the 3D application and game engine Unity. In May, at VisionSummit 2017, Microsoft announced that 91% of all HoloLens applications have been made with the software. But there's a section of Unity that you may not be familiar with, which has become very important to augmented, mixed, and virtual reality (known collectively as XR, for "extended reality") — Unity Labs.

Salt is one of my favorite ingredients, by far, and also one of the most overlooked foods in the kitchen. This is probably due to the fact that it's an essential component of almost any recipe; because salt is a necessity, it's easy to forget how dynamic and versatile it can be as well.

With a simple social engineering trick, sudo passwords can be captured in seconds without the target's knowledge. The passwords can then be saved to a file or exfiltrated to another computer on the network.

Using Netcat to backdoor a macOS device has its short-comings. If the compromised Mac goes to sleep, the Netcat background process will occasionally fail to terminate correctly; This leaves Netcat running infinitely in the background and the attacker with no new way into the device. As an alternative, we'll use the lesser-known Tcl shell which can handle abrupt backdoor disconnections.

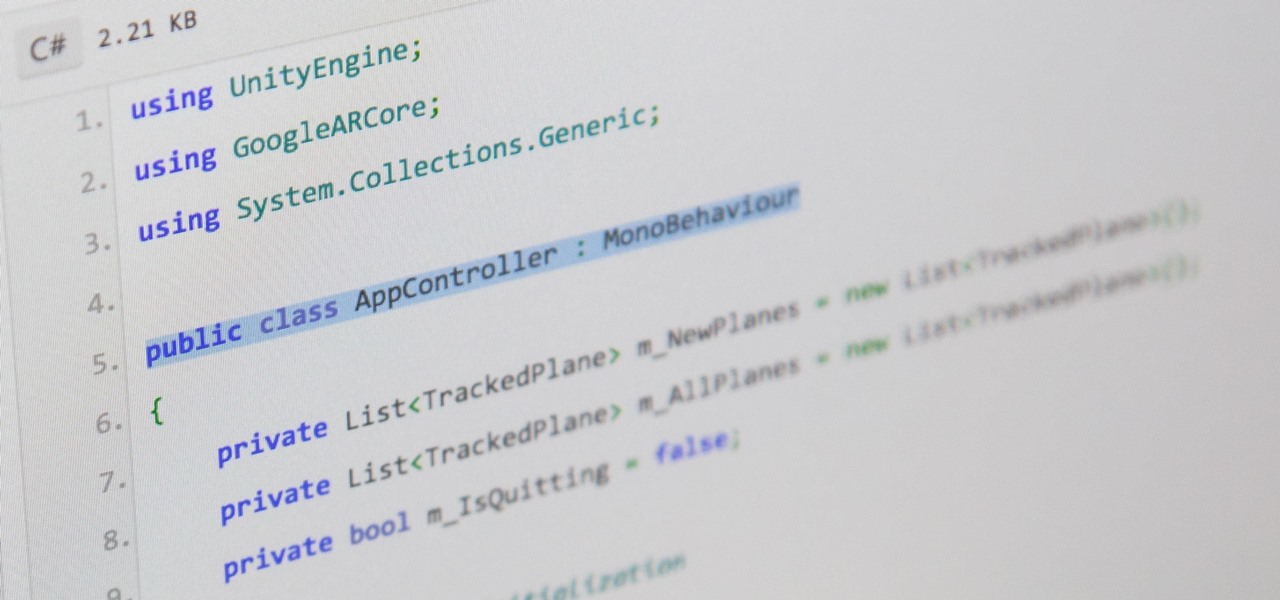
There are hundreds, if not thousands, of programming languages and variations of those languages that exist. Currently, in the augmented reality space, it seems the Microsoft-created C# has won out as the overall top language of choice. While there are other options like JavaScript and C++, to name a few, C# seems to be the most worthwhile place to invest one's time and effort.

If you need a tiny, flexible attack platform for raining down human-interface-device (HID) attacks on unattended computers, the USB Rubber Ducky is the most popular tool for the job. By loading the Ducky with custom firmware, you can design new attacks to be effective against even air-gapped computers without internet access. Today, you'll learn to write a payload to make "involuntary backups" through copying a targeted folder to the Ducky's USB mass storage.

Way back, life on the range was tough and unforgiving for a HoloLens developer. Air-tap training was cutting edge and actions to move holograms not called "TapToPlace" were exotic and greeted with skepticism. The year was 2016, and developers had to deploy to their devices to test things as simple as gauging a cube's size in real space. Minutes to hours a week were lost to staring at Visual Studio's blue progress bar.

Here's how to make dry-ice at home, or wherever you feel like it! All you need is a pillow case, and a CO2 fire extinguisher.

The iPhone 15, iPhone 15 Plus, iPhone 15 Pro, and iPhone 15 Pro Max are Apple's most powerful iPhones to date with features like USB-C connectivity, improved camera capabilities, and faster CPUs. But no matter how impressive these phones are, they can still freeze, become unresponsive, or get stuck when powering on — and a force restart is how you get things working again.

Web application vulnerabilities are one of the most crucial points of consideration in any penetration test or security evaluation. While some security areas require a home network or computer for testing, creating a test website to learn web app security requires a slightly different approach. For a safe environment to learn about web app hacking, the OWASP Juice Shop can help.

After a hacker has configured Metasploit on a remote private server, created a resource script for automation, and created a simple payload, he or she can begin the process of remotely controlling someone's Windows 10 computer with just a few moments of physical access — even if the computer is off.

The latest film addition in the American-produced Millennium series, The Girl in the Spider's Web, was just released on Blu-ray a few days ago. As you could expect, the movie has many hacking scenes throughout, just like the previous English and Swedish language movies centered around hacker Lisbeth Salander. Of course, with the quick pace of some scenes, the hacks can be hard to follow.

Individually addressable LEDs, also commonly called "NeoPixels" after the popular Adafruit product, are a bright and colorful way to get started with basic Python programming. With an inexpensive ESP8266 or ESP32 microcontroller, it's easy to get started programming your own holiday lighting animations on a string of NeoPixels with beginner-friendly MicroPython!

In this game, Black loses in 17 moves. Watch and listen to the debrief of the game, to see how to win or lose gracefully.

Inception may not be the lead contender for the 68th Golden Globe Awards, honoring the best movies and television from 2010, but Christopher Nolan's film still collected four nominations— Best Motion Picture, Best Director, Best Screenplay and Best Original Score.

You've had a massive hard disk failure.. ...in your PC or laptop and like a large number of people who think it will never happen to them...you did not have a backup of those 2000+ family pictures, those hundred of important Word documents, those family videos that you downloaded from the camera then erased from the cameras disk...the inevitable "I'm Screwed!'

Fingerboarding has never looked so high fashion. Gracefully orchestrated advert by Hermès.

Part Globetrotter, part Baseketball, our boy Q-Mack is a straight-up baller. He's got several tricks that will either earn you mad street cred or a technical foul.

Introduction In this post we will look at how to access a PosgreSQL database in your C/C++ application. It's not as hard as you might think, but you need to understand the procedure and the functions used.

Before you go running off to the Apple store, you may want to educate yourself. DVICE is kind enough to compile the 20 biggest complaints about the iPad from a whole slew of reviewers.

Minecraft is unique among computer games in that some users have created such breathtaking works of beauty and ingenuity that it challenges the very idea that Minecraft is even a game at all, but suggests that it is instead a tool for artistic expression much like Photoshop.