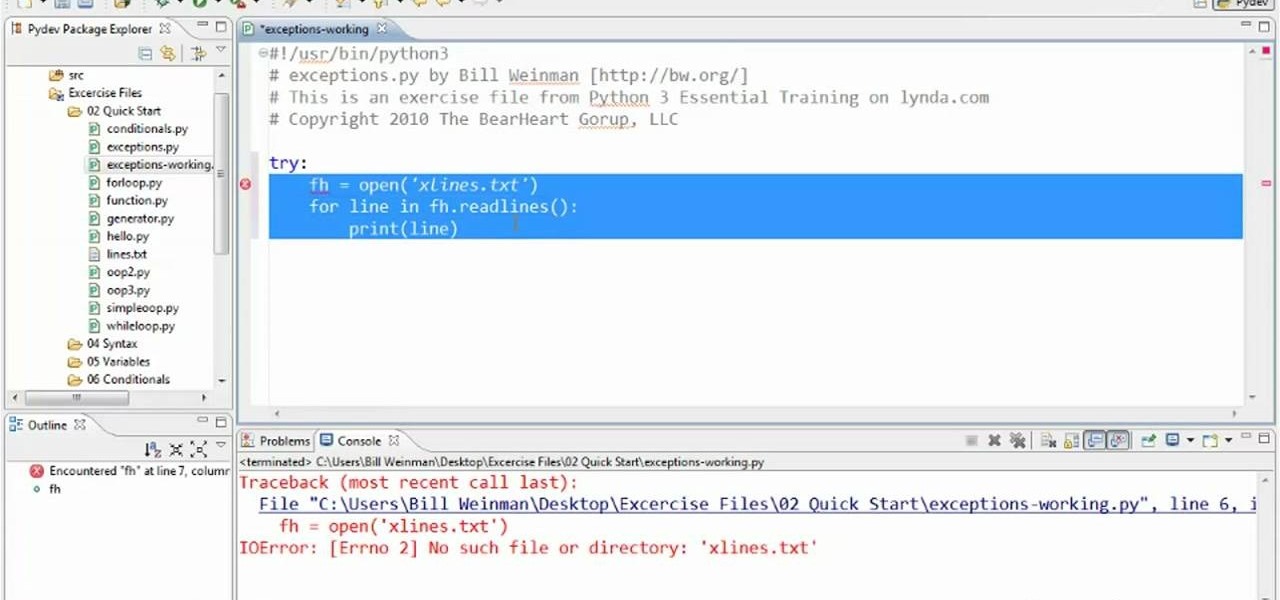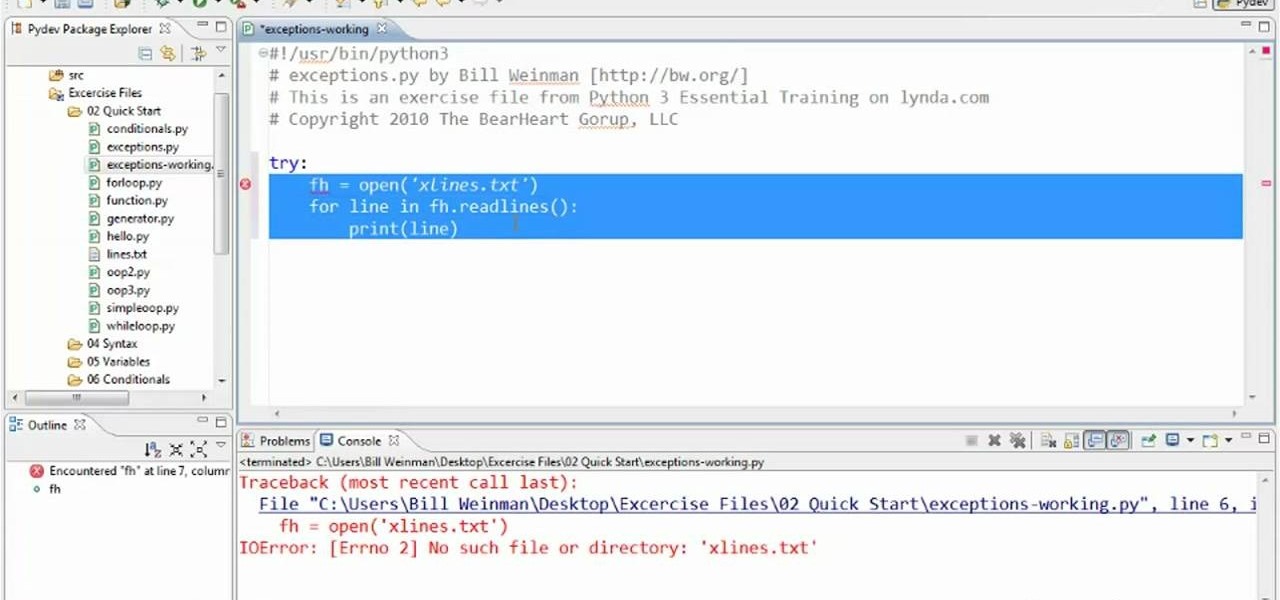
In this clip, learn how to use exceptions to handle errors when programming in Python 3. Whether you're new to the Python Software Foundation's popular general purpose programming language or a seasoned developer looking to better acquaint yourself with the new features and functions of Python 3.0, you're sure to benefit from this free video programming lesson. For more information, including detailed, step-by-step instructions, watch this video guide.
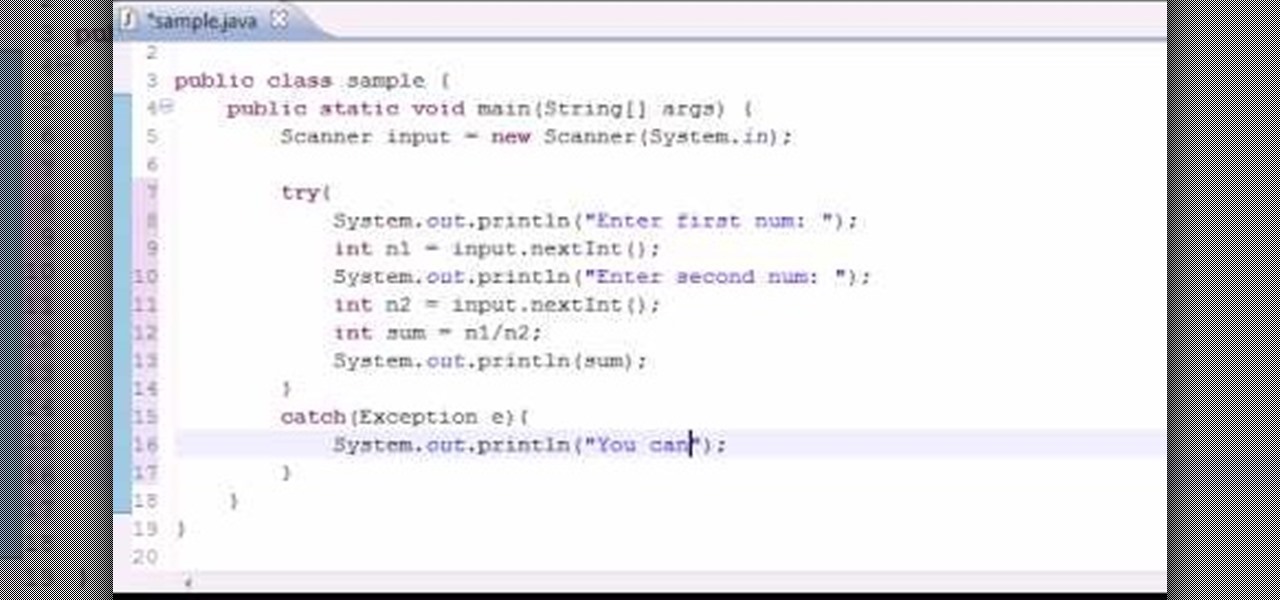
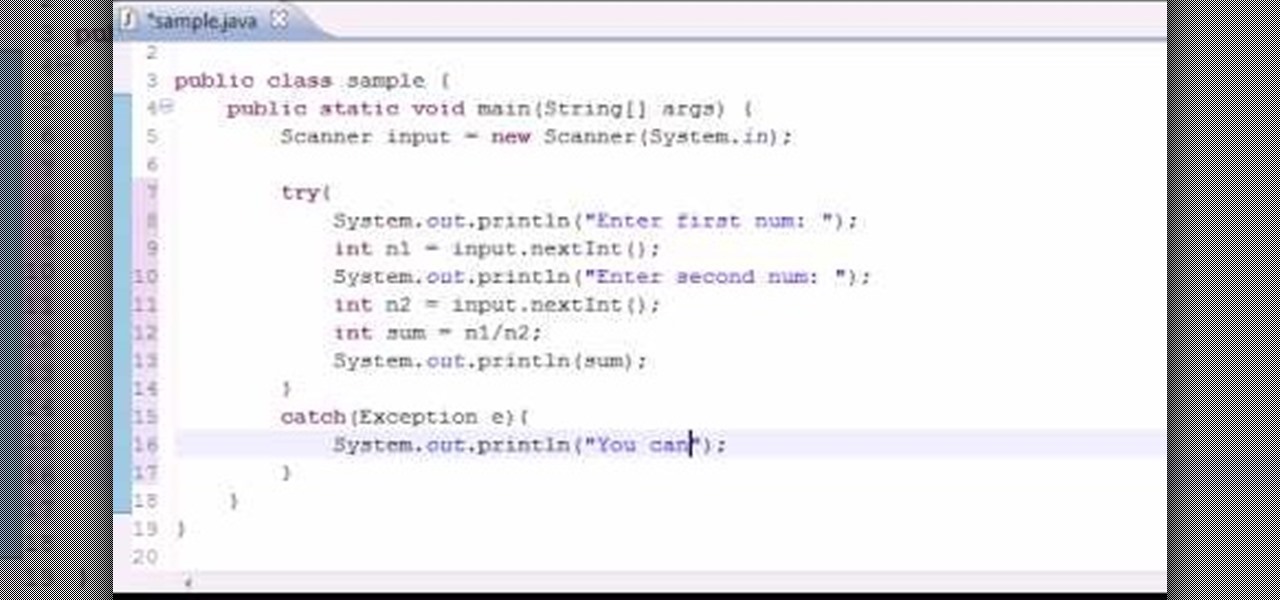
Want to program your own Java games and applications but don't know beans about object-oriented programming? Never you fear. This free video tutorial from TheNewBoston will have you coding your own Java apps in no time flat. Specifically, this lesson discusses how to to troubleshoot errors and exceptions when writing code in the Java programming language. For more information, including detailed, step-by-step instructions, watch this helpful programmer's guide.

English can be difficult because few words are spelled phonetically, and every rule has exceptions. But you can become a champ in no time by memorizing a few basic rules.
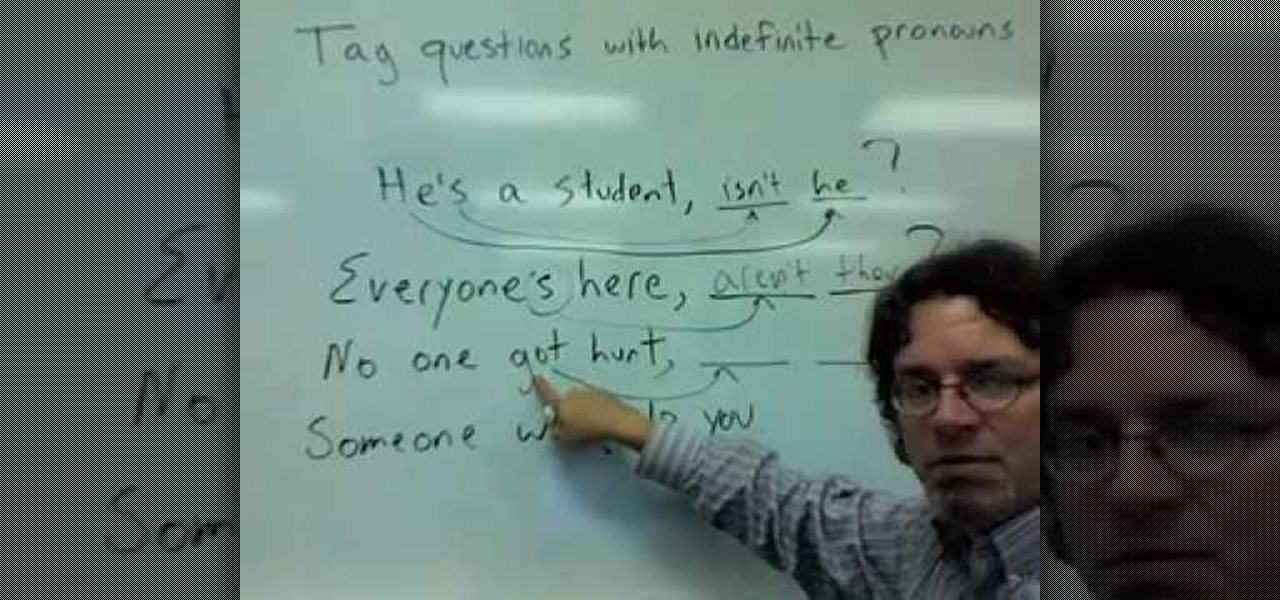
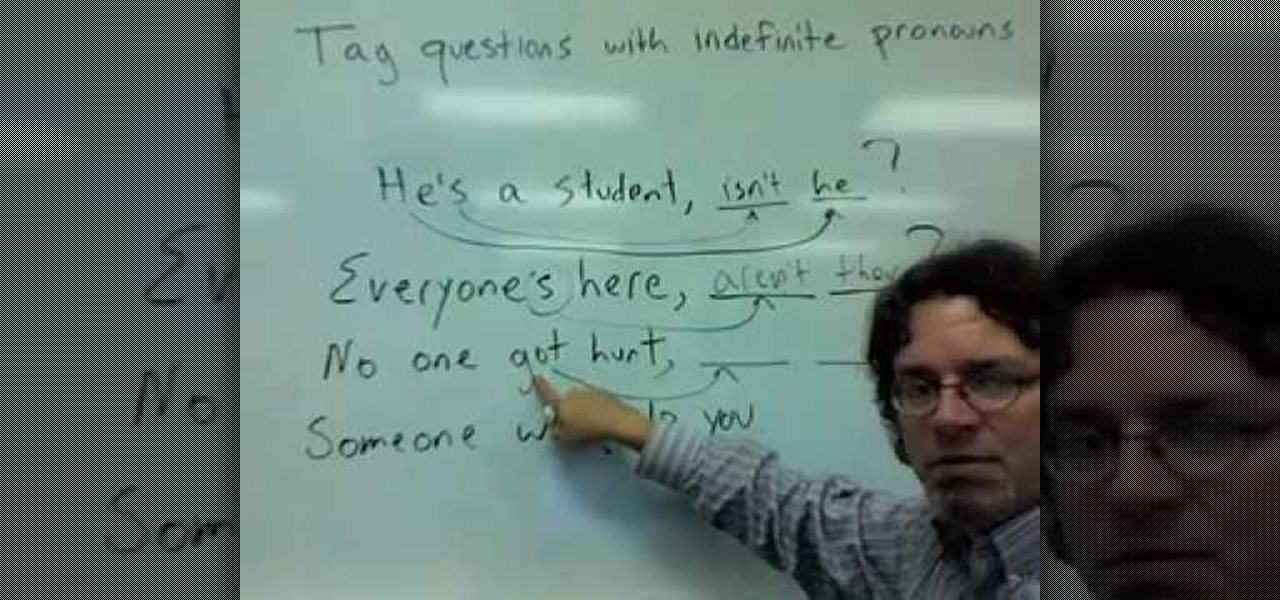
This is a video tutorial in the Language category where you are going to learn how to tag questions with indefinite pronouns in English. A tag question begins as a statement and ends as a question. Here's an example with a definite pronoun: He's a student, isn't he? Indefinite pronouns are exceptions to the rule. For example, everyone's here, can be made in to a tag question. But, the pronoun, everyone, is indefinite. Hence, when you make it in to a tag question, you can't use "it". The corre...
The basic tenet of origami is to create an object - a bird, cube, monkey, etc. - using a single piece of paper. And while for the most part this is possible, there are notable exceptions, including modular origami and this menacing red bull.

If you are a parent trying to protect your children from websites you don't want them to see or just a person who doesn't want to stumble upon certain websites by accident then this video is perfect for you. By using Net Nanny you can block any website you want in a fast and simple way. First, open Net Nanny to the dashboard screen and look under "Exceptions" on the lower right side of the screen. Under exceptions click on "Web exceptions" and then click the "Add" button. Now, type in the URL...

German phonemes pronounced, each with example words. I tried to cover all letters and letter combinations which learners of the German language need to pay attention to.

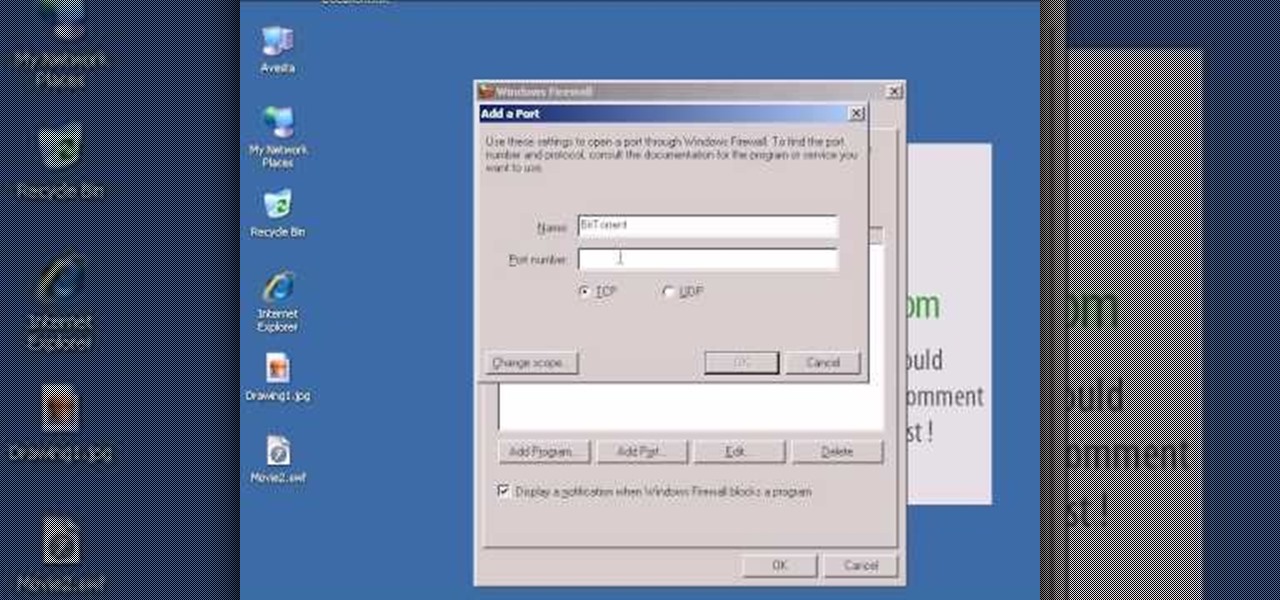
Dave Andrews from HelpVids is going to teach you in this video how to configure the Windows XP firewall. To do that, you need to follow these steps: 1. Go to Control Panel and make sure that you are in the classic view.

Breaking a lease is almost always considered a legal breach of contract, even if a tenant has a good excuse. Here are some exceptions to the rule

In this language video tutorial you will learn how to say numbers 11 to 99 in Vietnamese. For the numbers from 11 to 19, you simply add the number to the word for 10, that is, Muoi. For example, 14 will be Muoi Bon (Bon = 4) and 18 will be Muoi Tam (Tam = 8). For multiples of 10, simply add Muoi after the number. For example, 20 will be Hai Muoi (Hai = 2), 30 will be Ba Muoi (Ba =3), 40 is Bon Muoi and so on. For all other numbers, simply add the number after the multiple of 10. For example, ...

In this tutorial we learn how to use inductive reasoning. Start out with your equation that is giving you your statement. You need to prove whether this is true or not by figuring out the equation. Look at the different angles to see if they are a linear pair and then see if they are the same. Compare them to see if they add up to 180 degrees and use your mathematical logic. Once you understand the backbone to doing this type of math and what the exceptions are, then you will be able to figur...

In this video tutorial, viewers learn how to open ports in Windows firewall. Begin by clicking on the Start menu, go to Control Panel and select Windows Firewall. In the Windows Firewall window, click on the Exceptions tab. Here, users are able to add, edit or delete exceptional ports. To add ports, click on Add Ports. Now name the port, input the port number, select the port type and then click on OK when finished. This video will benefit those viewers who use a Windows computer, and would l...

This video shows the method to turn off pop-up blocker in Internet Explorer and Firefox. Firstly, open Internet Explorer and go to 'Tools' option. Go to 'Internet Options' and click on the 'Privacy' tab. You will see an option of 'Block pop-ups' at the bottom of the window. You must uncheck it and hit 'Apply' to turn it off. For Firefox, go to 'Tools' and 'Options'. You will see 'Block pop-up windows' as the first option. Uncheck it and the pop-ups will not be blocked. You can also set except...

Dr. Steven Jepson explains what you can do to shrink your pores. Pores are small openings in your skin that can become infected or get clogged with makeup or dirt if they are too large. In order to shrink the visible appearance of skin pores you need to clean the dirt and gunk out of the pore. First you need to cleans and exfoliate your face twice a day using a cleanser designed for the face. Exfoliators are mildly acidic and help to dissolve the dirt so that it can be removed. Dr. Jepson war...

The instructor goes about giving a crash course on finding the vertex of a parabola. This is a very nice review of the subject but not really a complete lesson. The instructor fails to explain many of the symbols and other expressions used. The simple way taught by the instructor is the short cut to finding an otherwise complex problem. The nice thing about this technique is that there are no exceptions to this short cut. This is not what someone should learn if they wish to understand the co...

Chronology in Microsoft Word is convenient when it comes to organizing your documents. Thankfully, you don't have to manually edit the document to put things in alphabetical order! This video shows you how to do it in a few clicks.

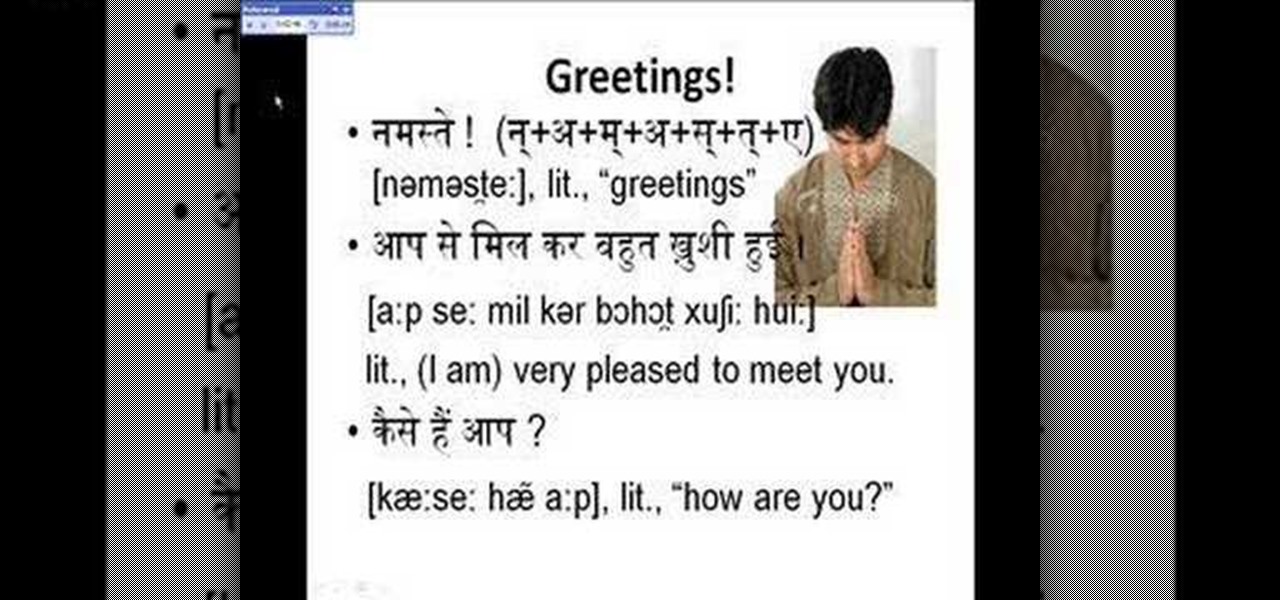
This is the sixth part of my video series on learning Hindi. We come now to basic conversations, such as those while socializing. Pronunciation is stressed and is in IPA, and some exceptions to pronunciations are noted.

Man-in-the-Middle attacks can prove to be very useful, they allow us to do many things, such as monitoring, injection, and recon.

Python is commonly touted as one of the best programming languages for beginners to learn, and its straightforward syntax and functionality makes that hard to argue with. But a lot of tutorials still use Python 2, which is outdated now. Python 3 introduces many new features, and it's important to be aware of them going forward, as well as the key differences between Python 3 and its predecessor.

To celebrate its tenth anniversary, PornHub has just exposed all of our porn habits. All. Of. Them. Before you panic, no individual information has been released. Instead, PornHub has exposed the adult video trends and preferences of a variety of demographics.

This tutorial for Devil May Cry 3 covers the basics of jump canceling and the overall advantages it will provide the player once mastered. The whole concept of a Jump Cancel (JC/JCing for short) is the cancellation of an aerial technique with a jump.

Step 1: What Exploit Development Is and Why Should I Be Interested on About This Topic

Almost every phone comes with biometric security of some sort these days, but the same can't be said of Windows computers. While fingerprint scanners are becoming increasingly common with laptops and desktops, they're nowhere near ubiquitous. Thankfully, your phone's scanner can be used as a sort-of remote authentication point for your PC.

The Pixel's "Flip to Shhh" feature may not be groundbreaking, but it is useful. Third-party apps are copying it for other phones because it's so convenient. But it's not enabled by default and it's fairly hidden in the settings. So to take full advantage of your Pixel's feature set, you should learn how to use Flip to Shhh.

As with most things on the Internet, browser cookies can be either helpful or harmful, depending on how they're used. On one hand, they make your experience more convenient by storing information about sites you use frequently. On the other, they can help companies track you across the web or cause your computer to be more vulnerable to attacks on public networks.

Normally, when you scroll down a webpage in Safari on your iPhone, it automatically hides the bottom toolbar and minimizes the top Smart Search field. But as soon as you scroll back up, they both reappear, which can be pretty annoying if you don't need them. Apple's iOS 13 update brings many new features to Safari, one of which solves the toolbar issue so you can keep it hidden when reading.

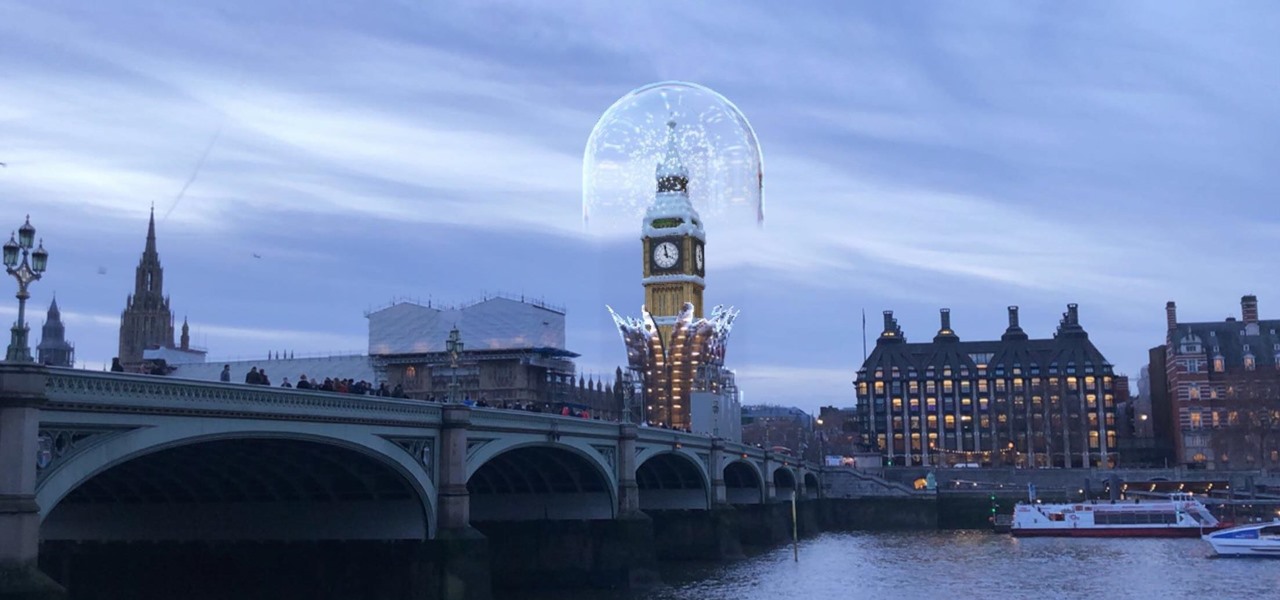
The city of London is getting a holiday gift this season, but it's not the kind you unwrap, since it's completely delivered in augmented reality.

Starting November 1, 2018, Google will require that all new apps and updates to existing apps target Android 8.0 Oreo or higher. This move means the developers behind many of your favorite apps are now scrambling to get their software modernized, while others are considering abandoning outdated apps altogether.

The AFL-CIO's Transportation Trades Division, which represents 32 unions in the US, has successfully lobbied for the removal of 10,000-lb. and heavier commercial trucks from provisions in bills expected to pass that could allow for millions of driverless vehicles on public roads and streets, Bloomberg News reported.

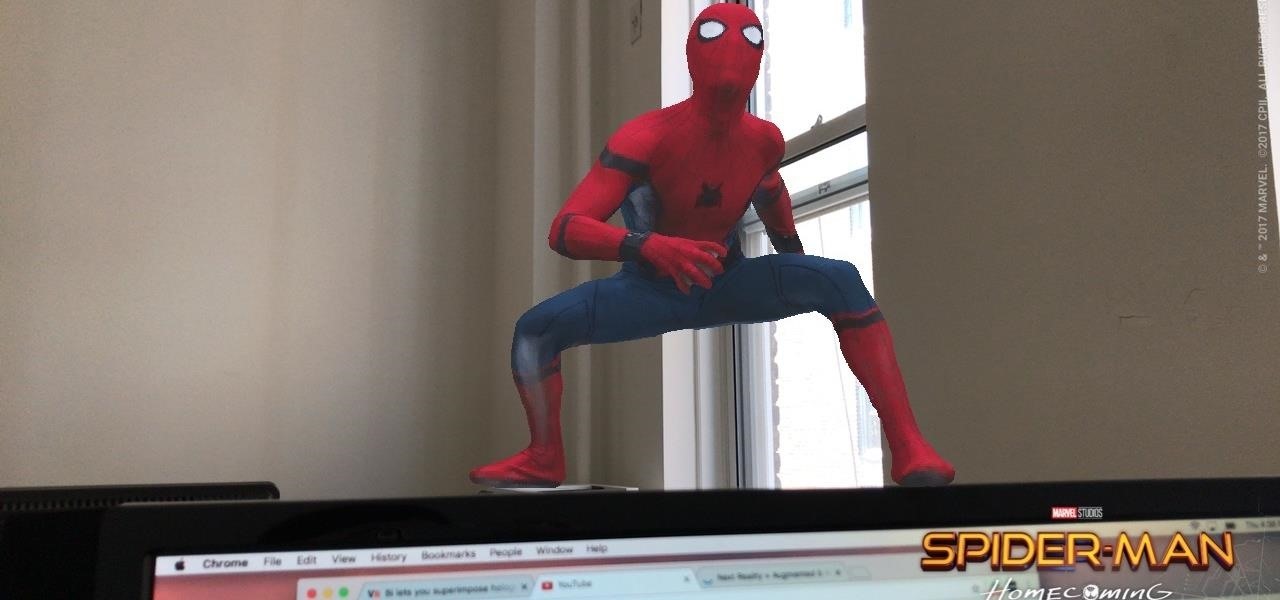
Can't wait till Apple's ARKit is released? Me neither. Luckily, a fun new app launched today that is close to what the ARKit promises to deliver in a few months.

With the FBI getting access to iPhones, and apps like Waze being used to track people's locations, you've got to wonder just how safe and secure your smartphone is... or isn't. When you consider everything you do on your phone, from taking and sharing pictures to mobile banking, keeping your information safe is a crucial step that may seem out of your hands.

This is not essentially the next part in the series, but an expansion of previous part about why should you not use cryptocurrencies.

Well, this is my first article so if it sucks tell me...lol!! Story Time

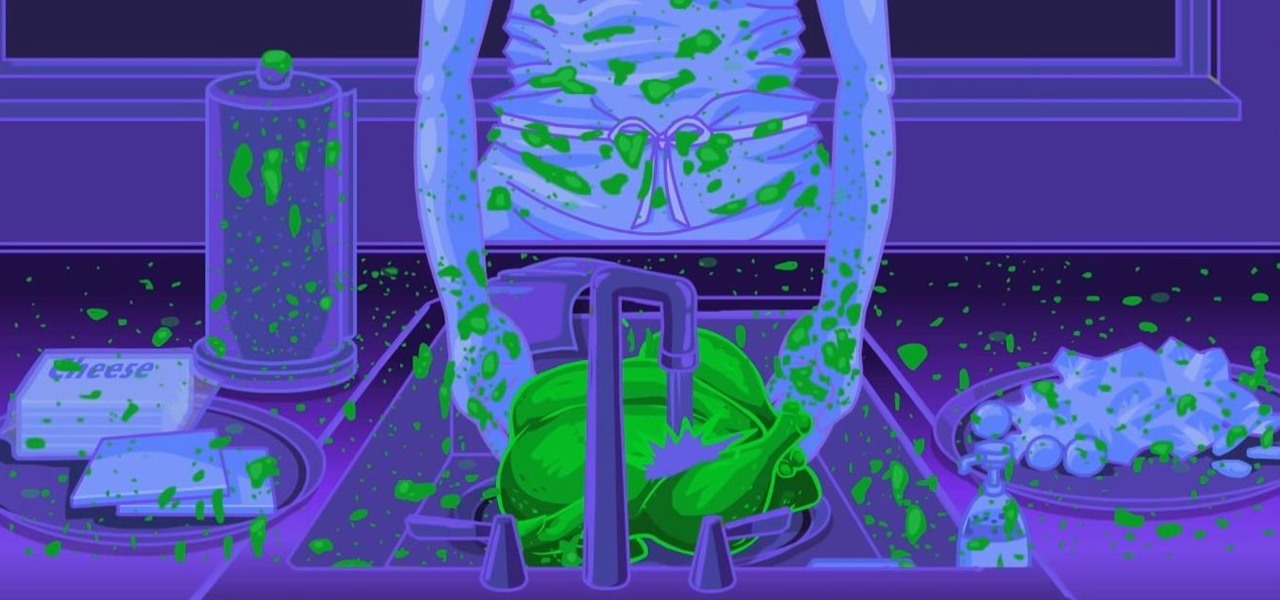
Both professional and home cooks have been rinsing raw chicken and turkey before cooking it for what seems like forever. It's one of those divisive practices—either you do it or you don't, and people tend to be rather opinionated on their stances.

While browsing the internet on your Samsung Galaxy S4, you've probably scrolled to the bottom of a very long webpage, Twitter feed, or down into the abyss of some other app. Depending just how far down you've scrolled, it can be a test of your patience (and fingertips) scrolling back up to the top.

Life has many perils: parasites, predators, and pitfalls. Eventually, any organism will succumb, and if that organism has not first passed on its genes, those genes will face extinction.

When you're at work or in class, there's nothing more annoying than sites that automatically play media. One minute you're happily distracting yourself, and the next, you're scrambling to hit pause while everyone stares at you. Not to mention now your boss knows you're slacking off.

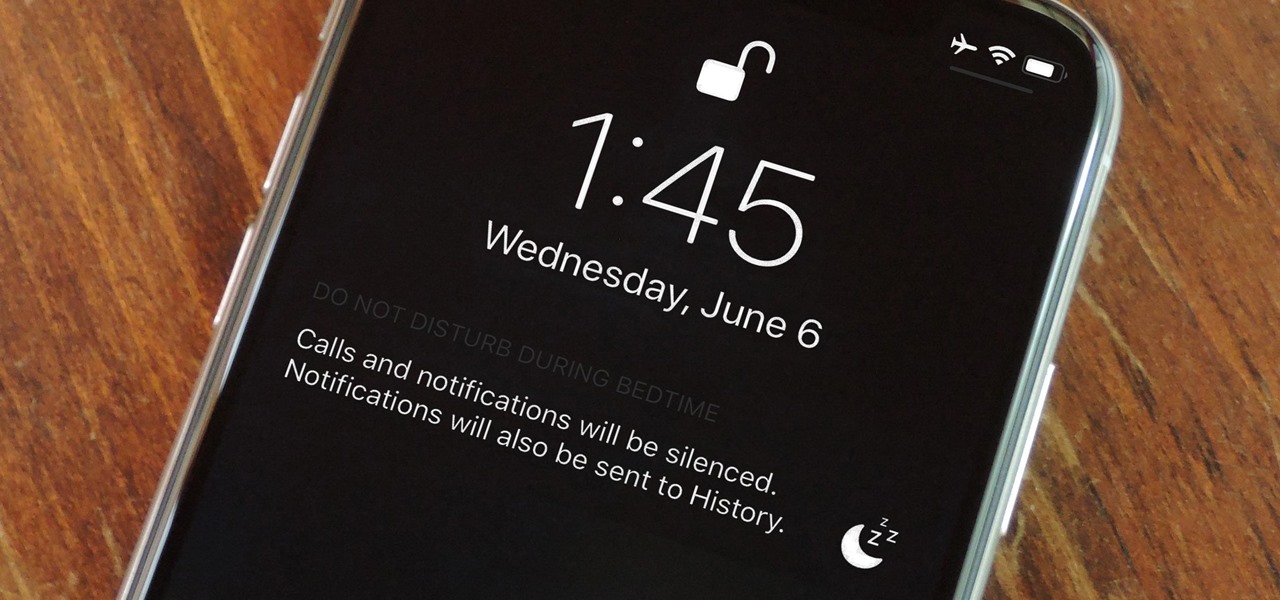
Let's say you wake up in the middle of the night and check your phone to see the time. As soon as you do, you're greeted by a wall of notifications on your lock screen. You just wanted to know how much longer you could sleep, but now your mind's racing after seeing all of the messages you need to deal with. Thankfully, iOS 12's new Bedtime Mode has a solution for this problem.

Noted analyst Gene Munster is predicting that Apple's initial entry into the augmented reality wearables category will be a year later than previous reports have estimated.

If you're not looking closely, it's easy to mistake last year's Galaxy S8 for the brand new Galaxy S9. Design, build materials, screen size, software — it's all virtually identical, save for a few exceptions. But those minor differences can add up.