Any medical student could benefit from this video lesson, whether you're training to be a doctor or a nurse. The very first step to finding out what's wrong with your patient is examining him/her for their vital signs. You must check the patient's pulse, respirations, blood pressure, and know how to use every kind of sphygmomanometer. To see the entire examination procedure, perfect for nursing students, watch the video to see how to examine a patient for vital signs, and refer to the steps b...

This medical how-to video demonstrates how to perform an examination of a traumatized hand. Doing such procedure can be a daunting task, as there may be several structures that may have been injured. Follow along as this resident surgeon shows you what guidelines to follow when examining a hand and wrist. Please note that this medical video is intended for medical professionals only.

Have you ever marveled at those knitting doyennes at Michael's who can just run up to the yarn aisle and speedily pick up some yarn because they know exactly what type of of yarn they need for their project without reading the yarn label? Most of us struggle with different yarn consistencies, scanning the label to get a feel for how the yarn would play out if knitted.

This video will show doctors the process of examining the upper extremity of the body. When you exam the extremities or any joints, it's good to have a systematic approach to how you will examine each joint. Learn about the inspection of each joint, range of motion, palpation and strength testing from Eve Bargmann, M.D. When examining the upper extremity, you should start with the shoulder and work you way down to the elbow, then the wrist, and lastly, the hand.

ER showed the world what goes on inside the emergency room, and in every episode, we experienced a common but very important procedure— intubation. But ER never made it seems easy; it showed just how hard it is for medical students to successfully intubate a patient due to fear and naivety. And for real-life doctors and medical practitioners, learning the art of airway management is just as difficult.

If you're a medical student, you'll learn a lot from this video lesson on examining your patient's eyes. If the patient is having trouble seeing, like double vision, blurred vision, pain or any other problem, a proper eye examination is detrimental to properly diagnosing and treating him/her. You can also determine and potential problems which may arise bases on your family history. Watch to see the complete procedure outlined, which is great for any med student or doctor. Even nurses can ben...

Most won't know what the acronym HEENT stand for, but if you're a medical student, doctor or nurse, you know that it stand for head, ears, eyes, nose and throat. To perform a HEENT examination properly, you must know all the steps and techniques to diagnose your patient. This video lesson will outline the examination procedure, from start to finish, and shows you general palpation techniques and examining the temporomandibular joint, superficial lymph nodes, thyroid gland, eyes, ears, nose, m...

There's no better way to learn then by visual media, and that's what makes this video lesson on performing a chest exam so great. It's perfect for any future doctor, and great for nursing students to understand the proper procedure for examining a patient's chest. Medical students can easily learn how to perform a general chest exam, because ever step and technique is outlined and shown. A chest examination is very important to determining what's wrong with your patient, and you will be able ...

Arguably the single most important aspect to modeling is topology. This overview tutorial takes a look at the topology of the human head, examining each of the main edgeloops, poles, etc. Whether you're new to the Blender Foundation's popular open-source 3D computer graphics application or are a seasoned digital artist merely on the lookout for new tips and tricks, you're sure to be well served by this free video software tutorial from the folks at CG Cookie. For more information, including s...

When you're examining a patient's chest, you start out by simply looking at them— by inspection. It will be hard to count the respirations visually on a healthy person's chest because it moves so little, but in a patient with respiratory distress, the chest might be overactive and strain may show in the neck muscles. Eve Bargmann, M.D., will also teach doctors about palpation, percussion, and auscultation of the chest and back.

In this medical video, learn the process of examining the lower extremity of the body. See demonstrations of how you inspect the lower extremity, how you palpate and then perform passive range of motion of the hip, knee and ankle. John D. Gazewood, MD, MSPH, will also teach doctors special maneuvers to help examine a knee injury. With any type of musculoskeletal exam, you're looking for things like deformity, swelling, and changes in coloration.

In this video, doctors can learn how to perform a full cardiac examination on a patient. The very first thing a doctor should do is visually inspect the patient, because there's a lot that can be gained by simply examining by eye. You'll want to carefully examine the respiratory pattern of the patient, the nature of their precordium, the anterior part of their chest over the heart. Feeling the pulse is also necessary when starting out this heart exam. To learn more, watch the full video.

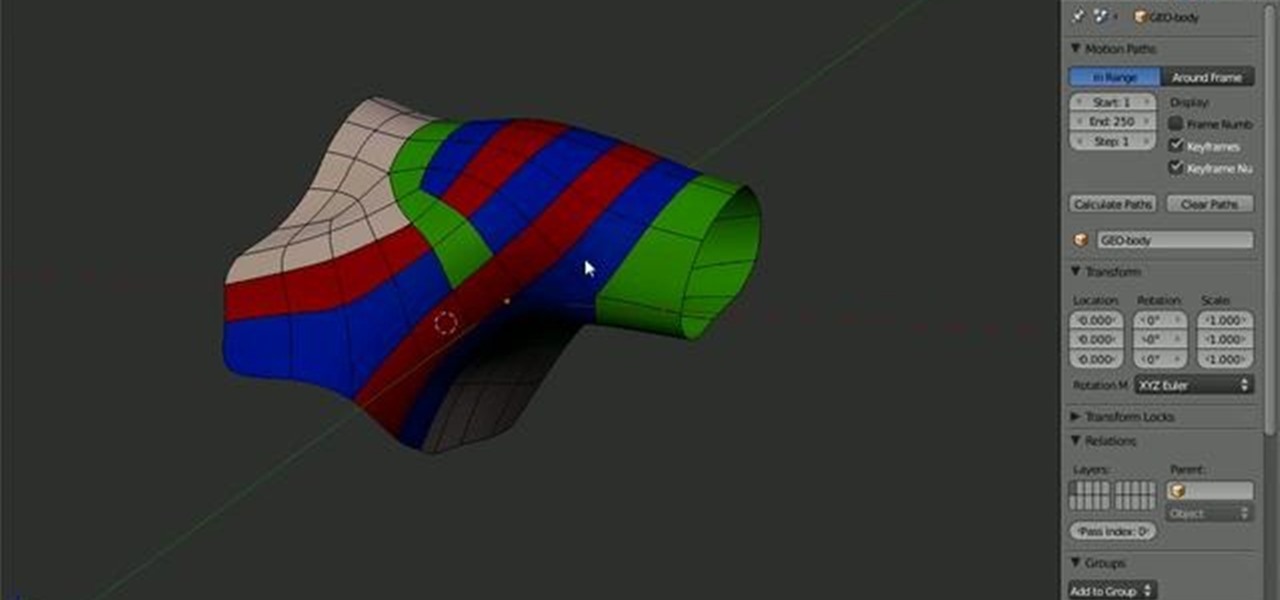
Arguably the single most important aspect to modeling is topology. This Blender 2.5 overview tutorial takes a look at the topology of the human shoulder, examining each of the main edgeloops, poles, etc.

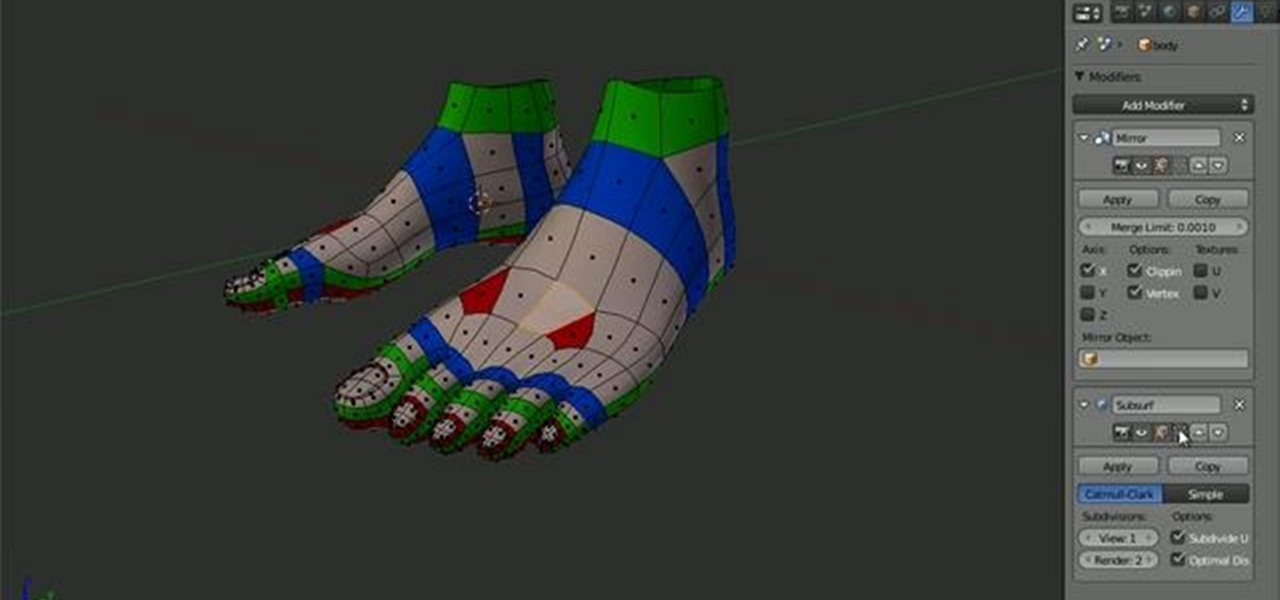
Arguably the single most important aspect to modeling is topology. This Blender 2.5 overview tutorial takes a look at the topology of the human foot, examining each of the main edgeloops, poles, etc. Whether you're new to the Blender Foundation's popular open-source 3D computer graphics application or are a seasoned digital artist merely on the lookout for new tips and tricks, you're sure to be well served by this free video software tutorial from the folks at CG Cookie. For more information,...

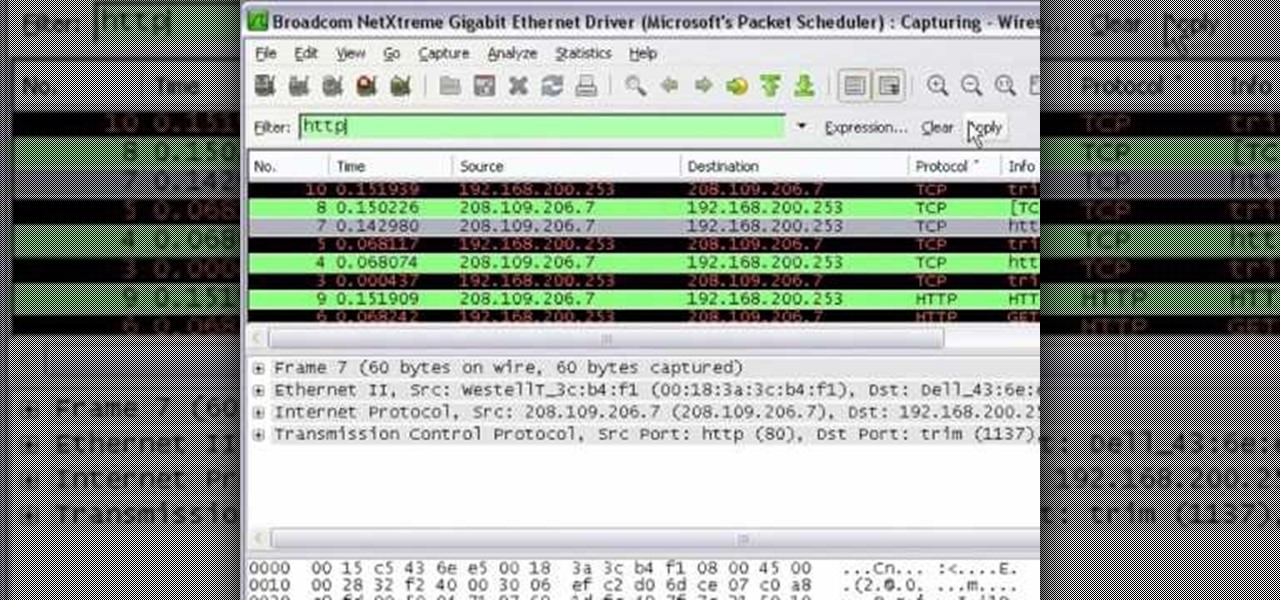
In this tutorial Mike Lively of Northern Kentucky University shows you how to get started with Wireshark. Wireshark is a network protocol analyzer for Unix and Windows. It is used for network troubleshooting, analysis, software and communications protocol development.

In this video tutorial, viewers learn how to cite a cereal box in MLA 2009. citation is a reference to a published or unpublished source. In general, a citation requires the author's name, publication information and medium type. Start by examining the entire cereal box for the information. Look on the front, back, sides, top, bottom and even inside. Usually, users will only be able to find title, medium, corporate sponsor and place of publication. This video will benefit those viewers who ar...

This is a short clip examining the use of the Eraser tool for 2D and 3D painting in modo 201 and higher. The eraser tool will erase pixels from the currently selected texture map on a modo model according to the currently selected brush. Choose the size brush you need and simply paint across the surface you need to remove the texture from. Learn how powerful a painting tool the eraser tool is in this modo tutorial.

The third dimension has finally arrived to internet browsing! Be sure to catch the wave of innovation with this series of tutorials. Initially, we'll be examining the importance of texturing basic 3D objects. Watch as the almost magical effects of texturing in 3ds Max transform a simple cube into a trendy clothes dryer. Polygons are saved, browsing is made speedier, and clients are bound to be happy. Next stop, bring it into Papervision3D! If you wish to learn about using 3D elements on the i...

Are you much for science? Cytoplasm. Nucleus. Endoplasmic reticulum. Organelle. These words might sound alien, but breaking down the parts of a cell and their functions will help you remember. This is one of the best ways for cell identification, and it's perfect for science class studying.

The Operative Framework is a powerful Python-based open-source intelligence (OSINT) tool that can be used to find domains registered by the same email address, as well as many other investigative functions. This reconnaissance tool provides insight about your target through examining relationships in the domains they own.

Welcome back, my novice hackers! One of the most common questions that Null Byte readers ask is: "How can I evade detection by antivirus software on the target?" I have already talked about how AV software works, but to obtain a deeper understanding, what better way is there than opening up and dissecting some AV software?

Seldom in recent history has a cyber security event caused so much media stir (maybe because it happened to a media company?) and international relations upheaval. Cyber security breaches seem to take place daily of major corporations, but the Sony hack seems to have captured the American imagination and, for that matter, the whole world's attention.

Welcome back, my novice hackers! My recent tutorials have been focused upon ways to NOT get caught. Some people call this anti-forensics—the ability to not leave evidence that can be tracked to you or your hack by the system administrator or law enforcement.

Researchers at Disney have demonstrated the ability to render virtual characters in augmented reality that are able interact autonomously with its surrounding physical environment.

Hello, fellow hackers. I'm sure we've all seen it somewhere: the undying question of "How do I hack the game so-and-so?" And the answer usually is, "Come back when you actually know how to hack!" But how does one even go about "hacking" a game? What could that even mean?

Restrictions are inconvenient, and for this reason I've sought out softmods that loosen the constraints for many of the features on my smartphone. Things like adding favorite apps to the Pen Window drawer or choosing any app for Multi Window mode are now must-haves on my Samsung Galaxy Note 3—and should be on yours as well.

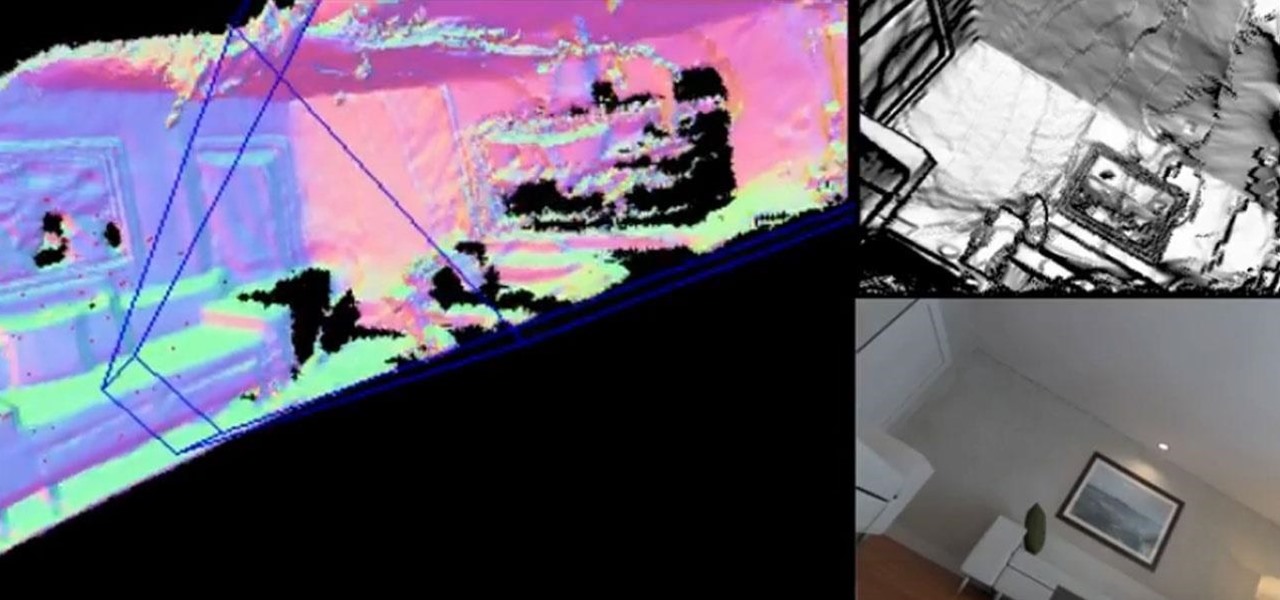
Augmented reality startup 6D.ai is now accepting applicants for the closed beta of its 6D SDK. While operating in the background on a smartphone, the computer vision platform captures a dense 3D mesh in real time using just the device's camera (such a feat typically requires a depth sensor).

How would you feel if the stethoscope used by your doctor to listen to your heart and lungs was teeming with potentially unfriendly bacteria?

In this article, we will explore the basics of radare2, a powerful package that comes with Kali. We are going to write a simple program, and then disassemble it, to see what is really doing in the processor.

Welcome back, my tenderfoot hackers! WordPress-based websites are among the most numerous on this planet (maybe other planets too, but I can't vouch for that). According to WordPress's own website, WordPress powers 23% of the top 10 million websites. That's approximately 2.3 million sites using WordPress!

Hi everyone! After messing around a little bit with IDA and Hopper disassemblers and briefly introducing you to memory, registers and Assembly, we are going to understand what happens when a process is running, which variables join the play and especially what happens when a function is called and why is this procedure-logic so interesting and useful along with the concept of stack.

Can you tell when someone is shooting you a fake smile? Even though fake smiles are easy enough to see through, we all still do it, attempting to show others just how happy we are when we're really feeling less than fantastic. Unfortunately, every smile we fake makes us a tiny bit more miserable.

As Microsoft continues to bask in the glow of its HoloLens 2 unveiling and begins ramping up the hype to launch, Nreal and Vuzix are carving out their own niches in the AR hardware landscape.

In its latest feature with an assist from augmented reality in storytelling, the New York Times shows readers the virtual crime scene it constructed to prove that the Syrian military conducted chemical warfare against its citizens.

Every Tuesday, Next Reality will give readers a rundown of the augmented and mixed reality news briefs from the preceding week that we didn't cover already. This way, you'll never miss anything of importance in the Next Reality landscape, and will always know what's going on with new augmented and mixed reality tech and applications.

If you want to appreciate the value of microbes, look no further than a chunk of cheese. Because cheese roughly traces back to the Neolithic Era, we might say the earliest cheesemakers were the first humans to manipulate microbes—without even knowing it. Now, thanks to microbiologists and the long tradition of cheesemaking, we know a lot more about the microbes that make our favorite types of cheese possible.

Welcome back to another tutorial on functions. Last time, we looked inside memory to see what functions looked like in the flesh and all that Assembly was pretty nasty. At least you have some exposure to it. This time, we will be examining how functions work with the stack.

Welcome back, my neophyte hackers! Digital forensics is one of the fields often overlooked by aspiring hackers. In a rush to exploit every and any system they can, they often ignore learning digital forensics—the field that may lead to them being traced.

Pain is, for the most part, unavoidable when you stub your toe, break your arm, or cut your finger open. It's instantaneous and, in some cases, long-lasting, but it only feels as bad as you want it to. Yes, that's right—that pain is all in your head.

The gag reflex: it can interfere while in the dentist's chair, upon seeing another person throw up, or even just getting a whiff of a disgusting, stomach-twisting scent. Every time this reflex kicks in, it stops us immediately, inducing a choking, gagging, coughing fit.