
Escapes Search Results


How To: Escape from a Jiu Jitsu headlock
Learn how to execute a couple of Jiu Jitsu head lock escapes from the ground.
How To: Escape Restricted Shell Environments on Linux
The moment arrives when you finally pop a shell on the web server you've been working on, only you find yourself in a strange environment with limited functionality. Restricted shells are often used as an additional line of defense and can be frustrating for an attacker to stumble upon. But with enough patience and persistence, it is possible to escape these restricted environments.

How To: Recover a lost Administrator password in Joomla
First things first: You can't actually recover a Joomla administrator password. That's because Joomla uses a one-way MD5 hash that prevents you from doing so. However, it is possible to reset your password.

How To: Stay Warm During a Winter Storm Without Any Electricity
It's that time a year when winter storms begin causing havoc across the United States, and when "rotating outages" are common to help sustain the electrical grid during intense cold periods. That means pretty much anybody with snow and ice in their backyard can succumb to power outages. And no electricity means no electric heat.

How To: Do the 1990's MC Hammer Hammerdance
Nowadays, thinking about why we fell for MC Hammer during the '90s escapes us: the too-big pants and funky songs are more than we care to think about now. But the guy sure knew how to shake what his mama gave him in every direction and way possible.

How To: Thaw beef properly without making it dry
Thaw a beef properly so you don’t lose the precious fluids. The more juice that escapes during defrosting, the less juice that goes in your mouth. Watch this video to learn how to thaw beef properly without making it dry.

How To: Make an indoor hydrogen rocket
The picture may look like a mushroom cloud, but it is actually a can filled with hydrogen exploding. The can is fired into the ceiling. This demonstration still needs a little improvement in the area of safety (but it looks really cool). The problem is the partial pressure of hydrogen drops as the gas escapes and is replaced with air. This causes the reaction to be an explosion instead of a flame. Hydrogen is a tempermental element like that.

How To: Safely use a crockpot
Next time you make dinner in your crockpot, be sure to follow these crockpot safety tips. The temperature should be at least 140 degrees. Food needs to cook at this temperature or higher to prevent the growth of bacteria. Do not put frozen foods into a crockpot. All foods should be defrosted before cooking, so the temperature can reach 140 degrees as quickly as possible. Do not lift the lid to stir, especially if you are cooking on the lowest setting. Each time you lift the lid, heat escapes ...

How To: Use Postenum to Gather Vital Data During Post-Exploitation
Post-exploitation is often not quite as exciting as popping the initial shell, but it's a crucial phase for gathering data and further privilege escalation. Once a target is compromised, there's a lot of information to find and sift through. Luckily, there are tools available that can make the process easy. One such tool is Postenum.
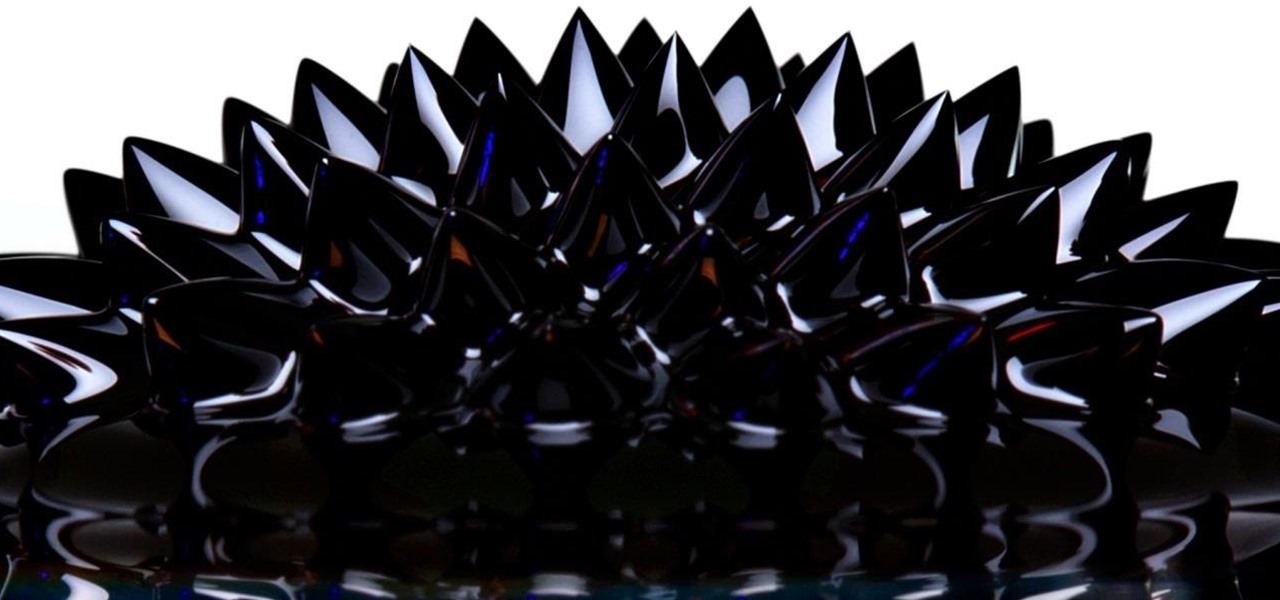
How to Make Ferrofluid: The Liquid of the Future
What Is Ferrofluid? Ferrofluid is a black, solvent-based liquid, that, in the presence of a magnetic field, becomes strongly magnetized. The fluid is made up of nanomagnetic particles coated with an "anti-stick" or surfactant compound, suspended in a "carrier", commonly an organic solvent. For mechanical applications, it is used in hard drives and speakers as a lubricant. However, it also has been implemented in artwork, as seen in the video below.

How To: Make Sodium Metal
Sodium (chemical symbol Na) is an interesting element. It reacts in contact with both oxygen and water, and several sodium salts are used to produce a yellow color in fireworks.
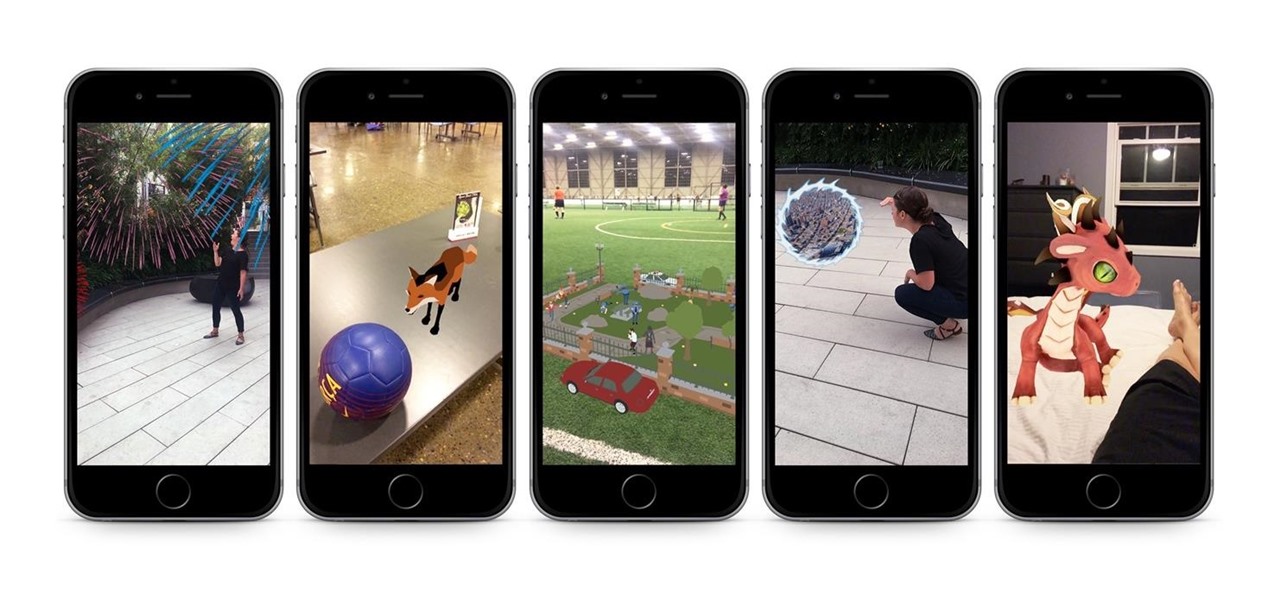
Apple AR: The Box Gives the Gift of AR with ARKit
If giving truly is better than receiving, then The Box AR should be the best ARKit app available when iOS 11 releases next week.

How To: Security-Oriented C Tutorial 0x11 - Command Line Arguments
In many programs on Linux, you'll come across programs which allow you to specify additional arguments instead of just simply running the program by itself. If you've used the Kali distribution, I'm more than certain you'll have come across these with the command line tools, else if you have been following these tutorials, we have already come across three tools which also use the same technique, i.e. gcc, gdb and wc. How do we do this with C? Let's find out.

How To: Create Japanese Style Landscape
So you've decided to transform your drab backyard into a Japanese Zen garden. You've made the right choice. Yes, tire swings and crab grass can slowly kill the soul. That being said, a bit of planning lies ahead. This article offers a list of How To tips, culled from the Landscape Network and other professional Japanese style landscapers, for planning an effective Japanese style landscape in your home. Step 1: Research.

How To: Turn a Cardboard Box into a Cheap DIY Smartphone Projector
Smartphones and tablets are great for watching movies and videos while you're out, but at home, the screen is just too tiny. There are quite a few projectors on the market that work with mobile devices, but they can get pricey.

How To: See-Through DIY Rocket Engine Lets You Watch Fuel Combustion in Action
Ever wondered what the inside of a burning rocket looks like? Well, thanks to Valve engineer Ben Krasnow, now we know. He built a homemade hybrid rocket engine that's see-through so you can actually watch how it works. And even though it's probably a really bad idea to try this at home, he made a video so you can build one, too. Just don't say I didn't warn you.

The Giving Plant: Same Asian Plant Used for Arthritis Treatment Gives Us Powerful HIV Drug
Natural remedies used through the ages abound, especially in Asian medicine. The willow-leaved justicia plant, found throughout Southeast Asia, has traditionally been used to treat arthritis, but scientists have just discovered it contains an anti-HIVcompound more potent than AZT. AZT was the first drug approved to treat HIV, and is still used in HIV combination therapy today.

How To: Skip the Oven—Microwave Your Fish
Fish are delicate, flaky, and can be damn tricky to cook; more often than not, you end up with a hard, dry block of flesh that makes your taste buds sad. And the best ways to cook fish that you know of—c'mon, who doesn't love a fried fish—take way too much effort for you to bother with on a weeknight. Or maybe you're looking for a healthier way to enjoy fish that doesn't require batter or frying at all.

How To: Freeze Your Bread the Right Way & Never Have It Go Stale Again
Bread doesn't have a long shelf life, as most of you probably know quite well from firsthand. You get it home from the store and before you know it, the loaf has turned from soft and perfectly pliable to hard and crumbly—and maybe even moldy! So what's the best way to keep your bread from going bad before you've finished off every delicious slice? Put it in your freezer. It's a simple solution that you've probably heard many times before, but one you probably don't use very often because you ...

How To: Turn a Bottle of Coke into Jello… Shaped Like a Coke Bottle
Soda bottle jello went viral when the popular YouTube channel AwesomeDisneyToys posted video directions for this revolutionary gelatin confection. I just had to try it out to see what the hype is all about.

Hack Like a Pro: Metasploit for the Aspiring Hacker, Part 6 (Gaining Access to Tokens)
Welcome back, my tenderfoot hackers! Hacker newbies have an inordinate fixation on password cracking. They believe that cracking the password is the only way to gain access to the target account and its privileges. If what we really want is access to a system or other resources, sometimes we can get it without a password. Good examples of this are replay attacks and MitM attacks. Neither requires us to have passwords to have access to the user's resources.
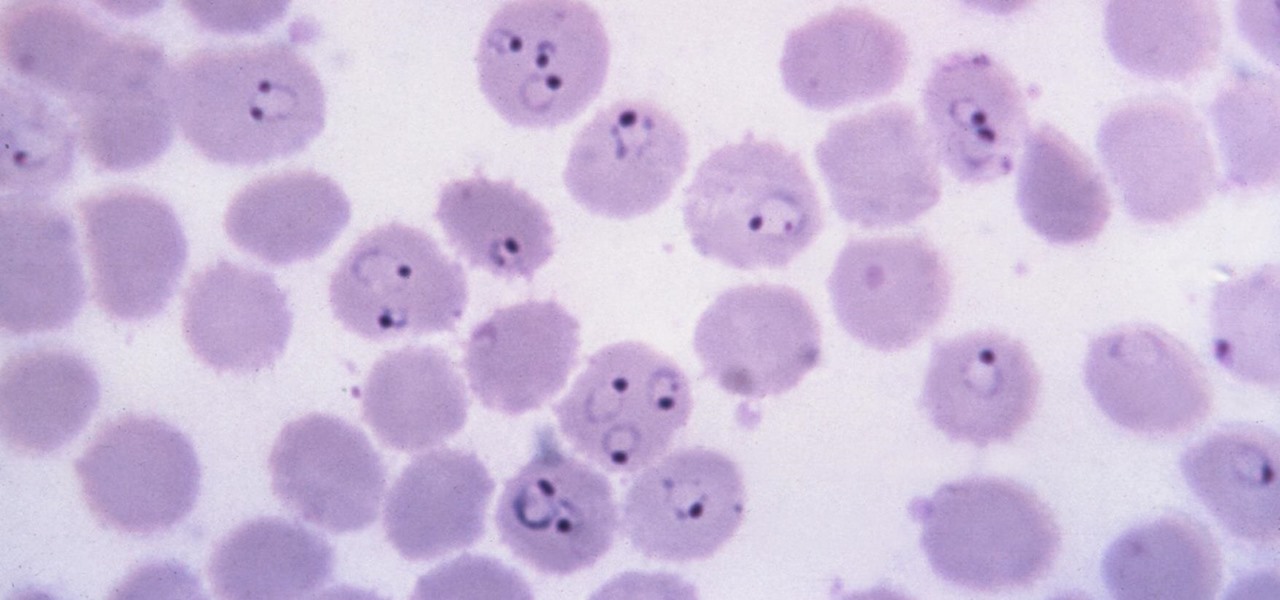
News: New Method Can Stop Malaria Spread — Even After It's in the Body
Malaria is a massive worldwide health problem. The Centers for Disease Control and Prevention estimate that 212 million cases of malaria occurred worldwide in 2015 and 429,000 of the infected people died.
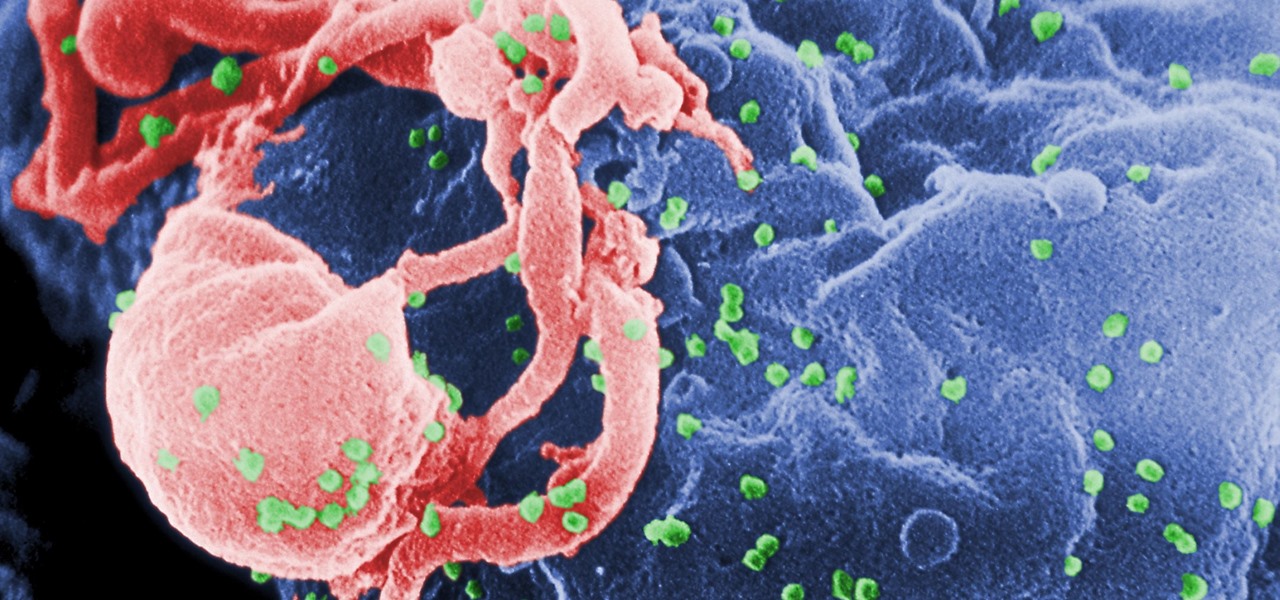
News: Taking Genetic Scissors to Infected Cells Could Cure HIV
Being infected with HIV means a lifetime of antiviral therapy. We can control the infection with those drugs, but we haven't been able to cure people by ridding the body completely of the virus. But thanks to a new study published in Molecular Therapy by scientists at the Lewis Katz School of Medicine (LKSOM) at Temple University and the University of Pittsburgh, all that may change.

How To: Cook Fish Without Actually 'Cooking' It
Preparing and serving seafood can be a daunting task. Fish is so delicate that one extra minute of heat can turn a juicy, flaky filet into a dried-out disaster. But that same fragility also allows us to use unconventional methods to chemically transform the fish into its cooked consistency.

How To: 15 Clever Ways to Use Coffee Filters for More Than Just Java
Even if you've put aside your percolator and have gone the way of the pod coffeemaker, there are still dozens of ways to use your leftover coffee filters. Incredibly cheap, absorbent, and shaped with a ruffle, coffee filters are useful in the kitchen, garden, and around the house.

How To: Make the Scariac (A Poor Man's Variable Power Controller)
Mixing water and electricity is extremely risky and potentially lethal, yet that's exactly what I did with the Scariac. In its simplest form, the Scariac is just a glorified version of two wires in a bucket of water, but it's actually one of the cheapest power controllers you can make.

How To: Advanced Techniques to Bypass & Defeat XSS Filters, Part 2
Cross-site scripting can be one of the easiest vulnerabilities to discover, but to be successful with this type of attack, it is essential to learn how to get past filters. In the previous guide, we explored some ways to do this, such as abusing attributes and event handlers and tricking the application into accepting unusual characters. Now, let's take a look at more techniques used to defeat filters.

Understanding OLED: The Difference Between LG's POLED & Samsung's AMOLED Screens
With the recent launch of the LG V30 and the Pixel 2 XL, LG has reintroduced the world to POLED. This display tech was showcased at CES 2015 and billed as a rival to Samsung's AMOLED displays, then promptly disappeared from the market for two years. But now that two of the biggest flagship phones this year are using the technology, many folks will be wondering what makes POLED different.

News: How to Avoid Food Poisoning & Keep Your Cooking Safe with These Tips
Even when no one is in your kitchen, it is crowded. The refrigerator, sink, and counters are all covered with microbes that are just hanging around. They are inadvertent remnants from the raw chicken you used in that recipe last night, brewing a bacterial cocktail in your Nespresso machine, or just growing their merry little colonies on your leftovers.

How To: Use a Misconfigured SUID Bit to Escalate Privileges & Get Root
Gaining access to a system is always exciting, but where do you go from there? Root or bust. Sure, a compromised host is a great way to run a botnet, or do some other boring, nefarious thing—but as hackers, we want root. We also want to take the easiest path possible, search out low-hanging fruit, and exploit them. SUID programs are the lowest of the low-hanging fruit.

Hands-On: Niantic's Harry Potter: Wizards Unite Brings New Magic to the World of Augmented Reality
Can lightning strike twice? Niantic is betting that it can with its latest augmented reality game based on the best-selling multimedia franchise Harry Potter.

How To: Make an Airsoft Machine Gun (AKA Halo Mobile Turret)
Airsoft doesn't get any better than a cloud chamber BB machine gun, aka Cloud BBMG. This design has an incredible rate of fire. If you've got a full charge of compressed air, it can easily fire more than 50 rounds per second at a 350 ft/s muzzle velocity. Since this is a legit airsoft build, it should be handled safely with the same care as any other airsoft firearm, and you should be wearing the same protective gear—protective mask, safety glasses, etc. My video details the build of this bea...

How To: Protect Your PHP Website from SQL Injection Hacks
As a web developer, I often read articles about hackers (from the lowly to the knowledgeable) infiltrating websites via the dreaded 'SQL Injection' method and completely taking control, changing, gaining access, or destroying the owner's data. As a fellow web developer, I'm sure you want to know how to protect against it. Well, here it is! In this article, you will find out what SQL Injection is, what you can do to protect against it, and additional recommendations that are easy to do and onl...

How To: Make Bubbles and Squeaks
I saw this on the Food Network and tried it out. We loved it. It is a great way to use leftovers and with the holidays upon us, I know you'll want to try it. I think it was Jamie Oliver who presented it although I couldn't find it on the website. It was described as a common thing done in the UK as the evening meal after a Sunday lunch. It is great with leftover turkey, dressing, and potatoes and gravy. The name comes from the sounds that it makes when it cooks. When you put the patties in th...

News: Super 8 - JJ Abrams & Spielberg's Secret Project
This is the top secret JJ Abrams project done with Spielberg, which debuted before Iron Man 2. Looks like Cloverfield set in the desert, or perhaps a Cloverfield prequel.

News: Poem of the Day
CITY OF ANGELS by: Luis Rodriguez Somewhere out there, lies the city.

How To: Do pass and move soccer drills for ball control
This UEFA Training Ground video helps develop your ability to pass and move the ball to fellow soccer teammates. Although it seems quite basic, proper passing in heated game situations is a nice skill to have and to fall back on if a recently learned soccer trick suddenly escapes you're caught between a rock and a pushy defender.

News: 100 Movie Spoilers in 5 Minutes
Movies spoiled

News: The Avengers (2012) Poster and Fan Art
After his fall from Asgard into space, the Asgardian Loki meets the Other, the leader of a warmongering alien race known as the Chitauri. In exchange for retrieving the Tesseract,2 a powerful energy source of unknown potential, the Other promises Loki a Chitauri army with which he can subjugate the Earth. Nick Fury, director of the espionage agency S.H.I.E.L.D., arrives at a remote research facility during an evacuation. Physicist Dr. Erik Selvig is leading a research team experimenting on th...

