Particular vulnerabilities and exploits come along and make headlines with their catchy names and impressive potential for damage. EternalBlue is one of those exploits. Originally tied to the NSA, this zero-day exploited a flaw in the SMB protocol, affecting many Windows machines and wreaking havoc everywhere. Here, we will use EternalBlue to exploit SMB via Metasploit.

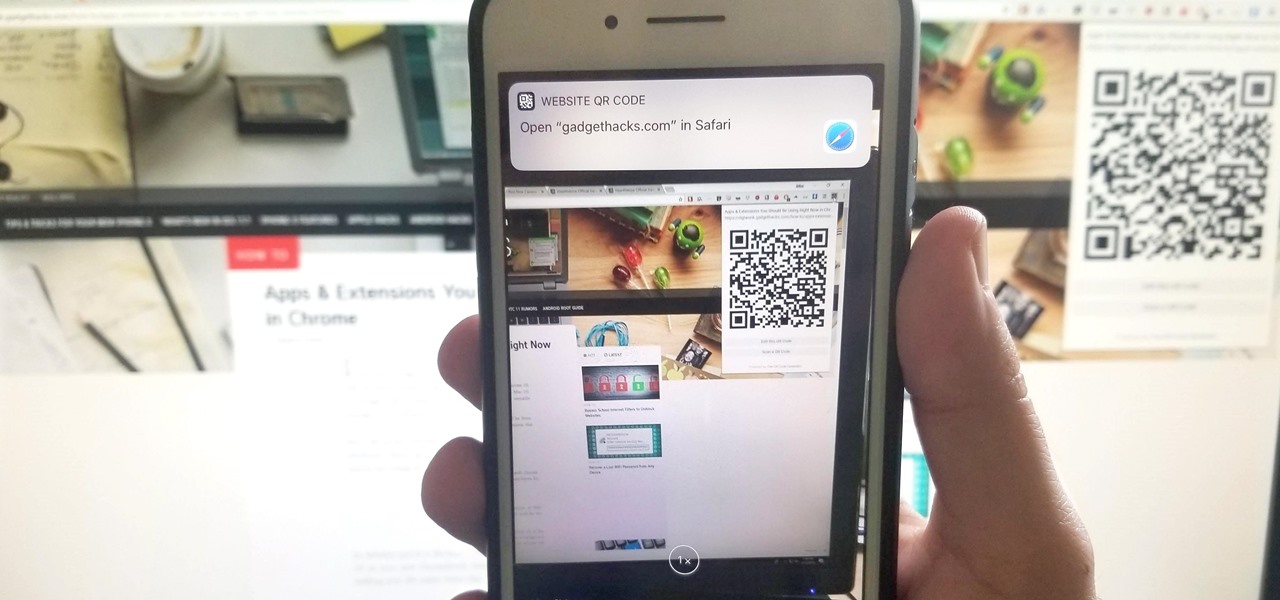
The default Camera app got a few more tricks up its sleeves when iOS 11 was released, and the best addition by far was the inclusion of a built-in QR code reader since that meant no more third-party apps just for QR code scanning. However, Apple's built-in QR code scanner did have a vulnerability at one point that would let hackers direct you to a compromised website without you even noticing it.

If you are looking for a UAV code for homebrew then this is the video for you. Check out this site for codes and follow the video to learn how to hack COD: Black Ops with a UAV code.

If you have friends or relatives living or traveling in another country, you may need to call them internationally. Check out this tutorial and learn how to dial a far away land just as easily as you would dial one close to home.
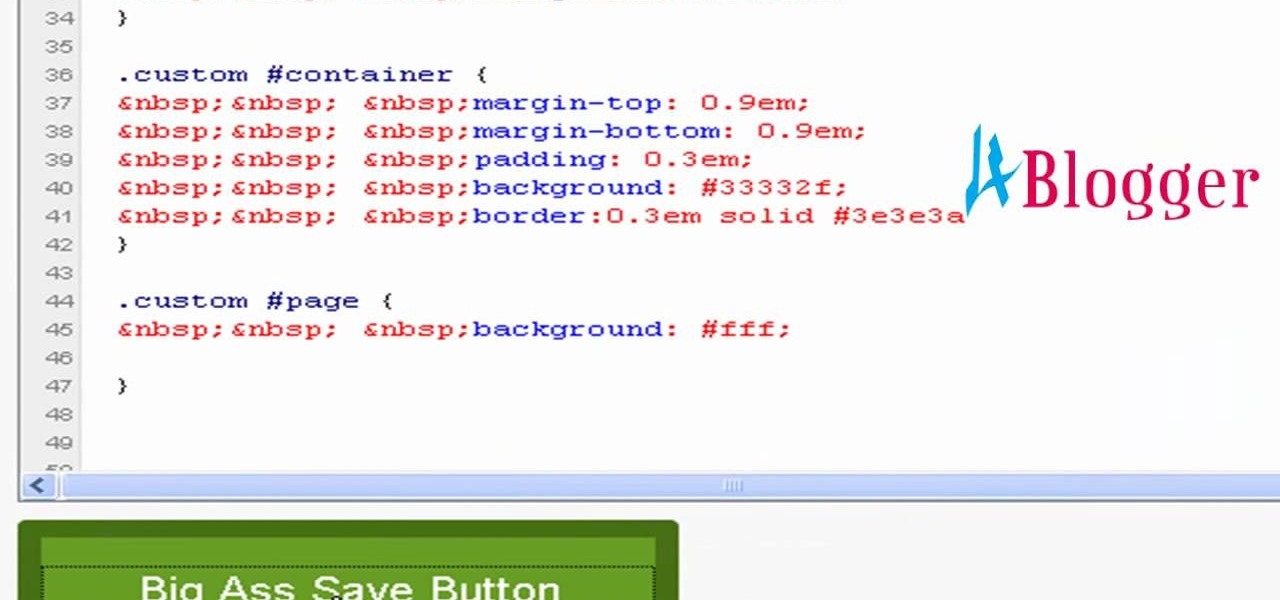
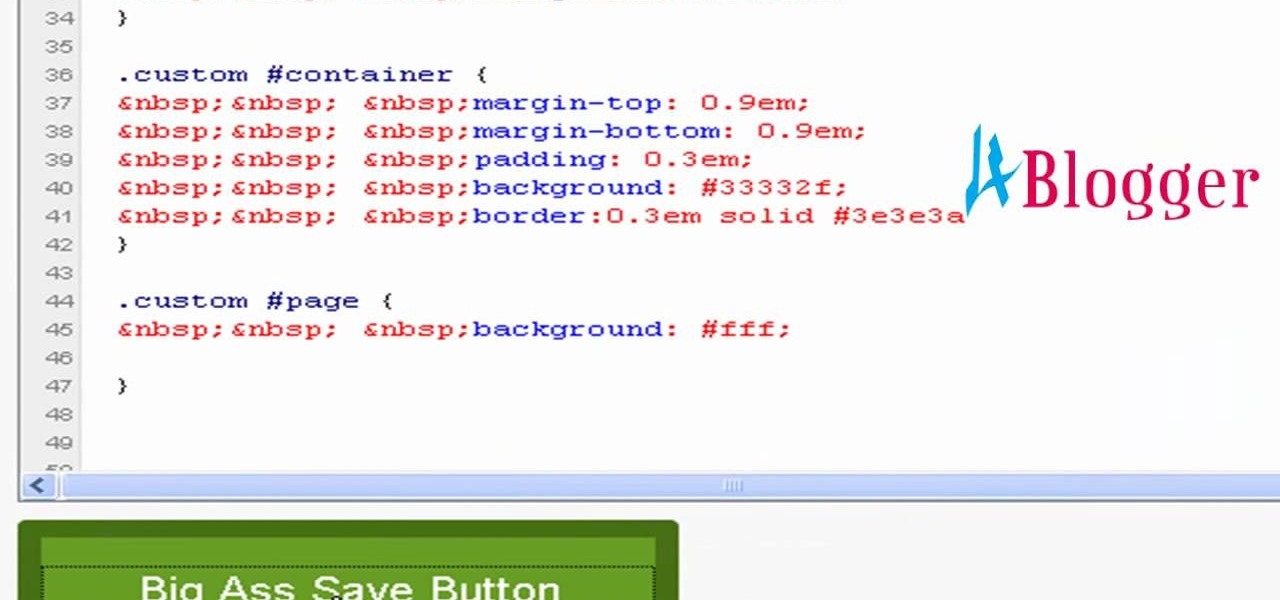
You can change thesis theme background color and size in Wordpress blog to do this first you need to go to your word press admin. And then you have to click custom file editor. There you will see the "Thesis custom file editor". Now you have to select custom.css in edit selected file menu. Now you will see there a code box. Here you will have to past the background changing code. The code is showing in the video you can type it and then copy and paste it in the place of the code box which is ...

MySpace gives users the ability to hide their friends list. This video walks you step by step through being able to view this list. First, go to the desired profile. You'll see the hidden friends list. Now, click on "Edit with notepad" and code will pop up on your notepad. Because the list is on the page, editing the source code will make the list appear on the page. Next, type the command >table border=0 cellspacing=0 align="center">. Now you'll be instructed on how to delete the source code...

In this video tutorial, viewers learn how to automatically play You Tube videos on My Space. Begin by going on the You Tube website and search for a video that you want. Then copy the embed code and paste it in a notepad document. There will be two URLs in the embed code in quotations. Type in "&autoplay=1" at the end of both URLs inside the quotations and then copy the embed code. Log into your My Space account and click on Edit Profile. Paste the embed code into the About Me section and cli...

This video shows you how to bypass expensive texting charges and use this free and easy way to text people without the need to download apps, go to websites, or jailbreak your device. Works on basically any cell phone. No need to ever pay $20.00 for unlimited texting with AT&T, watching this you'll be able to text for free whenever, and whoever.

Rich Brooks of the web design and internet marketing company Flyte New Media shows you how to add a Facebook Fan Box to your website or blog. This video briefly explains the importance of using Facebook Fan Box as a social networking tool to help build your business and increase your fanbase. Adding a Facebook Fan Box is as simple as following a few simple steps. You'll begin by clicking on the Fan Box button your Facebook page which will allow you to choose where to add this widget. You'll b...

Editing the sites with JavaScript code is one of the easiest method in the internet. First go to any web page, clear the address bar and the paste the code below, "javascript:document.body.contentEditable='true'; document.designMode='on'; void 0"(Without the quotes) and hit enter. Yep that's it, now you can select or click any part of the web page and edit what ever you need. If you follow the steps in this video you would be able to edit sites with JavaScript code easily.

This is a simple Adobe Flex Photo Viewer. It uses a number of techniques that are not found in any one place in the literature - data shorting, tile repeater, xml http services, inline mxml actionscripting, click on double functions, use of CDATA Tags, tooltip, glow and fade effects - all done in less than 100 lines of code (once you take out the blank lines). This was created by Mike Lively Director of Instructional Design at Northern Kentucky University for the Over The Rhine project.

In this software tutorial you will learn how to make a simple website using Photoshop. You may think it's too difficult to create your own site and that you need to use a template, but this tutorial will change all that! See how easy it is to design your own web page without a template right in Photoshop.

In this video tutorial, Chris Pels will show how to share data in between JavaScript and server-side code by using a hidden field in an ASP.NET page. Next, learn how to use the RegisterHiddenField method in server-side code to programmatically create a hidden field on the client. In addition, see how to programmatically create a HiddenField server control for sharing data on an ASP.NET page. Finally, use the RegisterArrayDeclaration method to create a container in server code for storing mult...

This is a Restaurant City 3 in 1 Hack (Working From 12th May 2009).

A QR code is a fun and convenient way to link people to a website or app. On iOS, you have a few ways to scan these codes. You can download a QR scanner to get the job done, but Apple has one built into iOS. Or you can add the QR Code Reader tile in Control Center, but that's not even necessary. There's a better way, one that requires basically no effort to pull off.

Attacks against databases have become one of the most popular and lucrative activities for hackers recently. New data breaches seem to be popping up every week, but even with all of that attention, databases continue to be a prime target. All of these attacks have to start somewhere, and we'll be exploring a variety of methods to gather information on PostgreSQL databases with Metasploit.

It's exciting to get that reverse shell or execute a payload, but sometimes these things don't work as expected when there are certain defenses in play. One way to get around that issue is by obfuscating the payload, and encoding it using different techniques will usually bring varying degrees of success. Graffiti can make that happen.

Web applications are a prime target for hackers, but sometimes it's not just the web apps themselves that are vulnerable. Web management interfaces should be scrutinized just as hard as the apps they manage, especially when they contain some sort of upload functionality. By exploiting a vulnerability in Apache Tomcat, a hacker can upload a backdoor and get a shell.

UnrealIRCd is an open-source IRC server that has been around since 1999 and is perhaps the most widely used one today. Version 3.2.8.1 was vulnerable to remote code execution due to a backdoor in the software. Today, we will be exploiting the vulnerability with Metasploit, examining the underlying code to understand it, and creating our own version of the exploit in Python.

QR codes are supposed to make life easier, but having to install potentially shady third-party apps just to scan one is more trouble than it's worth. Thankfully, there's a QR code reader built into all Google Pixels, but you wouldn't know it unless you stumbled across the feature.

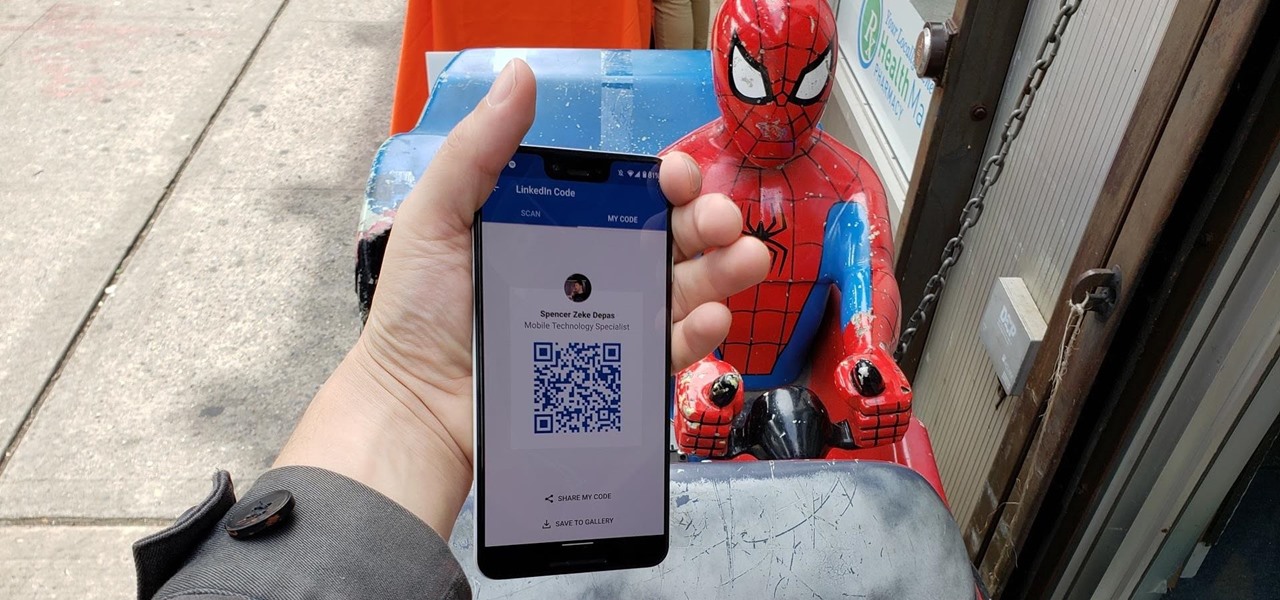
When attending networking events, a LinkedIn exchange is a common occurrence. Equally common is the awkward fumbling dance with how to add each other. Fortunately, we have the solution: the ultimate way to add LinkedIn contacts.

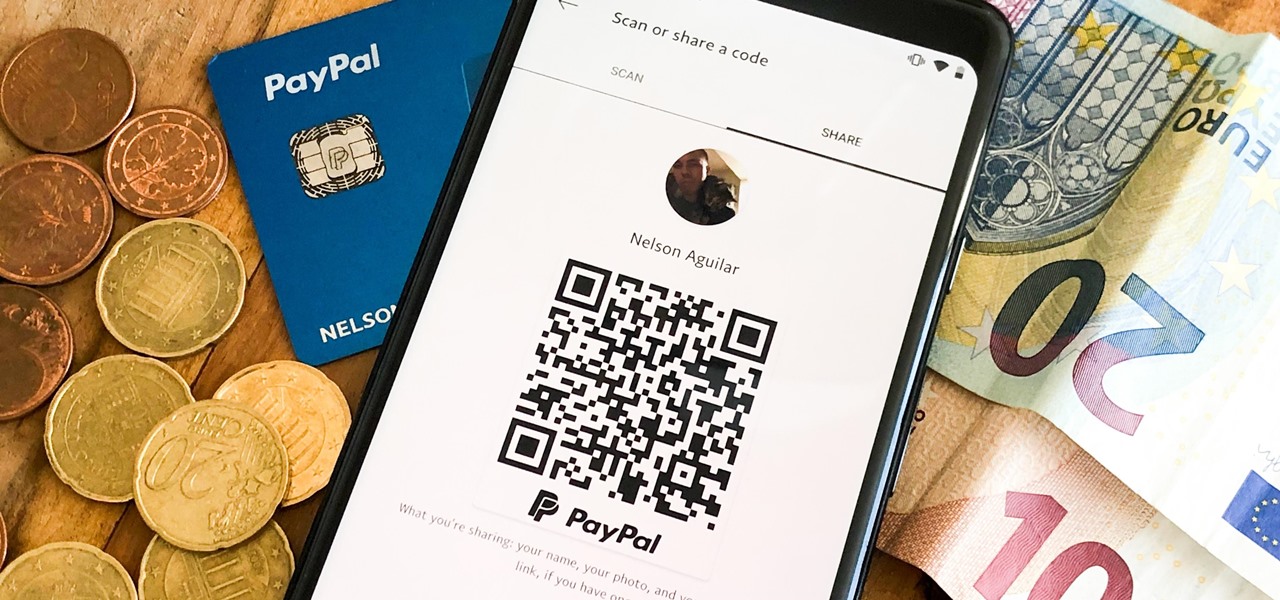
There are many ways to send and receive money on PayPal. You can use an email address, a phone number, or a PayPal.Me link, but if you're standing right next to the person you're trying to pay or get digital cash from, the easiest way, by far, is to use QR codes.

There is no shortage of defenses against cross-site scripting (XSS) since it is so prevalent on the web today. Filters are one of the most common implementations used to prevent this type of attack, usually configured as a blacklist of known bad expressions or based on regex evaluation. But there is hope with a wide variety of techniques that can be used to defeat these filters.

A week after the L.E.A.P. Conference, our cup of Magic Leap news continues to floweth over, with the company's content chief giving us some insight into the company's strategy, and Twilio sharing what its virtual chat app looks like.

Starting in iOS 11, Apple introduced a QR code scanner for iPhone that's baked right into the Camera app, reducing the need for a third-party scanner. However, not everyone knew it existed, so a lot of users were still using third-party QR code scanners. In iOS 12 and later, Apple addressed the issue, making theirs much more visible, as well as improved QR code scanning in general.

The arrival of Magic Leap One is tantalizingly close and, although the company has been saving the last details for launch day, a few of the more important details were found this week hiding deep in the code on Magic Leap's website.

Hackers rely on good data to be able to pull off an attack, and reconnaissance is the stage of the hack in which they must learn as much as they can to devise a plan of action. Technical details are a critical component of this picture, and with OSINT tools like Maltego, a single domain name is everything you need to fingerprint the tech details of an organization from IP address to AS number.

If you have a Mac, you can use Apple's Handoff feature to open one of your Safari desktop tabs in Safari on your iPhone. But if you prefer to use Google Chrome as your desktop browser, whether or not that's because you have a Windows PC, you can't "hand off" open tabs from Chrome desktop to Safari on your iPhone. There is a cool workaround, however.

While not specifically an augmented reality conference, IFA 2017 packed a plethora of presentations with AR themes, including devices with AR features from Sony and Motorola, a smartphone-based AR headset from Lenovo, and a new processor from Huawei that will facilitate AR experiences.

Cross-compilation allows you to develop for one platform (like Kali) and compile to run on a different platform (such as Windows). For developers, it means that they can work on their platform of choice and compile their code for their target platform. For hackers, it means we can compile exploit code for Windows from Kali.

With products and solutions offered by the likes of Scope AR, Trimble, DAQRI, VIATechnik, and others, augmented reality is becoming a hot commodity for improving productivity while maintaining safety in the construction and manufacturing industries.

While it remains unknown how exactly augmented reality will make its way into the mainstream (the Microsoft HoloLens sitting at $3,000 isn't exactly accessible), many brands have been trying to integrate the tech into their mobile apps, mimicking the success of Snapchat and its popular AR filters. One of those brands going all in on augmented reality is Shazam.

Welcome to the first coding tutorial on SQL here on Null Byte. Typo:

Researchers have discovered a "severe vulnerability" that allows attackers to use eBay to distribute malware, and the online auction company has no plans to fix the problem.

Determining exactly what of the thousands of parts on a modern car is broken is as difficult as doing the repairs many times. IN this video you'll learn how to diagnose and fix error codes P0171 and P0174 on a 2001 Ford Escape, which indicate vacuum problems.

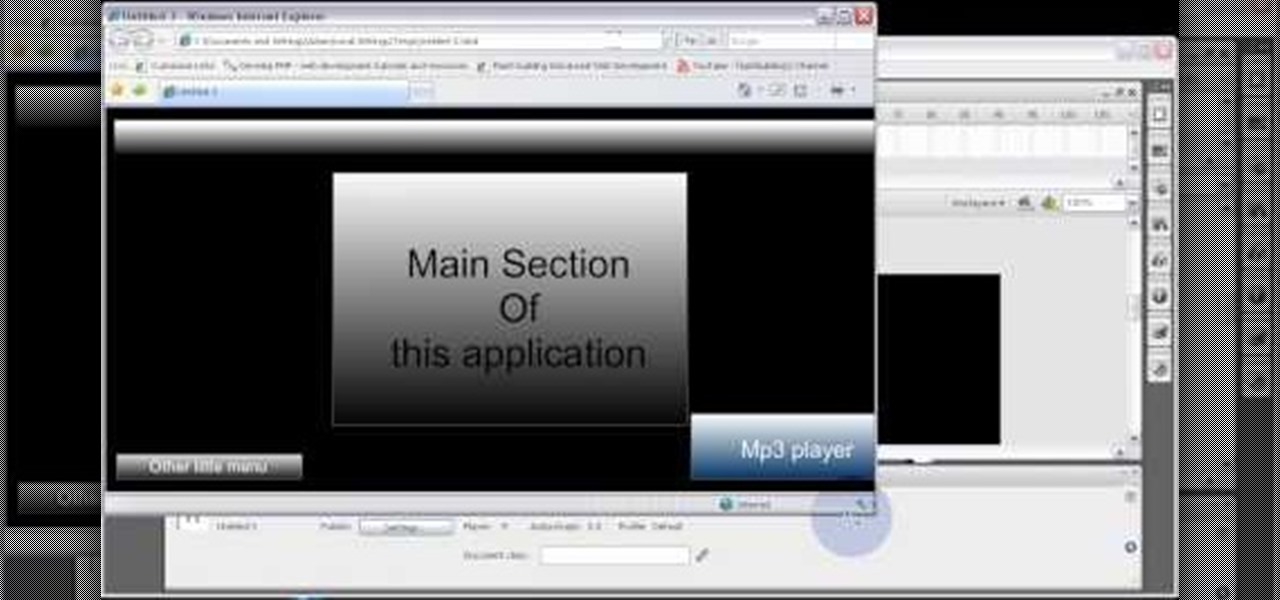
Code your Flash-based website so that your content can remain the same, no matter if visitors are viewing your site on a computer screen, smartphone display or even a high-definition TV. This tutorial shows how you can code your fluid website to achieve the true fit effect.

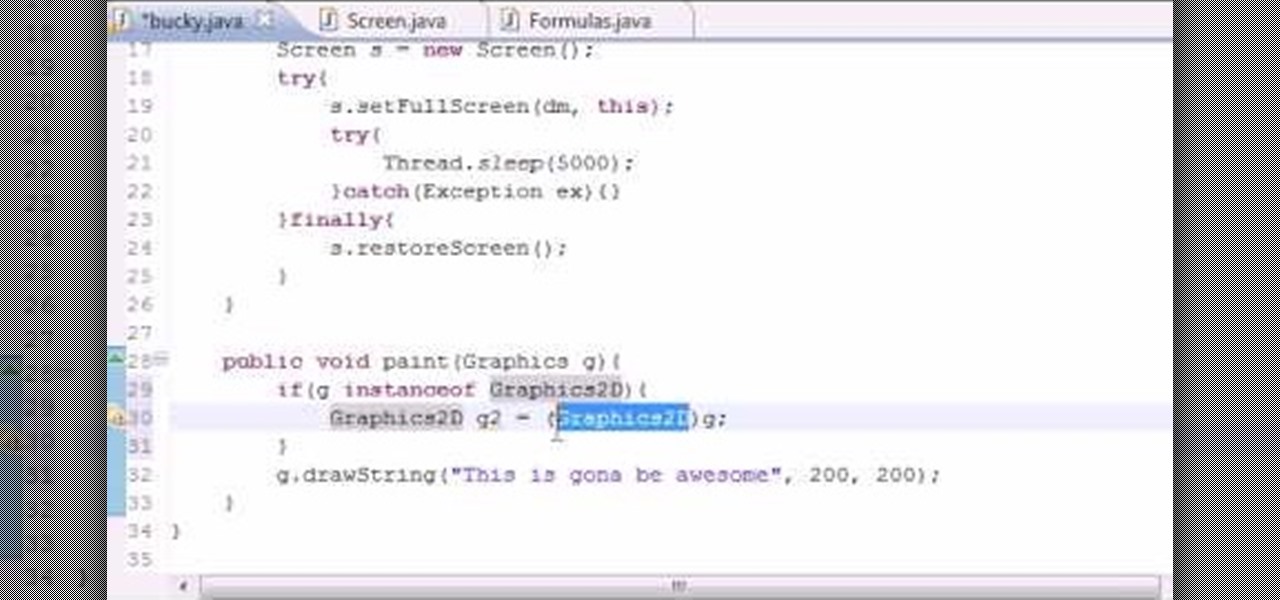
Want to program your own Java games and applications but don't know beans about object-oriented programming? Never you fear. This free video tutorial from TheNewBoston will have you coding your own Java apps in no time flat. Specifically, this lesson discusses how to anti-alias text when writing code in the Java programming language. For more information, including detailed, step-by-step instructions, watch this helpful programmer's guide.

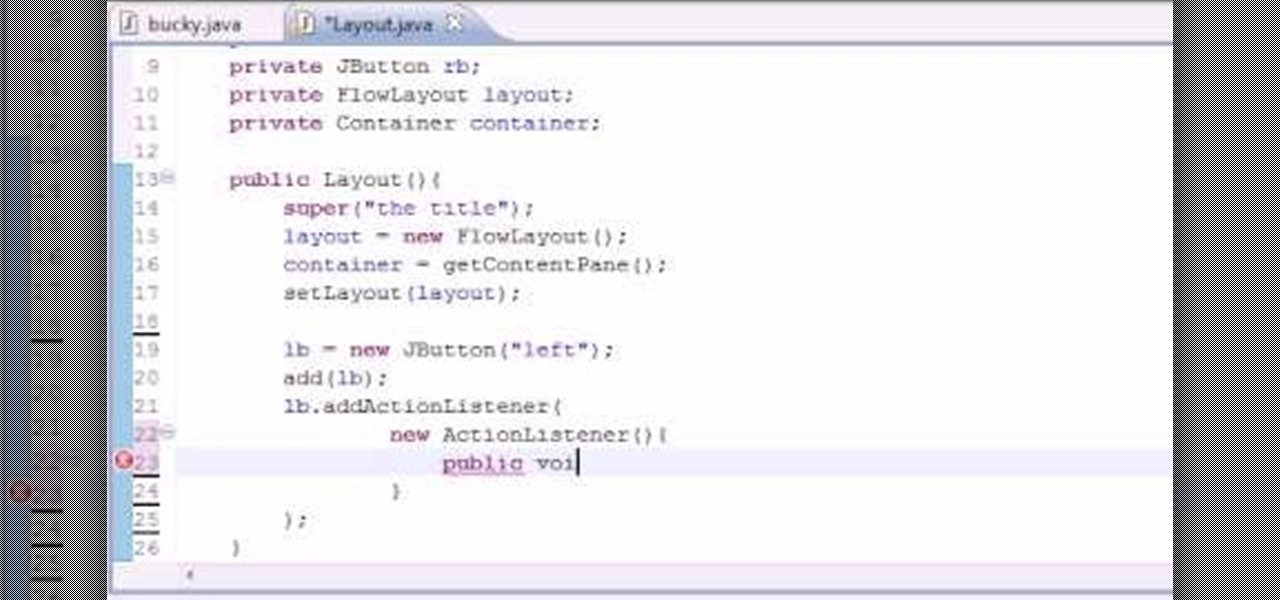
Want to program your own Java games and applications but don't know beans about object-oriented programming? Never you fear. This free video tutorial from TheNewBoston will have you coding your own Java apps in no time flat. Specifically, this lesson discusses how to work with the FlowLayout class when writing code in the Java programming language. For more information, including detailed, step-by-step instructions, watch this helpful programmer's guide.

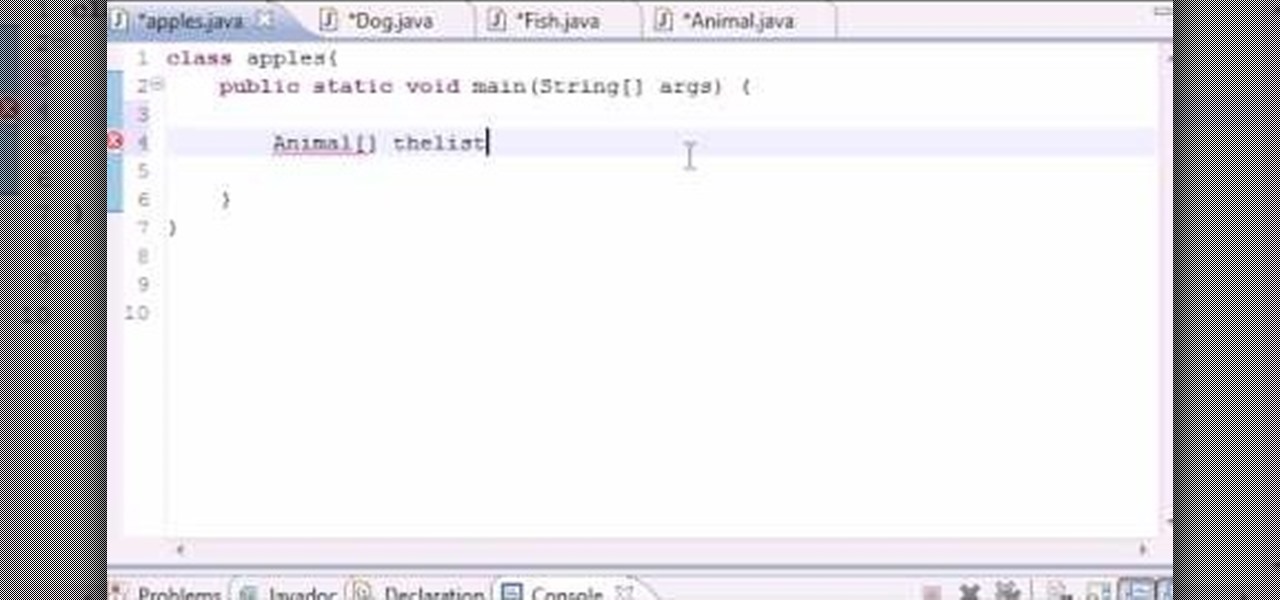
Want to program your own Java games and applications but don't know beans about object-oriented programming? Never you fear. This free video tutorial from TheNewBoston will have you coding your own Java apps in no time flat. Specifically, this lesson discusses how to work with simple polymorphism when writing code in the Java programming language. For more information, including detailed, step-by-step instructions, watch this helpful programmer's guide.

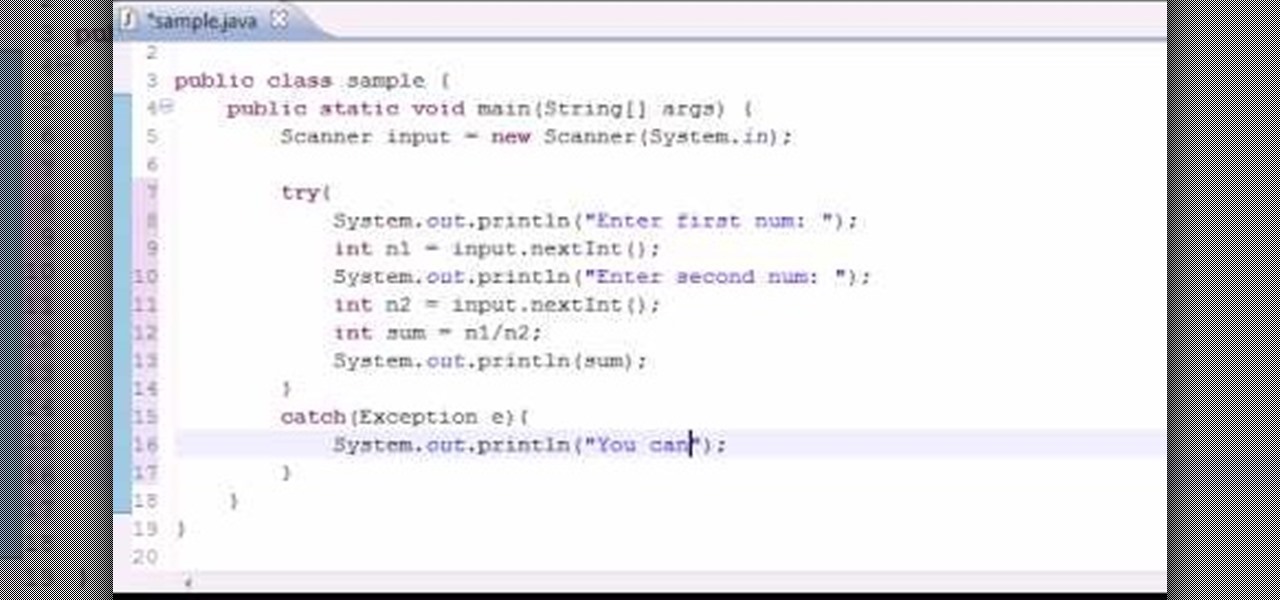
Want to program your own Java games and applications but don't know beans about object-oriented programming? Never you fear. This free video tutorial from TheNewBoston will have you coding your own Java apps in no time flat. Specifically, this lesson discusses how to to troubleshoot errors and exceptions when writing code in the Java programming language. For more information, including detailed, step-by-step instructions, watch this helpful programmer's guide.