When you're taking a video in the Camera app on your iPhone, there's a little white shutter button in the corner that lets you take a still image while you're filming. Apple brought that same concept over to the FaceTime app in iOS 11, iOS 12, and higher, so you can take Live Photos of your friends during video chats.

Single-serve yogurt cartons are so much fun. They're delicious, convenient, and the perfect size; no wonder it's so fun to open a new container of yogurt every morning. Yet as awesome as single-serve yogurt cartons are, there's something you really need to do: stop buying them!
A Steampunk's Guide to Sex was the subject of a recent successful Kickstarter campaign, and I now hold the finished book in my hands. As such, I can say (mostly) unreservedly that you should buy this book. Allow me to tell you why, before I get into the nitty-gritty about the book itself. Sex is something of an odd topic in America because it's perfectly legal, and yet taboo. Unlike things that are illegal and not taboo, like drug use, murder, theft, etc. What this means is that children can ...

Steampunk music is an oft-debated genre, full of bands playing all sorts of different sounds. While this can make it difficult to generalize about the genre as a whole, it means that the average person is bound to like at least some Steampunk bands. That's why it's a great idea to support some independent Steampunk bands this holiday season by buying their music for yourself, or sharing it with someone else.
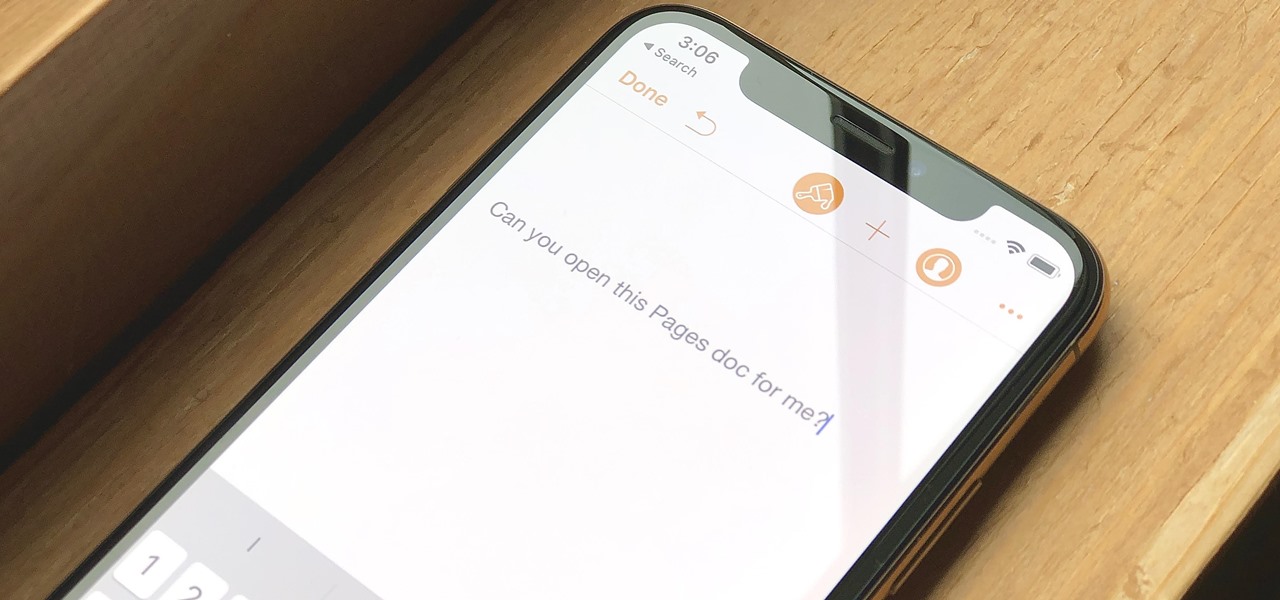
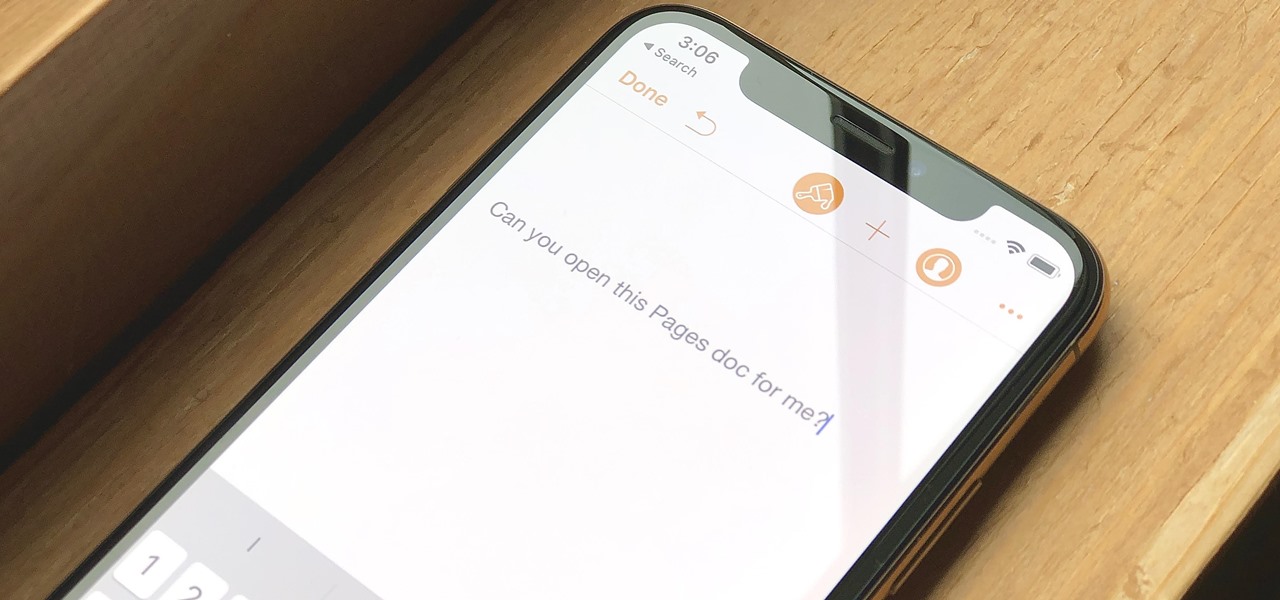
Let's say you have an important report to submit, but you want to check it over for any last-minute edits or changes. Times running out, and you simply can't find this Pages document anywhere. Wouldn't it be great if you could just ask your iPhone to open the report for you, so you could stop wasting time searching and finish the paper? Well, thankfully, Siri can help you out with that.
No one wants to appear stupid. Whether you rely on lengthy, complicated vocabulary to show your smarts, or enjoy highlighting your speedy mental math skills, everyone prefers emphasizing intelligence over hiding it.

As you know, it's impossible to be a Steampunk without a pair of goggles. In fact, there are entire communities dedicated to judging other Steampunks based solely on their goggles. A Steampunk without goggles is like Samson without his hair, or a duck without a beak—totally powerless. As I'm sure you also know, the right pair of goggles can instantly render any outfit Steampunk, no matter what it looks like.

One of Apple's most touted (but seldom seen on social media) apps, Clips, got an update on Wednesday.

How to fight multiple attackers with 5 simple Wing Chun techniques that will help survive a attack by a gang of multiple attackers. These are some of the best tactics on how to fight a group of people while staying safe.

It's easy to forget sometimes that even when you're sitting in the basement playing Grand Theft Auto 5 Online that you're not really alone. Everything you say into the mic can be heard by anyone else in that same session.

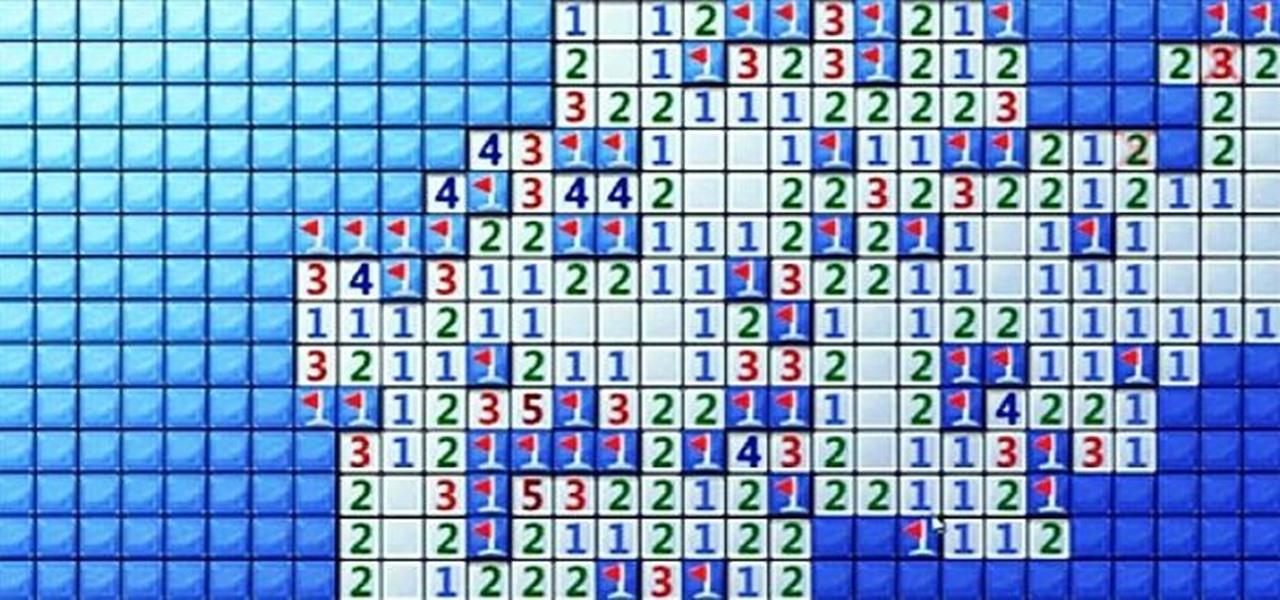
Minesweeper is one of those games that everyone plays, but hardly anyone actually knows how to play. Most people just click random squares and see how far they can get.

Deep fakes, the art of leveraging artificial intelligence to insert the likeness and/or voice of people into videos they don't otherwise appear in, typically focus on celebrity parodies or political subterfuge.

There aren't many people who will believe that a prosthetic zipper face or gunshot wound to the eye (disgusting as they are) are real, but greyscale from Game of Thrones? That'll really unsettle people for awhile because it totally looks like an actual, honest-to-God infection that someone in 2017 could conceivably have. Which makes it very effective come Halloween, whether it's for a full-on Princess Shireen, Jorah Mormont, or Stone Man costume, or to just infect a completely different chara...

T-Mobile's credit-checking system was recently hacked, and this one is about as bad as it gets. The names of 15 million customers, their date of birth and social security number, as well as driver's license numbers and additional information was illegally accessed, meaning the potential for identity theft here is huge.

Hackers have stolen over 225,000 Apple user's account information from countries all over the world—including the United States, China, and France—in what many are reporting to be the biggest known Apple hack in history.

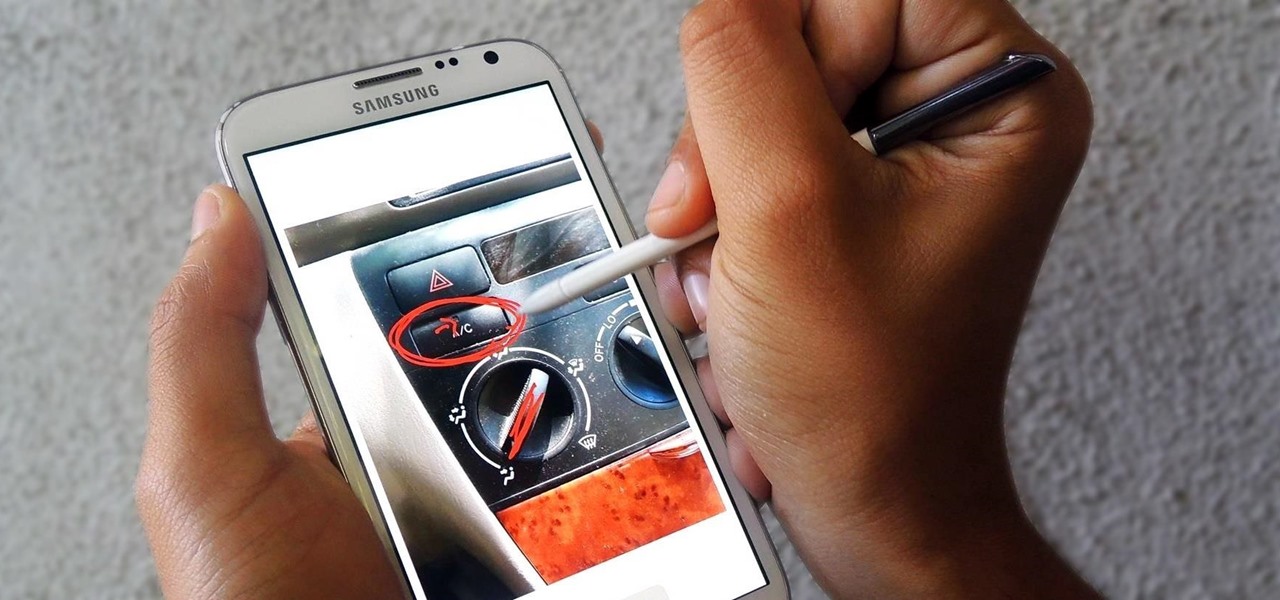
Trying to explain something difficult over the phone can be pretty frustrating if the other person doesn't understand you. Using text messages can be useless for auditory learners, and a phone call won't do much good for a reading or visual learner.

Full screen mode, also called immersive mode, is one of the most popular features on CyanogenMod, but it's almost exclusive to CM and other custom ROMs. What this feature does essentially is remove the Status bar and soft keys from your screen, creating a more mesmeric feel.

In early 2000, at the age of 19, Noah Kalina began taking a photo of himself with the same facial expression—every single day. Six years and over 2,000 photographs later, Kalina turned his project into a time-lapsed montage on YouTube. In just one day, his video received over a million views.

The first alarm clock in recorded history can be traced back to ancient Greek philosopher Plato, known for laying the foundations of Western philosophy and science. Plato was said to possess a very large water clock with an alarm signal similar to that of a water organ.

Adobe Premiere Clip is a great mobile app for users with little to no editing experience. Its automatic editor will sort your clips into a fun video in seconds, leaving you to just choose the music. But what if you're looking for more than automatic settings? What if you want some serious control over your project, from the editing to the way the image looks?

Most of us equate feeling cold with catching a virus—but we've also heard plenty of debunkers proselytizing that being cold isn't what gives you the flu.

A new hack has reopened an 8-year-old iPhone security loophole that Apple thought it had fixed back with iPhone OS 2.2. This is not one of those times when a theoretical attack gets identified and blocked quickly by Apple. On the contrary, it's a hack that actually exists right now, and it can have some serious real-world repercussions, so this is something all iPhone users need to be aware of.

If you read my previous post, "How to Hack into a Mac Without the Password", you know that it is very easy to break into someone's Mac if you have physical access to the computer. Now the question that lies is, how do we protect ourselves from this happening to us? Well, here is a way that guarantees that no one will be able to change your password through OS X Recovery.

There are few things more satisfying than fulfilling a craving with instant gratification. Companies like Pillsbury and have made this possible with the introduction of their famous Ready to Bake Cookies line: just rip open the package, break off the cookies along the creased lines, place on a cookie sheet, and bake.

One of the biggest hits this past fall wasn't a movie, television show, or book—it was an unassuming podcast called Serial, which centered around an unsolved murder from 1999 of a high school student in Maryland.

When we look back on it, 2014 may be remembered as the Summer of Android Wear. With two new flagship smartwatches due out soon, Google's been readying its mobile OS for the wearables sector.

It started in Australia, and now seems to have made its way statewide—hackers are remotely locking iOS and Mac devices, holding them for a $100 ransom. Users awoke to the loud "lost iPhone" ringtone, with a message on their lock screen stating that "Oleg Pliss" has hacked their device, and that "they" will unlock it after being sent $100 through PayPal.

I'm a pretty nice person, so when someone asks me to take a group picture of their friends or family, I can't easily say "no," even if I have somewhere else to be. Even worse—sometimes I'm the one asking, fully knowing just how annoying it can be. Maybe you've been told "no" before, and have had to settle for being left out of the picture, which kind of sucks.

If you thought humans were reading your résumé, think again. Robots do, and their one solitary objective is to systematically crush the hopes and dreams of those who don't make the cut. Instead of paying a few humans to read thousands of résumés over a couple weeks, many companies use computer programs that can do the job in less than an hour. In fact, at least 90 percent of Fortune 500 companies use what they call an applicant-tracking system, aka rejection machines.

We don't generally think of medicine as being very relevant to Steampunk, but it was a big part of Victorian science fiction. Notable examples that you may be familiar with would be Frankenstein and The Strange Case of Dr. Jekyll and Mr. Hyde.

Most of us have some sort of malware scanner or antivirus program on our computers, but what about our smartphones? A lot of people don't realize that computers aren't the only devices that are susceptible to malicious software and apps—they can follow you on your smartphone or tablet, too.

If you're here, you're probably one of the seven people dedicated to making Mac n' Cheetos a permanent part of the Burger King menu.

Researchers at the cyber security firm Zimperium have recently uncovered a vulnerability in roughly 95% of Android devices that has the potential to allow hackers to take total control over your phone with a simple picture message (MMS). The gritty details of this exploit have not been made public yet, but hackers now know the general framework for this type of attack, so you can be certain that they'll hammer out the details in no time.

Eggs are a staple food for most Americans, which is no surprise, considering how necessary they are in savory and sweet recipes alike. On their own, they're usually not too eggs-citing. However, these clever egg hacks will make your egg-making easier, more fun, and more interesting.

Seeing that you probably can't go ten minutes without lying (according to this study), you're probably interested in becoming a better liar. The best way to do so is to learn what makes a bad liar, and then do the opposite.

People take their Black Friday shopping seriously. Some of them are even willing to fight over it. Every year the stories get crazier and crazier, and someone always gets hurt (or even killed).

In October of 2017, Mathy Vanhoef released "Key Reinstallation Attacks: Forcing Nonce Reuse in WPA2." This paper demonstrates a way to decrypt traffic on practically any WPA2 network, the most commonly used form of wireless security (seeing as all other forms of Wi-Fi encryption have already been broken). Practically all of the network-connected devices we use will need to be updated in some way in order to protect against this vulnerability, each of them in a different way.

In this video, we learn how to prepare yourself for a major disaster. If you haven't planned ahead for storing water, you are going to be in big trouble. Your first option is to go purchase liters of water from the grocery store. The recommended quantity to store is 1 gallon per person per day. If you don't want to spend money at the store, you just need to fill up empty bottles with water from the tap and store these after cleaning. You can also fill the water in a large jug, just make sure ...

Are you an iMovie user looking to double down on yourself? Well, if so, watch this video and see how to clone yourself, quickly and easily. I mean, who wouldn't want to make two of themselves? It could be so helpful for so many situations! Though cloning may be far in the future, we can still clone ourselves in Videos. Apple's new iMovies, have changed from being small easy video processors to a more complex higher quality Video editing software. This video will use the Green Screen Function ...

Do you wish there were more of you? Well, at least two? At least in a video? This sweet video will show you how to do just that with Apple's iMovie. You'll also need a sturdy tripod that you DO NOT move. This is essential to creating the effect. If you move the tripod, this effect will NOT work, or come off as convincing. Also, of course, you will need a video camera. This technique is also possible by using other video editing software tools as long as they are capable of doing blue screenin...