Cryptography is the science of keeping secrets, or more specifically, the science of disguising them. As a point of fact, cryptography has progressed quite a bit farther and now encompasses file and message integrity, sender authentication, and pseudo-random number generators.

What started as an accessibility setting for hearing aids turned out to be a super helpful tool for anyone with a good set of Bluetooth headphones. The problem is that most iPhone and iPad users still don't know about it. If you're one of them, you need to see what this underrated gem in iOS and iPadOS can offer you.

While our smartphones are many things, one of their primary functions is to make calls. Many of us try to avoid ever having to make calls, but there are situations when it's a must, such as wishing your grandma happy Birthday or calling 911 — and in those times you want stellar call quality.

Hackers often find fascinating files in the most ordinary of places, one of those being FTP servers. Sometimes, luck will prevail, and anonymous logins will be enabled, meaning anyone can just log in. But more often than not, a valid username and password will be required. But there are several methods to brute-force FTP credentials and gain server access.

In a time where we're more connected than ever, privacy and security have never been more important. Maybe you're not concerned, but I'm sure there's someone in your life who is, and shopping for them can be daunting. However, with these gifts, you can provide them the tools they need to enhance their protection.

Trying to figure out which music streaming service to subscribe to can be a difficult task when the playing field is so crowded. Each has its benefits, as well as downsides, so finding the right one for your needs and wants can take a lot of overwhelming research. But we've done all the research for you to help you find the best music subscription your money can buy.

If you have a modern iPhone, you have an excellent video recorder at your disposal. Every iPhone since the 6S has the ability to shoot in 4K resolution, and each new iteration has brought new capabilities to the table. But even the best mobile shooter can use a little extra help. That's where these video recording apps come into play, to ensure the footage you capture is as good as can be.

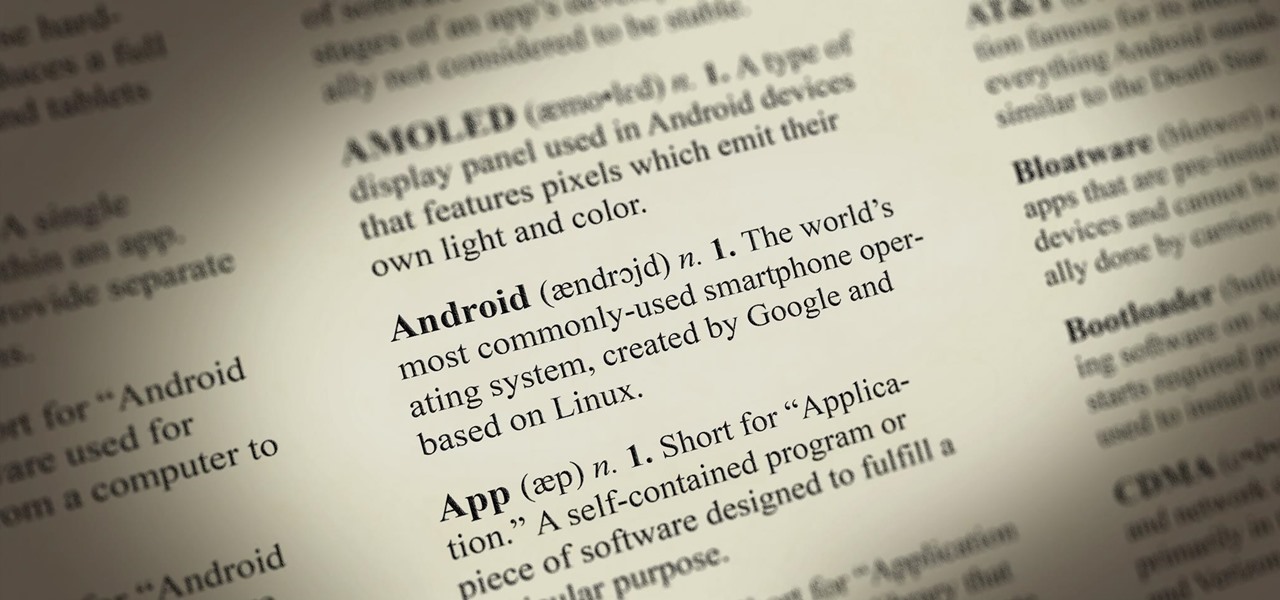
Android comprises an entire ecosystem of apps, games, functions, and features, so it would only make sense that it has its own lexicon. Words, phrases, and acronyms that didn't exist ten years ago are now used in an off-the-cuff style by developers and support technicians across the web.

Health, safety and security are three main issues which determine if your cruise is a successful vacation.

Check with your ISP about alternatives to the Internet. The speed of your Internet connection is the most important variable in your download speed. If you have dial-up Internet access, consider upgrading to a Digital Subscriber Line (DSL) or cable connection. Even if you already have cable, your ISP could have faster cable service available.

Here at Null Byte, we've spoken a lot about securing and anonymizing traffic. This is a big deal. With all of today's business taking place electronically via computers, we need to be secure when on-the-go. A lot of businesses don't even train their employees to secure their computers to protect from various threats. Here are a few things that should always happen when doing business on computers:

Wouldn't it be nice to just sit at your buddy's house, plug into his network, and see exactly what he's doing? What if it was as easy as that? What makes packet sniffers like Wireshark such potent tools is that a majority of local area networks (LANs) are based on the shared Ethernet notion.
Keyword Research Tool. This tool provides you with the ability to directly query the Google keyword databases and truck load of choices of keywords to use in your campaigns. With this keyword tool you are able to create, manage your keyword list and integrate with other tools like competition spy and list builder.

Here at WonderHowTo, we are often presented with morally questionable HowTo's. When it comes to stocking our library, we have to weigh in the community value of indexing tutorials with potentially negative repercussions. Where is the line when it comes to areas like weapons, sex, and drugs?

In many ways, we center a large portion of our lives around festivals. They provide us days off from work, allow us time to be content with our families and loved ones, and a give us a chance to eat as much as we want without Aunt Carol saying something about our necks (it's thyroidal, Carol). However, some festivals are determined to push the needle to crazy. Here, for your consideration, are those offenders.

Could the world really be coming to an end tomorrow? Presuming you believe the biblical prediction from 89-year-old Harold Camping, May 21st, 2011 is undeniably Judgment Day. If you have confidence in that prophecy, you're probably not even reading this because you're too busy either A) preparing for the Rapture or B) sitting in your backyard bunker hoping to outwit annihilationism.

As some of you may know, contemporary king of kitsch Jeff Koons exhibited at the French palace of Versailles last year. While the exhibition was embraced by many as an exciting context for contemporary art, predictably old fogies and critics of the art market balked.

Chris Burden's latest piece is a portrait of L.A.'s hot mess of traffic, entitled Metropolis II. The artist has constructed a miniature highway system, complete with 1,200 custom-designed cars, 18 lanes, 13 toy trains and tracks, and a landscape of buildings made with wood block, tiles, Legos and Lincoln Logs. Burden tells the New York Times:

A Self-Protection Guide 1) You can help protect yourself from violent crimes.

In the first part of this series, we learned about darknets, as well as how they came about. But these patches of forgotten Internet are not the oasis of free information you might think. Despite being hidden—or just harder to come across—these networks are no more safe then anywhere else on the 'clear' Internet. The nature of networking and routing means your location is always known in server logs. It only takes one phone call to your ISP with your IP address to obtain both your physical ad...

Record stealthily, in the dark. This hack is simple and will turn any LED flashlight into an infrared night vision light you can use with any video camera.

By Louis Tharp RealJock.com is pleased to present this first in a series of articles on improving your swimming form and performance from Louis Tharp, out gay man, swim coach for the Army Triathlon Team at the U.S. Military Academy at West Point, and author of the new book Overachiever's Diary: How the Army Triathlon Team Became World Contenders. Tharp is the first out gay coach in the history of West Point.