This is my first contribution in an ongoing series on detailing the best free, open source hacking and penetration tools available. My goal is to show you some of the quality tools that IT security experts are using every day in their jobs as network security and pen-testing professionals. There are hundreds of tools out there, but I will focus and those that meet four key criteria:
There are countless ways in which you can turn your love of tech and coding into a full-fledged career — from developing apps and websites as a freelancer to working in the IT departments of small startups or major tech companies. But one of the best ways that you can put your programming skills to good use is to join the increasingly important world of cybersecurity.

Another major retailer is putting all its chips in on the relentless rise of selfie culture. Sally Beauty is rolling out kiosks to try-on "some of its best" hair dyes in 500 of its stores throughout the US. The in-store augmented reality-powered kiosks invite you to view yourself on video, overlay a punky (or otherwise) hair color, and snap a selfie on the screen to share your #glowup with friends.

The Microsoft HoloLens has a fairly passionate, yet relatively small group of users pushing the developer-centric device forward, mostly spreading the word about the device through word of mouth and meetups. But this weekend, during the annual NBA All-Star festivities, we got a look at how Microsoft may be planning to market the device if it ever goes truly mainstream.
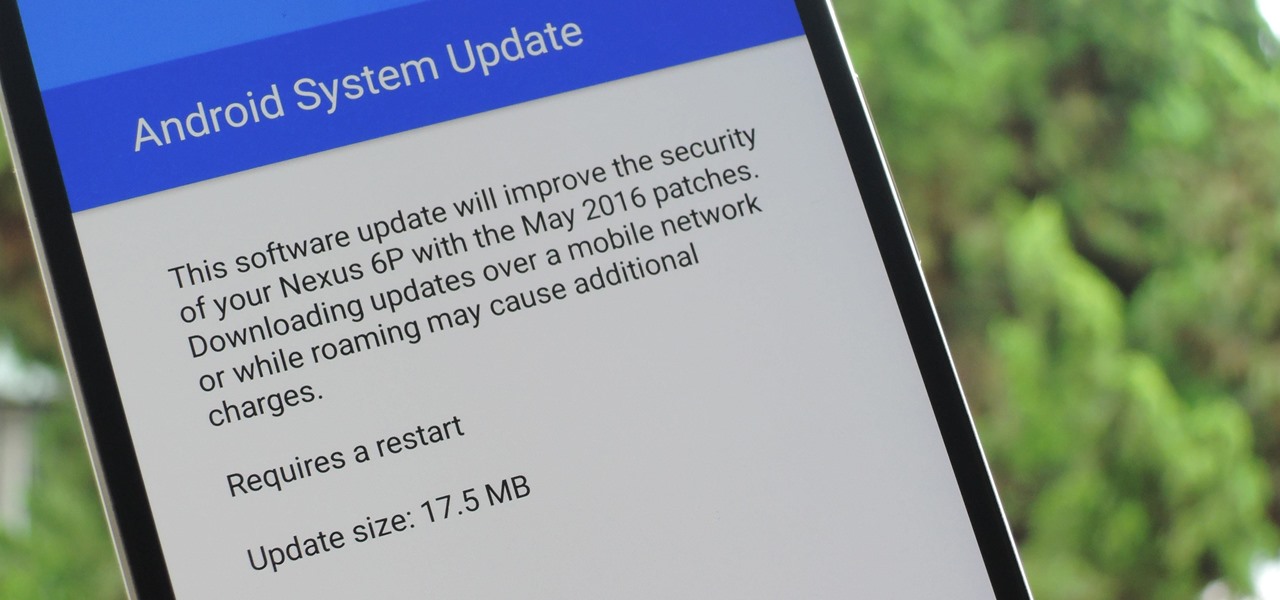
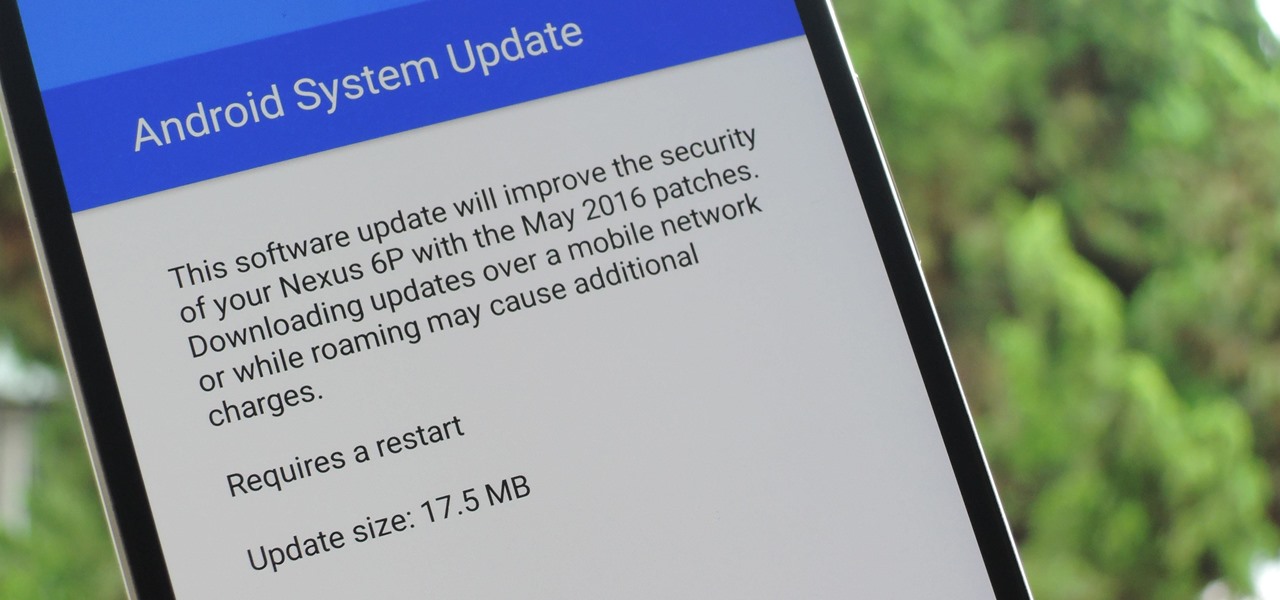
The beauty of Nexus devices is they receive firmware updates faster than any other Android phone, and keep getting updates for years longer than most of the competition. This means that you can always use the great new features that come along with an Android update, and even more importantly, your phone gets monthly security patches to keep hackers and malware at bay.

Greetings, hackers and friends! I know it has been a while since I posted a tutorial, and hopefully I can make up for that by posting a series.

We're living in uncertain times. The sudden outbreak of the novel coronavirus and subsequent self-isolation of roughly half the world's population has led to a massive reorganization of the economy, countless layoffs, compromised security networks, and a variety of other significant disruptions that will forever alter the landscape of our daily lives.

For $0.25 per transaction, PayPal will soon be allowing you to transfer money through their app that will get delivered within seconds rather than days.

Tequila is a hard liquor that's often been misunderstood. Produced from the agave plant, this aged spirit has complex flavors that bloom the longer it's aged and can rival the finest scotch.

If you want to quickly pick up a new skill over the holidays, learning to build your own Apple apps is one of the most impressive ones you can work on. This complete course bundle on SwiftUI and iOS 14 will have you submitting your own iOS apps to the App Store in just two weeks. Right now, The iOS 14 & SwiftUI Bootcamp Bundle is on sale at 95% off, for just $24.99 (regular price $600).

It's no secret that more and more talented computer science gurus and programmers are turning toward high-paying careers in engineering. Today's engineers stand at the forefront of some of the world's most important and exciting technological innovations — ranging from self-driving cars and surgical robots to large-scale construction projects and even space exploration—and our reliance on these talented data-driven professionals is only going to grow in the coming years.

In the not-so-distant past, cloud computing was thought of primarily in terms of online storage platforms. Now, however, massive cloud infrastructures are used by virtually every major business to reach clients, manage data, and deliver services.

If you're a regular Null Byte reader, you probably know your fair share of programming languages and have at least some experience with web or app development. But it's possible to apply your hard-earned coding and tech talents to other closely-related fields as well.
I see many people posting the same thing on the internet. "How do I become a hacker? Where do I commence?"

Welcome back, my rookie hackers! Many newbie hackers focus upon the technical aspects of hacking and fail to give enough attention to social engineering. In fact, I would say that technical hacks should ONLY be attempted if social engineering attacks fail. Why bother spending hours or days trying to hack a password if someone will simply give it to you?

BitTorrent—corporations hate it with a passion, but the people love it. The notorious file-sharing protocol was responsible for 36.8% of all upstream Internet traffic last year, as well as 10.3% of all traffic.

In a world that's becoming increasingly dependent on a variety of AI and machine learning applications, Big Data reigns supreme. As the primary forces behind everything from self-driving cars and surgical robots to home automation systems and even space exploration, Big Data and AI stand at the heart of today's most important innovations.

If you're a tech-savvy coding pro, you have a virtually limitless number of great career choices to choose from. Whether you're interested in working at a small tech startup, freelancing as a cybersecurity specialist, or founding the next Google, having a solid understanding of development terminology and general programming will inevitably get you far.

While we haven't covered Amazon Web Services, or AWS, on Null Byte before, Amazon's cloud computing platform is ripe for attack by hackers, pentesters, and cybersecurity researchers. It's also an excellent cloud hosting service to build or use vulnerable-by-design AWS setups and frameworks.

Many new parents will tell you how hard it is to name a baby. Some have stories of how they knew what the name of their child would be from before conception, only to change their mind when they were born. Sometimes new babies can go weeks without a name since there is an endless selection to choose from.

Welcome back, my rookie hackers! So many readers come to Null Byte to learn how to hack Wi-Fi networks (this is the most popular hacking area on Null Byte) that I thought I should write a "how-to" on selecting a good Wi-Fi hacking strategy.

Welcome back, my greenhorn hackers!

Welcome back, my hacker apprentices! Although there is a multitude of different hacker types, the one target they all share is the database. I often refer to the database as the hacker's Holy Grail, or the ultimate prize for an effective hack.

Welcome back, my greenhorn hackers! Now that we're familiar with the technologies, terminology, and the aircrack-ng suite, we can finally start hacking Wi-Fi. Our first task will be to creating an evil twin access point. Many new hackers are anxious to crack Wi-Fi passwords to gain some free bandwidth (don't worry, we'll get to that), but there are so many other Wi-Fi hacks that are far more powerful and put so much more at risk than a bit of bandwidth.

TouchDevelop is a browser-based programming tool that allows anyone to build your own Windows 8 apps directly from any touchscreen device, including iPad, iPhone, Windows Phone, Android, PC and Macs. Once the script is created and the app proves to work, it can be placed in the Windows Store for free or purchase.

This year, Google released two Nexus phones to glowing reviews, and as we've grown to expect, the Android community wasted no time in coming up with a root method for both. In fact, legendary root developer Chainfire even devised an entirely new "systemless" method for rooting that should make updating a bit less complicated, along with a few other benefits.

Conducting phishing campaigns and hosting Metasploit sessions from a trusted VPS is important to any professional security researcher, pentester, or white hat hacker. However, the options are quite limited since most providers have zero-tolerance policies for any kind of hacking, good or bad. After researching dozens of products, we came out with 5 potentials that are ideal for Null Byte readers.

An attacker with shell access to a Linux server can manipulate, or perhaps even ruin, anything they have access to. While many more subtle attacks could provide significant value to a hacker, most attacks also leave traces. These traces, of course, can also be manipulated and avoided through methods such as shell scripting.

Around this time in 2016, the predictions for the next year had reached something of a consensus: 2017 would be the year of augmented reality. But a funny thing happened on the way to the future — nothing much, really. At least not for the first half of the year.

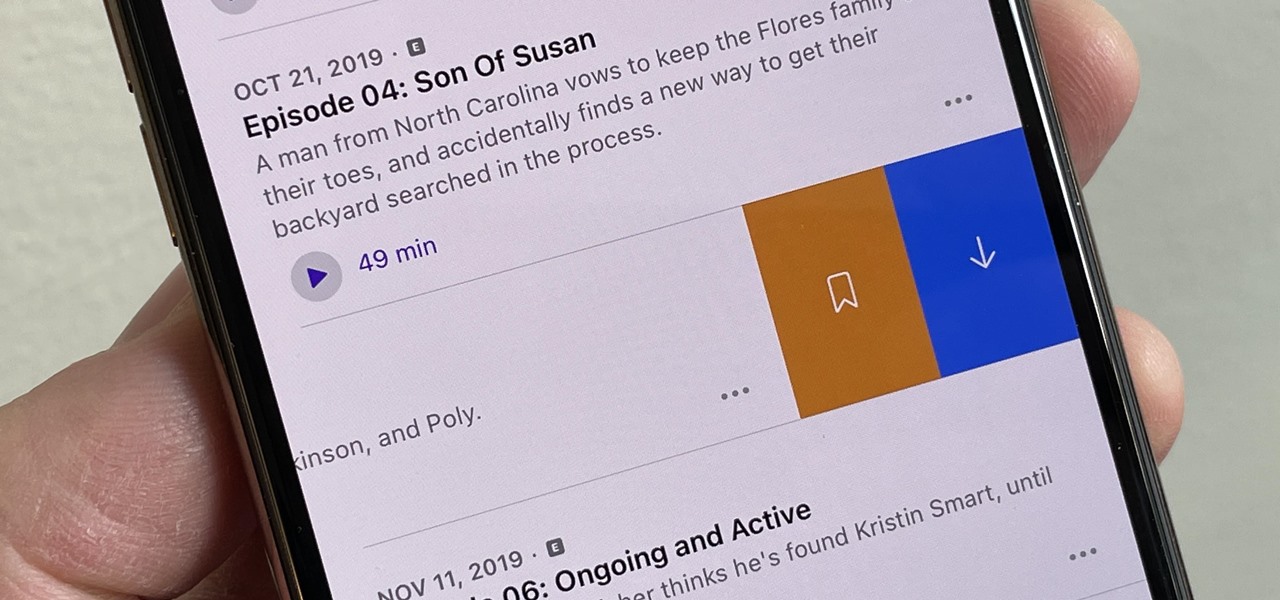
Spotify has caught up to Apple in monthly podcast listenership and is even forecast to surpass Apple soon, but Apple just made some serious changes to its Podcasts app for iOS and iPadOS that could keep Apple at the top.

Android comprises an entire ecosystem of apps, games, functions, and features, so it would only make sense that it has its own lexicon. Words, phrases, and acronyms that didn't exist ten years ago are now used in an off-the-cuff style by developers and support technicians across the web.

This retro informative video gives a general overview of a woman's menstrual cycle. A curious young girl asks her family questions about having a period, what's normal, what isn't, who gets one, who doesn't. While this video feels a bit dated, and eschews medical terminology, it offers some basic insight to that time of the month. Check out this video and learn how to understand the feminie menstrual cycle.

Sailmaking is the skill of designing, cutting, and trimming ship sails. Get expert tips and advice on canvas and sailing terminology in this free video.

In this video series, watch as trash talker extraordinaire Ryan Tapp teaches how to talk trash. Learn the objective of trash talk, how to verbally and physically smack talk, how to use technology, general media, broadcasting to talk smack, how to use verbal and physical imitation to humiliate your opponent, how to incite others to trash talk, how to use sports and gaming terminology to talk trash, and how to insult mothers and significant others as a part of trash talk. Your friends will prai...

There's three types of animal lovers in the world. The first are your basic pet owners. The ones with a

Think you have what it takes to amputate your own arm? What about somebody else's foot? Now, thanks to the wide array of mobile apps available from the iTunes App Store, you might not need to attend medical school to perform a tracheostomy.

Thinking of trying something new this weekend? How about wind surfing? Take a look at this instructional video and learn how to assemble and rig up your board for windsurfing. The board has a lot of parts to it, so be sure to follow these instructions step by step as it meticulously details all of the essential components you'll need to wind surf. This tutorial also covers how to rig steer and tacking so you can change course as you wind surf. Terminology is also explained in this tutorial. A...

This is a how-to demonstration for left-handed crochet, working the 'single crochet' stitch (American terminology).

This video production was released in coordination with the 2009 job posting for Army National Guard “Internment Specialists” that Kurt Nimmo reported on at the time. (The original post has been conspicuously removed since then). Notice that the job description, title and duties all seem to match the terminology used in the leaked document FM 3-39.40: INTERNMENT AND RESETTLEMENT OPERATIONS (at Army p/w protected link) outlining the plan to set up camps both globally and domestically (Yes, the...

Makeup application instructions can be hard to follow, if you can't tell your underbrow from your lower lid. This video maps out all the contours and planes of the face, from the browbone to the cheekbone to the jawline. Watch this video beauty tutorial and learn the proper terminology for parts of the face and how to distinguish them from one and other. Map out your face for easy makeup application.