
How To: Crochet a cluster shell
Hey crochet junkies, looking to try something new? In this video tutorial, learn how to crochet an adorable cluster shell. For written instructions, you can visit Crochet Mania's blogspot here.


Hey crochet junkies, looking to try something new? In this video tutorial, learn how to crochet an adorable cluster shell. For written instructions, you can visit Crochet Mania's blogspot here.

Learn how to crack an egg so that you can preserve the shell in simple steps. First take an egg and a butter knife and you have to make a hole at its top. To make the hole gently tap the top of the egg to make a crack. Now insert the knife in the crack and peel its top out. Pour the egg yolk in a container and rinse the shell several times with hot water. Spray an anti-bacterial spray to kill any germs in it and let it dry for sometime with its hole facing downwards.

Place slip knot on hook. Hold yarn taut with 2 sets of 2 of fingers placed about 1½” apart, with tail in other hand. Create loop that crosses over bottom of 1st strand with loop toward right side. Fold loop over main strand going past tail. Insert hook below at tail strand. Pull up a loop using main strand for this loop. Pull 2 ends of yarn taut while leaving slip knot on hook. In 1st chain work 1 single crochet. Skip 2 chains; work 1 double crochet in 4thchain. Picot stitch by chaining 3 & a...

Cracking an egg is a simple task once you have the technique down, so check out this video. Keep the shells out of your food!

In this installment from the Unorthodox Hacking series of Internet security tutorials, you'll learn how to get a shell on an Oracle database. To see how to pop a shell from within Oracle or even perform a port scan from the database itself, watch this hacking how-to.
If you're interested in learning a general purpose, high-powered programming language, Python might be the way to go. In this installment from his video tutorial series dedicated to programming in the Python programming language, you'll learn how to set up your bash shell for programming in Python.

Egg yolk mixed with your egg white? Bits of shell in your egg yolk? Here's an efficient and nearly foolproof way to separate whole eggs. With an added bonus...you get to play with your food! Watch this how to video to learn a great way to separate eggs.

With this video tutorial and with help from a little black powder, you'll know all you need to make small can shells for some awesome aerial fireworks.

The Catherine's Wheel is a great technique to add to your crocheting repertoire, and it's easy to learn as it's just a variation of the more basic round shell stitch. Learn how to crochet the Catherine's Wheel pattern by watching this handicraft how-to video.

Improve crocheting skills by creating solid motifs. This how to video is a crocheting tutorial that shows how to create a three sided solid motif. Crochet several of them, bind them together and create larger handmade projects. Learn these basic stitches by following along with these simple step by step instructions.

This video will walk you through the beginning to end on painting a RC (radio controlled) vehicle shell. Everything that you need to know on how to paint a shell is on here, from shaker cans (spray paint) to airbrushes. I use a Iwata by the way and a harbor freight air compressor. The paint used in this is Pactra silver and black. The airbrush paint is Spaz Stix candy apple green, blue, dark blue, and white. The lightning effect came out pretty well in my opinion, but you be the judge.

This shell embed soap is perfect for summer beach houses no matter where you live. And, it's very easy to make.

Learn how to teach your players the basics of defensive positions with the help of this great defensive shell basketball drill.

This is a tutorial for using the multi-replicate function in Bryce to create organic-looking shapes (shells, horns, elephant trunks, etc.)
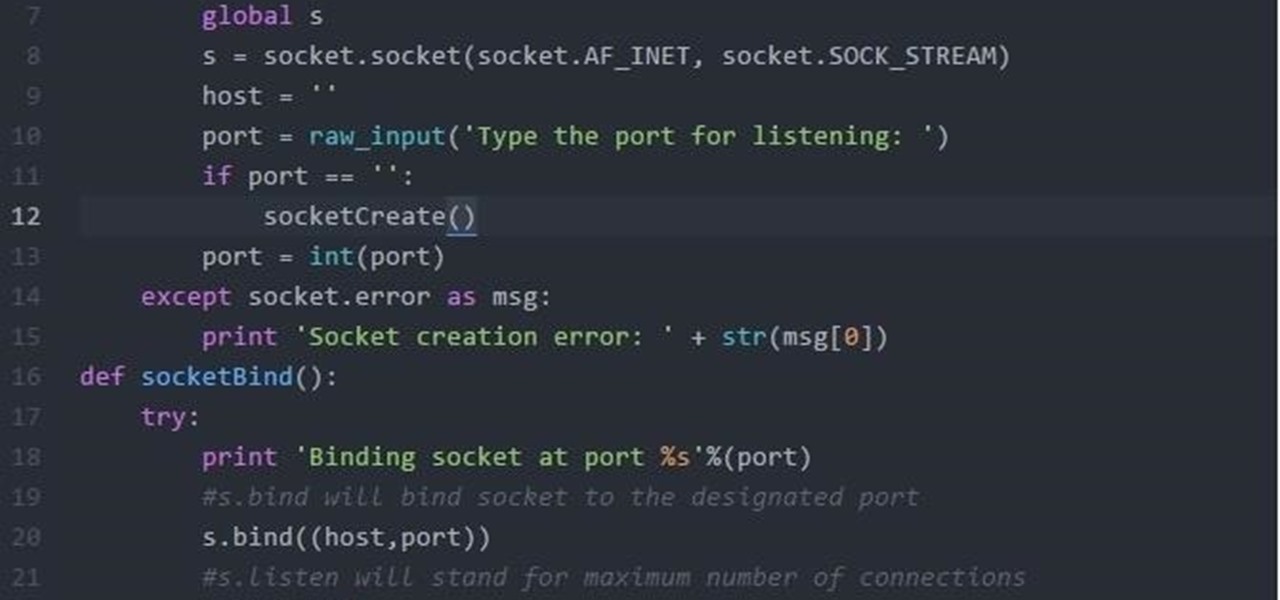
Hi Folks. This is my first post. I will teach how to create a server and client python reverse shell using sockets and python language. The script i'll post here is going to be very simple, and from here you'll have the possibility to adapt to your own purpose. For example, my original script can download files, upload files, make changes to registry, create user accounts and more. I'm sure you could do it on your own too.

I've cracked thousands of eggs in my life, yet I still usually mess up when I make my morning eggs. Sometimes I crack the egg to hard and end up leaving half of the white on the counter. Other times I don't crack the egg hard enough, and end up spending 20 seconds digging with my fingers until I can pry apart the shell. Sometimes I puncture the yolk on the shell, and other times the entire thing slips out of my hands.
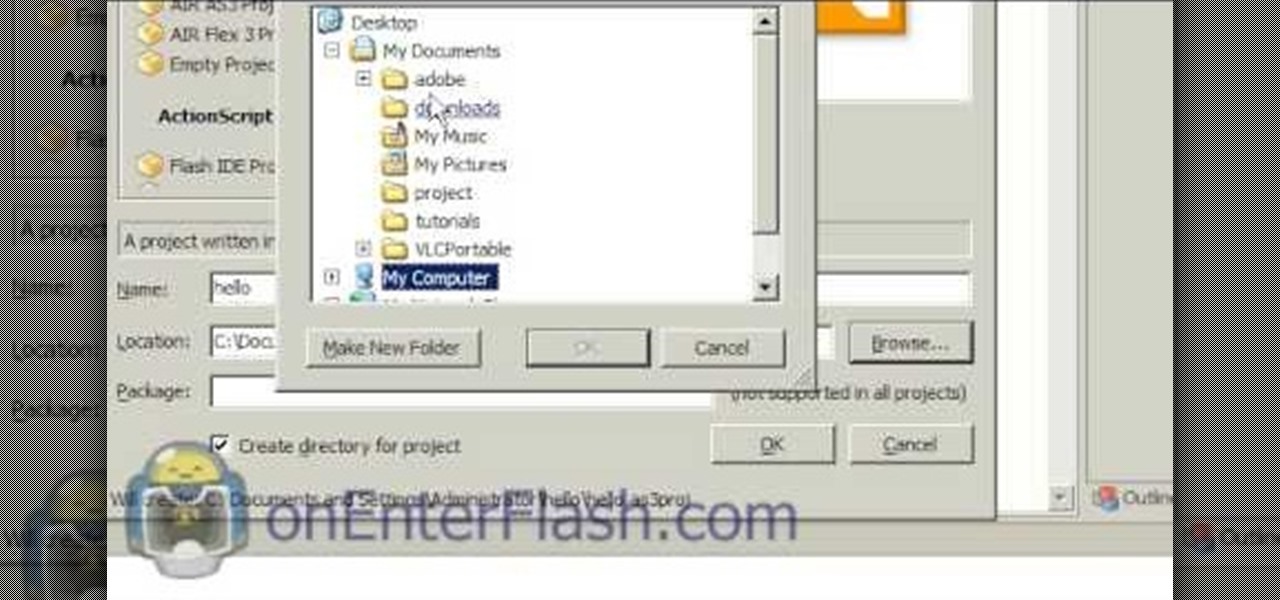
Flash development software can be very expensive stuff to come by, but it need not be. This video will teach you how to install and get started using FlashDevelop and Flash SDK together to edit Flash without having to shell out for the Flash IDE.

This is a method for making a native American free point spear using a bamboo stick, bamboo strips and some commonly found items. First take a sea shell and make a hole in it. Make the hole using a pointed stone and pierce an opening in the shell. Make the hole such that the shell fits the bamboo. Now the bamboo has to be split in half and for this you have to find a common stone which has a sharp edge on one side to split the bamboo. This is a common stone found anywhere. Now you have to tak...

Shell-covered pots are such beautiful decorations for the summer, bringing the beach into (or directly outside of) your home even if you live inland. They add a gorgeously breezy oceanic touch to your plants.

Julissa Roberts shows how to shuck an oyster. She shows us how to determine whether the oyster is safe to eat, how to shuck the oyster, and then one way to prepare a plate of oysters. If you don't properly check the oyster, and clean it, you could get a mouth full of sand, or get an oyster that smells like rotten fish. To check whether the oyster is good, smell it, it will smell like rotten fish if it's bad. Then tap the oyster on something solid, if the oyster is dead, it will sound hollow, ...

Ming Tsai with Simply Ming explains some shrimp basics. When you prep shrimp, you have to de-vein it, and you have to take the shell off. First cut off the head. Take a knife and slice sideways through the shell. Take out the vein, then get 3 bowls of water and add salt to 2 of them. After de-veining, put the shrimp in the first bowl of water. Keep adding shrimp until you get about a half pound of shrimp, or however much you wish to cook. Then peel the shrimp, and put it into the second bowl....
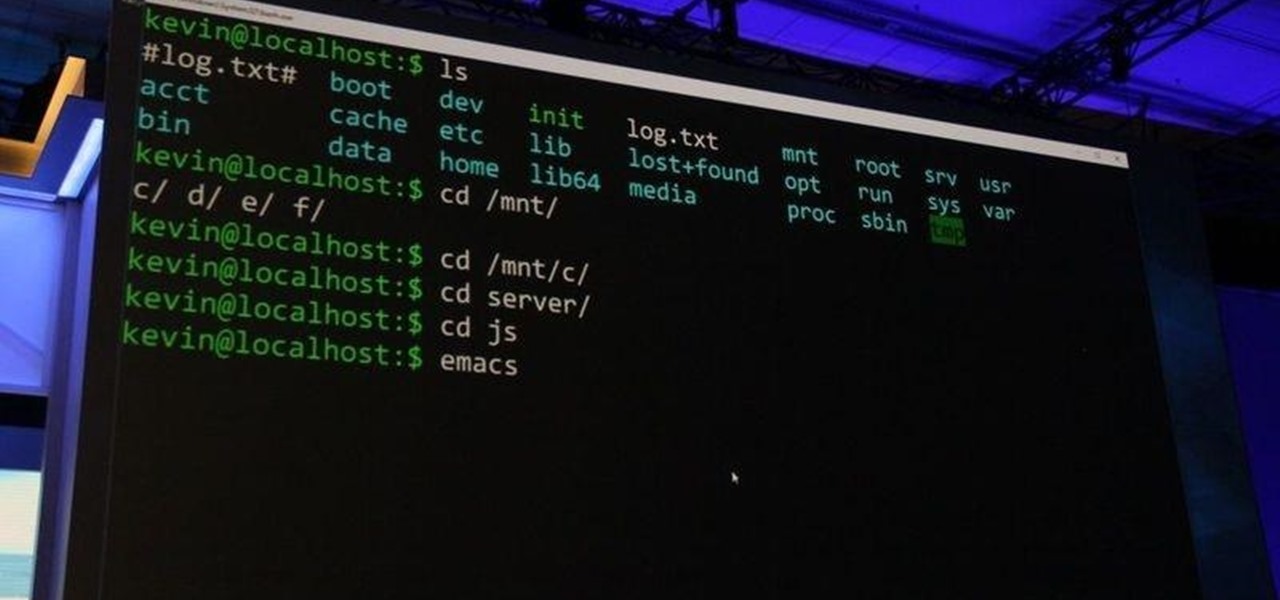
As most of you know, I am a strong advocate for using Linux for hacking. In fact, I would go so far as to say that you cannot be a hacker without knowing Linux well. I laid out various reasons for this in my "Why Every Hacker Should Know & Use Linux" article, and I even have a lengthy, continuing series on Linux Basics to help those new to Linux master it.

Hello, everyone. Stealth is a large part of any successful hack; if we don't get noticed, we're much less likely to be caught. In these next few articles, we'll be building a shell based on keeping us hidden from a firewall. There are many ways to stay hidden from a firewall, but we'll only be incorporating a couple into our shell. This article will outline and explain these evasion concepts and techniques.

When attempting to compromise a target, we want as much control as possible over the victim. Metasploit's meterpreter allows us to have immense control over the victim, the only issue is that sometimes we can't land a meterpreter. We may only be able to land a standard shell, but fear not, there is a way to upgrade our shell into the all powerful meterpreter!

In this video we learn how to make berries and whipped cream. First, pick the freshest berries, pastry shells, heavy whipping cream, powdered sugar, and vanilla. Start out by adding the cream to the bowl along with 2 tbsp powdered sugar and 1 tbsp vanilla. Take an electric beater and beat these together slowly at first, then increase the speed. Mix for several minutes until you see peaks start to form in the cream. Then, test it out to see if it tastes good. Serve this with your fresh berries...

Command injection is a technique used by hackers to execute system commands on a server, usually via a web application or some kind of GUI. This can happen when an application provides some sort of functionality to the user involving the use of system commands. When the input is not properly sanitized, commands not originally intended to be run are allowed to be executed.

It's 2017—new year, same us. We vow to keep scouring the net for the best how-tos and feature the makers and doers who create mind-blowing projects.

When a craving for crunchy tacos hits, it's undeniable. Don't Miss:

Shrimp is one of my all-time favorite foods. It's versatile, delicious, and incredibly fun to use in the kitchen.

This dish is easy, and the perfect thing to bring to a potluck or a picnic. Start with small pasta (such as elbow macaroni, shells or penne). After the pasta has been cooked, toss with your favorite fresh vegetables (such as tomatoes, olives, mushrooms or peppers) and some olive oil.

Variables are the core of nearly any programming language, and Python is no different. This tutorial shows you how to work with variables when you're starting to program in Python. This also shows you how to get familiar with the shell in Python.
Looking for instructions on how to reset the shell path on a Windows XP computer? It's easy! So easy, in fact, that this home-computing how-to from the folks at Britec can present a complete overview of the process in just over five minutes. For more information, including step-by-step instructions, take a look.

A beach ornament can be made by filling a clear Christmas ornament with red confetti, small sea shells and a bit of sand or glitter. Create a beach-themed ornament for the Christmas tree with instructions from an experienced craftswoman in this free video on Christmas crafts.

Improve you crocheting skills by learning decorative stitches. This how to video is a crocheting tutorial that will show you how to do shell decreases. Crochet several rows of this stitch to create larger yarn projects.

Improve you crocheting skills by learning decorative stitches. This how to video is a crocheting tutorial that will show you how to do shell increases. Crochet several rows of this stitch to create larger yarn projects.

One of our least favorite parts about making seafood for dinner? Dealing with all the shells that we have to painstakingly pull off one by one. But shucking the shells off your clams doesn't have to be a chore.

One of the ultimate goals in hacking is the ability to obtain shells in order to run system commands and own a target or network. SQL injection is typically only associated with databases and their data, but it can actually be used as a vector to gain a command shell. As a lesson, we'll be exploiting a simple SQL injection flaw to execute commands and ultimately get a reverse shell on the server.

File inclusion can allow an attacker to view files on a remote host they shouldn't be able to see, and it can even allow the attacker to run code on a target.

It seemed appropriate that we announce the winner of the first White Hat Award for Technical Excellence on the Academy Awards weekend. This is, in essence, our "Oscar" here at Null Byte. Remember, this contest began on January 4th, 2016 and just recently closed on February 15th. In this contest, I was looking for:

In this tutorial I will show you how to make a Macrame shell bracelet with pearls, it also has a very stunning look, kind of reminds me of Angel wings. Perfect for wedding, party and daily wear accessory.