Welcome back, my rookie hackers! Many newbie hackers focus upon the technical aspects of hacking and fail to give enough attention to social engineering. In fact, I would say that technical hacks should ONLY be attempted if social engineering attacks fail. Why bother spending hours or days trying to hack a password if someone will simply give it to you?

We all want to put our best face forwards on our social networking profiles. Facebook, MySpace, Twitter and all the rest are the best places to show great photos of yourself. You never know who might be looking. Employers, potential suitors, ex-high school classmates.. they are all snooping to see what you're doing and how you look these days.

One of the earliest players in the social virtual reality space, vTime, has just landed $7.6 million in new funding, which the company says is partially earmarked for developing and releasing an augmented reality version of its platform later this year.

With the upcoming Memorial Day weekend serving as the unofficial start of summer, Pepsi is turning to Instagram to help sell its soft drinks to quench the thirst of beachgoers and BBQers.

Ever since the planet went crazy trying to find augmented reality creatures in Pokémon GO, we've been waiting for the next virtual object game capable of delivering a similar hit. And now, we might finally have one coming, direct from the magical world of Harry Potter.

Greetings, hackers and friends! I know it has been a while since I posted a tutorial, and hopefully I can make up for that by posting a series.

Hello, hackers and engineers! Today we are going to dive a tiny bit deeper into the secrets of psychology, and how we can use them with hacking and social engineering attacks.

Trying to get more traffic for your Wordpress blog? Looking to connect with the people who visit you online? This video will show you how to facilitate web interactions by adding social media icons to your blog's header. This video uses the 2010 theme to demonstrate. CSS may be intimidating, but this video will show you exactly what to do.

The Droid 3 smartphone from Verizon has a great camera perfect for taking beautiful photos. If you want to learn how to perfect your on-the-go photography, take a look at this tutorial from Verizon Wireless that features instructions on all the different settings in the Camera app on the Android device.

If someone violates a protective order, there are — the remedy would be the police would be involved. You'll get arrested. So, basically, a protective order is usually good for two years, and it has all the specific things you cannot do. For instance, you can't go by that person's — within 200 feet of them or their residence or their employer. So it has some very specific things. A restraining order is different. It's a standard thing that's given that's a mutual thing where it just says be n...

before I move on to more exciting areas in this series, I want to also point out some things to protect your information & how to not get DoXed.

As this generation continues to evolve, we become more involved with social media. For example, you may have a Facebook, Twitter, and a Google+ account, and be heavily involved in using all three, but the constant switching between sites, logins, and conversations can get very tedious.

This video will show you how to add Social and Custom links in YouTube Channel Banner. You can employ it yourself. Watch the video and follow the steps carefully.

Bummed about your divorce? Feeling like a failure? Oh, stop! Get off the couch and jump-start your social life because there is life after a divorce! A great life! Get back into the swing of things by taking steps towards building a better you and regaining the confidence you once had. You might just look back on this period in your life and realize it was for the best!

We are totally buggin' about Pinterest's update to their Lens. I know, I had to.

Social engineering makes headlines because human behavior is often the weakest link of even well-defended targets. Automated social engineering tools can help reclusive hackers touch these techniques, but the study of how to hack human interactions in person is often ignored. Today, we will examine how to use subtle, hard to detect persuasion techniques to compromise a human target.

Snapchat has already found a compelling way to create advertisements in augmented reality with their branded filters, but they continue to experiment with new ways to monetize the bridging of the real and digital worlds. Their latest idea, which requires users to "snap" an image to unlock content, could succeed where QR codes haven't.

If you're playing Deus Ex: Human Revolution on the Xbox 360, you can unlock the 'Ladies Man' achievement during the Corporate Warfare side quest. You will need to have the social enhancer augmentation to obtain the achievement. This guide will help you sweet talk the woman character until she provides you with the information you need.

Your mom probably told you not to play with matches, but now that you're a little older it's time to start breaking that rule. Watch this video to learn how to play a fun trick on / mind game with people at a bar or other social occasion using matches.

Light shows are one of the best parts of raves, bringing people together to participate in a whole new type of social interaction. Gloves have become the most popular tools of the lightshow trade, and this video will teach you how to make your own custom set exactly how you want them. It discusses types of lights, batteries, and everything else you need to know to make your first set of gloves.

Facebook has added (yet another) brand new feature to their ever-expanding website. This new tool is called "social plugin" and it actually works all over the web. Now, Facebook will follow you wherever you go online. If you are on a completely different site (a news site for instance or a blog) you will see a little Facebook widget in the corner. You can then "Like" what you are reading or see if your friends "liked" it before you. This will then be published to your profile on Facebook for ...

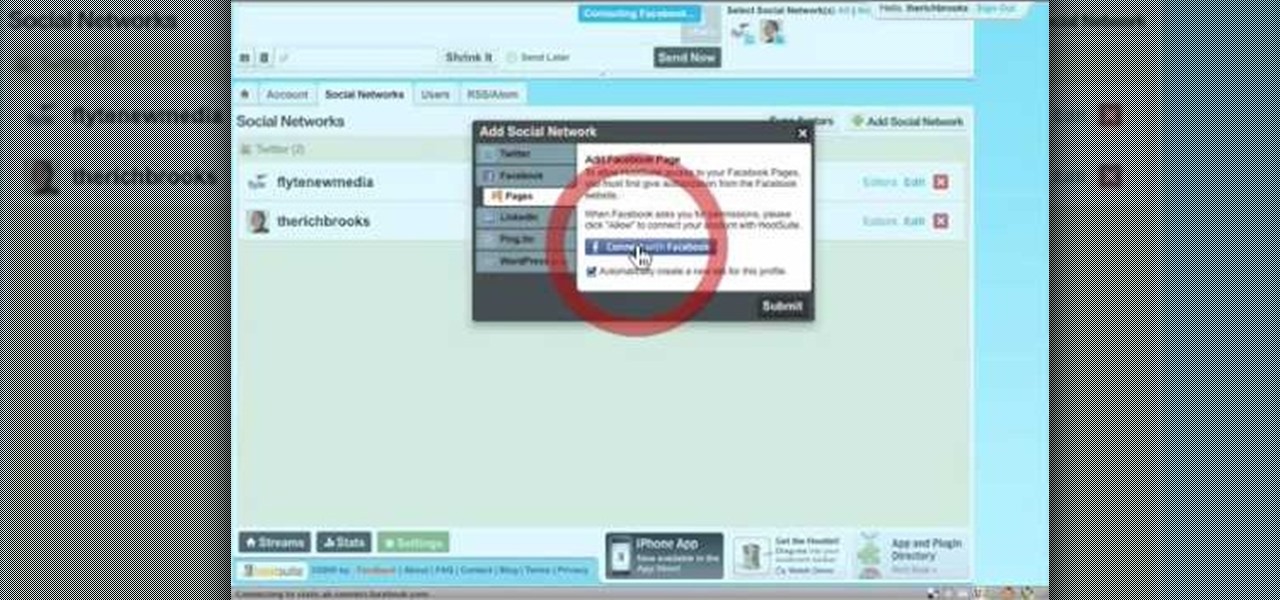
In this video tutorial, viewers learn how to sync Twitter with a Facebook fan page. Begin by going to the website: Hoot Suite and sign up for an account. Once logged into an account, click on Settings and click on the Social Networks tab. Click on Add Social Network and click on Pages under Facebook. Now click on Connect to Facebook and log into your account. Then select the page(s) that you want from your Facebook and click Add to Hoot Suite. Finish by typing in your message and select your ...

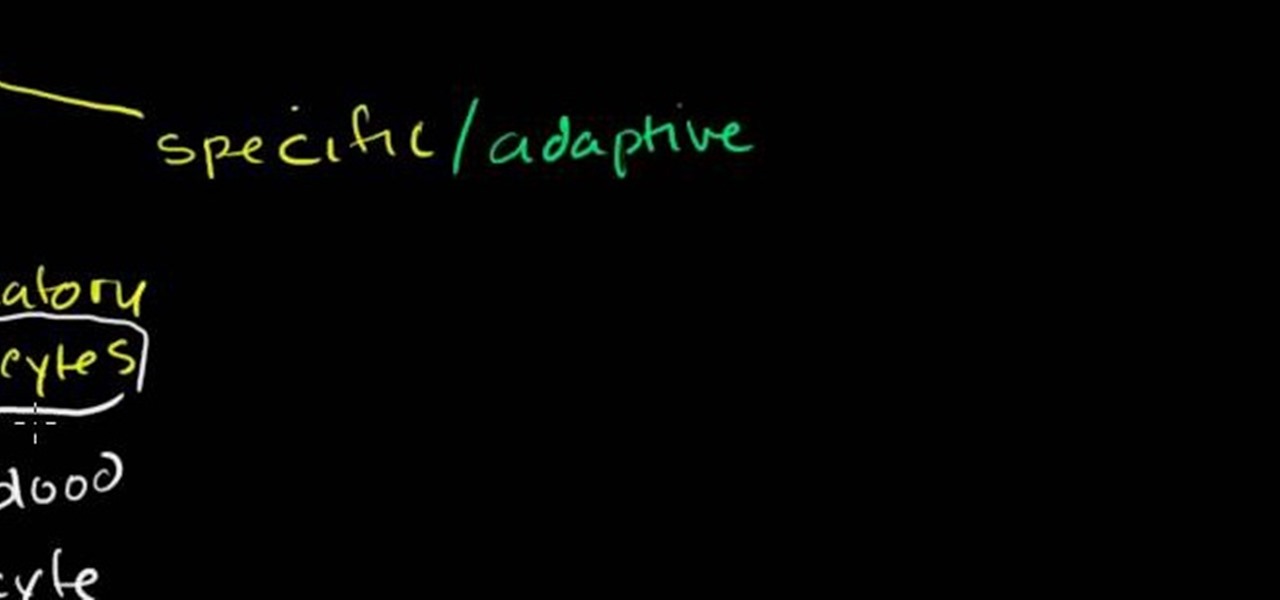
This is a presentation of different types of immune responses in human body. There are two types of immune systems i.e., non specific and specific or adaptive immune system. Again, non specific immune system is sub- divided into barriers. It is the first line of defense. The second line of defense is the inflammatory response. They are phagocytes. These are all products of white blood cells. It is also called as leukocytes. Lymphocytes are another type of white blood cells which are carriers ...

Hak5 isn't your ordinary tech show. It's hacking in the old-school sense, covering everything from network security, open source and forensics, to DIY modding and the homebrew scene. Damn the warranties, it's time to Trust your Technolust. In this episode, see how to packet sniff networks with the fundamentals.

The top five apps of the 2010s were all social media apps of some kind, and the fact that's not surprising to you says a lot. We may use them for other reasons here and there, but our phones are social media machines at their cores. The thing is, some make better machines than others.

When the Super Bowl airs, every other TV network puts on reruns because no one wants to face that juggernaut for ratings. The launch of a new iPhone is the Super Bowl of the tech world, with the launch of the iPhone X being the biggest one yet.

Social media is kind of depressing. On one hand, we love knowing what's happening in the lives of others. On the other hand, everyone seems happier, better looking, and more successful than you. We're putting on a facade by posting statuses and writing comments that present the person we want others to think we are, rather than truly expressing ourselves. Yes, social media has facilitated movements and miraculous events, but let's be real. For the most part, none of it matters.

If you're a Twitter user, it's a safe bet to assume that you've used a hashtag. On all social networking sites that have the capability, such as Instagram, Facebook, and Google+, the pound (#) symbol is used to mark and designate specific keywords or topics in order to make it effortless for users to connect with one another.

Need some help figuring out how to configure safe frames and grids in Maya 2011 when animating for specific output source? This clip will show you how it's done. Whether you're new to Autodesk's popular modeling software or a seasoned 3D artist just looking to better acquaint yourself with the Maya 2011 workflow, you're sure to be well served by this video tutorial. For specifics, watch this free video guide.

The impact of the COVID-19 pandemic caused by the novel coronavirus has practically guaranteed that the virus, along with the phrases "social distancing" and "flattening the curve," will rank among the top search terms of 2020. USA Today combined the phrases in its latest augmented reality experience, which quizzes your knowledge in the best practices of social distancing.

As long as you're on the internet, you can be hacked. With an estimated 2.65 billion social media users, these apps are prime targets for hackers.

We recently set out to find the best phones for people whose primary usage revolves around social media apps like Facebook and Instagram. Samsung, Apple, and Google were the three brands that made our top five, and while the latter only had one finalist, the two bigger OEMs had a pair of phones each. What struck us, however, was that Samsung's phones edged out Apple's not once, but twice.

An update to the iFramed social media gateway app for iOS adds an augmented reality feature called JuxImage that gives its users Snapchat-like photo and video effects.

Today I am going to teach the various ways that you can use social engineering to hack a system. For those of you that have followed my past tutorials, you know that social engineering can unlock a world of possibilities. This is because no matter how many firewalls, no matter how many patches there are on a server, the password is kept in the minds of people...and people, are not as smart as computers.

HTC's Sense UI is generally regarded as one of the best manufacturer-skinned versions of Android. This is mainly due to the subtle and classy styling of the interface, as well as some unique features that are added in here and there.

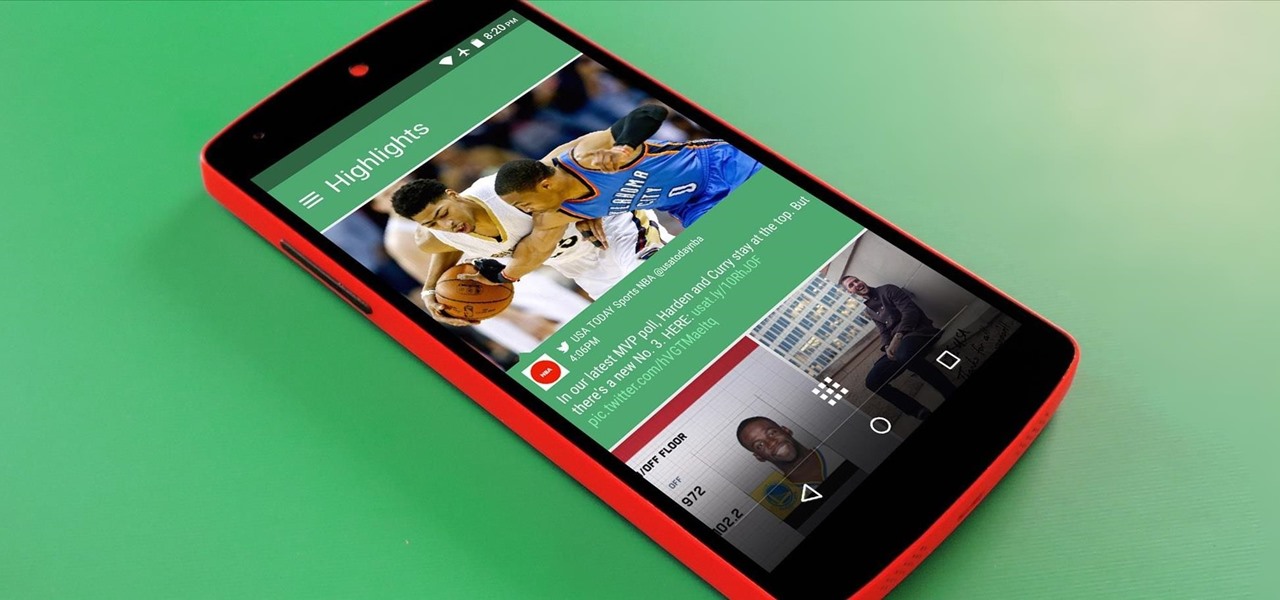
Social media is constantly evolving, and as a result, we're now capable of sharing much more than we were even just a few years ago. Television, on the other hand, continues to hold strong as one of America's favorite pastimes.

Since the days of Friendster and MySpace, social media platforms have taken leaps forward, revolutionizing how we live our lives by changing the way we communicate with others. Not only has social media become a catalyst for major uprisings around the world, but on a personal level, it connects people together in ways that were unimaginable even 10 year ago—no one was taking pictures of their brunch to share with the world in 2004.

Released last year for iOS devices, Frontback is a simple photo-taking and sharing app that not only snaps a picture of what's directly in front of the camera, but also behind it, which is to say, a selfie.

Have you been noticing a small stench trailing throughout your home? Is you teen going through "changes" and you don't know how to approach them? Follow these tips to keep your home and teen smelling like roses.

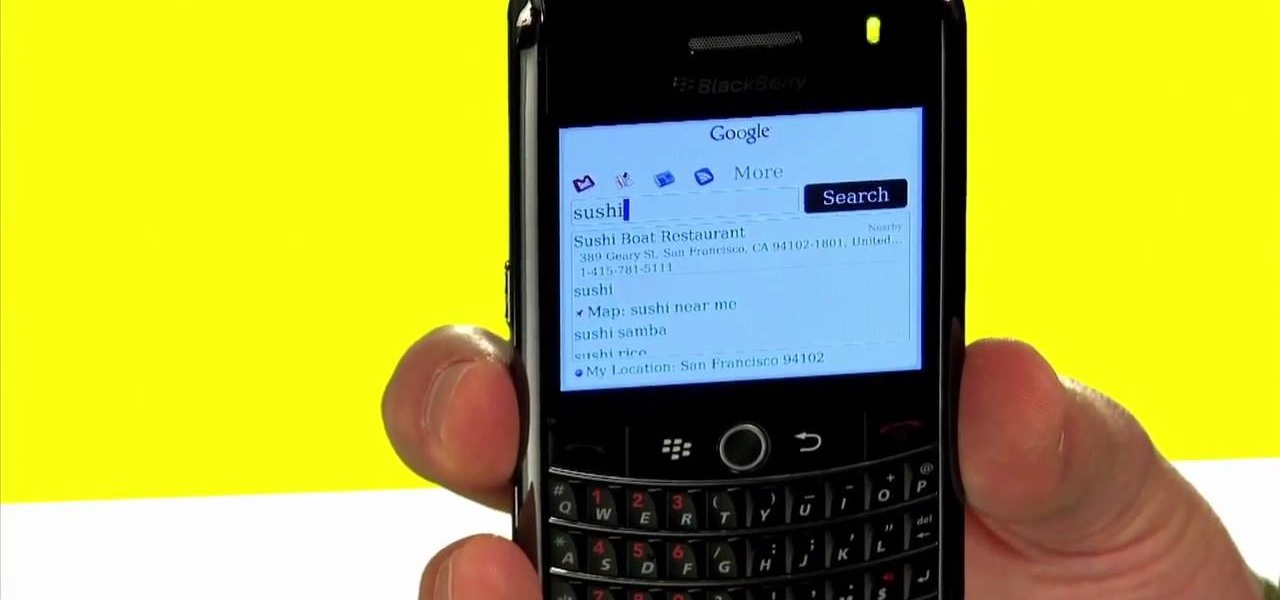
Best Buy shows us how to use the Google Mobile App for location specific searches on your mobile phone. Google Mobile can find you the nearest restaurant in your town, and provides maps and directions. It's pretty easy to use, and you can use it on many phones, including Blackberry, Windows Mobile, Droid, iPhone, and Nokia.