This is how to hack a computer for educational purposes. First you need its IP address, radmin viewer 3.3 or later, and an open port scanner. Okay so first you need the IP and scan the IP address of the computer. Now find what open port it has. Ok then open up radmin viewer and put in the IP address and open the port you found. Now right click after you enter the computer's IP address and the open port. Select full control or view only and there you go. The computer has been successfully hack...

One of the first steps in reconnaissance is determining the open ports on a system. Nmap is widely considered the undisputed king of port scanning, but certain situations call for different tools. Metasploit makes it easy to conduct port scanning from directly inside the framework, and we'll show you three types of port scans: TCP, SYN, and XMAS.

Hello, everyone. Stealth is a large part of any successful hack; if we don't get noticed, we're much less likely to be caught. In these next few articles, we'll be building a shell based on keeping us hidden from a firewall. There are many ways to stay hidden from a firewall, but we'll only be incorporating a couple into our shell. This article will outline and explain these evasion concepts and techniques.
I wrote a python script that allows you to easily ask what service runs on a specific port and vice-versa. Now, I am sure that such a program already exists on our lovely linux OS's, but... I didn't think of that before I started, and haven't found it yet. So if you haven't found it yet either, maybe you'll find this of some use. It's just called getport. If I have a port number, and want to know what services run on that port, I do:

Celebrate America's birthday the way the Founding Fathers might have, by whipping up a batch of Plantation Punch. Howcast presents this video recipe guide to mixing the alcoholic drink: The Founding Father's Plantation Punch. Perfect for the 4th of July.

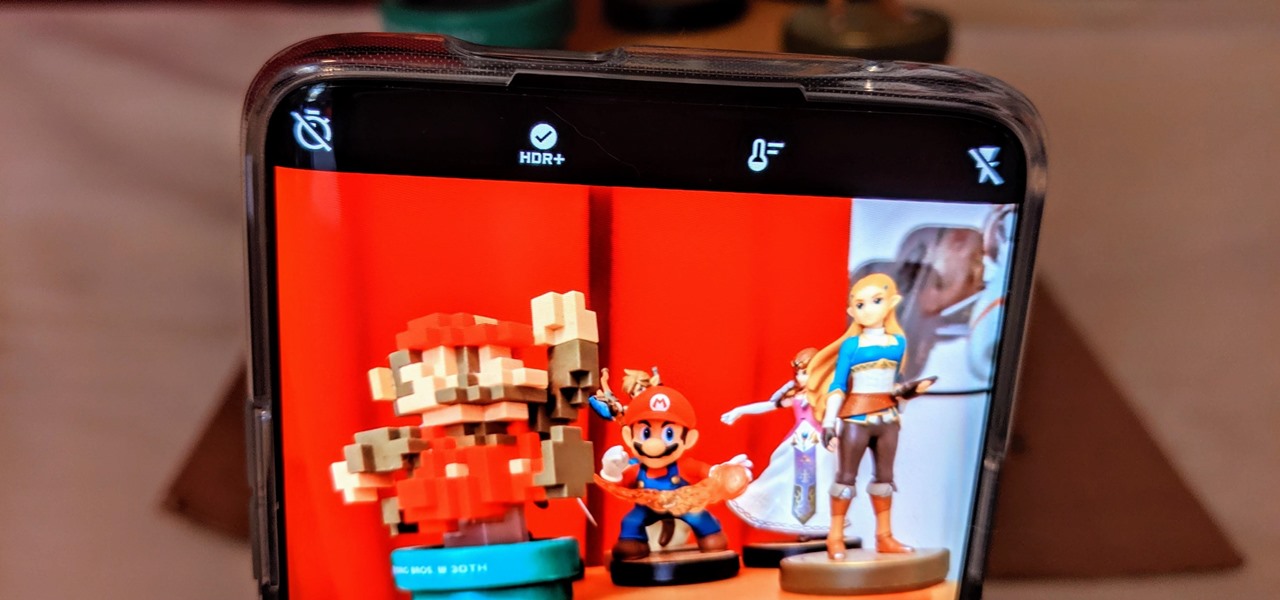
One of the coolest things about Android is the massive development community behind it. These developers keep on cooking up new things even after official support has stopped for an older device. It breathes new life into somewhat forgotten devices, which is always great news. With Android 10 out, it's time to see what phones will get the custom ROM treatment.

Local port forwarding is good when you want to use SSH to pivot into a non-routable network. But if you want to access services on a network when you can't configure port-forwarding on a router and don't have VPN access to the network, remote port forwarding is the way to go.

SSH is a powerful tool with more uses than simply logging into a server. This protocol, which stands for Secure Shell, provides X11 forwarding, port forwarding, secure file transfer, and more. Using SSH port forwarding on a compromised host with access to a restricted network can allow an attacker to access hosts within the restricted network or pivot into the network.

So, you want to perform an exploit on a victim, but you're not on the same network as their machine. In this tutorial, I'll be showing you how to set up a meterpreter reverse_tcp attack to work over the internet.

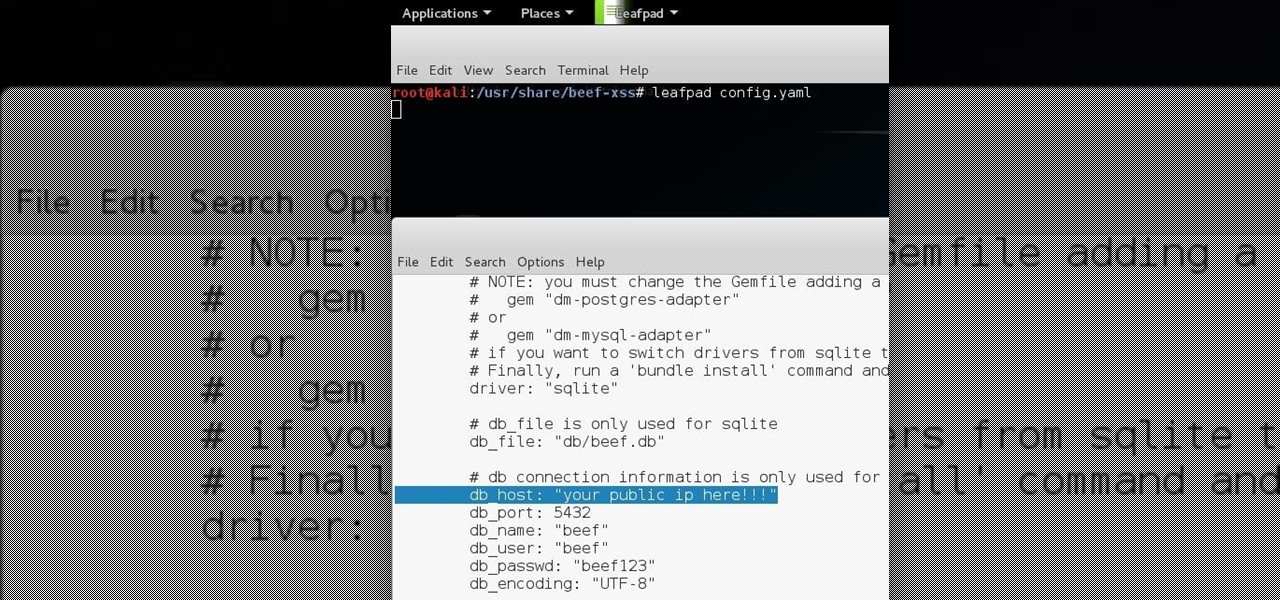
Hello all Just thought id share how ive managed to get beef working over the internet.

Macheads demonstrates how to install wine on mac. What is wine? Wine allows you to run and install windows program on Intel based machine. This program will work only on Intel and wont work on power PCs,unfortunately. First, we have to install macports which is something similar to installing unix programs on mac. The following are a bunch of requirements in order to install wine - an intel mac, admin account, X code installed, X11 (which comes mostly with intel macs). First of all we have to...

Hak5 isn't your ordinary tech show. It's hacking in the old-school sense, covering everything from network security, open source and forensics, to DIY modding and the homebrew scene. Damn the warranties, it's time to Trust your Technolust. In this episode, see how to hide secret data inside a photo.

Hook up your TiVo, Xbox and other television-based electronics to a single HDMI port. All you need is a switcher, which you can buy easily for around fourteen dollars. Then hook it up, and have multiple input devices attached to your TV!

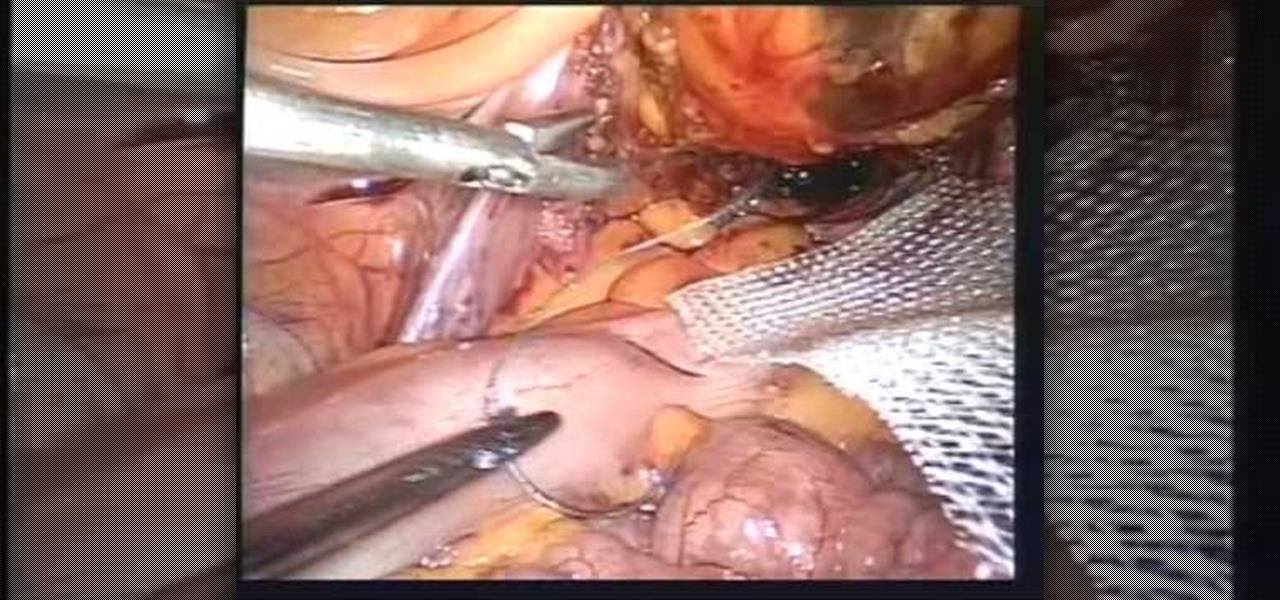
This video is about Laparoscopic Suturing Techniques.The video begins with the narrator saying that the technique is widely used in major abdominal surgeries and mastering of the techniques would give great confidence in the surgical procedures.There are various types of laproscopic needle drivers are available which can be selected according to preference.Different types of 10 millimeter laproscopic ports are available,however the valves used in the ports are important for performing extra c...

Welcome back, my fledgling hackers! Awhile back, I demonstrated one of my favorite little tools, netcat, which enables us to create a connection between any two machines and transfer files or spawn a command shell for "owning" the system. Despite the beauty and elegance of this little tool, it has one major drawback—the transfers between the computers can be detected by security devices such as firewalls and an intrusion detection system (IDS).

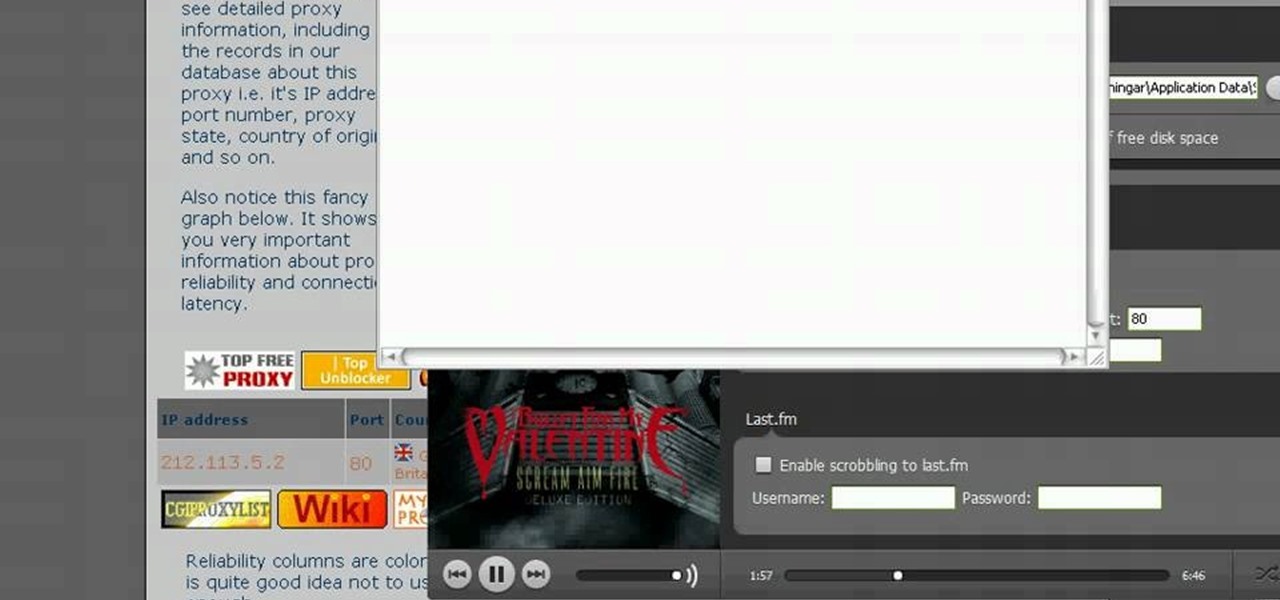
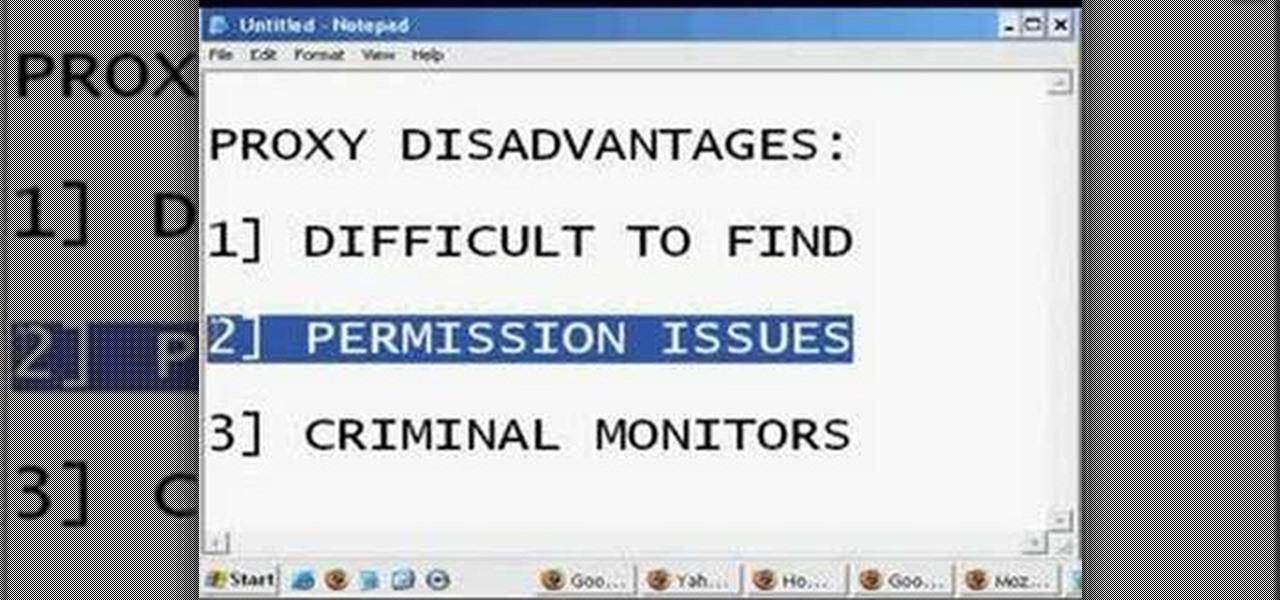
In this tutorial, we learn how to remove the ads from Spotify. First, you will need a proxy, which you can get from the website: Proxylist. Just simply click on a free proxy once you get to the site, then write down the proxy and port. Next, go to edit, then preferences. After this, change the auto-detect to https, then put the proxy next to the box that says "host". Next, type in the port next to where it says "port", then click on the "apply" button listed at the bottom of this window. Now ...

Cranberry sauce is one of the most important side dishes to any Thanksgiving dinner—even Christmas dinner! And if you're like me, you usually buy a can of cranberry sauce for the holidays because you don't have the extra time to go homemade with the turkey stealing the show.

2019 has been a great year for smartphone batteries. Several phones have topped the 5,000 mAh threshold, and Apple finally went all in on 18 W USB PD charging, which means millions of new users are finally taking advantage of fast charging. All of this gets even better when you have the right charger.

After learning that you'll need to spend at least $74 on a special charger and a USB Type-C Lightning cable to enable fast charging on the new iPhone X and iPhone 8 models, you may be wondering why you can't just use the standard Lightning cable. While we can't answer why Apple didn't include the USB-C cable in the box with their new phones, we can explain why you need USB-C to enable fast charging.

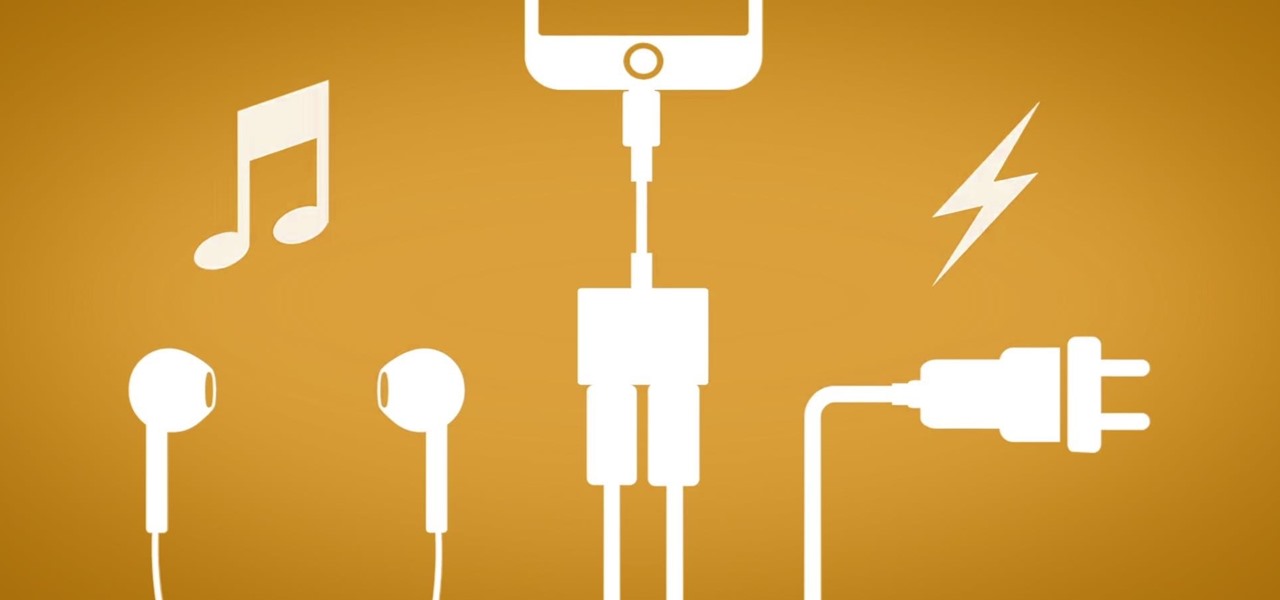
The fact that this guide even exists is a downright shame, but that's neither here nor there. The truth of the matter is the iPhone 7 and 7 Plus don't have 3.5 mm headphone jacks, and since they use the Lightning connector to output audio, it's hard to charge your phone while your headphones are plugged in.

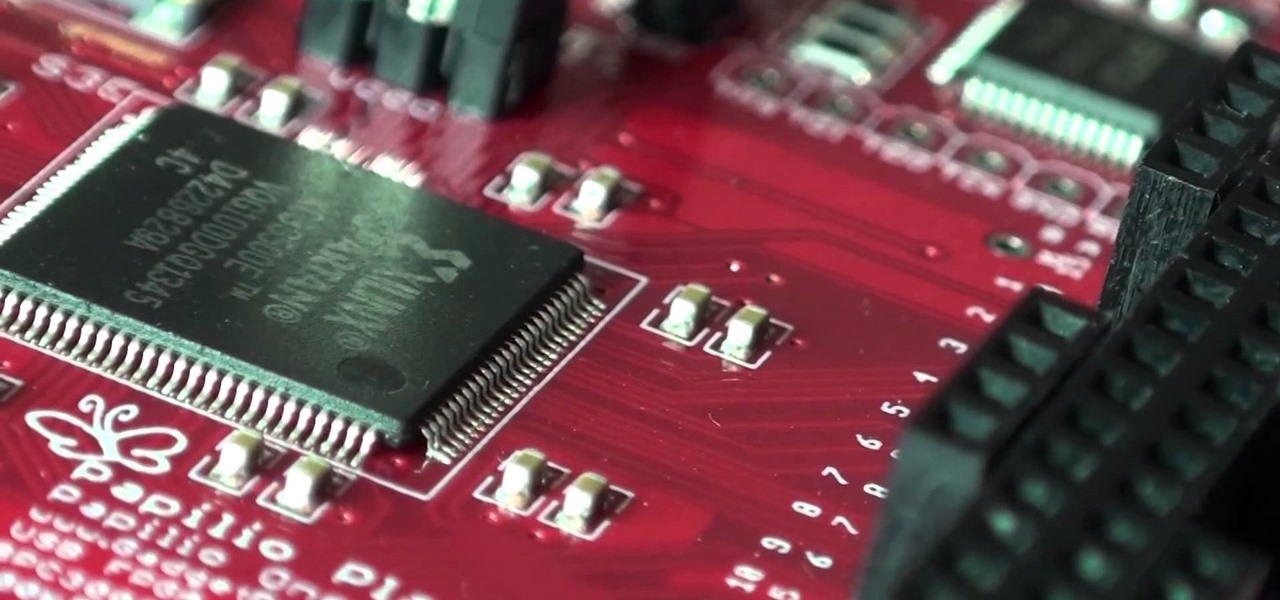
A FGPA is chip that is programmable with the computer to create circuit. It is a totally different type of programmable board compared to an Arduino for example. The Arduino will follow lines of codes to generate the necessary outputs. A FPGA won't however read lines of code, but it is a circuit itself. When the chip is programmed, a series of AND-ports, OR-ports and many others ports are linked together. The FGPA will increase the speed and the possibilities of your designs! I assume that by...

If you've ever had issues charging your iPad, iPhone, or iPod touch, like most other Apple products, the culprit to blame is usually a frayed or damaged cable. It's a common design flaw due to the thinness of the cords and the weak sheath surrounding them — but that's not always the problem.

Welcome back, my budding hackers! We've spent a lot of time learning to compromise Windows systems, and we've successfully compromised them with Metasploit, cracked their passwords, and hacked their Wi-Fi. However, very little time was spent developing ways to extract the information from the system once inside.

As if there weren't already enough problems with the iPhone 5, now the new Lightning USB cable is reportedly getting stuck in USB power adapters and computer ports. The newer Lightning cables have deeper divots and a slightly thinner mouth on the USB plug than the old 30-pin cables did, so the cable can get stuck inside your USB port.

In this tutorial, we learn how to change your IP address in five different ways. First, go to your security settings and clear all cookies, then start to browse the internet with private browsing from your internet browser. You can change your IP address by going onto your internet browser and changing the LAN settings. Type in your address and port, then bypass the proxy server. Next, go to options and then advanced on your browser. Type in the proxy and port, then click where it says no pro...

This video tutorial is in the Computers & Programming category where you will learn how to set up an FTP connection using Firezilla. Open up your filezilla program. On the top left, click on the file menu button, and select 'site manager'. In the window that opens up, select 'new folder' and give it a name. Now create a site to store in this new folder. Click on 'new site' and name it. Now on the right hand side, enter the host and the port. The default port is 21. Under server type, select F...

In this video, Sierra Snowboard gives us some tips on how to select the snowboard that's right for you. Each board comes in a number of different sizes, and most boards come with a size chart specific for that board. These charts can be vague, but are good starting points for selecting your size. One thing to consider is your bossy type. The weight of the rider is the primary factor in selecting the size of a snowboard. You'll notice that the height of a rider is not listed on a size chart. I...

1.First take 1 cup of All purpose flour in a plate and 2 cups of same flour in another plate. And then take a stuffer can be anything like sweet coconut, chocolate flavor to put inside the puff.2.First add one tablespoon of vegetable oil to each plate and slowly make it out by hand and add some water and make flour mix. Now separate the 2 cups flour mix into 4 to 5 big pieces and separate the 1 cup flour mix into 4 to 5 small pieces.3.cover the small pieces with big pieces of each. Now just r...

In this video from lunawebs we learn how to use an external monitor with a camcorder. The best way is to use an HDTV and use your HDMI output on the TV. The sound can also come through the monitor if you have a headphone port on the monitor. If you want to go outdoors, it will be more of a challenge. If you do not have an HDMI out on your camera, there is a component you can use. Composite AV outs are cheaper when it comes to monitors and camcorders. If you have a composite monitor, assign th...

In this video, Caroline, host of 10MinuteCook, demonstrates how to create a traditional chestnut stuffing. The ingredients used in this recipe are: 500g ground sausage, 1 onion and 1 garlic clove - finely chopped, 75g dried cranberries - soaked in 50mL of port wine for an hour, 3 slices of bacon - chopped, 2 1/2 cups of bread crumbs, 1 can of chestnuts - finely chopped or pureed, 1 tsp thyme, 1 large egg. She begins by frying the bacon and onion and garlic mixture together, first. Once the on...

Ports allow network and internet-connected devices to interact using specified channels. While servers with dedicated IP addresses can connect directly to the internet and make ports publicly available, a system behind a router on a local network may not be open to the rest of the web. To overcome the issue, port forwarding can be used to make these devices publicly accessible.

The internet is constantly under siege by bots searching for vulnerabilities to attack and exploit. While conventional wisdom is to prevent these attacks, there are ways to deliberately lure hackers into a trap in order to spy on them, study their behavior, and capture samples of malware. In this tutorial, we'll be creating a Cowrie honeypot, an alluring target to attract and trap hackers.

Until Star Wars Jedi Challenges arrives in November, a forthcoming ARKit revision of HoloGrid: Monster Battle from Tippett Studios and Happy Giant, might be the closest most Star Wars fans can get to playing the HoloChess game from the movie.

If history holds true, we'll see the iPhone 7 arrive this September, and just like many times before, there are already a ton of rumors about its features. As usual, many claims are pure speculation, but there are some trustworthy reports and lots of good information we can use to make some educated guesses regarding Apple's upcoming flagship.

As we're all aware, recon is vital to a successful hack. We need to know everything we can about the target in order to perform the best possible attack. Port scanning is a basic recon concept that is introduced very early in learning proper reconnoissance. The issue with port scanning is that is makes a lot of noise. Every connection to every port will be logged. This is where stealth scanning comes in. Also known as SYN or half-open scanning, stealth port scanning is a bit quieter, and is l...

Imagine this scenario: You exploited a system using metasploit and you want to install a backdoor. You have a few options;

OTW's great Tutorial Hack Like a Pro: How to Save the World from Nuclear Annihilation gives me the inspiration to try this on Win7 sp1.

After many years of rumors, the second-generation iPhone SE is here. At $399, it is the most inexpensive iPhone Apple has sold since the original iPhone SE came out. And while the new SE comes with Apple's typical five-watt power adapter, the smartphone supports fast charging — you just need to get a fast charger separately.

The triple camera system on the OnePlus 7 Pro is the best setup they've ever done so far, but it could always be better. The primary sensor packs a whopping 48 megapixels, but as history has taught us, megapixels don't equal better photos by default. In fact, with where we are in terms of hardware right now, it's the software that determines a phone's camera performance.

Sharing your Wi-Fi password is like giving an unlimited pass to snoop around your network, allowing direct access even to LAN-connected devices like printers, routers, and security cameras. Most networks allow users to scan and attempt to log in to these connected devices. And if you haven't changed the default password on these devices, an attacker can simply try plugging them in.