
How To: Make a skirt out of shorts
Clothing alterations, patches, inserts, and skirts! Learn how to turn shorts into a skirt in this free sewing video.


Clothing alterations, patches, inserts, and skirts! Learn how to turn shorts into a skirt in this free sewing video.

Learn how to enter code breaker codes on the PCSX2 Playstation 2 emulator for the PC. Entering these codes will allow you to cheat on emulated PS2 games. YOu will need to use a variety of other programs like Daemon tools to do this.

In this video, the author shows how one can make one's own playlists on YouTube, and also get the code which can be embedded on one's website or blog. All one has to do' according to the author, is to first load all the videos which one wants in a playlist and pause them. Then one has to click the 'Playlists' option under the video pane. In the drop-down list which opens, one can choose one of the existing playlists or create a new one, and then, simply click the 'add' button. This action has...

Want all of the GTAIV cheats? This is a Grand Theft Auto hack like you'd never believe. Get the cheat codes for every glitch and cheat in the game.

Mike Lively of Northern Kentucky University shows you how to create a light switch in Second Life with scripting. Part 1 demonstrates how to create a prim switch which turns on (brightens) a prim in Second Life. Part 2 goes through the Light Switch code line-by-line and adds a rotor to the light switch. The code is provided for free distribution on Google Code at

A QR code is a fun and convenient way to link people to a website or app. On iOS, you have a few ways to scan these codes. You can download a QR scanner to get the job done, but Apple has one built into iOS. Or you can add the QR Code Reader tile in Control Center, but that's not even necessary. There's a better way, one that requires basically no effort to pull off.

Attacks against databases have become one of the most popular and lucrative activities for hackers recently. New data breaches seem to be popping up every week, but even with all of that attention, databases continue to be a prime target. All of these attacks have to start somewhere, and we'll be exploring a variety of methods to gather information on PostgreSQL databases with Metasploit.

A stager is a small piece of software that's typically used by malware to hide what's happening in the early stages of infection and to download a larger payload later.

It's exciting to get that reverse shell or execute a payload, but sometimes these things don't work as expected when there are certain defenses in play. One way to get around that issue is by obfuscating the payload, and encoding it using different techniques will usually bring varying degrees of success. Graffiti can make that happen.

UnrealIRCd is an open-source IRC server that has been around since 1999 and is perhaps the most widely used one today. Version 3.2.8.1 was vulnerable to remote code execution due to a backdoor in the software. Today, we will be exploiting the vulnerability with Metasploit, examining the underlying code to understand it, and creating our own version of the exploit in Python.
QR codes are supposed to make life easier, but having to install potentially shady third-party apps just to scan one is more trouble than it's worth. Thankfully, there's a QR code reader built into all Google Pixels, but you wouldn't know it unless you stumbled across the feature.

QR codes are everywhere, from product packaging to airline boarding passes, making the scanners that read them a juicy target for hackers. Thanks to flaws in many of these proprietary scanning devices, it's possible to exploit common vulnerabilities using exploits packed into custom QR codes.

EternalBlue was a devastating exploit that targeted Microsoft's implementation of the SMB protocol. Metasploit contains a useful module that will automatically exploit a target, as long as it's vulnerable. But what if we wanted to exploit this vulnerability without Metasploit holding our hand? It can be done using a Python file to exploit EternalBlue manually.

Particular vulnerabilities and exploits come along and make headlines with their catchy names and impressive potential for damage. EternalBlue is one of those exploits. Originally tied to the NSA, this zero-day exploited a flaw in the SMB protocol, affecting many Windows machines and wreaking havoc everywhere. Here, we will use EternalBlue to exploit SMB via Metasploit.

The road to becoming a skilled white hat is paved with many milestones, one of those being learning how to perform a simple Nmap scan. A little further down that road lies more advanced scanning, along with utilizing a powerful feature of Nmap called the Nmap Scripting Engine. Even further down the road is learning how to modify and write scripts for NSE, which is what we'll be doing today.

The misconception that macOS is more secure than the Windows operating system is far from the truth. With just one small command, a hacker can completely take over a MacBook and control it remotely.

The default Camera app got a few more tricks up its sleeves when iOS 11 was released, and the best addition by far was the inclusion of a built-in QR code reader since that meant no more third-party apps just for QR code scanning. However, Apple's built-in QR code scanner did have a vulnerability at one point that would let hackers direct you to a compromised website without you even noticing it.

Cross-compilation allows you to develop for one platform (like Kali) and compile to run on a different platform (such as Windows). For developers, it means that they can work on their platform of choice and compile their code for their target platform. For hackers, it means we can compile exploit code for Windows from Kali.
Right, So i've been asking alot of questions here on Null-Byte and everyone has been really helpful to me.

Welcome back to another episode of Java Tutorials, In today's tutorial, we'll be learning about what methods are, proper syntax when writing Methods, and why they are beneficial in a program's code.
Hi guys, I'm gonna keep this short because I got assignments and a lot of notes to study and also other how-tos and forums to reads. lol...Since I'm keeping this short...no story time just scenario. And I want to thank n3stor for giving me the idea to post this.

Welcome back, my amateur hackers! Over the course of the next year, we will be developing our own zero-day exploits. In my first article in this series, I introduced you to buffer overflows, which are the source of some of the most lethal exploits, particularly the "remote code execution," so we are focusing our exploit development here on a buffer overflow.

Having short hair is both a blessing and a curse. Short hair is a LOT easier to maintain than long hair, but at the same time there are fewer options for styling.

If you are looking for a UAV code for homebrew then this is the video for you. Check out this site for codes and follow the video to learn how to hack COD: Black Ops with a UAV code.

If you have friends or relatives living or traveling in another country, you may need to call them internationally. Check out this tutorial and learn how to dial a far away land just as easily as you would dial one close to home.
You can change thesis theme background color and size in Wordpress blog to do this first you need to go to your word press admin. And then you have to click custom file editor. There you will see the "Thesis custom file editor". Now you have to select custom.css in edit selected file menu. Now you will see there a code box. Here you will have to past the background changing code. The code is showing in the video you can type it and then copy and paste it in the place of the code box which is ...

Short hair is so appropriate for summer, since it's both easy to style and tomboyishly chic. Plus, it's extremely lightweight, so you won't be sweating up a storm like you would with longer locks.

MySpace gives users the ability to hide their friends list. This video walks you step by step through being able to view this list. First, go to the desired profile. You'll see the hidden friends list. Now, click on "Edit with notepad" and code will pop up on your notepad. Because the list is on the page, editing the source code will make the list appear on the page. Next, type the command >table border=0 cellspacing=0 align="center">. Now you'll be instructed on how to delete the source code...

In this video tutorial, viewers learn how to automatically play You Tube videos on My Space. Begin by going on the You Tube website and search for a video that you want. Then copy the embed code and paste it in a notepad document. There will be two URLs in the embed code in quotations. Type in "&autoplay=1" at the end of both URLs inside the quotations and then copy the embed code. Log into your My Space account and click on Edit Profile. Paste the embed code into the About Me section and cli...

This video shows you how to bypass expensive texting charges and use this free and easy way to text people without the need to download apps, go to websites, or jailbreak your device. Works on basically any cell phone. No need to ever pay $20.00 for unlimited texting with AT&T, watching this you'll be able to text for free whenever, and whoever.

To recycle an old towel into shorts, fold the towel and cut it into a short leg's length worth of fabric. Cut another piece into a short leg's length worth of fabric. Draw a curved seam on one edge. Stack the towels and pin them to hold the fabric in place. Cut out the seam on both of the towels. Separate the towels and sew up the seams on both of the fabric pieces. Do not sew the top seam and front side seam of the shorts. Instead, sew the front and back side seams together. Thread and sew a...

Editing the sites with JavaScript code is one of the easiest method in the internet. First go to any web page, clear the address bar and the paste the code below, "javascript:document.body.contentEditable='true'; document.designMode='on'; void 0"(Without the quotes) and hit enter. Yep that's it, now you can select or click any part of the web page and edit what ever you need. If you follow the steps in this video you would be able to edit sites with JavaScript code easily.

In this software tutorial you will learn how to make a simple website using Photoshop. You may think it's too difficult to create your own site and that you need to use a template, but this tutorial will change all that! See how easy it is to design your own web page without a template right in Photoshop.

Check out this instructional cello playing video to learn how to create short cello notes. When creating a short note on the cello, divide the note into two sections. This tutorial recommends practicing with a few martele exercises until you're comfortable making short notes on the cello.

In this video tutorial, Chris Pels will show how to share data in between JavaScript and server-side code by using a hidden field in an ASP.NET page. Next, learn how to use the RegisterHiddenField method in server-side code to programmatically create a hidden field on the client. In addition, see how to programmatically create a HiddenField server control for sharing data on an ASP.NET page. Finally, use the RegisterArrayDeclaration method to create a container in server code for storing mult...

Web applications are a prime target for hackers, but sometimes it's not just the web apps themselves that are vulnerable. Web management interfaces should be scrutinized just as hard as the apps they manage, especially when they contain some sort of upload functionality. By exploiting a vulnerability in Apache Tomcat, a hacker can upload a backdoor and get a shell.
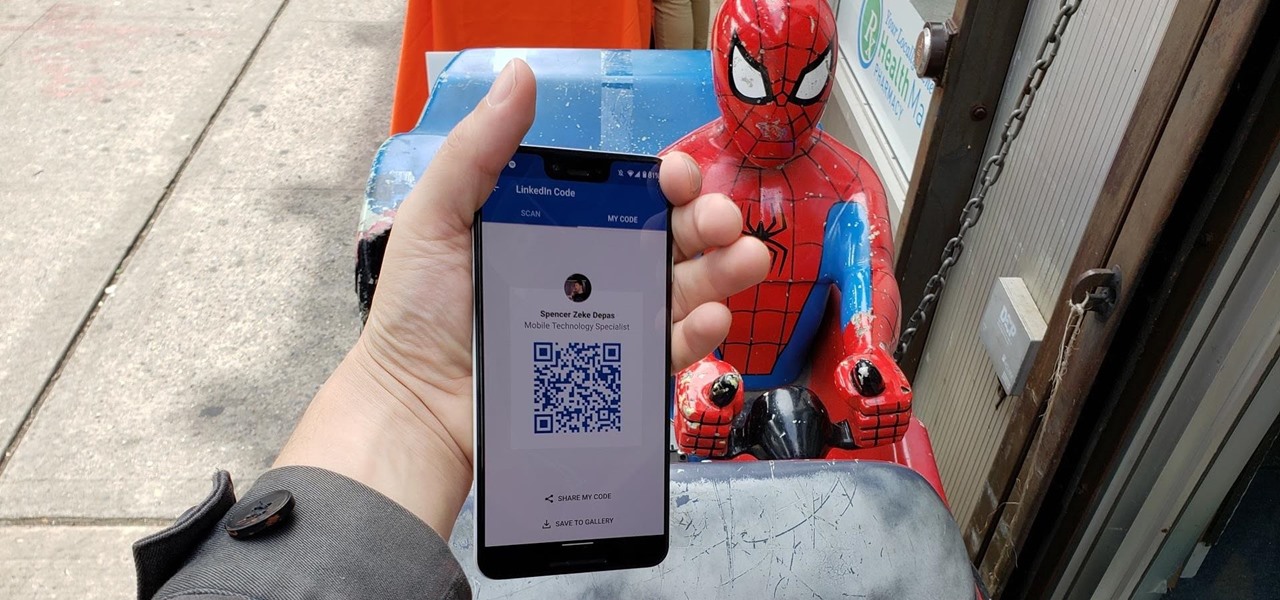
When attending networking events, a LinkedIn exchange is a common occurrence. Equally common is the awkward fumbling dance with how to add each other. Fortunately, we have the solution: the ultimate way to add LinkedIn contacts.

KeePassX, 1Password, and LastPass are effective against keyloggers, phishing, and database breaches, but passwords managers rely on the operating system's clipboard to securely move credentials from the password vault to the web browser. It's within these few seconds that an attacker can dump the clipboard contents and exfiltrate passwords.
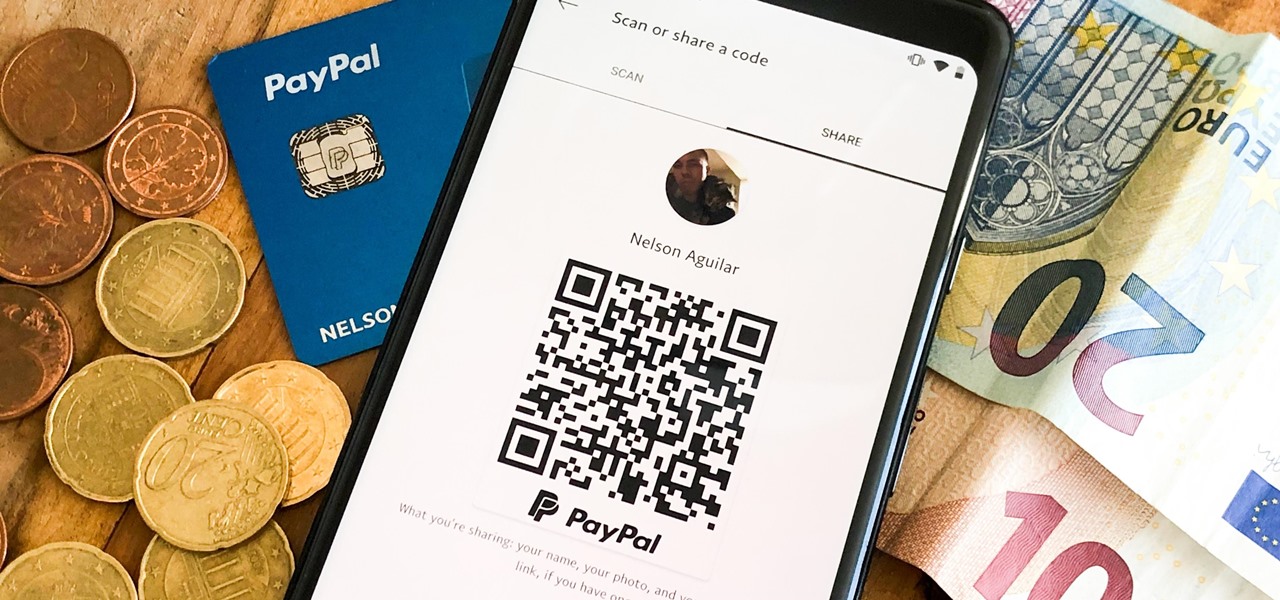
There are many ways to send and receive money on PayPal. You can use an email address, a phone number, or a PayPal.Me link, but if you're standing right next to the person you're trying to pay or get digital cash from, the easiest way, by far, is to use QR codes.

Websites are often misconfigured in ways that allow an attacker to view directories that are not ordinarily meant to be seen. These directories can contain sensitive information such as private credentials or configuration files that can be used to devise an attack against the server. With a tool called Websploit, hackers can scan targets for these hidden directories without difficulty.