In today's world of ordering food from your PC or hailing a cab with an app, it almost seems archaic when we have to actually use our vocal cords to contact a local business. It sure would be nice if we didn't have to use our smartphones as, well, you know...phones.

Welcome back, my fledgling hackers! The database is the hacker's "pot-of-gold," as it contains information that is very valuable to both the business and the hacker. In this, the second of my series on hacking databases, we're on the "hunt" for Microsoft's SQL Server. Although far from the most commonly used database (Oracle hold's that title), Microsoft's SQL Server is very often found in small-to-medium sized businesses. Even a few big businesses use it.

Business casual is a popular style for men in modern business environments, but it's very difficult to pin down. How casual can I go? How businessy is too businessy? Watch this video to learn how business casual works and how you can rock it yourself.

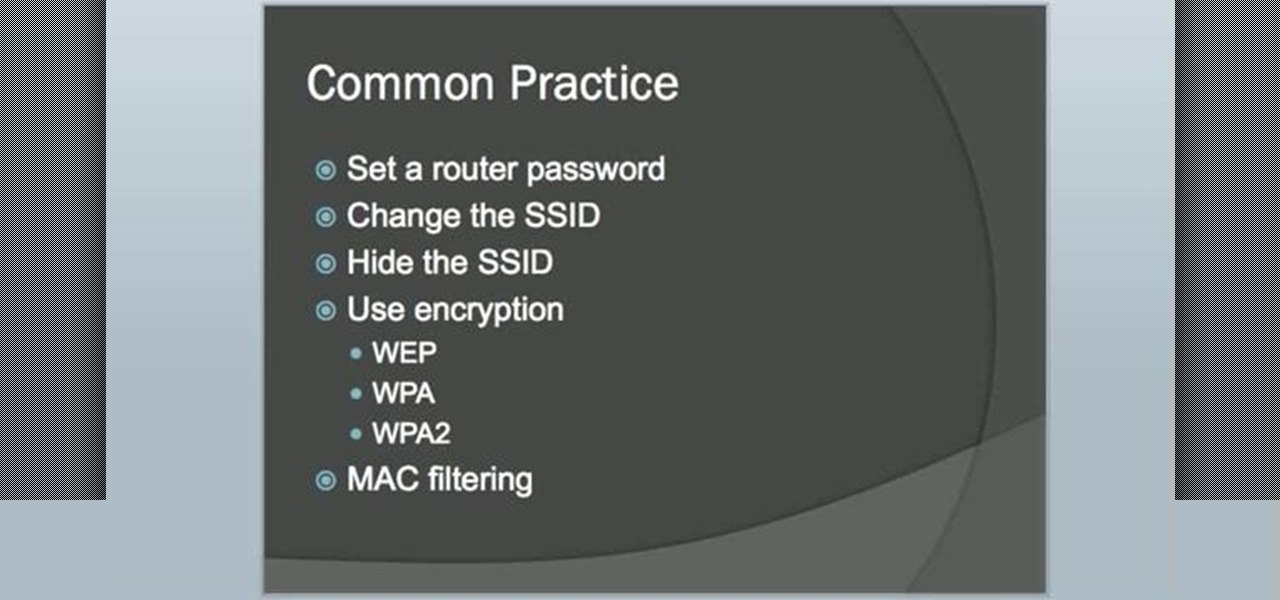
VPN's are an invaluable set up for small business', and larger business', when it comes to keeping your information secure with remote employee's. This video details all of the info that you need to know about setting up and maintaining a great VPN!
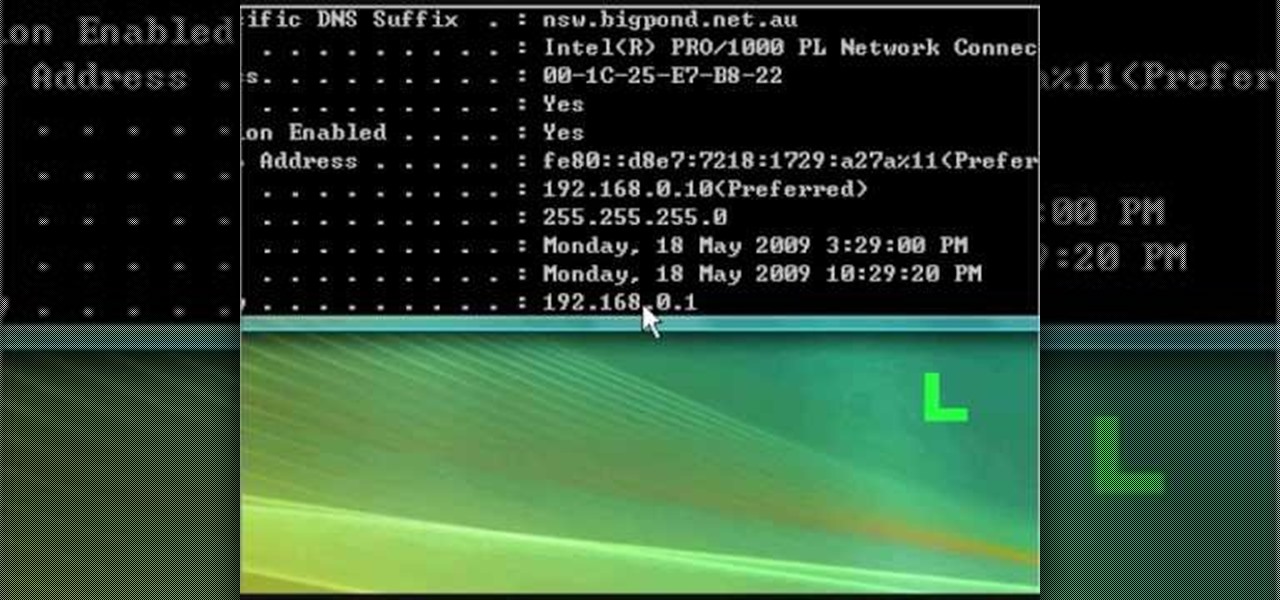
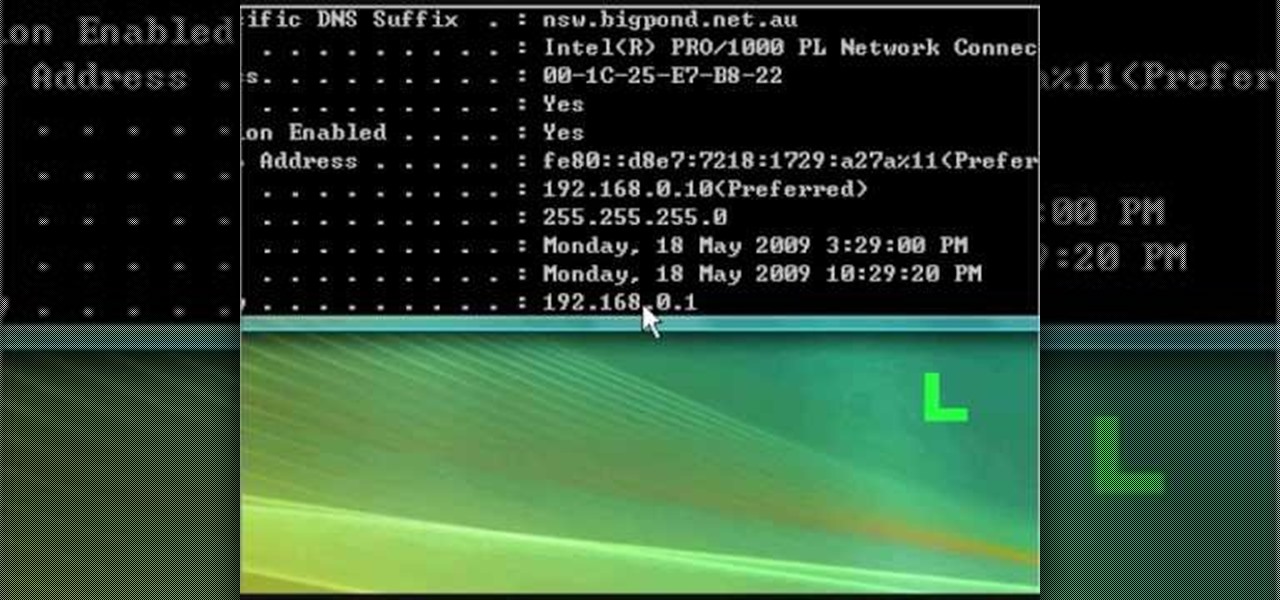
In this tutorial, we learn how to fix security mode for nds Wi-Fi. First, open the command prompt in Windows. Next, type in "ipconfig/all" in the black window that appears. After this, copy your default IP the screen just gave you, then type it into your address bar online. After this, you will be able to log into your security account and make default changes you prefer. Change different station accesses and any other security preferences you want to change. After this, you can change your p...

Having security setting on your web browser is a pretty important tool. It keeps you safe from potential hackers and makes sure you don't visit unsafe sites that could lead to a virus. But sometimes the security settings on a web browser can be a pain and the best choice would be to turn it off. So in this tutorial, you will learn how to easily change the security settings to INternet Explorer 8. So sit back and enjoy!

Job seekers and business professionals everywhere always think they have it made when their shiny new business cards ship in, but then they realize they have absolutely nowhere to put them.

Bar tricks, gotta love em. This is an easy trick that's hard for someone to win unless they know the secret. Place a small coin on a business card and the business card on a bottle. Now remove the business so that the coin falls into the bottle. business card trick. Unless you know this business card trick it is very hard to figure out. Make a bet and you can win with this business card trick.

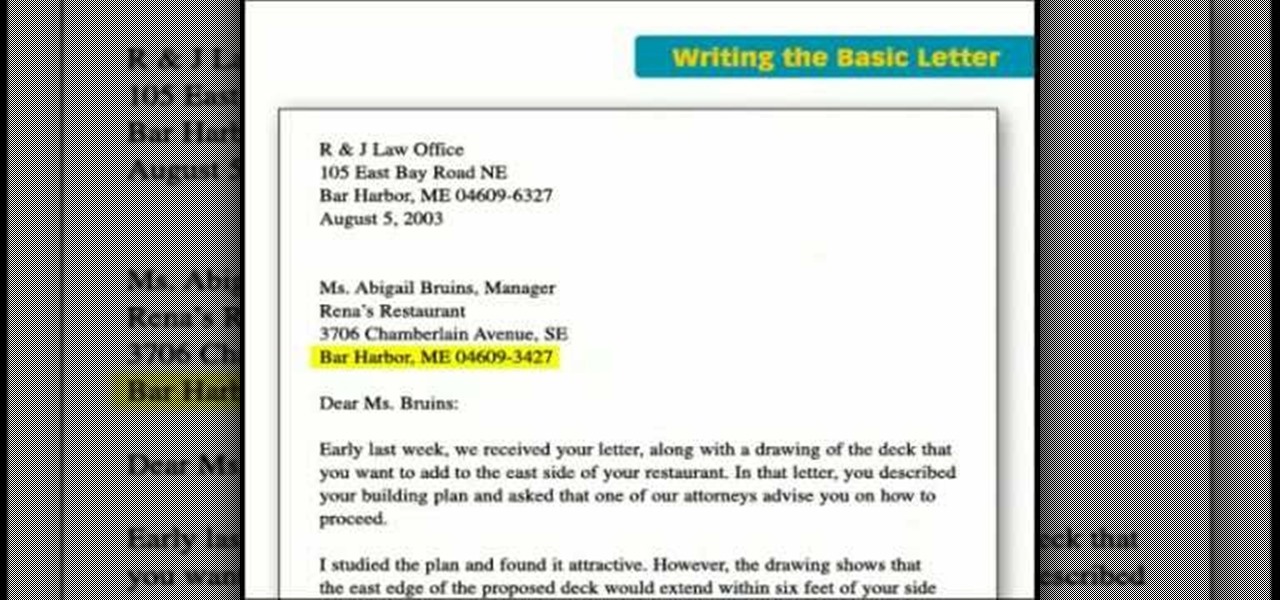
This incredible video breaks down the basic business letter into easy steps, going over some of the most key points in creating an effective business letter: make it straight, and too the point, non-confusing, and easy to read.

Cyber Security is a horrible computer virus. It mimics a virus protection program and invades your system, making it nearly impossible to remove. In this tutorial, learn how to remove this annoying trojan horse from your PC and save your computer.

This is a cool optical illusion that makes your business card appear to be blank on both sides but then you print color onto it with your hand. A magical way to hand out your business card.

Video tutorial showing how to make your own solar-powered wireless security camera using an off-the-shelf solar panel and any wireless webcam. See creator site for more detailed graphics.

Great ideas often strike at random times, but messaging friends and loved ones at an inopportune hour not only risks their wrath, but also increases the chances of your message not being paid proper attention to. Thankfully, there's an app that lets you create and post WhatsApp messages at the time you wish for maximum effect.

BlackBerry has formally announced the arrival of its flagship, the KeyOne, during Mobile World Congress 2017 in Barcelona. The all-Android KeyOne looks distinctly BlackBerry, with its 4.5" screen and physical QWERTY keyboard. Here's the lowdown on this elegant handset that hearkens back to BlackBerry's heyday, which had previously been known by its code name, the BlackBerry Mercury. Aluminum Unibody with Physical Keyboard

Security researcher Samy Kamkar, best known for his MySpace Worm, and most recently for his online calculator that can help you crack any Master Lock combination, is at it again. This time he's figured out how to break into security doors that have a motion-sensing egress system.

When it comes to antivirus software, you don't want some fly-by-night developer having access to the sensitive data that these apps can scan. Luckily, most of the longest-tenured antivirus companies from the realm of desktop computers offer complete security suites for Android these days.

If you're looking to start a retirement plan for your employees, this how to from the IRS is a great, informative video. Everyone knows that keeping great employees is essential to staying competitive and growing in today's business world. Find out how to start a retirement plan to keep those great workers right there where they are.

In this tutorial, we learn how to remove security tool in less than one minute. First, restart your computer, then press "ctrl+alt+del" when your new window starts up. After this, wait for a few seconds, then if you see the security tools pop up, end the task for it. Then, go to the start menu, then all programs, then look for any security tools. Right click, on "find target" then delete it! After this, your security tools will be deleted and will stop annoying you. You will be able to delete...

Do you own a small business, but find yourself unable to understand the intricacies of your financial statements? You are not alone. This video features a small business coach explaining some of the intricacies of financial statements. The tips provided here should help you better understand your financial statements and use the information gleaned therein to improve the profitability of your business.

If you've changed jobs or transferred your old Rolodex onto the computer, you will have a ton of left over business cards. Why not go green and reuse the cards as something unique? Check out this video for tips on what to do with all those tiny squares of paper.

If you're a small business operator and AT&T is your carrier, you'll want to take advantage of the AT&T Online Account Management portal for small business customers. This video shows how to request an online registration code (required to register your account), how to use it to register your account, and how to set up your username and password.

In a bad economic environment, providing a great customer service experience is even more important than normal. Word of that great experience will spread via Twitter and Youtube, helping your business attract buzz without requiring it to spend cash on marketing. This video features a business technology expert explaining how to create a "wow" experience for your customers and use the ability to do so to improve your business.

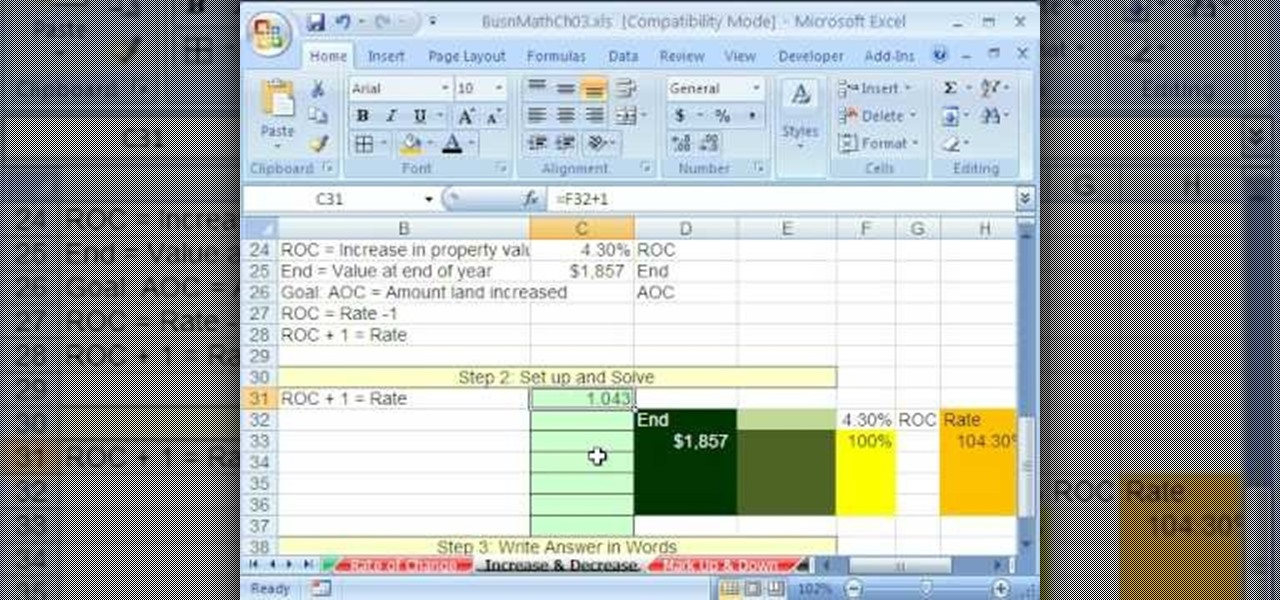
As you might guess, one of the domains in which Microsoft Excel really excels is business math. Brush up on the stuff for your next or current job with this how-to. In this tutorial from everyone's favorite digital spreadsheet guru, YouTube's ExcelIsFun, the 32nd installment in his "Excel Business Math" series of free video lessons, you'll learn how to solve increase and decrease (Rate and Percentage) applied business math word problems.

Sometimes you find ideas from the most unlikely objects. This video gives proof. Here are easy instructions for making a small box to hold business cards, ATC's (artist trading cards), gift cards, etc. Watch this video tutorial to learn how to make a small business card-sized box out of an old Orbit gum package.

The Nessus vulnerability scanner, is the world-leader in active scanners, featuring high speed discovery, configuration auditing, asset profiling, sensitive data discovery and vulnerability analysis of your security posture. Nessus scanners can be distributed throughout an entire enterprise, inside DMZs, and across physically separate networks. In this network security video tutorial, you'll learn how to hack a network using Nessus 3.

By DevonLocks.Com - Security pins can be a pain. This video shows you how to bypass them. See our other video on how to spot them.

Ever wanted to learn how to pick a lock? Well, there's no better time than now to start learning the craft of so many locksmiths out there... lock picking. Just watch this video tutorial to see how to pick a Brink's high security lock.

Have you ever been the victim of theft? It sucks. Why would these lazy scumbags rather steal from us than work hard like everybody else?

In the business world, it's sometimes said that "where there's smoke, there's fire." At Snapchat parent company Snap, Inc., it appears the equivalent of smoke is executive turnover.

Welcome back, my novice hackers! This new series on Bluetooth hacking was inspired by a recent episode of Mr. Robot (my favorite TV show). In episode 6, Eliot hacked the bluetooth keyboard of the police office in order to hack the prison and release his nemesis, Vera. This is just one of the many hacks we will explore in the series.

As great as the Internet is, it is not without its dangers. Hackers at any time may be breaking into your online accounts and compromising your sensitive information. Last year, hackers broke into Facebook, Gmail, and Twitter and made off with 2 million stolen passwords.
(Series designed to help explore whether your ideal employment ideas should be formalized into a business venture or as an employee or volunteer value added problem solver).

The name of your business will leave an impression on people as this is probably the first information they will receive. Make sure to express yourself and give the impression you intend by choosing the best name for your business.

Susie Henderson, owner of Auntie's Beads, explains how to be successful in the bead industry. Learn how to make up business cards, get the business name out there, display the product, have the product ready, and how to present the product nicely. Watch this instructional video series and follow along to pick up these great business tips.

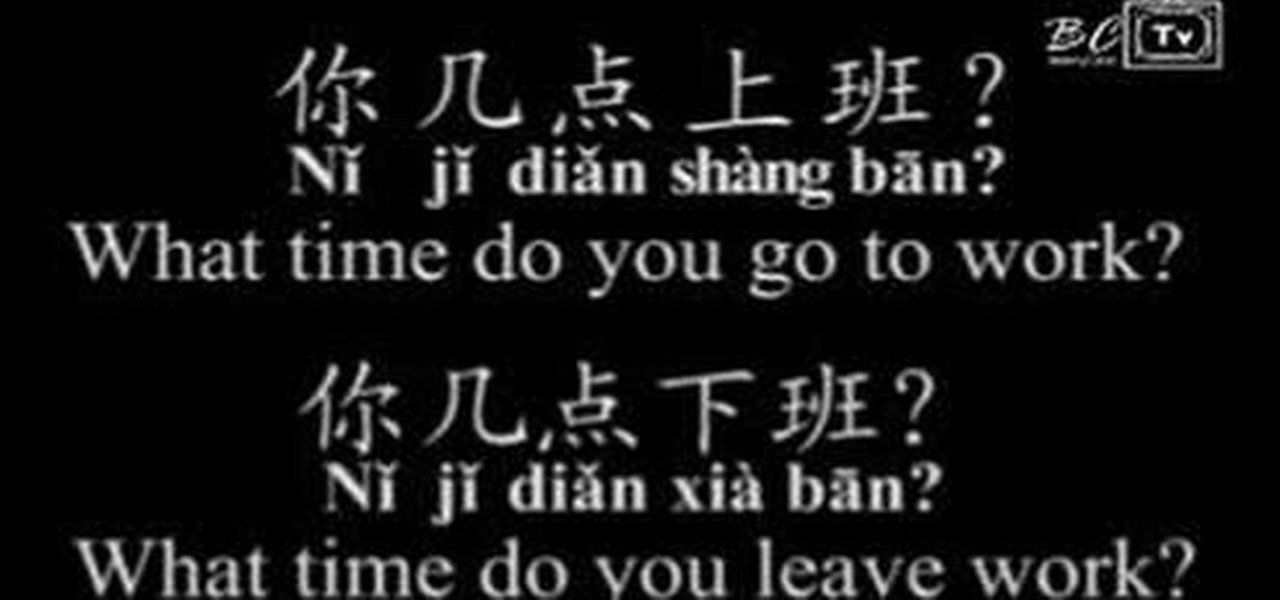
Benny teaches you some Mandarin Chinese business phrases including "Go to Work," "Leave work," and "Overtime."

If you're using Social Media to promote your business, don't forget to promote yourself as well. Put a face to your Facebook page by watching this video and learning how to display the Page Owner feature on your business' Facebook page.

In this clip, you'll learn how to use the BackTrack Linux distro and the Aircrack-ng WiFi security app to hack a WEP network. The process is simple. For more information, including step-by-step instructions, and to get started testing the security of your own WiFi networks, watch this hacker's how-to.

Learn how to use the Backtrack Linux distro and the Aircrack-ng WiFi security app to crack a WEP key. The process is simple. For more information, including step-by-step instructions, and to get started testing the security of your own WiFi networks, watch this hacker's how-to.

In this clip, you'll learn how to use the Backtrack Linux distro and the Aircrack-ng WiFi security app to crack a 64-bit WEP key. The process is simple. For more information, including step-by-step instructions, and to get started testing the security of your own WiFi networks, watch this hacker's how-to.

Business cards are one of the most effective ways of networking with professionals, and making good ones without breaking the bank is hard to figure. This video will show you how to make your own professional looking business cards at home and use them to improve your career.