These days, that pocket-sized computer we call a smartphone is home to your entire digital life. But with the onset of mobile payments and online banking, the line between your virtual world and the physical realm is becoming increasingly blurred.
Some people are of extremely secretive nature. They do not like sharing their personal events in their lives with anyone. Thus people around that person wont be able to figure out details on their life's personal matters. It is not like they want to hide some mysterious secrets from the world, but it is just their nature that they do not want others to know much about them or are too shy to share their feelings with others. Being secretive is neither good nor bad, it is just how they are.

Every day it seems like new information comes to light about how the National Security Agency creeps into our lives. Knowing that they can backdoor into our seemingly private devices is a scary thought, whether you have information to hide or not.
In this video, we learn how to install dry acoustic flooring with Fermacell. To start, you will level the floor and apply compound if you need. Next, you will lay the Fermacell around the room on top of the leveling compound. Push the flooring tightly together so there are no spaces in between them. You may need to cut the flooring to make sure it's the correct shape for the wall. After this, apply flooring adhesive to the seams to make sure they are secure as they are laid down. After this, ...

In this video, we learn how to use secure online passwords. There are a ton of things to consider when creating a password. A weak password is something that someone can easily guess. If you are using a birthday, common dictionary word, child's name, or something common then you are at risk. Your password should combine letters and numbers, and be at least eight characters long. It should also be completely random and have upper and lower case letters. You can use a password assistant if you ...

The way to wear hijab shown in this demonstration with a simple wrap around the head, securing the hijab with bobby pins at the back of the neck. The ends of the hijab are pulled forward to the chest. Then a thin scarf in a contrasting color can be wrapped around and tied at the nape of the neck as well. A portion of the hijab is pulled forward over it and pinned over the ear. Then one of the ends is pulled under the chin to the opposite ear and pinned to the head. The other end is wrapped ar...

Several Tanzanian girls demonstrate how to tie a kanga (an African sarong). The first method is to wrap the kanga around the waist and tuck the end in at the waist to secure. The second method is to wrap the kanga into a cylinder to use it as a base for carrying a parcel on the head. Another way to wear the kanga is to wrap it around the neck like a shawl or wrapped under an armpit and tied over the shoulder for a fancier look. To wear the kanga as a scarf, fold it into quarters the long way,...

To create an apostolic or pentecostal hairstyle, start with a poof in the front of the hair. It can be ratted behind for stability. Use two bobby pins to secure the back corner of the poof. Squirt the hair with hairspray before moving on. Then create a low ponytail in the back of the hair, pulling the top up and out slightly while forming the ponytail so it creates another poof in the back of the head. Spray the ponytail with hairspray then smooth out the hair on the top of the ponytail. Wrap...

This video illustrate us how to make a light bulb oil lamp. Here are the following steps; Step 1: Take all the things required that is bulb, socks,adhesive tape,scissors,kerosene, rim with a hole in the center.

In order to secure a PDF with a password when opened in Adobe Acrobat 9 Pro, press the secure button and go into password security settings. Here you can change on what versions of this software the file will run on, the next option asks which portion of the document is to be encrypted when a password is placed. Further below here is where you actually choose the password, this ensures that only people who know the password will be able to see the contents of the document. Below this is the d...

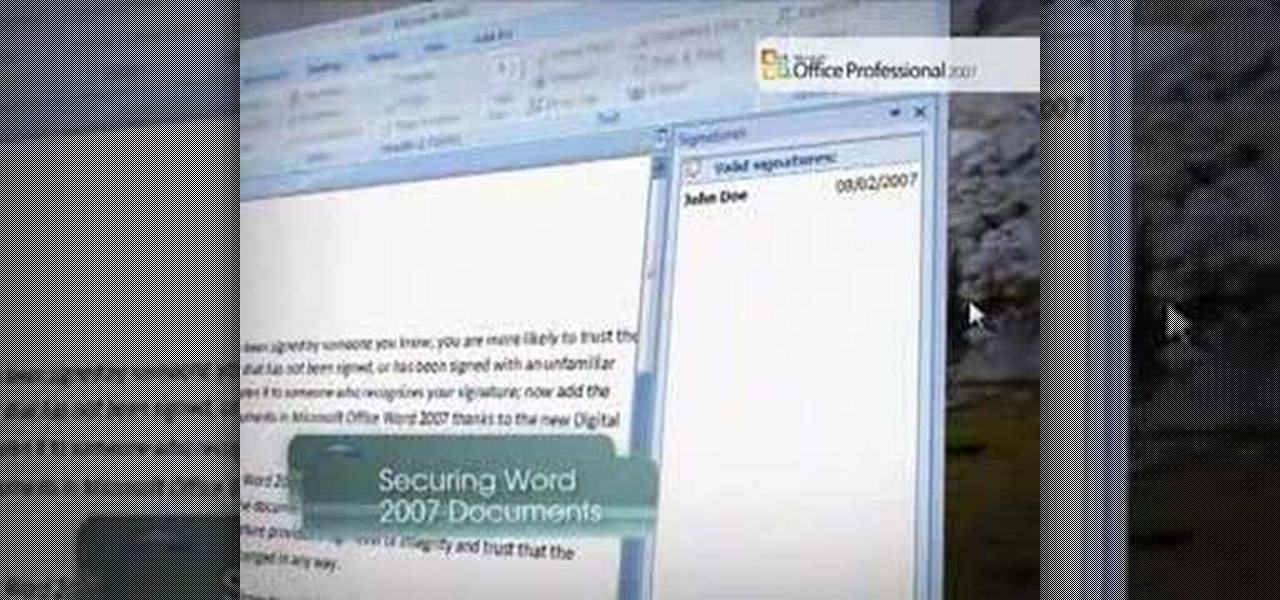
Securing Microsoft Office Word 2007 documents with Digital Signatures - When you receive a document that has been signed by someone you know, you are more likely to trust the contents than those of a document that has not been signed, or has been signed with an unfamiliar signature. Signing a document validates it to someone who recognizes your signature, now add the same degree of integrity to your documents in Microsoft Office Word 2007 thanks to the new Digital Signatures feature. For more...

This half-hour episode of Hak5 covers several topics: Using a DSLR camera to create HD footage, building your own Google TV, unlocking & copying locked files with Lock Hunter, using PicPick for screen capture, using WinDirStat for analyzing & cleaning your hard drive, setting up a secure FTP server with Ubuntu Server, and secretly copying data from USB drives with USB Dumper.

Justice might not have produced any new material in a while, but their place in electronic music history is already secured due to their filthy electro-house beats that have become ubiquitous in the years since they first broke out. Watch this video to learn how to make a dirty electro bass synth line like theirs in Reason 4.

Julia, AKA Hairbeauty4you, gives detailed instructions on how to do a quick half up-do with a twist in under 10 minutes. She notes that this style is best for medium to long length hair. Julia starts with straight hair, then sections off the top part and clips temporarily. She then separates another section on either side of the top part- from the ear to the clipped section- and pulls it back into a high pony tail and repeats identically on the other side, securing each with clear rubber band...

The Lab Rats, Andy Walker and Sean Carruthers, explain Media Access Control (MAC) addresses. Filtering MAC addresses allow you to very specifically control access to your wireless network.

Tie a clove hitch knot again, again, and again.

You're at your friend's house. All you've heard about all day is his new laptop. He's got a brand new top-specced MacBook Pro, and he won't stop going on about it. It particularly annoys you as all you've got is a 4 year old cheap laptop, even if it is running Linux.

In spite of the degree of difficulty it is to install, CyanogenMod has steadily climbed the ladder to become one of the most popular third-party firmwares for Android devices.

In this video, we learn how to do wrapped pigtails on your American Girl doll. First, separate the hair from side to side. Then, take a small section from the front of the hair and put it aside. After this, you will need to comb the hair back into a ponytail and secure with a rubber band. Secure the other side into a ponytail as well, but put all the hair back into it. After this, you will take the front from the other side and wrap it around the ponytail. Clip it into place and then you will...

In this video, we learn how to tie a Palomar knot to secure a fishing line. This knot is pretty easy to tie, it won't take long. First, you will take the fishing line and make it into a loop. After this, insert it through the eye on the hook. Next, bring it back over and then tie an overhand knot, leaving it a little loose when you tie it. You should be able to see the working end hanging down. Now, take the loop and put it over the hook. Now when you tighten it up, you will have the complete...

In this video, we learn how to do the triple nifty knots hairstyle on your AG doll. First, comb the doll's hair back and then take the hair from the crown of the head. Put this into a ponytail and then secure with a rubber band. After this, section the tail off into two parts and twist them individually. Then, bring these around each other and create a bun at the top of the doll's head. Secure this with a rubber band. Do this with two other sections of the hair on the left and the right. When...

In this tutorial we learn how to fix an RV awning that will not retract. If you find yourself in the situation where the awning on your RV just won't retract, then this is the video for you! To secure the awning you will first need to go to the roof of the RV. When you get on top, you will need to look at the awning and see if something is stuck and causing it to stick. Manually secure the awning when you go to the roof so that it will stay in place for when you need it. If this doesn't help,...

In this tutorial, we learn how to install a cold air intake for a 96-04 Mustang. First, you will need to lift up the hood and locate/disconnect all wiring harnesses. Then remove the bolt around the air filter housing and set aside. Separate the intake and the housing, then pull out the air filter housing. Reinstall rubber grommets that may have come out, then disconnect all hoses from the engine. Put the intake and the pieces together, then you will start to place it back into the car the way...

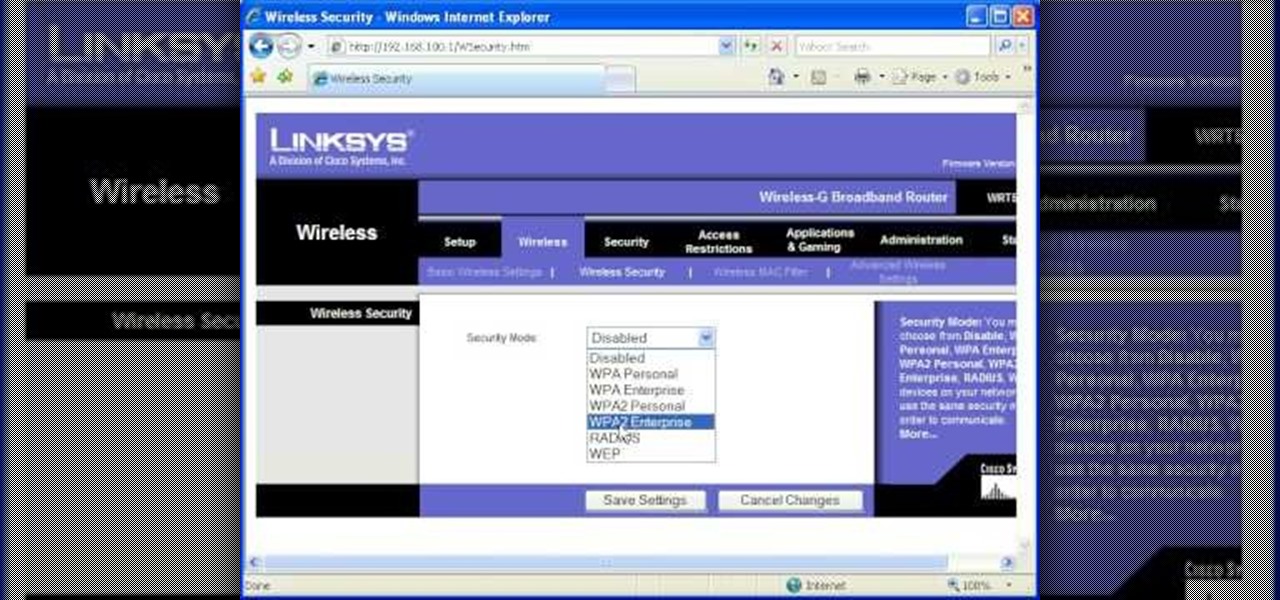
In this tutorial, Brian teaches us how to make your wireless network secure. First, go to the start menu, then go to run and type in "cmd", then type in "iconfig /all". Now a new window will pop up and you will look for the default gateway. Find the IP address to log onto the routers you have. Now, type in your IP address into your address bar on your internet browser. You will be asked to log into your account with your password and user name, which you can find at the manufacturers website....

In this video, we learn how to make a box. First, fold the piece of paper into a triangle, then another triangle. Now, unfold the paper and fold all the sides into each other, making a square. After this, fold in the sides once more, making sharp creases on the edges. Now, open up the paper and do this again on the other sides, opening up again when finished. Now, fold the sides of the paper and turn it upside down. Follow the creases that you just made to fold the box up into a secure box. M...

In this tutorial, we learn how to set up and secure a wireless router. First, take your cable and plug it into your modem from your computer. After this, plug in an Ethernet cable into your modem to a wireless router. Now, plug the wireless router and modem into the wall. Now, look for the icon on your computer that says you have connected a new device to it. Go through the set up wizard to make a new wireless network, once it doesn't find one, connect a USB to the computer. Now, click on the...

In this tutorial, we learn how to replace the spark plugs on a 2008 Kawasaki Ninja 250. First look underneath your bike to find out exactly where the spark plugs are at. Next, use wrenches and ratchets to loosen the parts around the spark plugs, then remove the spark plugs completely. After you have pulled them out, replace them with the new one and secure them into place. When finished, replace all the casing around the plugs and make sure you secure them tightly. Add on all bolts when you a...

In this tutorial, we learn how to make a floating illusion style necklace. You will need: beading wire, crimping pliers, wire cutters, beads (your choice), crimp beads, crimp covers (3mm), and a clasp (barrel clasp). First, cut your beading wire to the length you want your necklace, add 3-4 extra inches. Next, space your beads out on a beading board evenly, 1 1/2" apart. Now string a crimp bead onto your wire and take the end of the wire and string it through the crimp bead on the opposite si...

In this video, we learn how to properly pack glass for moving. Make sure you have a table or work area that has a furniture pad on it. Now, place packing paper onto the bottom of a box carton for glasses and china. Glass should be on the top of the box while plates should be placed at the bottom. Put the glasses into a rolled piece of paper until secured, then place upside down into the box. When finished, add crushed paper to the top of the first layer to avoid any glass from breaking. Make ...

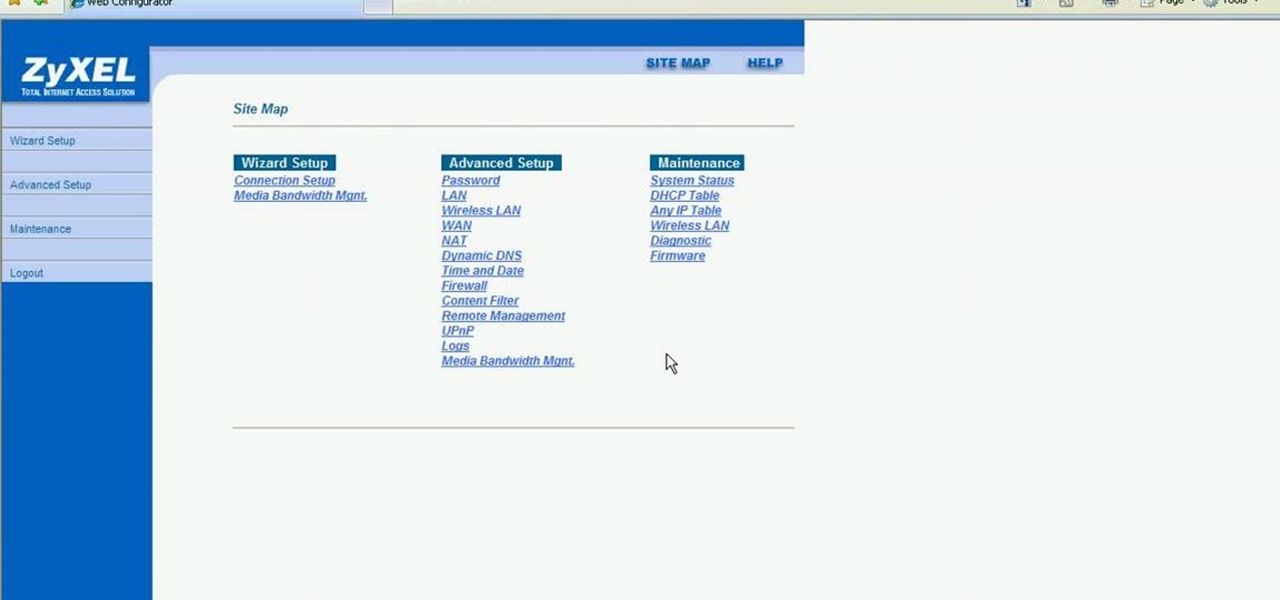
This video shows how to secure a wirelees internet connection on your Zyxel P-660hw-t1. For this, first click on Start button and open Internet Explorer(or any other browser). On the address bar of the browser, type in the IP address of your router. On the next page, enter your password and on the next page, either change the password or ignore. On the next webpage, under Advance setup, click on Wireless LAN. On the next page, click on 8021xWPA. Select authentication required and then click a...

Abigail Goss demonstrates a traditional Apostolic hairstyle, the vertical roll with pin curls. She starts by creating a poof, back combing the roots from the crown to the forehead. Then she creates a section of hair above the ears. She rolls this hair several times in one direction and then puts all of the hair into a ponytail at the base of the neck. At this point the style looks like a french twist with a ponytail at the bottom. She then coats the hair with gel. To make the curls, she takes...

This video illustrate us how to make a piano bracelet on a loom. Here are the following steps: Step 1: First of all secure the piano tabs to the loom and criss cross the string on the tabs.

In this how to video, you will learn how to keep your Windows operating system secure by look for and closing open ports. First, you will need to run the program called Net State. Once this is open, type in netstat -a. This will list main connections. Next, type in netstat -an. This will give you the numbers of ports that are open. Some may be used for file sharing and anti-virus programs. If you want it completely secured, you should only have one running. This video shows you how easy it is...

Most of the home wireless networks are not set up by professionals and hence they might lack in security features. People just set up the wireless networks by connecting the devices and powering them up and never care to apply security settings to the network. This may result in your wireless network being compromised by unwanted external entities. How ever you can do a web based configuration settings and secure your wireless network by password protecting it. This settings differ from the m...

How to build a high tunnel to protect your plants

This is a video using Swarovski Crystals to make jewelry. This video shows how to make one with a gold bow. You need a pendant with 2 hoops (in this case it is a gold bow), a pendant holder, a crystal, a bill, and pliers. You take the bill and hook the crystal on it. Then you hook the bow on it and secure it using the pliers. You take the pendant holder onto the top of the bow pendant, and press it down to secure it, and you’re finished. You can also make rings, earrings, necklaces, and many ...

This video shows the viewer how to secure crimp beads using both crimping pliers and chain-nose pliers for the purpose of jewelry making. The video uses two millimeter crimp beads, beading wire, and both sets of pliers to demonstrate the technique. To crimp using the crimping pliers, the viewer will utilize both notches of the pliers to crimp the bead onto the wire. In order to crimp using the chain-nose pliers, one must simply flatten the bead onto the wire. Crimping is a good method to secu...

Hak5 isn't your ordinary tech show. It's hacking in the old-school sense, covering everything from network security, open source and forensics, to DIY modding and the homebrew scene. Damn the warranties, it's time to Trust your Technolust. In this episode, see how to secure remote desktop.

You don't want anybody to have access to your cell phone. Nobody. Well, instead of the standard unlock mechanism, the one anybody can unlock your cell phone with, the Motorola DROID, and Android enable mobile device, allows you to create your own unlock pattern, secret to anyone else, which wakes it from sleep mode. Best Buy has answers. The Best Buy Mobile team explains how simple it is to set up a secure lock on a Motorola DROID cell phone.

In order to begin, you will need the following: Three hair tiesBobby pinsHair spray or spray gelRat tail combHair net