While Magic Leap World gets its share of fun apps for playing with Porgs, watching TV, and exploring the ocean's depths, developers are making a strong business case for the Magic Leap One as well.

The recent industry whispers in augmented reality are mostly about Apple and its rumored fashion-friendly smartglasses, but one company isn't waiting for the iPhone heavyweight to enter the fray.

Who's ready to let future Facebook augmented reality smartglasses read their brain? Well, ready or not, the tech giant is making progress in the area of brain control interfaces (BCI) by funding research.
Android's stock battery menu is pretty decent. You can see which apps have been using the most power, and you can tell when your CPU was awake or asleep, among other things. But a lot of times, battery-sucking services will get lumped under the generic "Android System" header, and even though you can see when your CPU was awake, you can't exactly see why.

Hello again, reader! In this post, we are going to cover some data types and how to declare variables. It shouldn't be too hard so just sit back, relax, grab some popcorn and enjoy the ride (while you still can!).

Welcome back, my aspiring hackers! Those of you who use Windows in a LAN environment understand that Windows machines can share directories, files, printers, etc. using "shares." This protocol dates back to the 1980s when the then dominant computer firm, IBM, developed a way for computers to communicate over the LAN by just using computer names rather than MAC or IP addresses.

Welcome back, my novice hackers! In a recent tutorial, I showed you how to use shikata_ga_nai to change the signature of a payload to evade detection by security devices (firewalls, IDS, etc.) and AV software.

No one can deny that Bashar Al-Assad’s regime has been responsible for violence. But in failing to equally acknowledge the fact that NATO-backed rebels have also carried out innumerable atrocities is not only dishonest, it represents a deliberate effort by the press to manipulate the narrative of unfolding events in Syria as a one-sided war crime rather than the truth – which is the fact that Syria is in a state of civil war.

Magic. Does it really exist? Can you really put a hex on somebody… or a love spell? Can you really cast supernatural spells? Believing is up to you, but anyone can be bewitching with the help of a little black — and white — magic.

Good day to everyone, today I will present some basic and advanced concepts that targets sophisticated attacks on the social basis, also I will write about some steps that can prevent this attacks from occuring, basically we will examine Social Engineering from the angle of attacker and victim, some people who are interested in security and work for middle-sized companys can learn and use something interesting from this post.

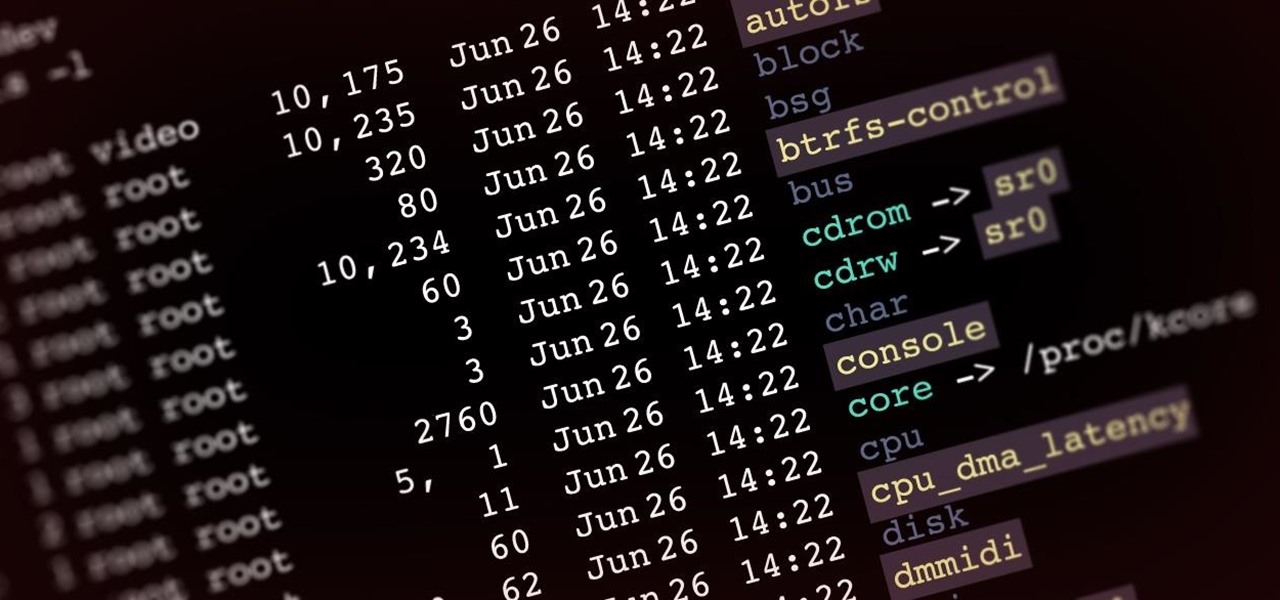
Welcome back, my aspiring hackers! In recent tutorials, I have made reference to the name and location of the Linux devices in the file system, such as sda (first SATA or SCSI drive). Specifically, I have mentioned the way that Linux designates hard drives when making an image of a hard drive for forensic purposes.

The Oscars are just a couple of days away when Hollywood will celebrate the best crop of films from 2019 in the US and internationally.

The research team from Nvidia is returning to SIGGRAPH, an annual hotbed of innovation, with two new advancements in augmented reality displays.

With the macOS stager created and the attacker's system hosting the Empire listener, the malicious AppleScript can be designed and disguised to appear as a legitimate PDF using a few Unicode and icon manipulation tricks.

Soon, kids young and old aspiring to imitate Iron Man will only need to learn how to duplicate Tony Stark's snarky wit, because Hasbro will now supply the augmented reality helmet.

With the addition of the OpenSSH client and server in the Windows 10 Fall Creators Update, you no longer have to rely on third-party programs to open an SSH server and connect to a Windows machine. While still a beta feature, this represents a long-overdue update fulfilling a promise made back in 2015.

Earlier this year at WWDC, Apple made a big show of featuring augmented reality as a central part of iOS moving forward. But since then, other than comments from the company's CEO, Tim Cook, we haven't seen much direct promotion of augmented reality from the company. Until now.

One of the most highly-cited drawbacks to the HoloLens is its limited field of view (FOV), but now it appears that Microsoft has solved that problem.

If you're a regular reader of this site, there's a good chance friends and family turn to you as their volunteer technical support staff.

It's no secret that devices leak data, but sometimes they do so in ways you may not expect. Your phone, laptop, printer, and IOT devices leak Wi-Fi information that can (and is) used to track you.

We can't be in two places at once, but with virtual touch interfaces we can theoretically use a machine to act as our second body in a remote location. Over at MIT, Daniel Leithinger and Sean Follmer, with the advisement of Hiroshi Ishii, created an interface that makes this possible.

Welcome finally, to a tutorial on buffer overflows! At last we have reached an exciting part of this series where I will dedicate the entire article on explaining and exploiting the notorious vulnerability. Grab some popcorn, sit back and enjoy the show.

If you want to raise your children in a Christian way, it is very significant to make them understand what Jesus' sacrifice did for them.

The big question this week would be the controversial Obamacare mandate. And heres the answer: Yes. Obamacare passes Congress' filters and is now an official OK. Texas college hacks drone in front of DHS — RT.

This is a pretty simple how-to, because a doorbell is a pretty simple mechanism! The difficult part is in understanding music note blocks.

The Galaxy Note 20's speakers are so loud and capable that they almost never need to be set to 100%. But by the same sense, it can be hard to find that just-right volume level since one increment represents a bigger change in sound output. Believe it or not, there's actually a first-party tool to fix this problem.

Its official: On May 8, T-Mobile finally released the Android Oreo update for the LG V30 and V30+. Now, every major US wireless carrier has pushed the update. For me, this update is a big deal. Not only does Android Oreo bring some new tools and features, but LG has also included a few additions as well.

Millions of travelers pass through airports each day without understanding how powerful and insecure a boarding pass can be. Anyone can scan the boarding pass barcode with a mobile app, allowing access to frequent-flyer accounts and even a passenger's temporary airline account. In this guide, we will explore how hackers scan and decode the information contained in a boarding pass barcode and why.

Thanks to backups, Signal conversations can span over multiple years and multiple phones. These archives can get rather large as you share photos, videos, and other files with friends. But between the other apps and large files on your phone, you might not be able to afford to keep all those messages.

After stealing the show at the HoloLens 2 launch and starring in Qualcomm's unveiling the Snapdragon XR2, holographic video conferencing app Spatial has landed a leading role in Magic Leap's second act with the enterprise segment.

It looks like Jaunt's pivot from VR to volumetric captures services for augmented reality experiences has paid off.

After teasing what smartglasses powered by Snapchat might look like with two product cycles of camera glasses, Snap has now added augmented reality capabilities to its third take on Spectacles.

While these days it is better known for the cross-platform gaming sensation Fortnite, Epic Games also makes Unreal Engine, one of the top development environments for 3D content and, in turn, augmented reality and virtual reality experiences.

Adding another arrow to its quiver of augmented reality acquisitions, Apple has reportedly acquired Spektral, a computer vision company with technology for real-time compositing (otherwise know as the "green screen" technique in broadcast TV and film).

It is almost indisputable that smartglasses and head-worn displays are the future of augmented reality. However, at this precise moment, they are still a very niche market.

Developers can now publish augmented reality experiences that are viewable through the experimental version of Chrome and ARCore.

For years, Magic Leap has promised to deliver stunning augmented reality experiences that will outperform any other competitor, and a newly revealed partnership hints that the company may be able to deliver on those promises.

For social media platforms like Facebook, augmented reality represents a whole new art form with which users can express themselves online. Now, Facebook is giving those users a new brush.

Fast-casual burger restaurant Bareburger expects to soon replace all of its paper menus with 3D models of its burgers and other items rendered in augmented reality, but for now, the company is preparing some rather interesting limited AR interactions.

Google's AI investment arm, Gradient Ventures, has joined a $10.5 million round of funding for Ubiquity6 and its platform for shared augmented reality experiences, just weeks after Google's GV fund backed a competing AR cloud platform.