Garden of Imagination demonstrates how to make a miniature corn on the cob out of polymer clay. First, roll and flatten two small balls of green clay to make the corn husks. Make the husks pointed on both ends. Take a piece of yellow clay and roll it into a conical corn cob shape. Insert the corn on the cob into the texture piece and roll it to achieve the textured corn kernels. Wrap the corn on the cob between the two green husks. Make sure the husk leaves overlap in the front. Squeeze the c...

In this video tutorial ChowTime will show you how to grill caramel corn on the cob and Italian corn on the cob. These recipes are easy and fun. Remember to use the corn as soon as it is picked to ensure the quality of taste. Fun facts include that corn was first cultivated about ten thousand years ago in the highlands of central Mexico and that the average ear of corn has eight hundred kernels! after the corn has soaked for a minimum on thirty minutes, place it on the grill with the temperatu...

Lightly grease the bottom of a baking dish with corn oil. Set aside. In a mixing bowl, throw in cornstarch, sugar, water and coconut milk. Stir the mixture until the ingredients are blended well.

This video demonstrates how to make raw vegan nori cheese sticks. First, put sunflower kernels, nutrition flakes, salt, olive oil, water, shredded cheese, and a whole jalapeno into a blender. Blend until the mix is paste-like in consistency. Slice sheets of nori into smaller pieces and spoon some of the paste onto the smaller pieces. Wrap them into little cylinders. Set them out and let them dry until most of the moisture from the paste has gone, and the stick is firm. This video is useful fo...

Hak5 isn't your ordinary tech show. It's hacking in the old-school sense, covering everything from network security, open source and forensics, to DIY modding and the homebrew scene. Damn the warranties, it's time to Trust your Technolust. In this episode, see how to get free WiFi by tunneling through DNS.

We need to take our privacy and security much more seriously. Whether it's malware-infected apps or the mishandling of our data by companies like Facebook, there are threats all around us in this digital world. Fortunately, some smartphones are simply designed to protect us better.

Sometimes, you come across a recipe or a food hack and think, "That is the weirdest thing I have ever heard of; who would make that?" That was my initial reaction when I read Food52's piece about popcorn milkshakes.

Probably one of the most sought after features of the LG G2 is its "Knock Knock" capabilities. Rather than dealing with that pesky power button, you simply double-tap portions of the screen to either sleep or wake your device.

Privilege escalation is one of the essential skills a hacker can have and often separates the newbies from the pros. With a continually changing landscape and a plethora of exploits out there, it can be a problematic aspect of any attack. Luckily, some tools can help expedite the process. Linux Exploit Suggester is just one of many to help you get root.

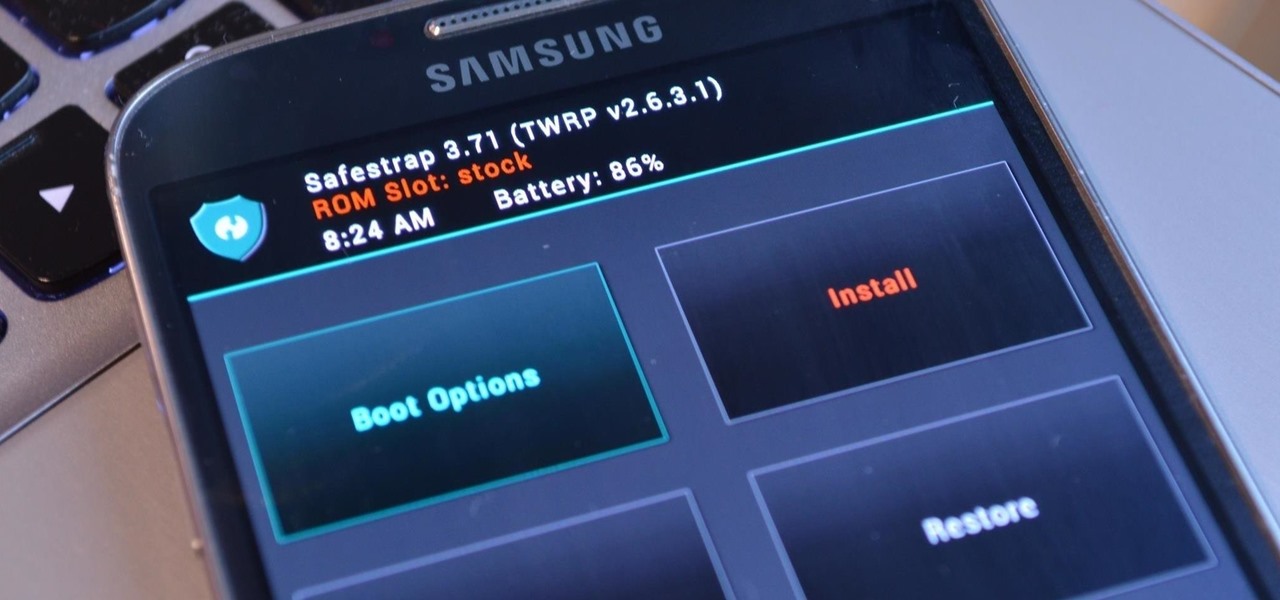
Rooting has a long and storied history in the Android community. As OEMs push out more refined software, the need to root has diminished — still, the number of incredible things you can do with a rooted phone is enough to tempt many enthusiasts. Luckily, some manufacturers are still putting out root-friendly devices.

One of the only downsides to the Pixel XL is that Google's flagship phone does not have stereo speakers. But if Android's awesome development community has taught us anything over the years, it's that limitations like these can be bypassed with some creative software tinkering.
Hello everyone! This is my first attempt at a tutorial here. There are a couple great assembly tutorials here, and I wanted to toss my coin in the fountain.

welcome back my masters , teachers and classmates , in this second part of this 0-day series we will learn the basic of fuzzing, and i bought some gift for nullbyte(a 0 day vuln that will be released today exclusively on null-byte) .

Welcome back, my amateur hackers! When you are using and administering Linux, it is important to be conversant in the use of the log files. As you know, log files are the repository for much information about our system, including errors and security alerts.

Third-party ROMs like CyanogenMod are the ultimate form of customization for softModders. Hard-working developers offer us alternate Android experiences to replace our often bloatware-riddled stock ROMs.

Sense appears on over forty Android devices, but HTC's notorious GUI was actually designed with a completely different mobile OS in mind—Windows.

Post-exploitation is often not quite as exciting as popping the initial shell, but it's a crucial phase for gathering data and further privilege escalation. Once a target is compromised, there's a lot of information to find and sift through. Luckily, there are tools available that can make the process easy. One such tool is Postenum.

Getting root is considered the Holy Grail in the world of Linux exploitation. Much like SYSTEM on Windows, the root account provides full administrative access to the operating system. Sometimes even a successful exploit will only give a low-level shell; In that case, a technique called privilege escalation can be used to gain access to more powerful accounts and completely own the system.

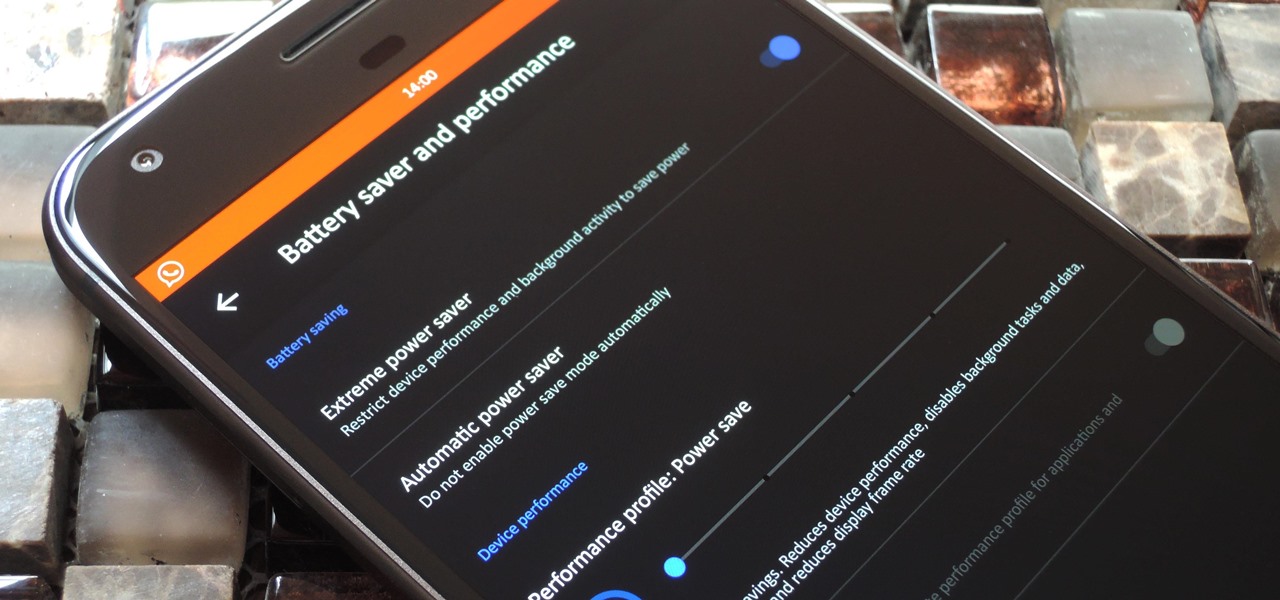
The OnePlus 3 and 3T are a pair of phones which allow you to do practically anything you want, because OnePlus is such a developer-friendly company. They almost always release kernel sources, and their phones sport an unlockable bootloader that doesn't void the warranty. But while their software is certainly solid (miles ahead of Samsung's TouchWiz), it still has room for improvement.

LineageOS, the successor to the wildly popular CyanogenMod custom ROM, is adding an interesting new feature that could potentially save lots of juice when your battery is running low. When enabling "Extreme power saver" mode, which can be set to kick in automatically at 15%, you'll soon have the option of changing your kernel's performance profile as well.

The OnePlus 3T was released about five months after the OnePlus 3 with several noticeable upgrades. Firstly, it has a new processor, the Qualcomm Snapdragon 821, which is the same one that the Pixel and Pixel XL sport. Second is the 16 MP front-facing camera with a different sensor. And the next big change was a slightly larger 3,400 mAh capacity battery.

Ever since developer bponury created his TouchControl app for the Galaxy Nexus back in 2011, manufacturers and modders alike have been racing to re-implement the "Double-tap-to-wake" functionality it brought to the table. We've seen LG do it with their "Knock On" feature, we've seen Motorola put a twist on it with "Active Display," and we've even seen Google implement the feature in their Nexus 9 tablet.

Welcome back, my aspiring hackers! Although this article may have been better placed first in this series, I doubt that anyone would have read it when just starting out studying Linux. Now, that you are well into your Linux studies and have some familiarity with how it operates, I'd like to take this moment to explain the philosophy around the Linux operating system.

Desktop users have taken advantage of dual-booting operating systems for decades now. If your core system software is lacking in any regard, dual-booting a secondary OS can give you access to those features that you're missing out on.

Finding the right mix of custom ROM, kernel, and tweaks for my OnePlus One has left me flashing every new release I come across. This has led to many hours going through thread after thread trying to find the latest and best software out there for my phone. While I do enjoy the hunt, I would rather have a centralized location that covers all my bases, so that's why I have started using OnePlus One, an app by Alex Inthiaano.

Learn how to make your own homemade granola with Kat Curlee in this video tutorial. Granola is a great healthy snack that can be eaten alone or added to yogurt. You will need 3 cups of regular uncooked oats, 1/2 cup flake coconut, 1/2 cup sliced almonds, 1/2 cup chopped or halved pecans, 1/2 cup walnuts, 1/2 cup pine nuts, 1/4 cup honey-crunch wheat germ, 1/4 cup sunflower kernels, 1/4 cup plus 2 tablespoons honey, 1/4 cup vegetable oil, 2 1/2 tablespoons water, 2 tablespoons brown sugar, 3/4...

Chef John from FoodWishes prepares a grilled halibut steak with corn and chanterelle mushrooms. You can find chanterelle mushrooms in most upscale markets. Before cutting into chanterelle mushroom make sure you remove as much dirt as possible by using a brush or the edge of a fork. Next, cut chanterelle mushrooms into thick meaty slices.

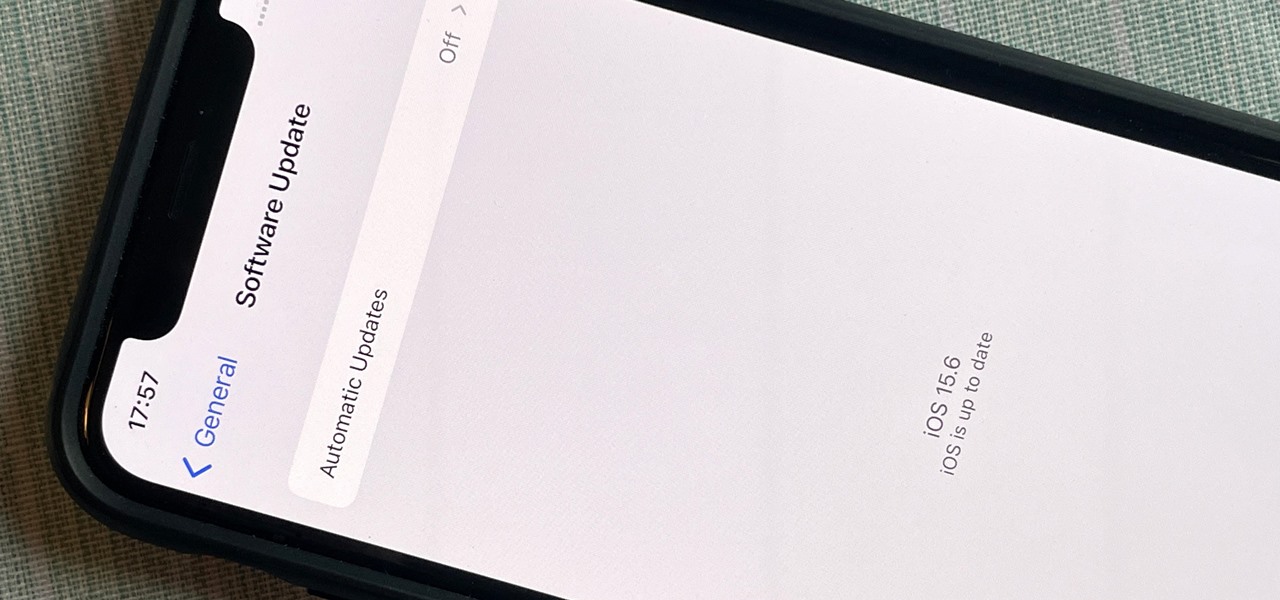
After nearly two months of beta testing, Apple is finally pushing the iOS 15.6 software update to all iPhone users. While it's not as feature-rich as the iOS 15.5 or iOS 15.4 that came before it, there are still a few things you'll want to know about it.

A quick tutorial showing how to, with one click, show kernel times in your task manager.

After gaining access to a root account, the next order of business is using that power to do something more significant. If the user passwords on the system can be obtained and cracked, an attacker can use them to pivot to other machines if the login is the same across systems. There are two tried-and-true password cracking tools that can accomplish this: John the Ripper and Hashcat.

KNOX is a major pain for Samsung owners who like to modify their devices. Its combination of hardware and software security measures make things rather difficult when you're trying to modify system-level files and functions without voiding your warranty.

Welcome back, my greenhorn hackers! In previous Wi-Fi hacking tutorials, I have shown you ways to create an Evil Twin, to DoS a wireless AP, and to crack WEP and WPA2 passwords, but in this tutorial, I will show you something a little bit different.

With a root bounty of over $18,000 up for the taking, developers were highly motivated to get the AT&T and Verizon Wireless variants of the Samsung Galaxy S5 rooted. Legendary hacker George Hotz, aka Geohot, has won the race and can now step up to claim his prize.

Finger foods. They're the best party snack, and the best snacks for children more worried about playing than eating. There's a lot of good ones you can make, like fruit kabobs, barbecue wieners, lunchmeat rolls, cheese balls, popcorn, and pesto dip. Make these six delicious recipes for your next party and you’ll have your guests coming back for seconds!

In this how-to video, you will learn how to make kettle corn. Fist, add 1 tablespoon of salad oil in a 3 quarter pot. Add a third of a cup and 1 tablespoon of popcorn. Stir the mixture for a while so the kernels will not burn. Keep the lid near. Make sure you are using a circular motion when stirring. Next, add 2 tablespoons of sugar and a fourth of a teaspoon of salt. Keep stirring the mixture. You can use the lid in order to shield yourself from the steam and popping. Once the popcorn start...

What's better than homemade corn tortillas? Follow these simple steps for homemade corn tortillas that will make your guests shout "Ole!"

Prepare this easy vegan meal that serves six. The quinoa and black beans takes 15 minutes to prep and 35 minutes to cook.

With the same starting price as its predecessor and a nice list of improvements, the OnePlus 6T is a great buy for a number of reasons. But for many Android users, the main selling point for the latest OnePlus flagship is how easy it will be to root and mod the device.

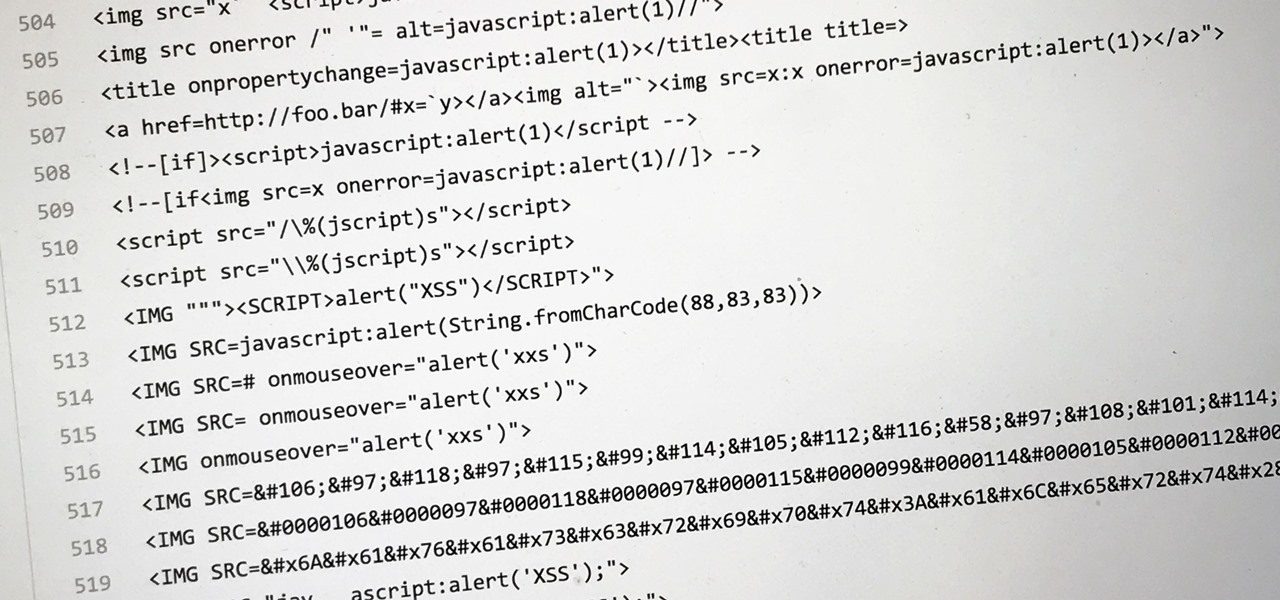
Dirty, malformed, and outright mischievous text strings have long been the enemy of interactive website developers. Strings contain any combination of letters, numbers, spaces, and punctuation, and are entered into text boxes on websites by users. These strings in particular can do everything from highlighting XSS vulnerabilities to soliciting 404 error pages.

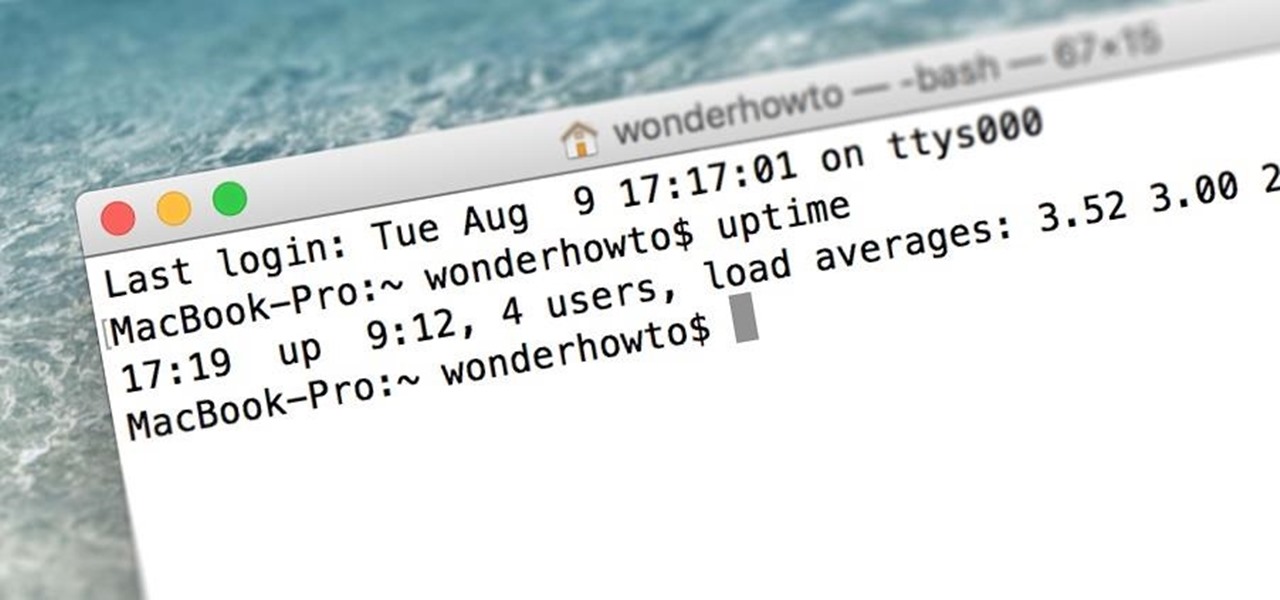
When was the last time you restarted or shutdown your Mac? In the post-iPhone era, most devices are now powered on almost constantly. For better or for worse, the computing landscape has accommodated this "always on" trend, but you still need to periodically restart your devices—especially your Mac.