
How To: Completely make a foam boffer sword for LARPing
This four-part video tutorial will show you how to make a basic boffer sword for full contact padded weapons fighting and live action role-playing.


This four-part video tutorial will show you how to make a basic boffer sword for full contact padded weapons fighting and live action role-playing.

Look at the money you are receiving. Carefully inspect it for any strange colors, marks, or texture. Do not assume that a different color, texture, or design is simply a mistake made at the treasury. The bills there are all made the same based on the denomination.

Looking to get an FHA loan? The Federal Housing Administration, FHA for short, provides mortgage insurance on loans made by FHA-approved lenders throughout the U.S. Here's how to get your FHA-insured loan. Learn how to get one with help from this video.

Watch this automotive video tutorial to see how to clean the mass air flow sensor in a Toyota FJ Cruiser. These detailed instructions will show you exactly how to remove and clean the MAF (mass air flow) sensor in the FJ Crusier, to ensure that your engine runs at peak performance.

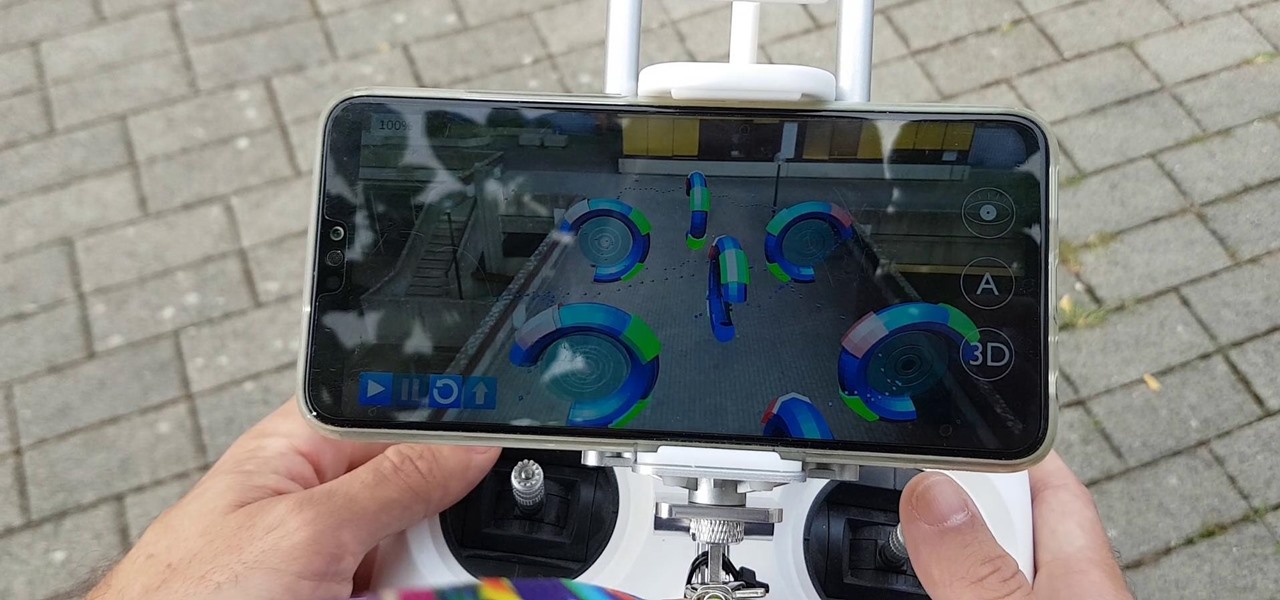
If you call yourself a hobbyist or a kid at heart, you know that remote-controlled vehicles are more than just fun. If you're a serious R/C man, you'll know all about doing everything to your model truck or car, like fixing wheels, vamping the pinion gears, waterproofing, troubleshooting, electronic diagnostics, setting up, programming and finally... racing. As much as you know about these remote-controlled vehicles, it will never be enough, you'll always be looking for more...

An inadequate soldering job, assuming it passes inspection, can cause leaks, corrosion and call-backs. But a quality soldering job done on copper piping can last a lifetime. For a look at professional soldering techniques for the plumbing craftsman, take a look at this two-part video tutorial series.

How to pick plants and trees at a nursery

Are you getting the most out of your sprinkler system? Are there parts of your lawn that always remain dry and brown? Every springtime you should perform an inspection of your sprinkler system. This how to video shows you the steps to appraising you sprinkler system and some remedies for common sprinkler problems. Watch this how to video and you can have a more beautiful lawn this spring.

This video shows you how to inspect a pool for safety and proper maintenance.

Reduce your chances of becoming the seatmate everyone hates by learning how to head off a screaming jag.

Determining the antivirus and firewall software installed on a Windows computer is crucial to an attacker preparing to create a targeted stager or payload. With covert deep packet inspection, that information is easily identified.
Drone mishaps, such as the collision that scratched a military helicopter in New York, are becoming something of an everyday hazard.

You can feel it in your bones. You may die if you don't get this phone. There's just one problem — the price. Suddenly, you come across what seems like manna from heaven. That very device, at a deeply discounted rate, can be yours.

Four months after unveiling the latest productivity apps for the HoloLens, Microsoft now has a series of compelling real-world use case videos showing how the augmented reality device and its apps are helping oil giant Chevron.

The first augmented reality hardware and software functional requirements guidelines have been released today by UI LABS and the Augmented Reality for Enterprise Alliance (AREA).

In an article published in early-2015 by Peninsula Press, it was reported that the demand and the salaries for cyber security professionals are exploding! They cite that 209,000 cyber security jobs were unfilled last year, and that job postings have increased over 74% in the last 5 years. Job opening are expected to grow by another 53% over the next 3 years. You are definitely in the right field, my tenderfoot hackers! Some researchers are expecting information security jobs to continue to gr...

Did you know you can help protect yourself when traveling with a gun? No, not like that; and not in any way that's going to land you in prison. Simply by packing a gun, you can ensure that not only will your luggage be safer, but that the airline will make certain that it reaches its destination. Photo by Alamy

It has been a long while since I last came here to write an article. Graduate school keeps you busy. After I looked over what I had written previously, I decided that I should introduce another fun topic from cryptography. In this case, steganography.

In case you didn't already know, augmented reality is here. It's no longer just an idea in a cyberpunk novel. And while augmented reality has been around for a long time, the actual technology is finally catching up to the idea.

Perhaps in tribute to the season premiere of Game of Thrones, Google Glass is demonstrating that what is dead may never die, as Alphabet's X (formerly Googlex) has revealed that the Enterprise Edition of the smart glasses are now available to businesses.

Multistate outbreaks of Salmonella infection in humans have led the Centers for Disease Control to advise caution when interacting with poultry. A press release on June 1st mentioned eight multistate outbreaks connected to backyard flocks. As of May 25, 372 people in 47 states were reported infected with the outbreaks' Salmonella strains. That means this year could be as bad as 2016, a record year, for salmonella outbreaks with 895 people infected.
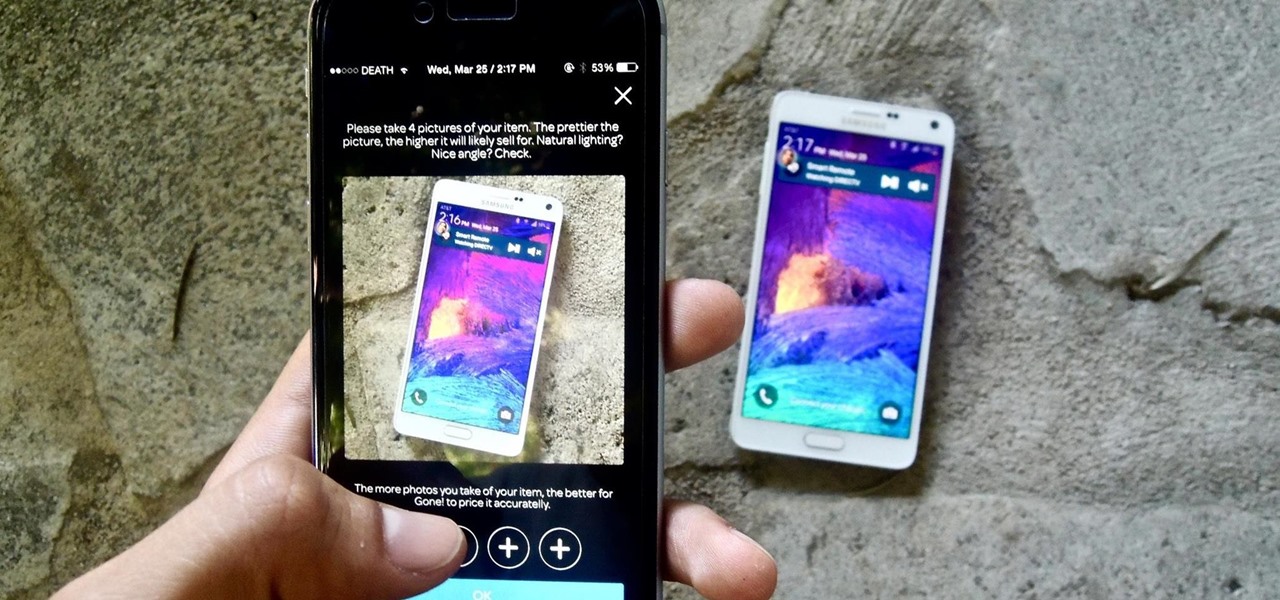
If you want to sell all of the old electronics lying around your home, it takes a lot of work. If you go the eBay route, you have to take tons of pictures, describe it accurately, wait for a week until someone bids on it (or not), then package it, ship it, and wait for feedback. Craigslist is a little bit easier, but usually requires you driving somewhere to meet the buyer in a public place (if you want to play it safe).

After performing a Vital Signs examination on a patient, usually, the next step for a doctor is performing the HEENT.

Buying a home is a big step so find out just what is involved when you are ready to bid for the house of your dreams. The whole process can be bit nerve-racking but as long as you stick with it you’ll be a home-owner in no time.

Automotive lighting is one area of mechanics and car care that might seem intimidating to the average driver when it comes to do it yourself repair and replacement. However, vehicle headlamps work very similarly to all the lighting fixtures encountered around the home or office: bulbs illuminate the road, and occasionally need to be replaced to ensure safety on the road and proper standards for inspection. In this video clip series, you will learn the basics of headlight and taillight removal...

A good endoscope camera can be an incredible tool for a variety of jobs. Whether you have to look under something heavy before you move it, look down a pipe before you clean it, or just give yourself extendable, bendable vision, an endoscope camera can be a fantastic tool when it works.
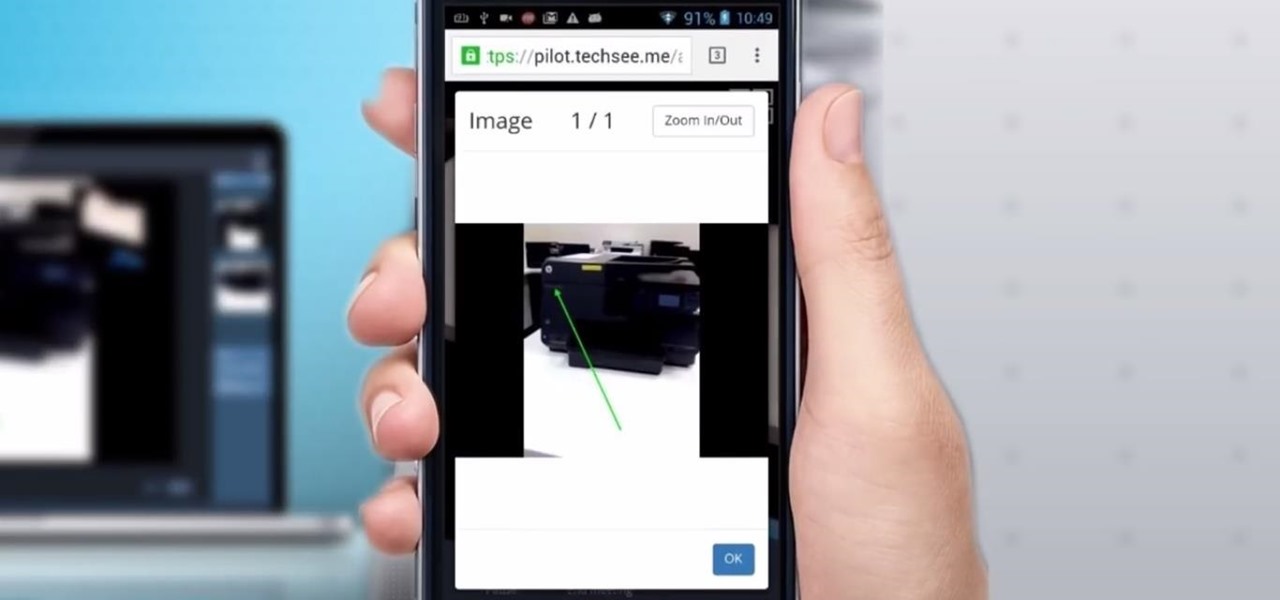
Four augmented reality companies made deals this week to grow their businesses. Two companies, TechSee and Car360, completed funding rounds, while DAQRI signed with a production partner and Decalomania landed a prime spot with a top retailer.

Welcome back, my greenhorn hackers! Throughout this series on Metasploit, and in most of my hacking tutorials here on Null Byte that use Metasploit (there are many; type "metasploit" into the search bar and you will find dozens), I have focused primarily on just two types of modules: exploits and payloads. Remember, Metasploit has six types of modules:

Everyone hates to feel like they've been taken advantage of, especially when buying a used vehicle. The thought comes across every car buyer's mind... "Did I just get taken by that smooth-talking salesman?" When it comes to cars, how do you know if you're really getting a good deal, or if you're being offered a fair price for your car? After all, cars are most peoples second largest investment, so we need to make this decision wisely.
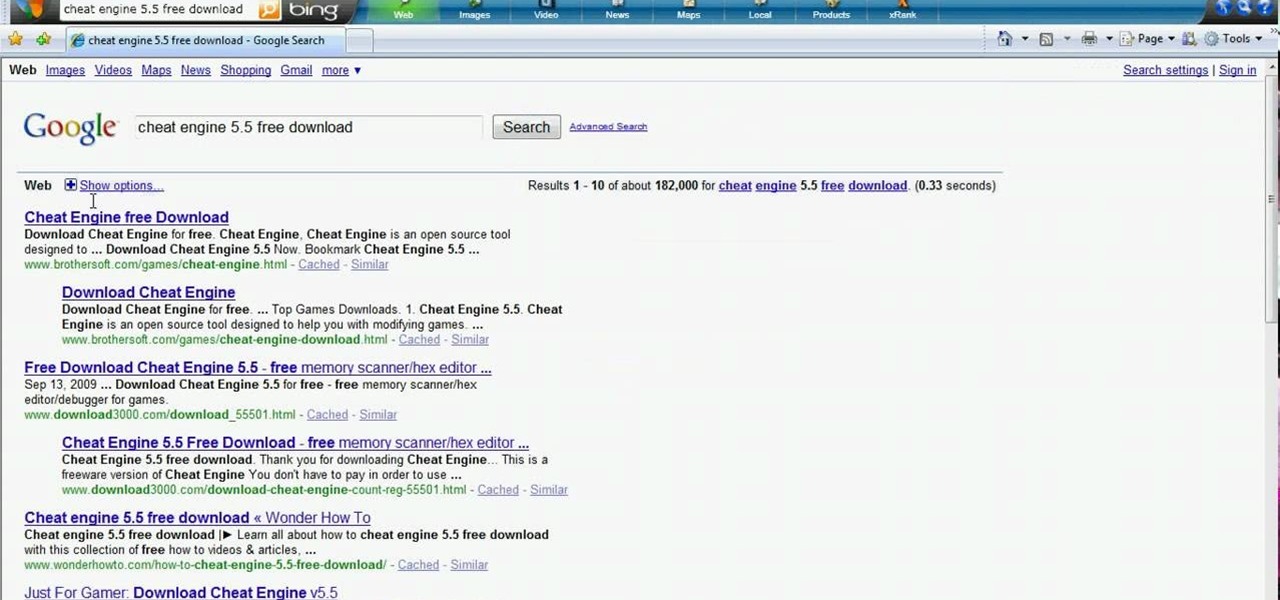
Hacking flash games is the new coolest thing these days... now hackers can be anywhere, ever expanding, all thanks to a little cheating program called Cheat Engine. Check out this video tutorial to learn how to download and install Cheat Engine to hack flash games.

Identifying vulnerable devices and services on a target router can be difficult without leaving logs and other traces of an active attacker on the network. However, there is a way to covertly decrypt and view Wi-Fi activity without ever connecting to the wireless network.

Firewall solutions for macOS aren't impervious to attacks. By taking advantage of web browser dependencies already whitelisted by the firewall, an attacker can exfiltrate data or remotely control a MacBook, iMac, Mac mini, or another computer running macOS (previously known as Mac OS X).

Code execution in Microsoft Word is easier than ever, thanks to recent research done by Etienne Stalmans and Saif El-Sherei. Executing code in MS Word can be complicated, in some cases requiring the use of Macros or memory corruption. Fortunately, Microsoft has a built in a feature that we can abuse to have the same effect. The best part, it does so without raising any User Account Control security warnings. Let's look at how it's done.

One thing that I got more and more excited about as we got closer and closer to the Microsoft Build 2017 developers conference was finally learning about the new Acer Windows Mixed Reality head-mounted displays (HMD). Brandon Bray, Principal Group Program Manager at Microsoft, had teased us a few weeks earlier at the Vision Summit event in Los Angeles, California, and said there would be a lot more information at Build. Fortunately for us, he was right.
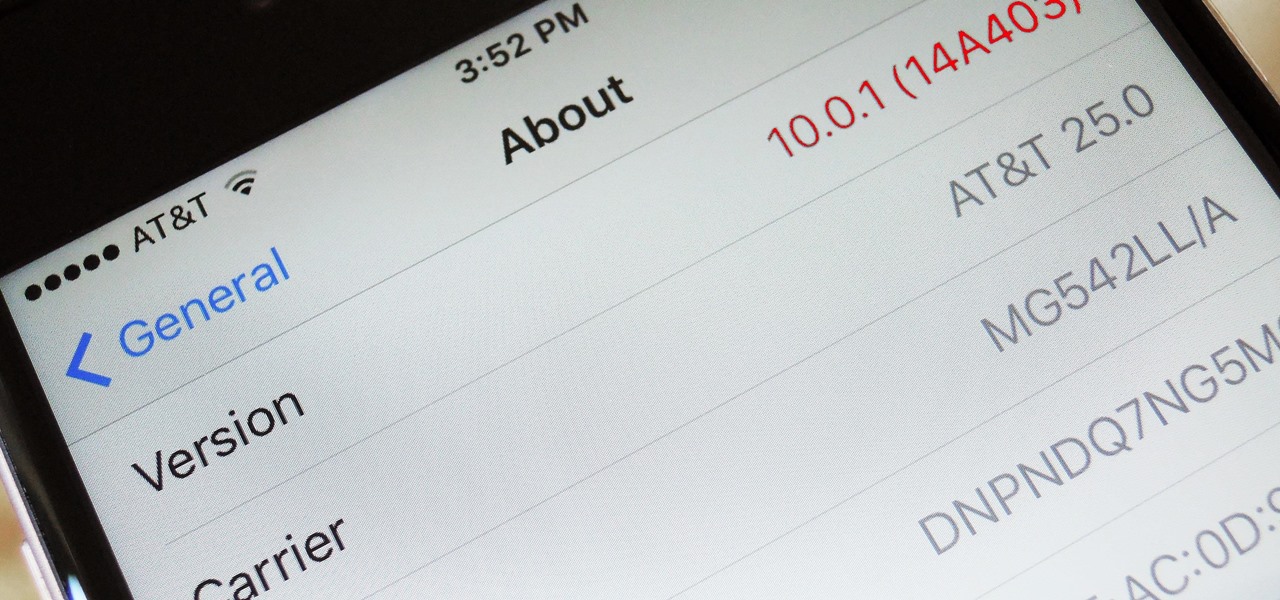
When a new version of iOS comes out, everybody gets caught up in the craze of finding features and playing around with new functionality. But this generally leads to a lack of coverage on the finer aspects of the update—things like bugs, minor tweaks, and pain points that users discover along the way.

Welcome back, my novice hackers! One of the most common questions that Null Byte readers ask is: "How can I evade detection by antivirus software on the target?" I have already talked about how AV software works, but to obtain a deeper understanding, what better way is there than opening up and dissecting some AV software?

I am very new to Null Byte but I find much of its content and community incredibly interesting. I spent quite a bit of time just chronologically going through the posts and I noticed a common theme in many of the beginner posts. Many people seem to want to know the 'secret' or a paragraph on "How to Hack" and become a hacker in a few minutes. I started off this post as a reply to a question from a beginner but thought it might be beneficial to have for those stumbling across this site.

The COVID-19 pandemic forced many businesses into remote work models, whether they were ready or not, making Zoom a household (or home office) name for its video conferencing service.

Microsoft.com is one of the most extensive domains on the internet with thousands of registered subdomains. Windows 10 will ping these subdomains hundreds of times an hour, making it challenging to firewall and monitor all of the requests made by the operating system. An attacker can use these subdomains to serve payloads to evade network firewalls.

Complex shell scripts can be implanted into photo metadata and later used to exploit a MacBook. In addition to obfuscating the true nature of an attack, this technique can be used to evade network firewalls as well as vigilant sysadmins.