How To: Make a white chocolate raspberry cheesecake
The recipe can be found on www.yesdivascancook.com. An eBook containing this and other cheesecake recipes is also offered.

The recipe can be found on www.yesdivascancook.com. An eBook containing this and other cheesecake recipes is also offered.

In five short years, three generations of ultra-low-cost Raspberry Pi devices have challenged the boundaries of what a person can do with a $35 computer — especially with Kali Linux.

Just because you want to look like a pin up doesn't mean you have to go the full blown route of Dita von Teese. In fact, the pin up look presented in this video is one you can wear on a daily basis.

When we think of jam, we usually think of luscious, thick strawberry or raspberry preserves, made rich and saccharine with loads of molasses or table sugar. But did you know you can actually add other interesting ingredients to your jams, including herbs and spices?

Cooks and pastry chefs like to use a lot of jargon in the naming of their cooking ingredients and finished foodstuffs to make their work sound fancier. Tuna tartare, for example, is really nothing more than finely choppsed tuna flavored with seasonings and sauces.

This makeup style is fun and vibrant, without being too over-the-top. This "fresh berries" makeup look plays around with layering colors, which create a unique effect when you turn your hair, making the colors gleam. This berry fresh look is great for spring or summertime (probably because it's reminiscent of fresh and delicious looking berries).

The Watch Dogs video game series came out in 2014, enamoring audiences with the idea of a seemingly magical smartphone that could change traffic signals, hack web cameras, and even remotely control forklifts. This may sound like science fiction, but The Sonic uses a customized flavor of Kali Linux to allow you to unleash the power of Kali from any smartphone — all without the need to create a hotspot to control it.

Oh, Mario. The guy that's been a part of our lives since as long as we can all remember. Well, Adam Ringwood and his friends did something pretty cool with one of Mario's most exciting games at the HackIllinois event in February 2016—they hacked a Chevrolet Volt's steering wheel into one big Nintendo 64 controller for Mario Kart.

Mirror, mirror on the wall, who's the smartest of them all? Since Max Braun's Medium post went viral back in January of 2016, smart mirrors have been appearing on tech blogs in all shapes and sizes. Some are technically sound, some incredibly easy, but all are visually compelling. However, we've never seen one with a fully functional operating system and gesture support—until now.

This tutorial is one technique to use the full functionality of your Pi. The small size makes it ideal for inside hacks, but still has the capabilities of a average desktop or computer. I should mention that a tutorial that OTW has done, but I'm gonna take it a step further. OTW made a brilliant article, but only touched on the surface of the possibilities. I hope this article will both show you many the possibilities and also allow you to start causing havoc, but I'm planning on making this ...

If you've been watching the latest USA TV Series Mr Robot, you will have seen the Raspberry Pi used by Fsoeciety to control the HVAC system. OTW covers this very well here with his take on setup they may of used.
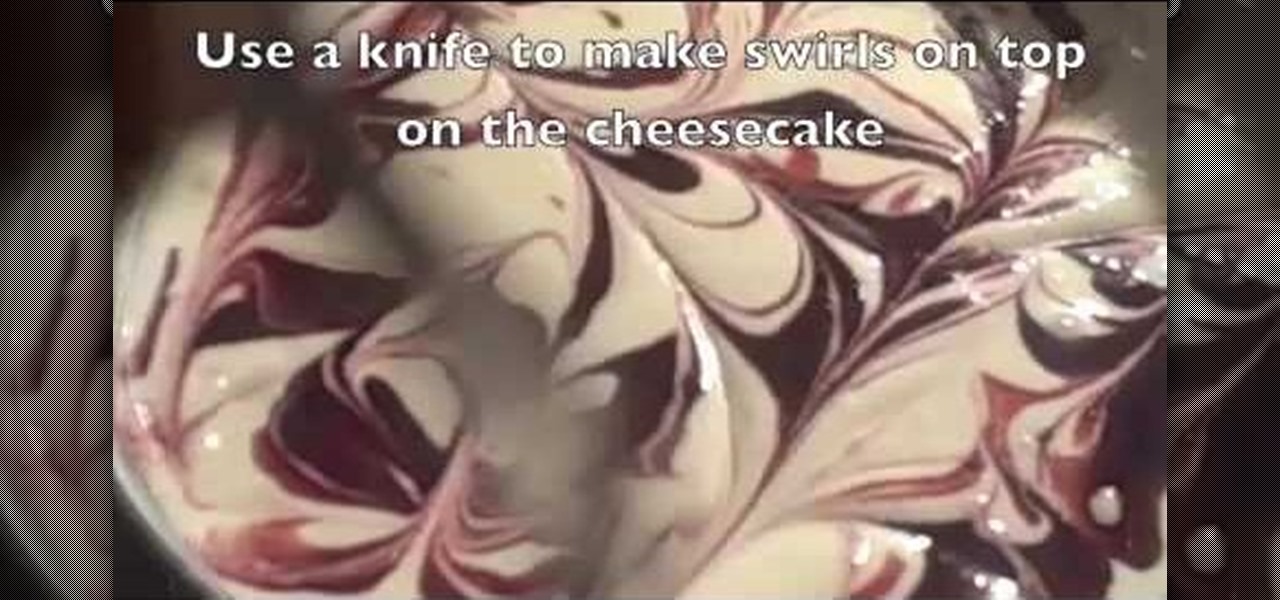
Long time reader, first time 'How To' poster. This tutorial has been highly requested. Here are the steps to perform a Pixie Dust attack to crack a WiFi password that has WPS enabled.

A couple months ago, I attended a Pokémon-themed party. Everyone dressed as their favorite Pokémon or trainer, Poké balls flew around the backyard, and more importantly, there was a lot of Poké booze. My friend who created the colorful drinks you see below informed me that they were infused with Skittles. This, my humble readers, was a defining moment in my life.

You are going to use a food processor but if you don't have one chopping is fine. Into the food processor you are first going to put three Roma tomatoes that have been sliced in half. Next you will cut out the core of the green pepper and put that into the processor. Place a onion into the mixture and add about fifteen sprigs of cilantro. Put one jalapeno and a handful of roasted corn with the juices of one lime into your food processor along with the rest. Now a special ingredient is a large...

Making a fruit salad is easy with just a few simple steps. First, peel, core and cut some pineapple. Next, peel and cut up some mango. After that, remove the pulp and juice the orange and grapefruit. Add all the fruit to the serving dish. Place the raspberries around the edge of the dish for appearance. Now add the red currants and chopped basil. Drizzle with lemon oil and sprinkle with sugar to complete the dish.

Discover how Almond Oil can be combined with Maltodextrin to become a crunchy, melty, delicious desert topping. Then combine it with gelato and spun sugar. What more could you want out of desert? This is a lesson in Molecular Gastronomy. Learn how to make gelato with an almond crunch and spun sugar.

With Virtual Network Computing, you don't need to carry a spare keyboard, mouse, or monitor to use your headless computer's full graphical user interface (GUI). Instead, you can connect remotely to it through any available computer or smartphone.

Sangria... the elixir of summer. When properly prepared, there are few things more refreshing and magical. If you're looking for a way to mix things up and "get out of the bottle," try one of these lovely libations before the warm weather ends: peach-mango sangria, pineapple-basil sangria, watermelon-raspberry sangria, or blueberry-plum sangria.

When it comes to dressing up your face for the holidays, your LBD of makeup looks is without a doubt the classic neutral eye and red lip combo. Beautiful since the days of Marilyn Monroe, this look is timelessly feminine and sultry.

In this tutorial, we learn how to blend greens into a nutritious smoothie. The key to making a smoothie with a lot of greens is to balance it out with fruit to mask the taste of all the vegetables. A great recipe will have things in it including: spinach, broccoli, cucumbers, kale, bananas, apples, blueberries, raspberries, strawberries, and more. If there is a whole fruit or vegetable near you, try using it in your smoothie as you make it! This can make you feel much more healthier and live ...

If you've paid attention to the red carpets or fashion news at all recently, then you know that the gorgeous Rachel Bilson made waves - quite literally - recently when she wore a tight finger waves hairstyle to the red carpet premiere of "Sherlock Holmes."

Kerri Newell introduces Chocolatier Paul Young who shows us how to make chocolate truffles. He explains that truffles are filled with ganache and chocolatiers sometimes call truffles ganaches, which is the smooth, creamy filling. These are usually for special occasions.

This video tells us the method to decorate an angel food cake with cranberry garnish. Cut the cake into half horizontally by using a serrated knife. Remove the upper portion of the cake. Mix together half cup of raspberry jam and two teaspoons of orange peel. This mixture is spooned over the top of the lower portion of the cake. Put the top of the cake back on the lower portion. Take 8 ounce of whip topping and apply it to the outer portion of the cake. Now, take frozen cranberries and thaw t...

Karen Knowler, The Raw Food Coach, demonstrates how to make a wonderfully filling raw muesli. Start with a cereal bowl. Coarsely chop and add two or three varieties of nuts of your choosing. In this instance, Karen adds hazelnuts, almonds and brazil nuts. She then adds cut dried apricots, dates and raisins. Blend together with your hands. Now, add fresh fruit of choice. Bananas, blueberries, raspberries and apples are good picks. Stir to blend and finally, pour almond milk to taste over all. ...

During the holidays, nothing beats the satisfying taste of Brie cheese encrusted in puff pastry. Holiday Kitchen shows you how it's done with this Brie en Croûte recipe that's a must-serve appetizing classic any time of year. To spice up the classic French treat, they've added cranberries, apricots and almonds, dressing it up especially for the holidays

With a cheap computer, smaller than the Raspberry Pi, an attacker can create a remote hacking device. The device can be attached to a target router without anyone's knowledge and enable the hacker to perform a variety of network-based attacks from anywhere in the world.
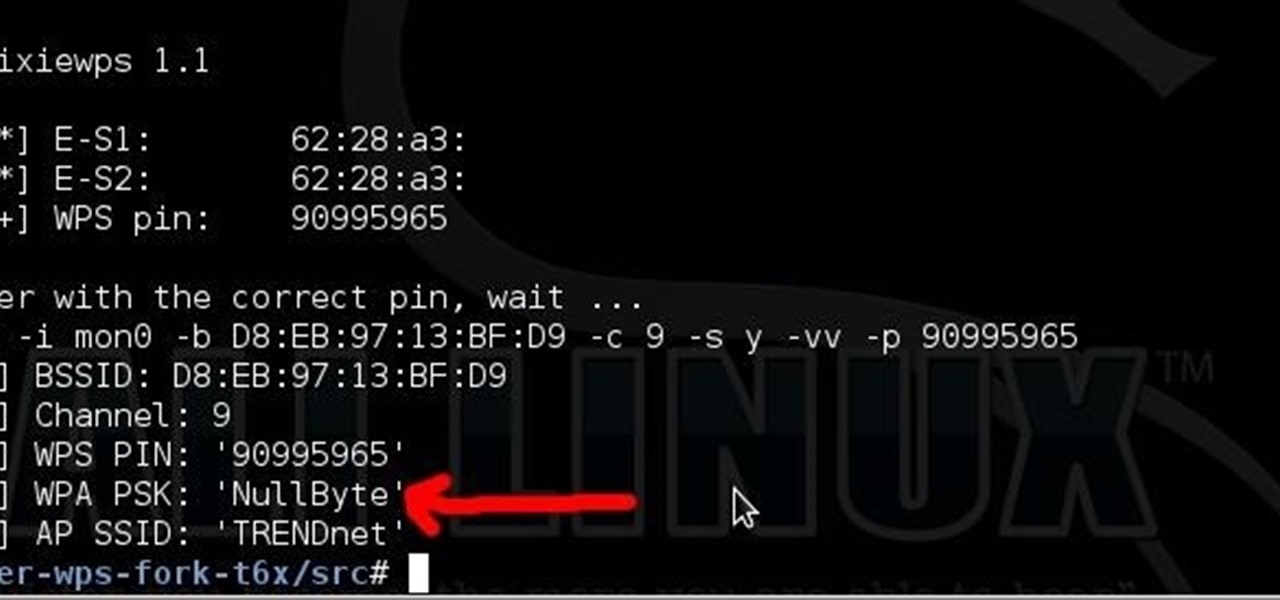
When setting up a Raspberry Pi, it's easy to overlook changing the default password. Like many IoT devices, the Raspberry Pi's default Raspbian operating system installs with a widely-known default password, leaving the device vulnerable to remote access. Using a tool called rpi-hunter, hackers can discover, access, and drop custom payloads on any weak Pi connected to the same network.

Hackers can be notoriously difficult to buy gifts for, so we've curated a list of the top 20 most popular items Null Byte readers are buying during their ethical-hacking studies. Whether you're buying a gift for a friend or have been dying to share this list with someone shopping for you, we've got you covered with our 2017 selection of hacker holiday gifts — just in time for Christmas.

We're wild for whipped cream in our coffee, atop our brownies, and in-between wafer cookies, so we always have some in our fridge. To be specific, we always have homemade whipped cream in our fridge, because the taste is just so much better than the pre-made stuff.
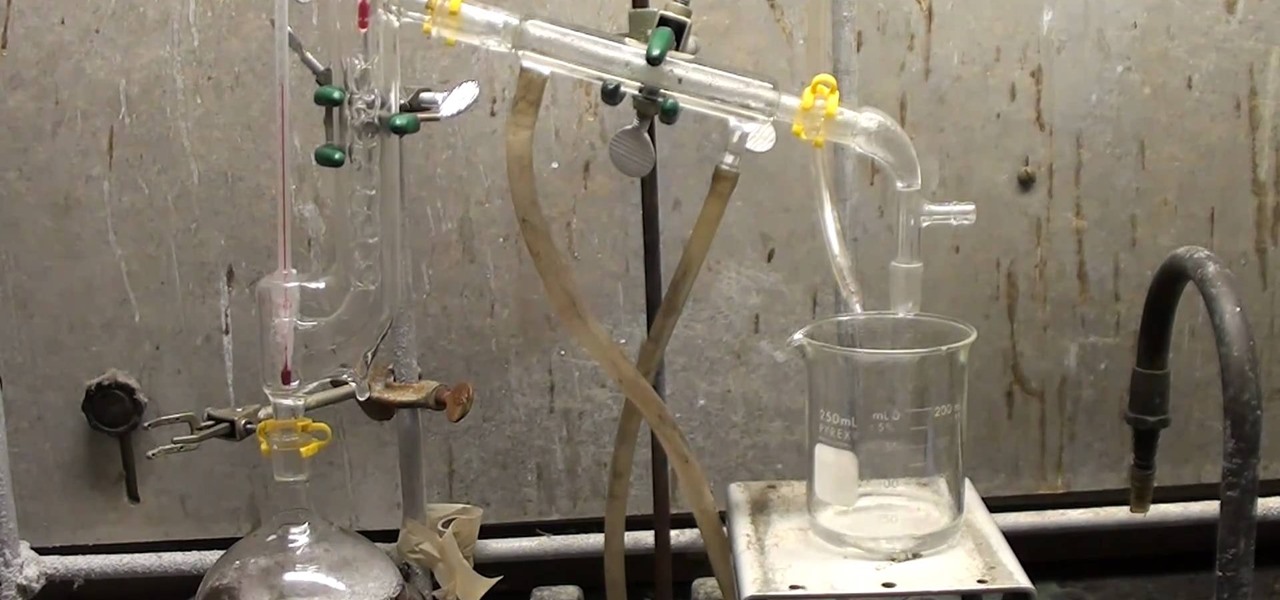
Hydrazine sulfate has many uses, but most notably, it's been used under the trade name of Sehydrin, a treatment for anorexia, cachexia and some even think cancer. But for we DIY chemists, it's useful for something entirely different— as a substitute for the more dangerous pure liquid hydrazine in chemical reactions. NurdRage shows you how to make it via some hypochlorite and the Ketazine process.

Surveying a target's Wi-Fi infrastructure is the first step to understanding the wireless attack surface you have to work with.

If you've ever turned on an episode of Iron Chef or Top Chef, chances are you've seen a contestant in gloves and goggles, yielding a canister that looks far more fit for a chemistry lab than for a kitchen. Wonder what's in the canister? Liquid nitrogen, the go-to tool/ingredient of molecular gastronomy, and one of the trendiest items in many gourmet chefs' kitchens.

Tequila, triple sec, sour mix, and Chambord raspberry liqueur make up the raspberry margarita cocktail. Follow along with bartender Claudia as she gives step by step directions for how to mix up this fruity specialty drink. Watch this video beverage making tutorial and learn how to mix the raspberry margarita cocktail.

Surveillance is always a useful tool in a hacker's arsenal, whether deployed offensively or defensively. Watching targets yourself isn't always practical, and traditional surveillance camera systems can be costly, lacking in capabilities, or both. Today, we will use motionEyeOS running on a Raspberry Pi Zero to create a small, concealable Wi-Fi connected spy camera that is both affordable and easily concealed.

In our first part on software-defined radio and signals intelligence, we learned how to set up a radio listening station to find and decode hidden radio signals — just like the hackers who triggered the emergency siren system in Dallas, Texas, probably did. Now that we can hear in the radio spectrum, it's time to explore the possibilities of broadcasting in a radio-connected world.

Most of you probably heard about Rasberry Pi and if you haven't; what is wrong with you? But nothing less a Rasberry Pi is a computer a very small computer. Despite these size limitations, the Rasberry Pi is to not be underestimated. Not only can it do anything like a normal laptop or desktop, but, in my opinion on of the coolest features is that it boots off a Micro SD card. It can do anything that you want, but it's built to be played with. A hacker heaven.

Welcome, my hacker novitiates! As part of my series on hacking Wi-Fi, I want to demonstrate another excellent piece of hacking software for cracking WPA2-PSK passwords. In my last post, we cracked WPA2 using aircrack-ng. In this tutorial, we'll use a piece of software developed by wireless security researcher Joshua Wright called cowpatty (often stylized as coWPAtty). This app simplifies and speeds up the dictionary/hybrid attack against WPA2 passwords, so let's get to it!

Leave it to some lazy college kids to attempt to figure out a way to brew a pot of coffee without leaving the couch.

To hack a Wi-Fi network using Kali Linux, you need your wireless card to support monitor mode and packet injection. Not all wireless cards can do this, so I've rounded up this list of 2019's best wireless network adapters for hacking on Kali Linux to get you started hacking both WEP and WPA Wi-Fi networks.

The USB Rubber Ducky comes with two software components, the payload script to be deployed and the firmware which controls how the Ducky behaves and what kind of device it pretends to be. This firmware can be reflashed to allow for custom Ducky behaviors, such as mounting USB mass storage to copy files from any system the Duck is plugged into.