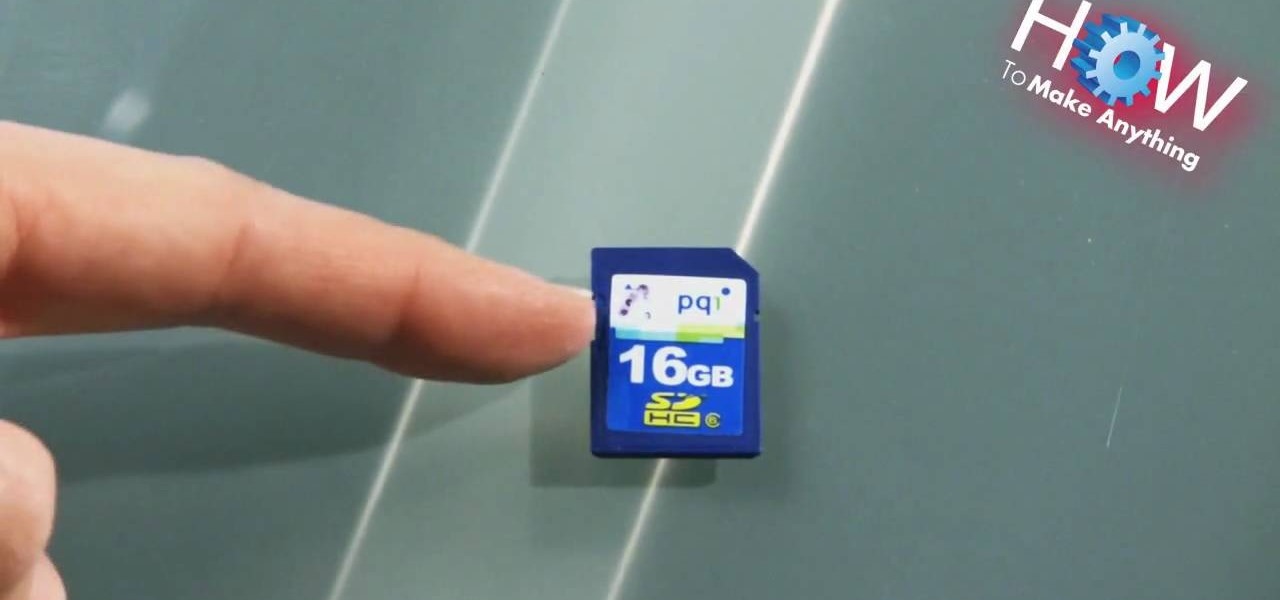
In this video tutorial, viewers learn how to repair the write protect on an SD card. An SD card is a non-volatile memory card format that is used in portable devices. If the write protect on a SD card is broken, the user cannot record any files onto the card. To fix this, viewers will need a small piece of scotch tape. Put the tape on the notch of the SD card. Do not cover the metal tabs at the back. This video will benefit those viewers who have a SD card and would like to repair the write p...

This Spirituality video clip will show you how to wrap a Wiccan cinnamon stick bundle for protection. You need some cinnamon sticks, scissors and ribbon. Cut a very long piece of ribbon, lay it down on a table, place the cinnamon sticks on the ribbon, tie a basic knot flip it over and tie another knot. With one end of the ribbon, go over and in between the sticks and with the other end, go under and in between the sticks. Now put one more knot in between the sticks. One more time go under or ...

Dave Andrews from HelpVids is going to teach you in this video how to configure the Windows XP firewall. To do that, you need to follow these steps: 1. Go to Control Panel and make sure that you are in the classic view.

Learn how to cut tile with this DIY video tutorial. If you need to make angular and circular cuts, use an angle grinder and fit a diamond disk. You'll need to fit a continuous diamond disk, not a segmented one, because a segmented disk will chip the tiles. And if you're using an angle grinder, don't forget your personal protection equipment, ear muffs, dust mask, and eye protection.

1. First of all you need go to the 'view' button at the top bar menu. From the drop down click on 'view options'. Then click a 'check mark' against the 'kind' and then click 'ok'.

This video tutorial program is designed to promote ground crew safety when working under and around helicopters during external load operations. This is not a safety-training and is only intended to be used with the participation of a ground crew safety officer, trainer or other qualified personnel. All training and refresher courses must be done in accordance with federal and provincial regulations and the Canada Labour Code.

What's the easiest way to keep track of your website passwords? Maybe in a password-protected document on your computer? Makes sense.

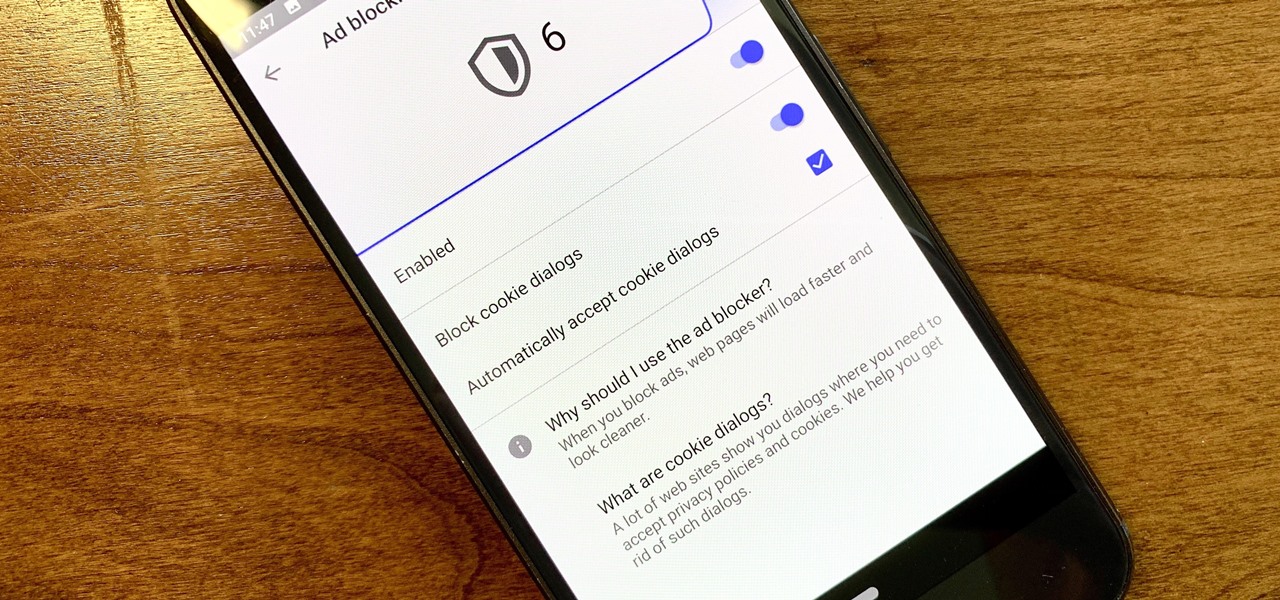
Ever since the GDPR was implemented, it seems every website on the internet needs to inform you of how its privacy policies have changed. If your web browsing experience has been marred by a constant barrage of these cookie pop-ups and privacy dialogs, you should know there's an easy way to block these web annoyances so you never have to tap another checkbox or accept button again.

The Galaxy S9 is now in the hands of millons of excited users. Getting a new phone is always fun, but it's important to think about protecting your device. Perhaps the most popular cases for the Galaxy S9 are the official OEM options from Samsung. There are a plethora of cases, whatever your preference and needs may be. Let's take a look at each case individually, along with the pros and cons.

Many people think antivirus apps are useless — why pay a subscription fee when most malware can be avoided with common sense? But the thing is, there were an estimated 3.5 million malicious Android apps discovered last year, with many of them making their way onto the Play Store. As this number continues to rise, can you truly depend on common sense to protect you?

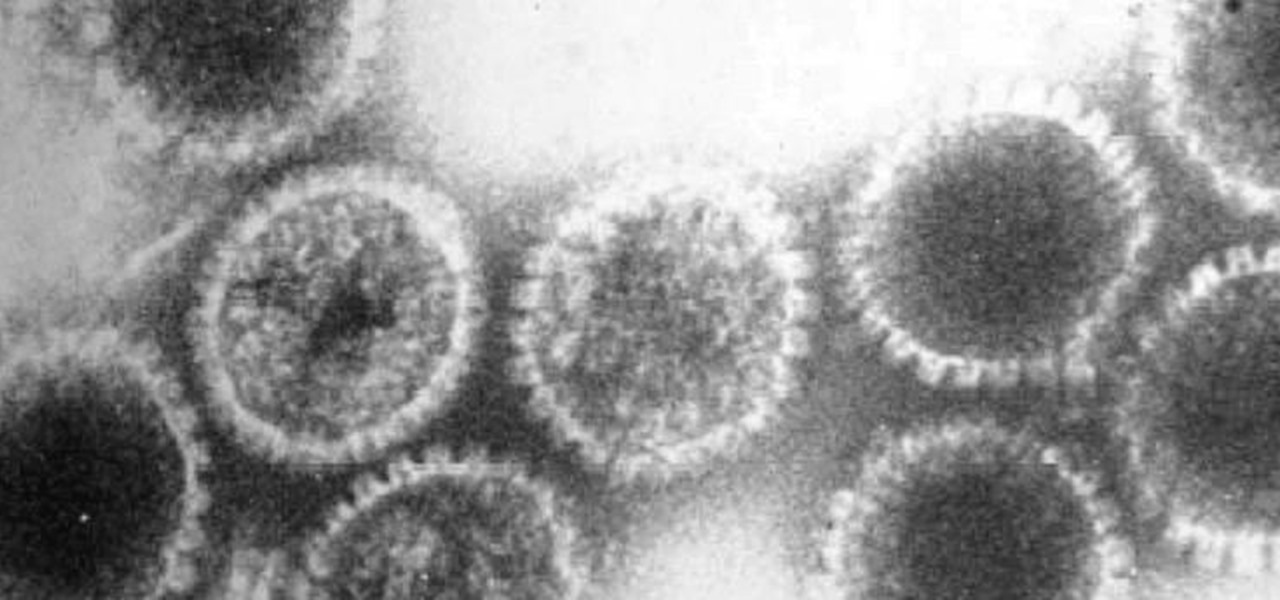
How can a drug used to treat cancer be effective against viruses, too? The answer lies in the drug's shared target — specifically, cellular components that control the activity of genes. A new research study showed that one such type of drug, histone methyltransferase inhibitors used in cancer clinical trials, has activity against herpes simplex virus, too.

One of the joys of having a large yard is the riding lawnmower! It's not that intimidating. This video shows you a few basic ways to use a riding lawnmower. Always make sure you wear close toed shoes and eye protection!

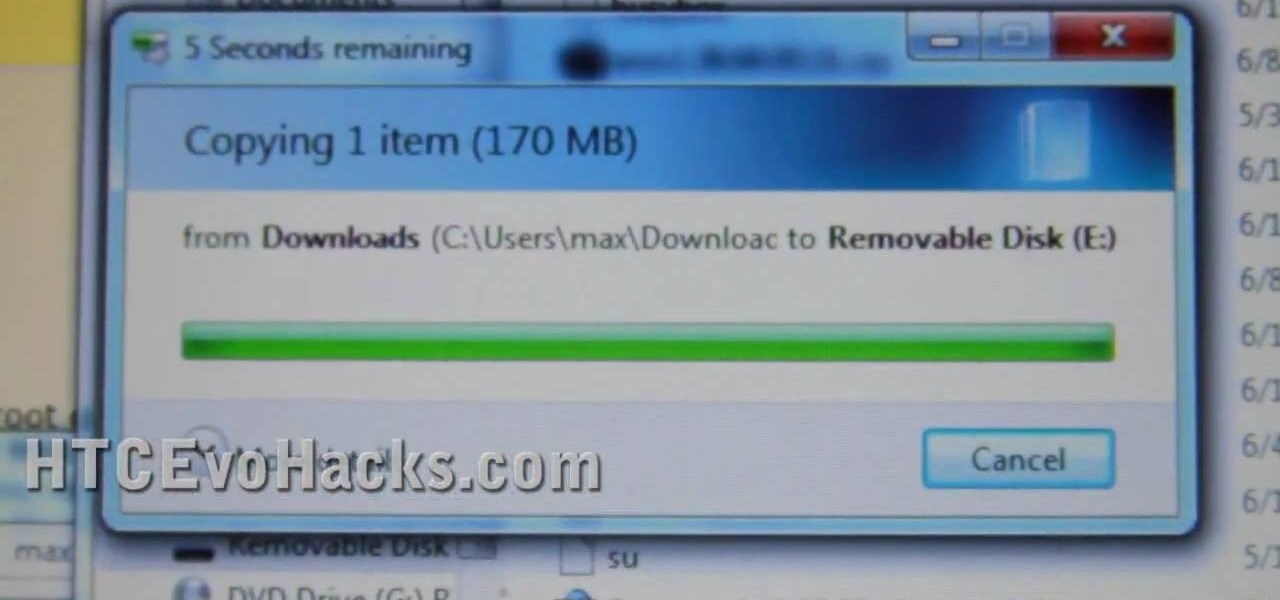
In this clip, you'll learn how to unlock NAND and install a recovery menu on a rooted HTC Evo 4G. Whether you're the proud owner of an HTC Evo 4G Google Android smartphone or are merely considering picking one up, you're sure to be well served by this video tutorial. For more information, including a complete demonstration and detailed, step-by-step instructions, take a look.

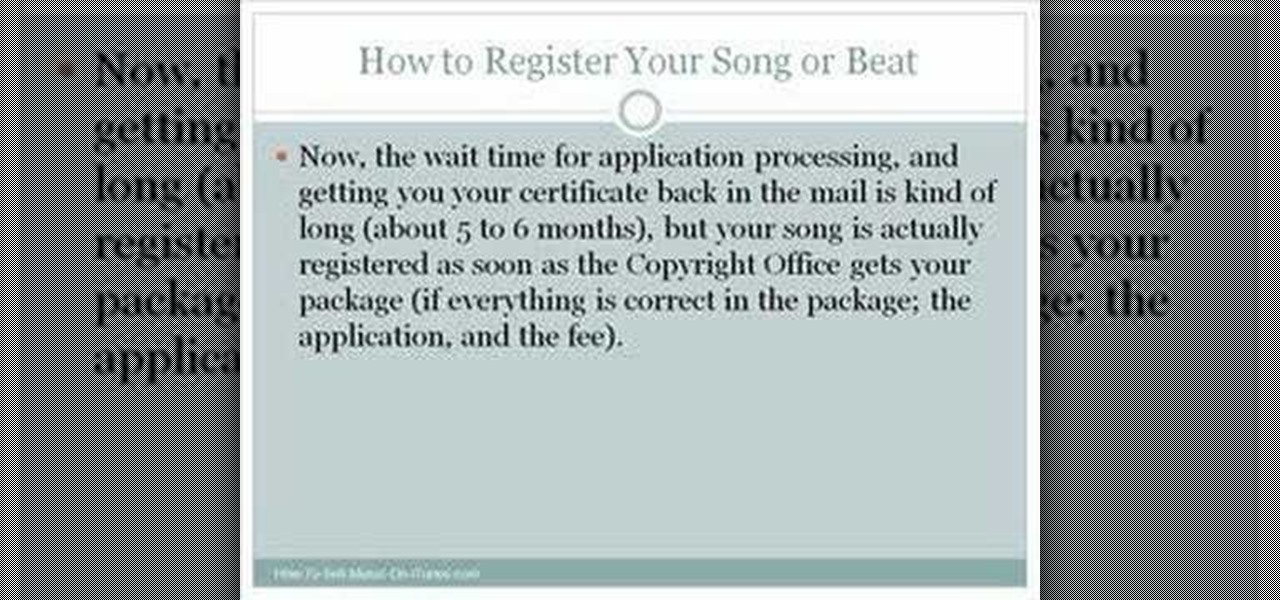
While big parts of copyright protection are applied automatically to creative works like songs and beats (hence the need for orginizations like the Creative Commons), registering your work with Copyright Office is useful to the extent that it can allow you to seek greater damages in the event of an infringement. For more information, including how to register your own songs with the US Copyright Office, watch this free video tutorial.

Cyber Security is a horrible computer virus. It mimics a virus protection program and invades your system, making it nearly impossible to remove. In this tutorial, learn how to remove this annoying trojan horse from your PC and save your computer.

This video shows you how to remove the Digital Rights Management(DRM) protection from iTunes music. DRM is a way for Apple ITunes to control your music and where you save it. Hack the iTunes so that it does not interfere with you like this.

They're finally here. Apple announced three new iPhone models at their "Gather Round" event in Cupertino, and they're all absolutely gorgeous phones. With bezel-less screens and polished titanium edges, the iPhone XS, XS Max, and XR are truly marvels of engineering — but perhaps the most impressive design feat Apple pulled off is the fact that two of these models are rated IP68 under the IEC standard 60529.

Accused of violating whistleblower and age discrimination laws by its security director, Magic Leap has taken an internal situation to the US District Court to clear its name of the allegations.

Unlike many browsers, Firefox gives a lot of control to the user. By default, Firefox does a great job of balancing security and performance. However, within the app's settings, you can modify options to shift this balance in one direction or another. For those looking to shift it toward security, here are few suggestions.

It's easy to have your password stolen. Important people like executives, government workers, journalists, and activists face sophisticated phishing attacks to compromise their online accounts, often targeting Google account credentials. To reduce this risk, Google created the Advanced Protection Program, which uses U2F security keys to control account access and make stolen passwords worthless.

The Play Store hasn't been the most secure place for apps lately. A quick Google search for "Play Store malware" will give you a taste of some of the malicious apps that snuck their way onto Android's official app store. Google is aware of the problem and they're tying to fix it, but their new Play Protect program doesn't have a great track record, so you might want to look elsewhere.

You don't have to spend hours weeding your garden - just use a weed whacker! Always make sure you wear close toed shoes and eye protection when using a weed whacker. And make sure to keep your hands away from the strings!

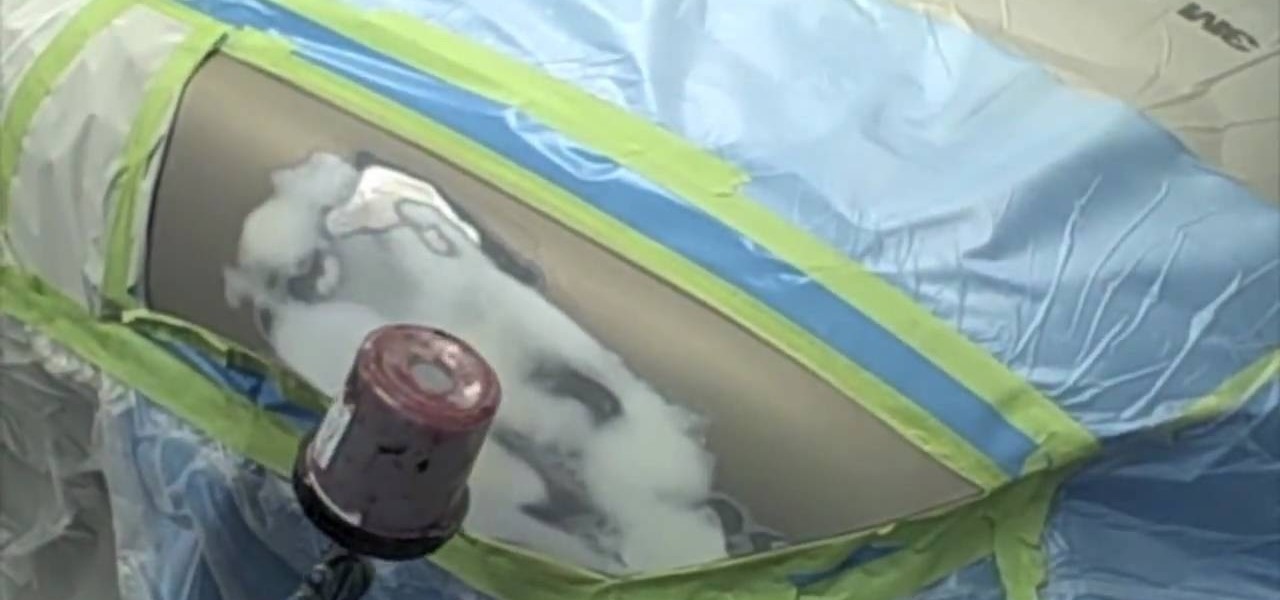
In this video, you are shown how to apply epoxy to your car area after it's been repaired. Epoxy is a great primer because of its advantages in adhesion and corrosion protection. You can apply one or two coats if you so desire. Watch this video and you'll learn all about the advantages of epoxy primer.

Oh no! You're lost in the wilderness without an adequate survival shelter! Protect yourself from inclement weather by using soil, clay, mud and other materials found in nature to build your own mud hut for protection from the elements.

Fumbling the ball is the most embarrassing thing that a running back can do on the football field. This video features NFL skills instructors demonstrating one good drill for teaching ball protection skills: having the running back player run through a gauntlet of other players who will all try to strip the ball from them.

In this garden video, you'll learn how to get ready for the winter by laying down mulch for new plants. Mulching new plantings for the winter is very important for protection during the snowy months, and it improves the look of the beds, keeps some weed down, and keeps the moisture in the soil (although too much keeps the moisture out).

This menstrual hygiene video offers information on the insertion and removel of wearing a menstrual cup, the latest method in menstrual/period protection. Menstrual cups provide an alternative to potentially unhealthy and wasteful methods of feminine hygiene such as the tampon or sanitary napkin. Follow along with this feminine hygiene video and learn how to properly insert and remove a menstrual cup.

This is an instructional video featuring Doug Prime, founder of the Future Engineers Center at the University of Massachusetts Lowell. Aviation snips cut small metal like aluminum, but not big pieces like nails. Nails and large pieces of metal should be cut with bolt cutters. Use eye protection during all cutting of metal. This video shows the cutting of pipe straps.

The most important items in a tool kit, are the protection and safety equipment, like a breathing mask, ear muffs, and eye goggles. Other than that, tools vary on your needs. Some basics are a handsaw, a hacksaw, a level, a hammer, screwdrivers, a measuring tape, a shifting wrench, a chisel, pliers, a combination square, a utility knife, and a clamp. Watch this video home improvement tutorial and learn how to select tools for a basic tool kit.

Make your iPod do so much more than carry tunes. An individual iPod can keep your iPod from getting mixed up with someone else's. Cases and skins can offer protection from damage. Watch this video iPod tutorial and learn how to customize your iPod.

Between "genuine danger" and "raving safety paranoia," there must be some sensible middle ground for dry ice.

After you've taken your iPod Nano apart and fixed it, you might want to put it back together. Check this video out to see how to assemble the iPod Nano Generation 2 with narration for each step.

I explain how to view and control your computer from your iPhone/iPod Touch. This works over Edge and Wifi connection, but obviously the better your connection the faster it will go. If you are having problems connecting try going to control panel then security center then turn your firewall off. Also try turning off anything like virus protection.

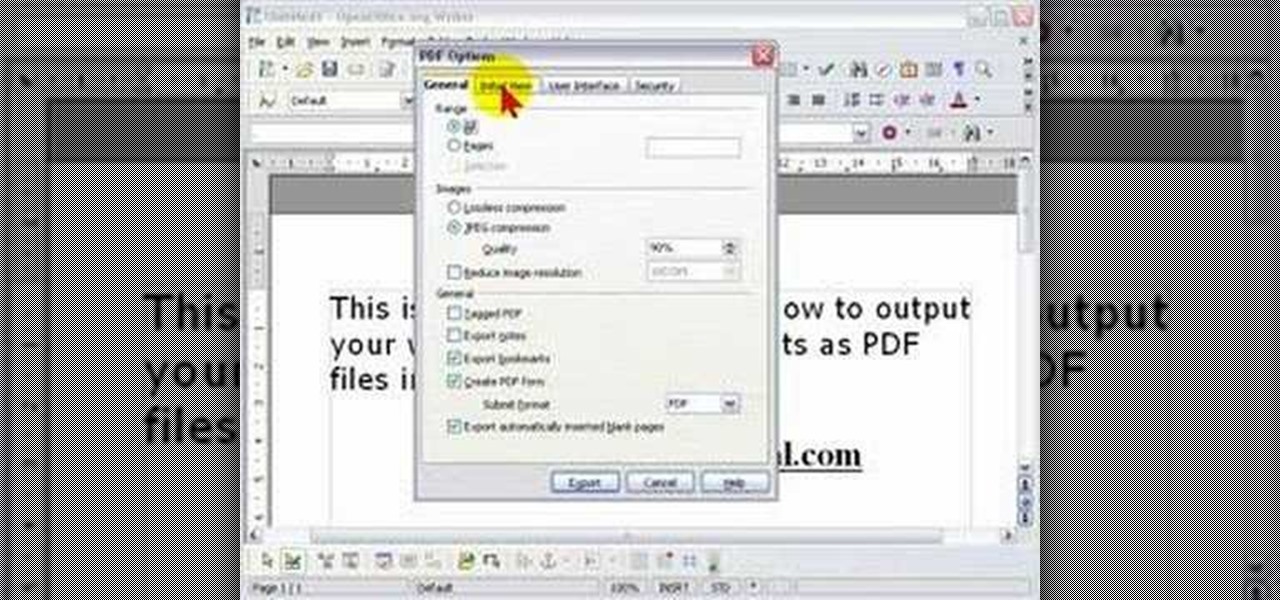
In order to protect your word processed documents, it is a good idea to export them for distribution as PDF files, which allows you to encrypt, and add password protection to your work.

With all the documents ready, we need to fill our wallet with money for the travel. This video discusses various ways of filling the pocket. That is how to prepare the money for international travel. Over the years credit cards have been widely used by many travelers, which is safer than carrying cash. In this case we need to contact the credit card provider well in advance and notify them about the travel. Also we need to learn about the various fees applicable to international purchases. Th...

If you use Office 2008 for Mac and all its applications (Word, PowerPoint, Entourage, Excel), than you need to know about the predefined workflows available using the Script menu that uses Automator to help perform mind-numbing tasks. The Microsoft Office for Mac team shows you just how to save time by using predefined workflows in this how-to video.

When Google introduced the Pixel 3 on October 9th, one of new additions they briefly mentioned was the Titan M security chip. While they did talk about how it will improve overall security, they didn't expand on the number of changes it brings to the Pixel 3's security. Well, they finally shared more, and it's a pretty big deal.

Smartphones are still "phones," which means communicating with others is usually a primary use. Ranging from a simple "hi" to a more personal conversation and even sharing passwords, our messages should remain private so that only the intended recipient sees their content. While many apps tout end-to-end encryption, not all apps prioritize security and privacy.

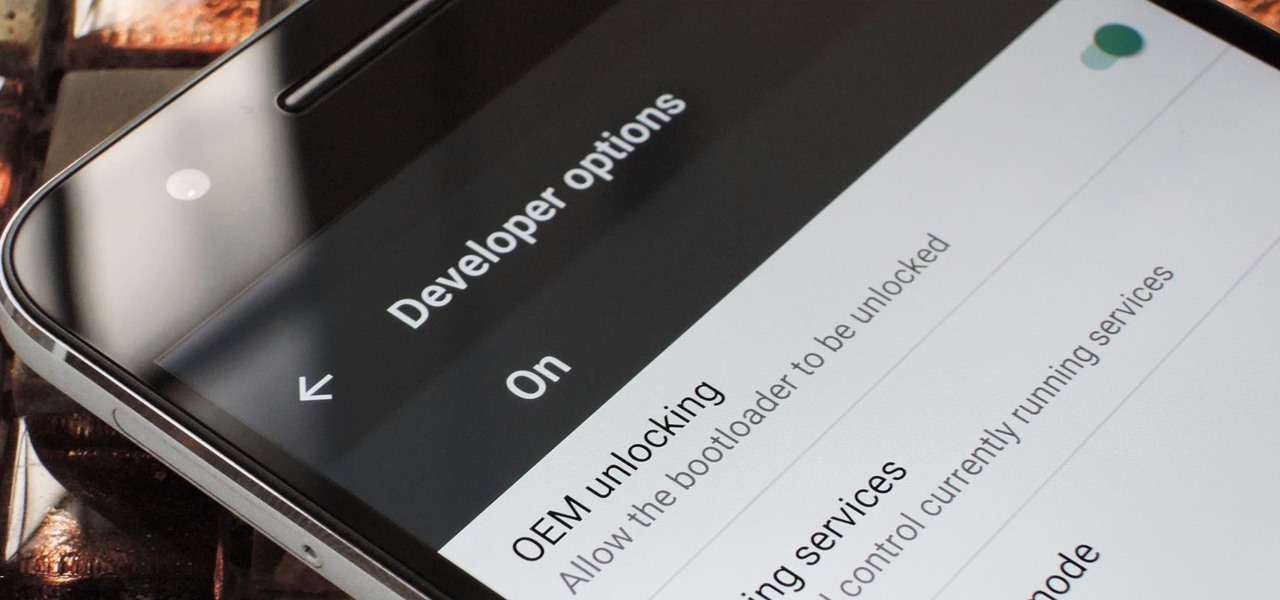
If you've ever rooted an Android device in the past or installed a custom recovery, you're surely familiar with the term "unlocked bootloader." But if all of this sounds like gibberish to you, some major changes in Android have made it to where you should definitely get familiar with the concepts.

Samy Kamkar, the security researcher known for the MySpace Worm and his combination lock cracking skills (using an online calculator), is back—and this time, he's after your credit cards!