A below elbow arm amputee shows how to open bottles one handed, without a prosthetic device. This technique is also great for people with arthritis pain, cerebral palsy, weak joints, stroke, and people who want to be ready for the worst-case-scenario that they suddenly have only one free hand and have to dismantle a bomb that is hidden inside a bottle! This is a great tutorial for handicapped, disabled or individuals that have lost a limb to amputation.

The oyster stitch is an isolated stitch. It is a combination stitch using the twisted detached chain stitch which is "surrounded" by an "open" chain stitch, or even a fly stitch. The oyster stitch makes a filled oval shape, suitable for flower petals or individual buds and accents. Watch this video from Needle 'n Thread to see how it's done.

In Jiu Jitsu the standard goose neck wrist lock may not work of very stong individuals. That means that your level of force must go up in order to deal with the increased resistance.

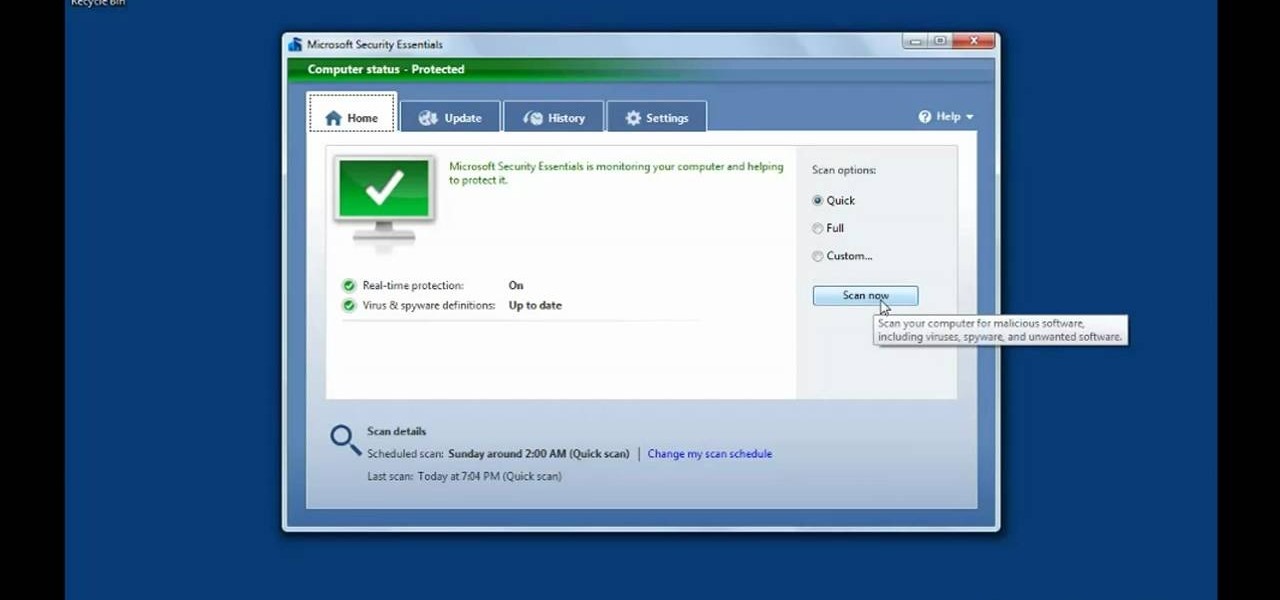
This video talks about protected mode for internet explorer 7 and Windows Vista. The person tells you that protected mode helps protect your computer from types of spyware. It is not the best solution and they tell you one should not rely on this alone. By default protected mode is on. You want to make sure it hasn't accidentally been disabled. To check your settings, double click on the area on the bottom of the screen that says protected mode. The security tab will pop open. Look to see if ...

In the Colonist Mission of Safe Haven on Starcraft 2: Wings of Liberty, you'll have two choices, either to "Protect the Colony" or "Purify the Colony". This video will show you how to "Protect the Colony," because you want to make sure the Doc is pleased. Watch the full NextGenTactics campaign walkthrough to see all the action.
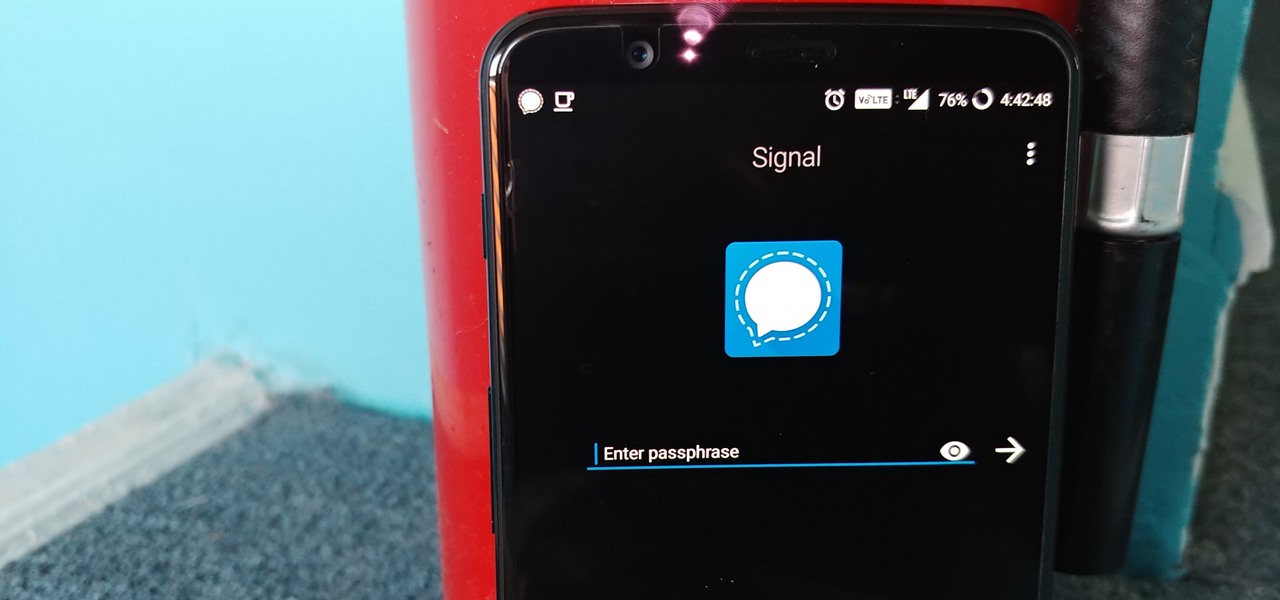
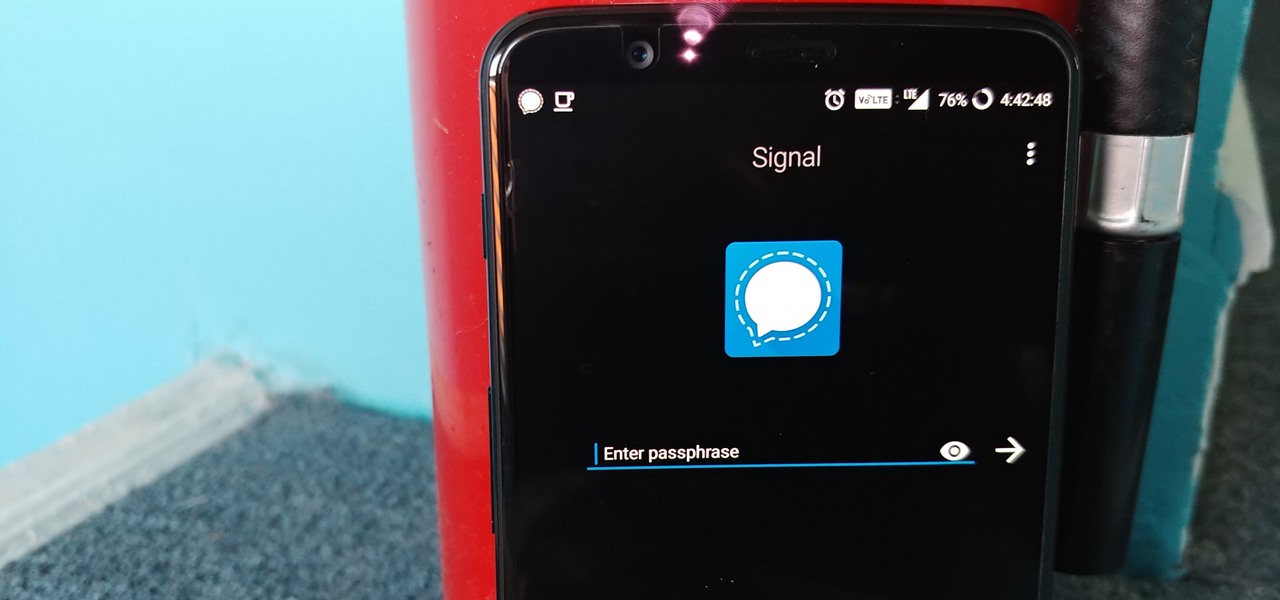
Messaging apps can be a double-edged sword. Not only do they let you interact with other people, but they also let you go back and reminisce on past exchanges. However, that same archive can be used against you in certain situations. Luckily, Signal can be manipulated to remove any record of past messages.

Due to the overnight success of smartphones, millions of people are connecting with others. Currently, over 15 million text messages are sent every minute worldwide. Most of this communication is happening in the open where any hacker can intercept and share in the discussion unbeknownst to the participants. However, we don't need to communicate insecurely.

Just like in the Spy Kids 3D movie, US soldiers may soon upgrade their mission planning from 2D to 3D. Welcome to the wonderful world of augmented reality, US Army.

Thanks to a couple of photoshopped images that made rounds across Twitter last year, iPhone users were duped into thinking that iOS 8 included a security feature that would lock individual apps. Of course, none of it ended up being true, but we covered other features and apps that could accomplish roughly the same thing.

Back in iOS 6, deleting individual text messages in a conversation was just a matter of tapping the edit button on the right-hand corner of the thread, selecting which texts to delete, and then pressing delete.

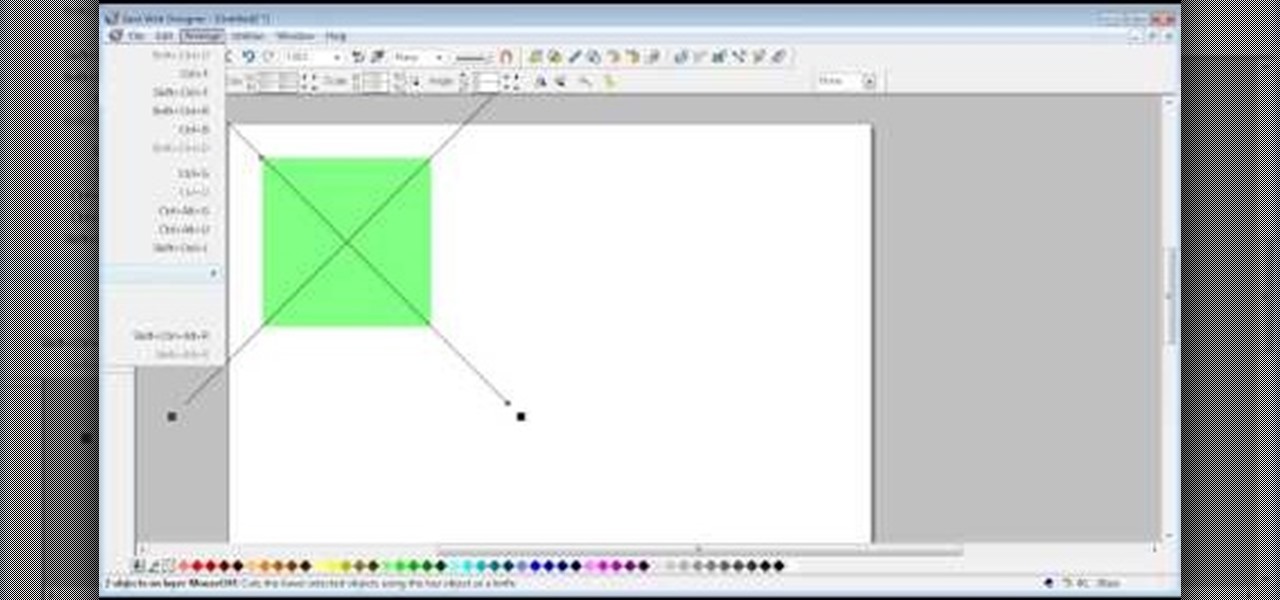
The video shows us how to create bevels in Xara web designer. Firstly using the rectangle tool hold down the Ctrl key to create a square. The problem with the Xara web designer is that it hasn't got a convert to edit the shape features which actually means that you cant select individual nodes with the shape editor tool which may create some other line. However you can select individual nodes by going to arrange/combine shapes/add shapes with selecting the rectangle. And by doing changes the ...

Evergreen bows, like Hemlock, can be placed over tender plants to protect them against cold, winter winds. Gently place them over the plant creating a tepee or tent form. It will allow some air circulation underneath so the protected plant doesn't rot but the Evergreen bows protect it against the cold.

Looking for a guide on how to protect a Microsoft Windows desktop computer or laptop from viruses, spamware and other malicious software? This clip provides a very good starting point. For complete details, and to et started protecting your own Windows PC from viruses, watch this home-computing how-to.

See how to protect your home computer from spyware. This home-computing how-to from the folks at CNET TV will teach you what you'll need to know to do just that. For more information, and to get started protecting your Windows PC and your own privacy, watch this helpful video guide.

Password protect your files and folders in Mac OS X. This free video tutorial from CNET TV will show you how. Thwart would-be snoopers with this home cryptography guide, which presents easy-to-follow, step-by-step instructions on how to protect your privacy by encrypting your sensitive data.

Password protect your files and folders in Microsoft Windows XP or Vista. This free video tutorial from CNET TV will show you how. Thwart would-be snoopers with this home cryptography guide, which presents easy-to-follow, step-by-step instructions on how to protect your privacy by encrypting your sensitive data.

How to password protect a folder and make files invisible in Windows XP.

Bennett Froddy brought us the Flash game sensation QWOP, and now has released a free sequel called GIRP. You control you character's individual limbs with the keyboard as before, but this time you're controlling a rock climber and using keys to grab particular handholds. It's tricky at first, but this video will show you how to beat the first 25 meters. Damn that bird!

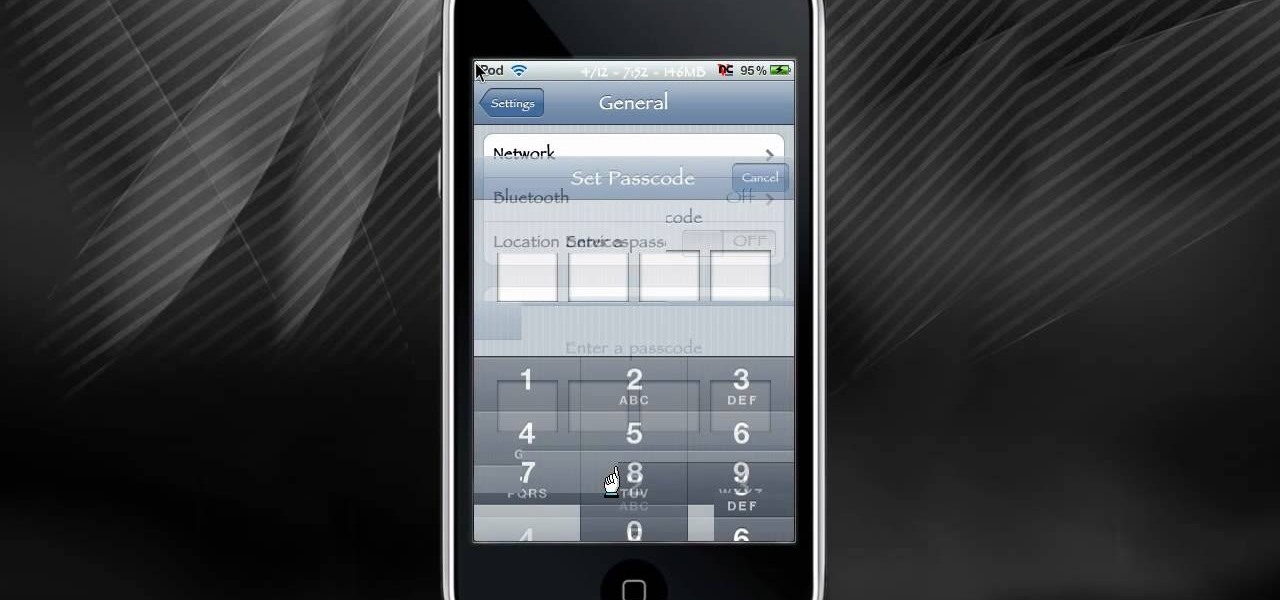
Back in the olden days, if a lock was, well, locked, you couldn't get in the door. At least, the average individual couldn't get in the door. But inventive and scheming folk (read: ye hackers of olde) devised crafty ways to pick lock keys and sometimes even created skeleton keys that opened any door or chest. This will let you unlock someones password on an ipod or iphone touch.

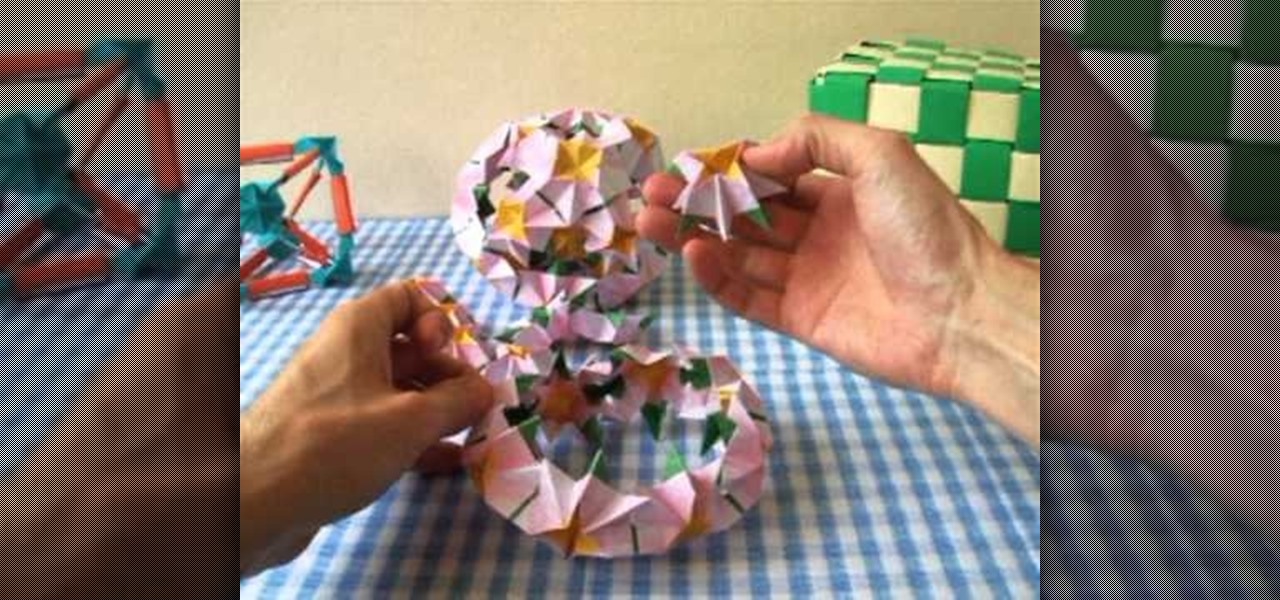
When you have to use 18 individual pieces to create an origami project, you know it's going to be hard. Thankfully, with this video you'll be guided through exactly how to maneuver every crease and fold.

Enhance your visual skills and demonstrate your manual dexterity as a magician by incorporating the "RockIt" card fluorish by Ayres into your repertoire. Playing card fluorishes are typically performed as part of larger magic performances and can also be shown on their own as individual exhibitions of skill.

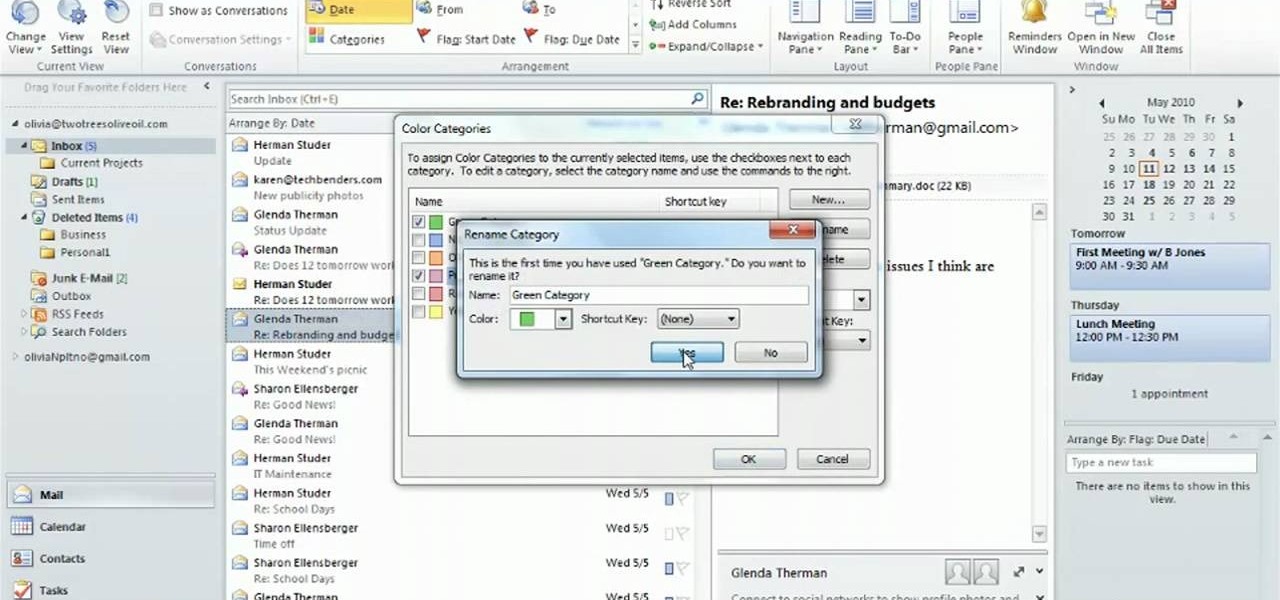
See how to organize your email by creating categories and flagging individual messages within Microsoft Office Outlook 2010. Whether you're new to Microsoft's popular email and scheduling application or a seasoned MS Office professional just looking to better acquaint yourself with the Outlook 2010 workflow, you're sure to be well served by this video tutorial. For more information, and to get started organizing your own inbox, watch this free video guide.

Even with all the technological advancements, iPhones and Blackberries look sleek but lack individual style, their backs a basic black or silver. Turn a blah cell phone cover into a fairytale work of art by watching this video.

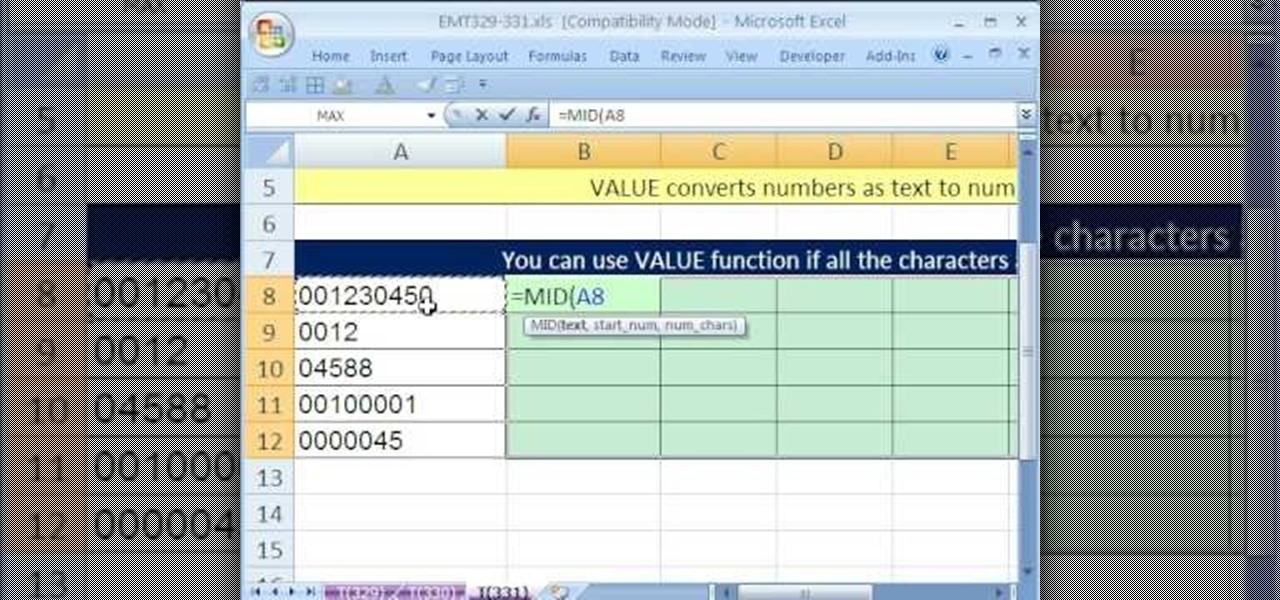
New to Microsoft Excel? Looking for a tip? How about a tip so mind-blowingly useful as to qualify as a magic trick? You're in luck. In this MS Excel tutorial from ExcelIsFun, the 331st installment in their series of digital spreadsheet magic tricks, you'll learn how to extract individual characters without extracting the leading zeroes through use of the MID, VALUE and COLUMNS functions.

Here is a series of hot and complex sexy salsa dance patterns. This is a more complicated salsa pattern. It is a very long pattern, so take it in strides and small bites. We have named the individual moves to help you piece the entire salsa combination together.

How to use a can opener with one hand or without a prosthesis. This is an adaptive equipment tutorial for handicapped, disabled or individuals that have lost limbs to amputation. This trick is important to ensure healthy living and daily tasks like opening food in the kitchen. Live without limits!

A below elbow arm amputee demonstrates how to tie a shoe with his prosthetic hook. This is an adaptive equipment tutorial for handicapped, disabled or individuals that have lost limbs to amputation. The prosthetic arm outfitted with a hook or hand can be body powered or myoelectric. The operation is important to ensure healthy living and daily tasks like dressing yourself.

A below elbow arm amputee demonstrates how to turn a car key with his body powered prosthetic hook. This adapted equipment video is helpful for handicapped, disabled or individuals whom have lost limbs due to amputation. He's using a prosthetic arm outfitted with a hook to start the ignition of his car.

A below elbow arm amputee demonstrates how to hold and use a knife with his prosthetic hook. This is an adaptive living video that helps handicapped, disabled or individuals that have lost a limb due to amputation. Using a prosthetic hand or hook can be challenging in the kitchen. Using a hook to hold and use a knife is an important skill to learn when using prosthetic limb adaptive equipment.

This audio editing software tutorial will show you two different types of editing in Logic Pro. First, Connor Smith shows how to edit multitrack drums in a group (to fix timing of hits) in Logic Pro. Then he covers how to ungroup your drums and take out pops, clicks (etc.) on individual drum tracks in Logic Pro.

This science video tutorial includes step-by-step instructions for extracting DNA from wheat germ, the embryonic plant attached to the wheat seed. Individual wheat seeds, or kernels, separate readily from the plant. This kernels have a tough outer coating called bran. If you want to know more, just watch this science experiment.

You can give your song texture by adjusting individual tracks to become louder and softer to emphasize particular moments. With GarageBand, this process is easy and yields professional-sounding results.

You already know you can create photo pages by selecting a photos template and dragging in individual photos from your iPhoto library. Now there's an easy way to add entire photo albums to your site, each with their own dedicated photo pages.

When BlackBerry made the move to Android OS, they were aware of the limitations it presented. Unlike with BB10, they didn't create the operating system and would have to deal with the vulnerabilities already included. As a result, they added numerous security enhancements, and at the heart of this is DTEK.

Smartphones are becoming pocket computers, jammed full of data essential to our personal and professional lives. With AT&T's 360 Backup app you can protect your important information with the push of a few buttons.

When you start a blog of your own you will want to make sure you protect yourself. Even before your blog takes off you will want to research trademark law when you attempt to register for a domain name.

Getting back to nature can be an incredibly rewarding experience – unless critters come along and ruin it! Here's how to keep your food from being plundered. To keep your food protected while camping out in the great outdoors, try bringing along a cooler, a cloth or nylon sack, a sock, some rope, and sealable, waterproof plastic bags. Keeping your provisions safe will decrease the risk of animal attack, and make your journey out into nature a fun experience.

Fantasize about role playing? One of the most popular venues for role playing medieval fantasy is the board game, Dungeons and Dragons. Get a group of three or four together and have a blast!

Protecting the ball in water polo is key to playing a solid game. This water polo instructional includes many drills designed to improve 1-1 play. It includes tips for both the water polo defense and attacker on how to protect the ball in play. This also refers to TV clips of league and pro games to connect it to actual game play.

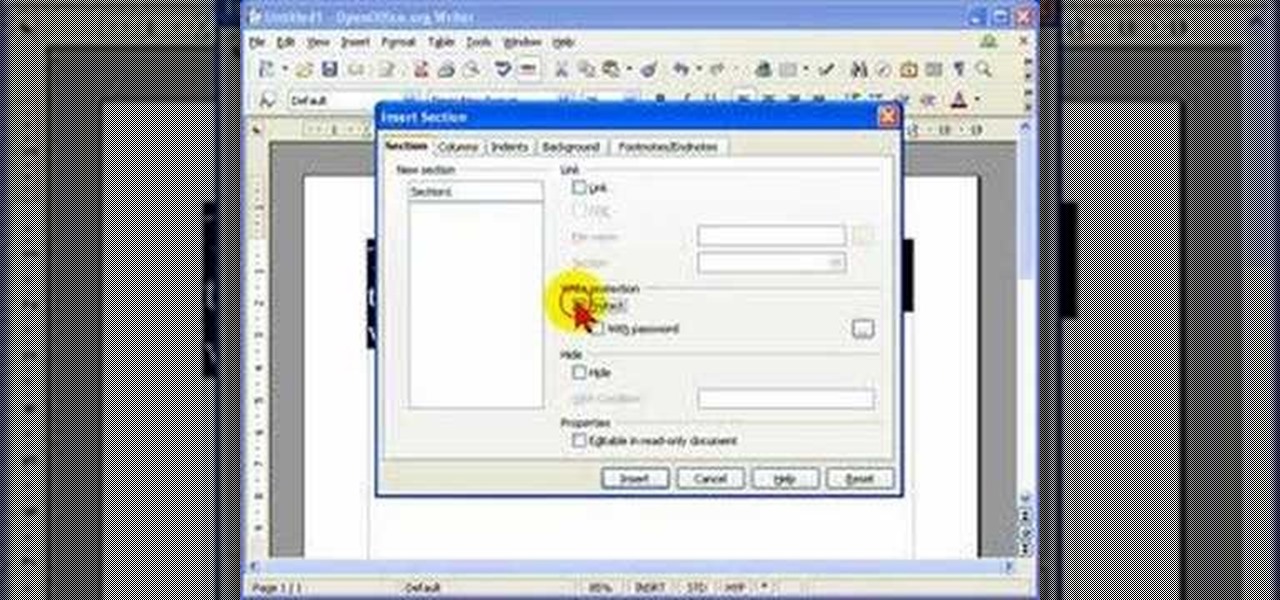
When you are editing your documents, it is sometimes a good idea to protect areas of text, so they cannot be edited, just in case you make a mistake and edit the wrong part.