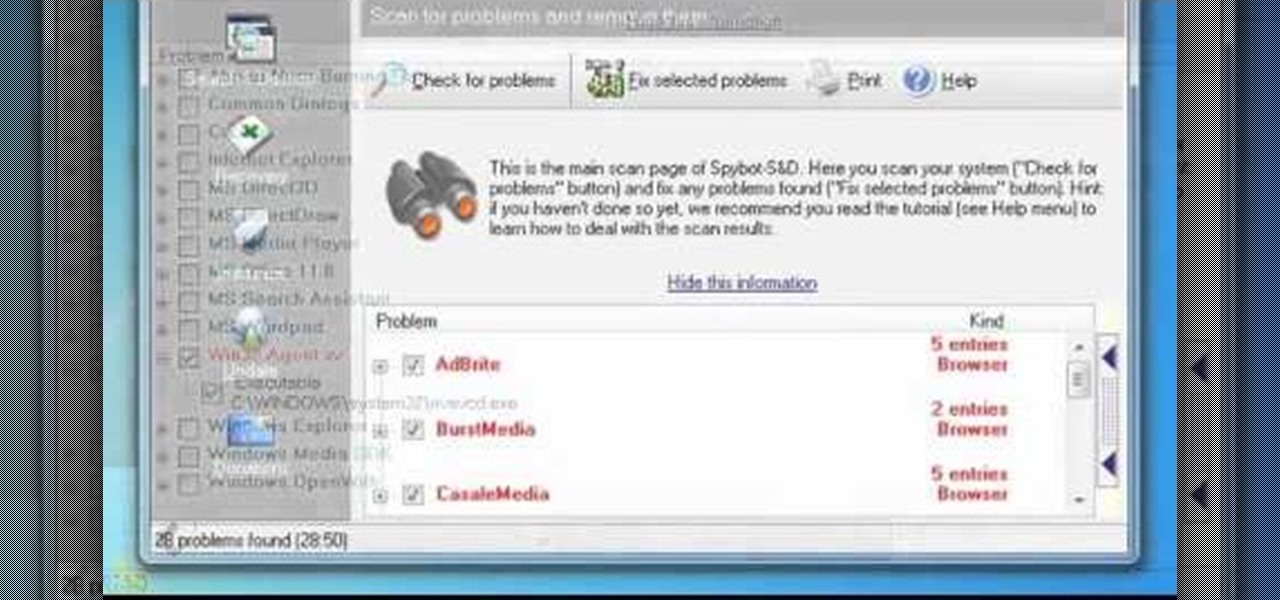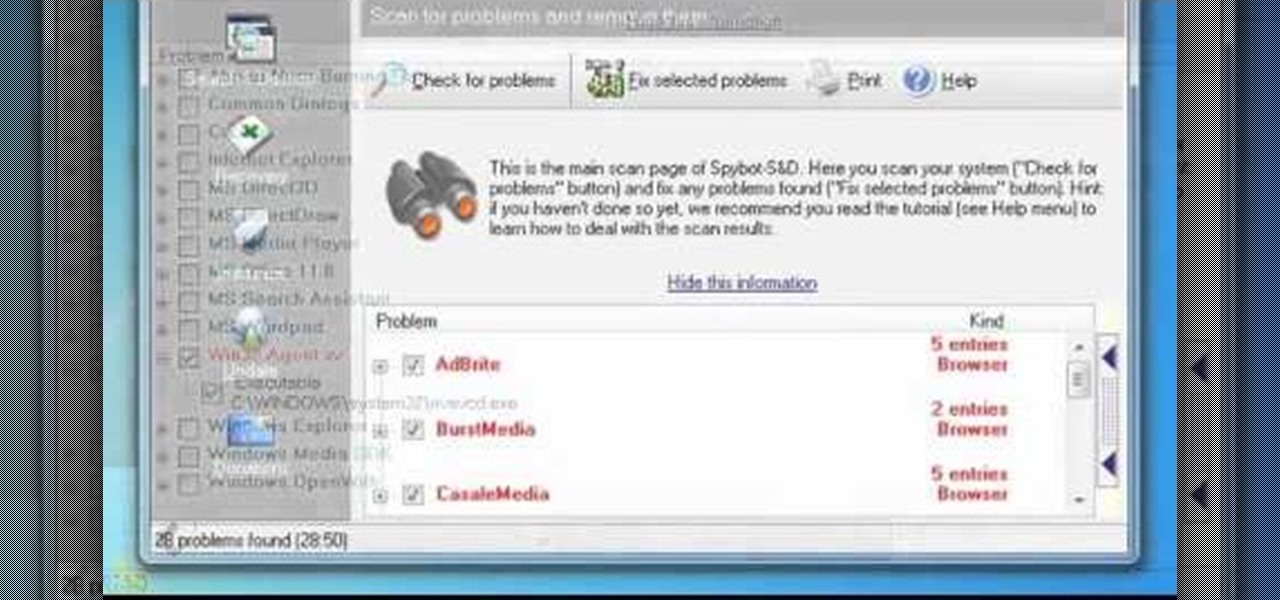
In this clip, you'll learn how to use the free Spybot Search & Destroy tool to protect against and remove malware on a Microsoft Windows PC. For more information, including detailed, step-by-step instructions, and to get started using Spybot on your own Win PC, take a look.

Looking for an easy way to protect your privacy when using Google Search? With the right habits, it's easy. So easy, in fact, that this home-computing how-to from the folks at CNET can present a complete overview of the process in just over a minute. For more information, including detailed, step-by-step instructions, take a look.

In this clip, you'll learn how to use the Backtrack 3 Linux distro and Aircrack-ng WiFi security app to crack the password to a WEP-protected wireless network. The process is simple. For more information, including step-by-step instructions, and to get started testing the security of your own WiFi networks, watch this hacker's how-to.

Interested in finding out just how secure your WEP-protected wireless network is? Let this video be your guide. It's a simple process and this home-networking how-to will teach you everything you'll need to know. For specifics, including detailed, step-by-step instructions, and to get started cracking WEP networks with BackTrack yourself, watch this helpful video guide.
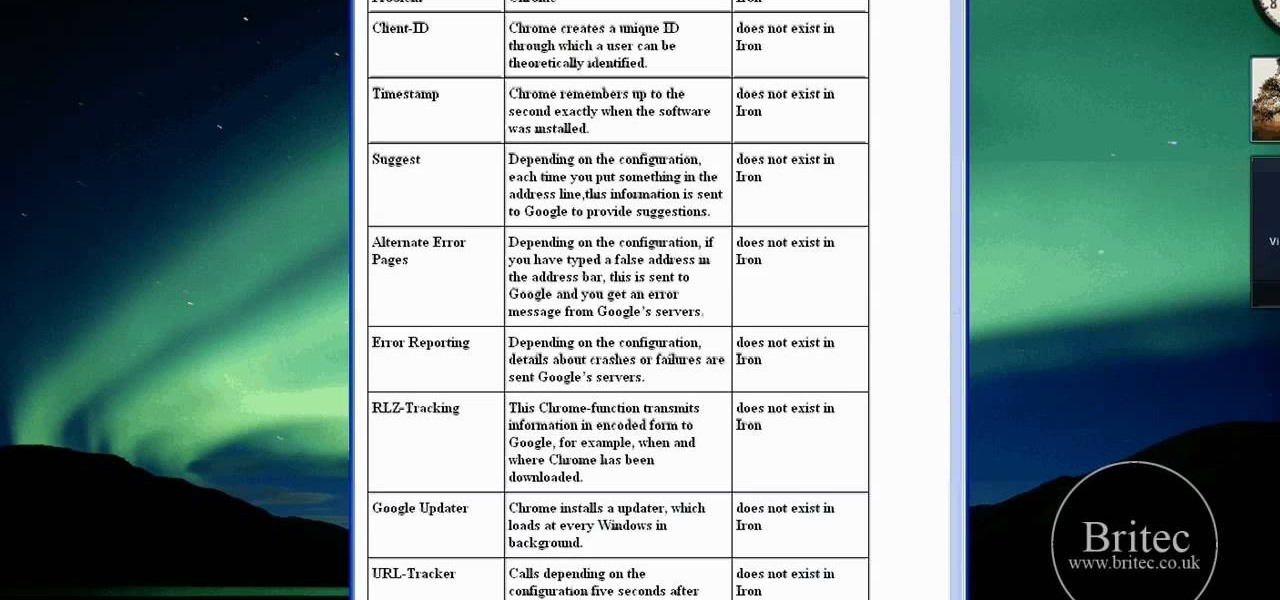
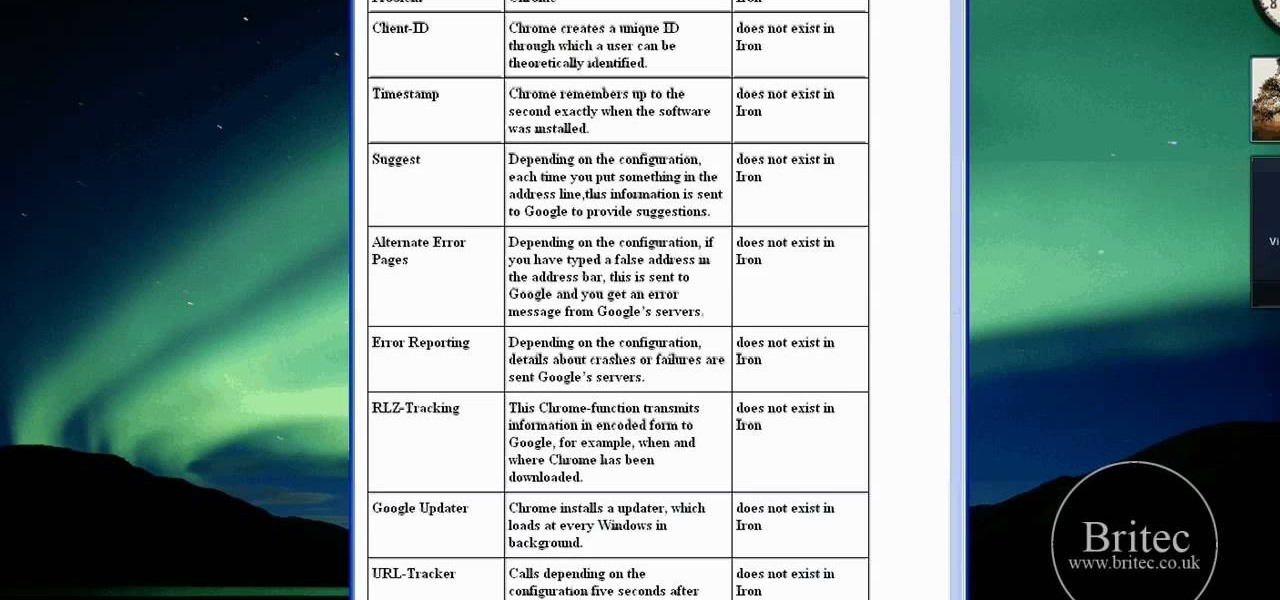
Interested in using Google Chrome but concerned about protecting your privacy while surfing the web? Meet Iron Browser, a secure but otherwise identical clone of the Google Chrome web browser. This clip from Britec will teach you where to find it, how to install it and how to get started using it.
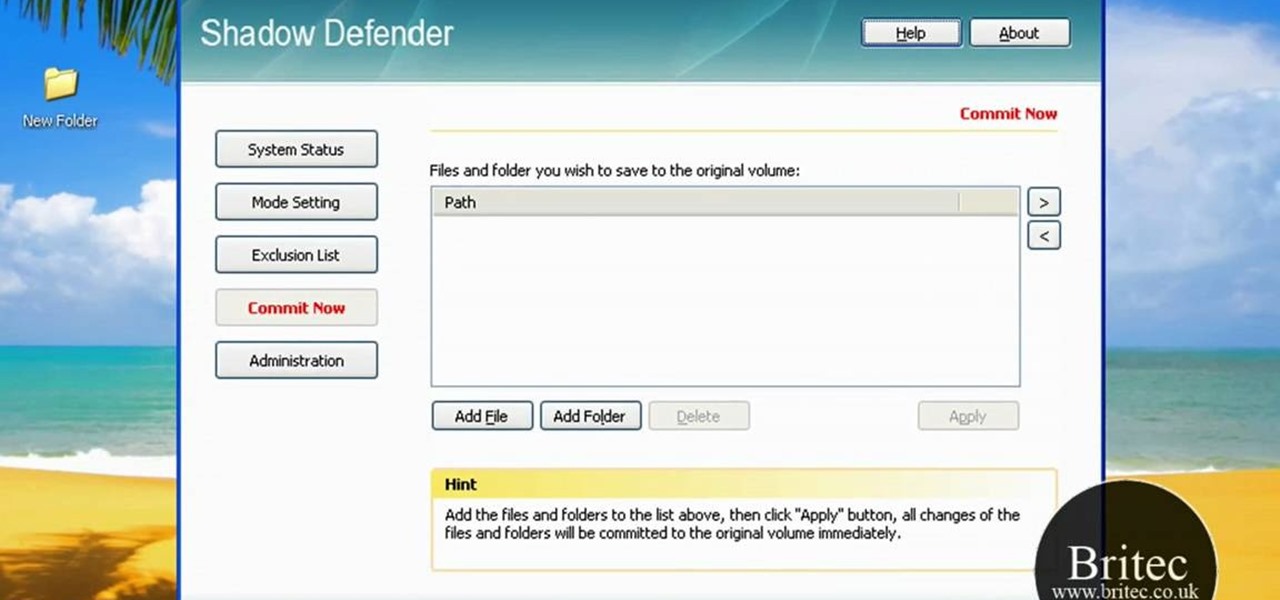
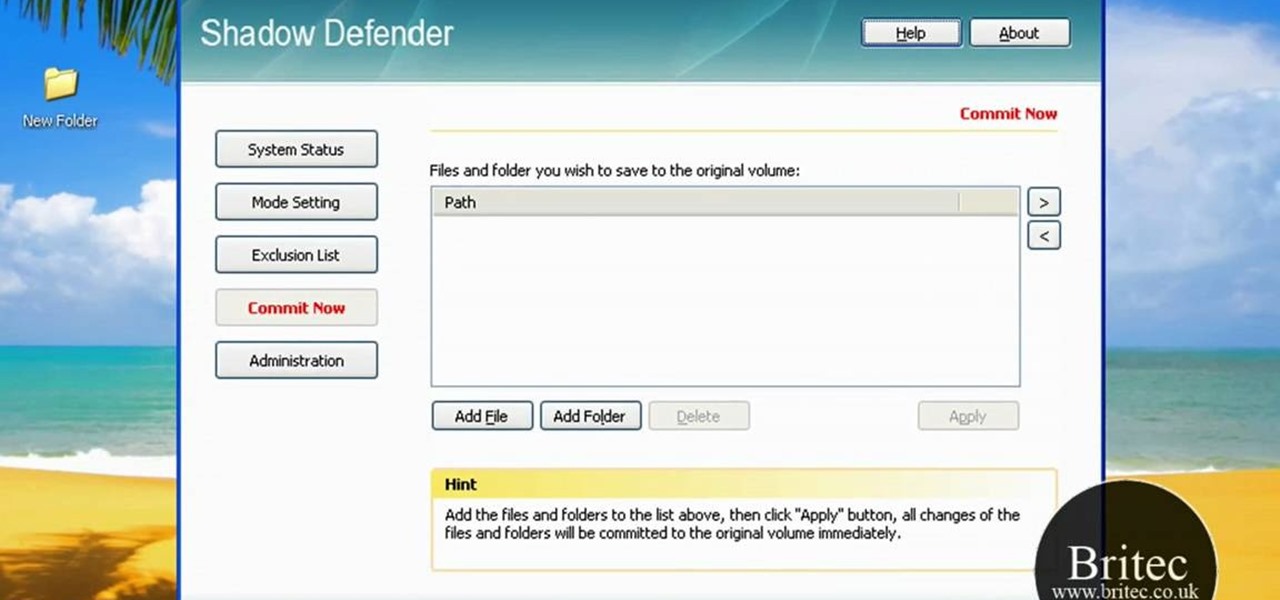
Looking for a security solution for your Microsoft Windows PC? With Shadow Defender, it's easy! So easy, in fact, that this home-computing how-to from the folks at Britec can present a complete overview of the process in just under ten minutes. For more information, including step-by-step instructions on how to get started using Shadow Defender to protect your own desktop computer or laptop, take a look.

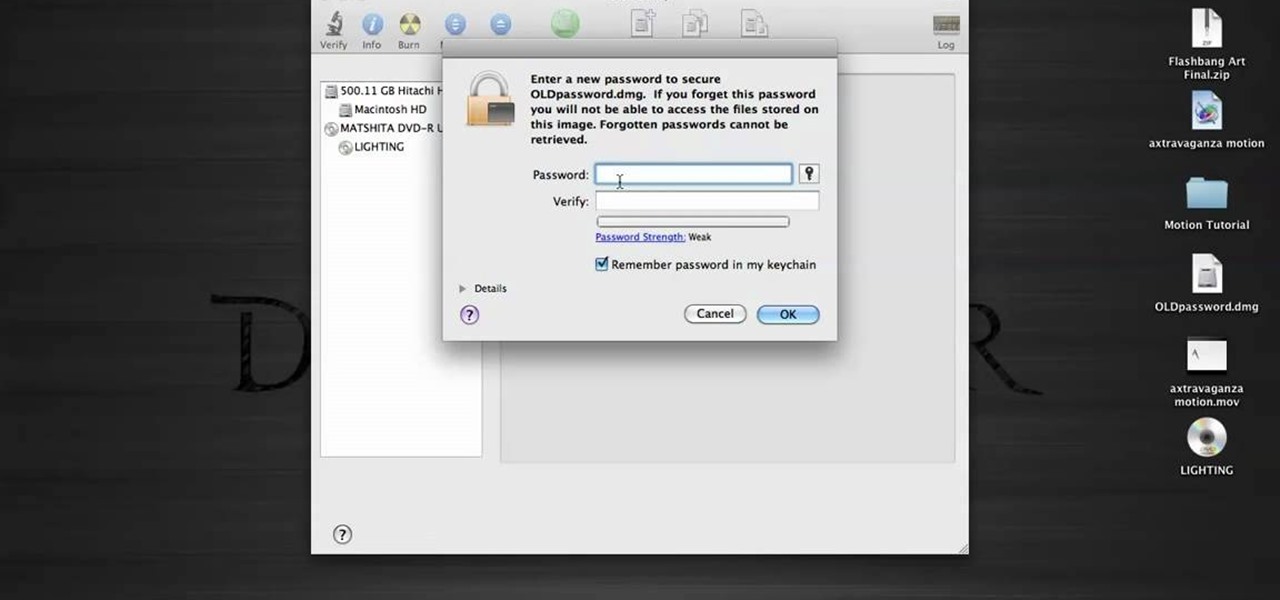
In this tutorial, we learn how to password protect a folder in Snow Leopard on your Mac. First, go to the finder and click on "utilities". Now go to "file, new, disk image from folder". Now, you can select the folder you want and then click "image". Make it a read/write folder so you still can edit the files and enable the encryption. Save this, then it will ask you for a password. Create a password and then verify it. When finished, uncheck the "remember my password", then click on "ok". Now...

If you're restoring an old vehicle, it's always important to make sure you take the necessary precautions for preventing any damage. In this particular video tutorial, you'll find out how to protect your door panels on a classic VW Beetle Bug without any problems. So good luck, pay attention, and enjoy!

My Blackberry TV demonstrates how to protect your Blackberry device with a password. Protecting your Blackberry with a password will help to stop people from accessing your personal information on your device. From the home screen, press the Blackberry menu key. Then, select the options choice. Next, scroll down to the password choice on the options menu. Select password and then select the set password button on the password screen. Enter your desired password and then press the enter key. V...

As any SLR or DSLR owner knows all too well, the price of lenses can often approach or even exceed the cost of your camera. As such, it's important that you take the necessary precautions to protect them. With this free photographer's guide, you'll learn about using UV (that is, ultra-violet) filters to protect your single lens-reflex camera lenses from sun damage.

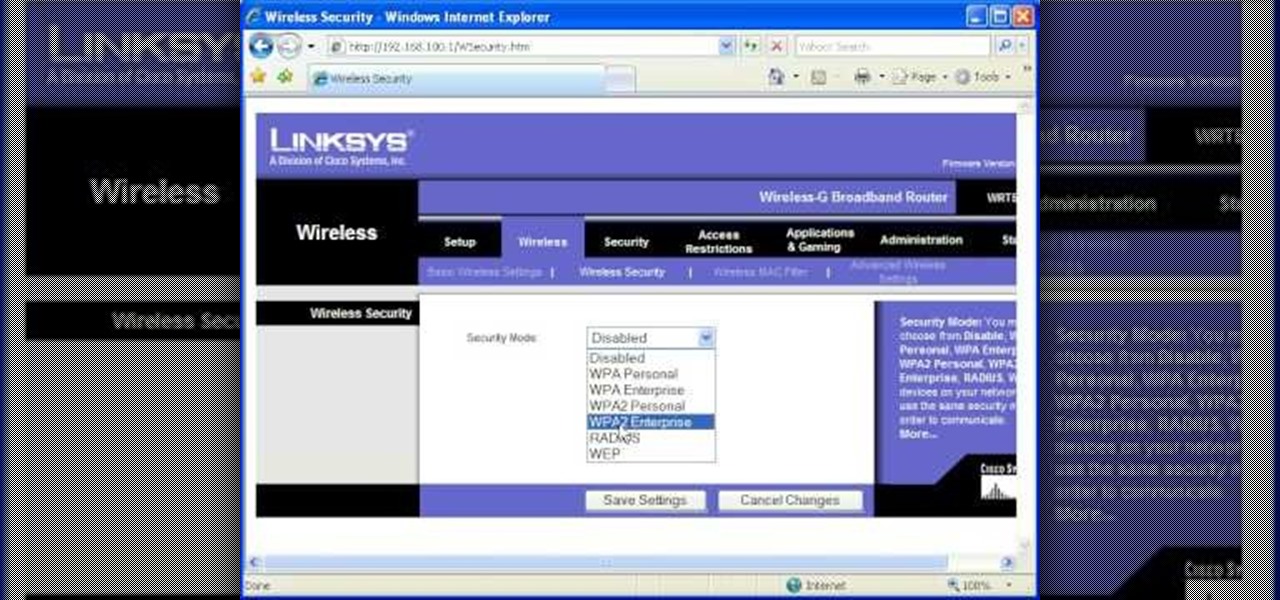
Most of the home wireless networks are not set up by professionals and hence they might lack in security features. People just set up the wireless networks by connecting the devices and powering them up and never care to apply security settings to the network. This may result in your wireless network being compromised by unwanted external entities. How ever you can do a web based configuration settings and secure your wireless network by password protecting it. This settings differ from the m...

If you live in a hurricane prone area, it is a good idea to protect your windows with security film. This video will teach you how to install hurricane security window film on your own and protect your home and assets.

Ron Hazelton explains how to protect your foundation or basement wall from being affected by water that is discharged from your downspout. He explains how downspout extenders can be used to carry the water away from the foundation. Ron will show you three variations of downspouts that you can use. You'll learn how to install each kind of downspout so you can decide which is right for you. If you follow the advice given in this video, you're sure to further protect a very important part of you...

In this video a professional boxer demonstrate the basics of boxing so that you can protect yourself. First of all, you should stand in such a manner that your left foot is in front and the right foot is in back (if you are right-handed). Make a fist, put both hands in front of your face. The distance between both the hands should not be much so that in any case, you can cover and protect your face. Your left hand should always turn up and pull back. For punching, take your right hand fist ne...

Watch this video for a helpful tip on how to use secret folder application and protect folders in your MAC PC by hiding it. you could download secret folder application from version tracker.com for free go to the Website and click download button to download the application on your Mac PC open the secret folder application. click on the required password button, put your desired password and re enter to confirm. to access your file, click the plus button at the lower left. choose the desired ...

Looking to get an FHA loan? The Federal Housing Administration, FHA for short, provides mortgage insurance on loans made by FHA-approved lenders throughout the U.S. Here's how to get your FHA-insured loan. Learn how to get one with help from this video.

Living within your means can be done. You don't want to be a slave to the credit card company, do you? Learn what to do to stay out of credit card debt. This how to video will give you the tips. Credit card debt is a slippery slope.

Need to unlock your music? Want to save Rhapsody or Napster files on more than your own computer? This is how to unlock, remove drm and convert protected wma files from napster and rhapsody to mp3 without having to pay for them. Also how to put napster and rhapsody files in iTunes and on your iPod.

The Microsoft Office Access 2007 relational database manager enables information workers to quickly track and report information with ease thanks to its interactive design capabilities that do not require deep database knowledge. In this Microsoft Access video tutorial, you'll learn about protecting your VBA code from snoopy little trolls. For more information on keeping your VBA code secure, watch this MS Access how-to.

Sadly, into each life at least one mean, nasty, low-down, no-good boss must fall. When it's your turn, you'll want these survival tips. Trying to remain calm and protecting yourself are important strategies to protect your career. Watch this video job skills tutorial and learn how to cope with an unfair boss.

Watch this Chinese language video tutorial and learn useful phrases and additional vocabulary when making purchases with a credit card, such as "Number" and "Can I use my credit card here?" Learn how to correctly pronounce the words and phrases, and how to use them properly in the real world with your Mandarin teacher Benny. Sharpen your Chinese language speaking skills.

Early iPhone buyer? Watch this video tutorial to learn how to find out if you're eligible for a $100 Apple credit, and watch how easy it is to collect. This how-to video will help you get your $100 iPhone credit quickly if you are eligible.

In this video Bob Schmidt shows you how to protect yourself when working with fiberglass insulation when insulating or doing removals during your home improvement projects.

Watch this video to learn how to make a password protected video.

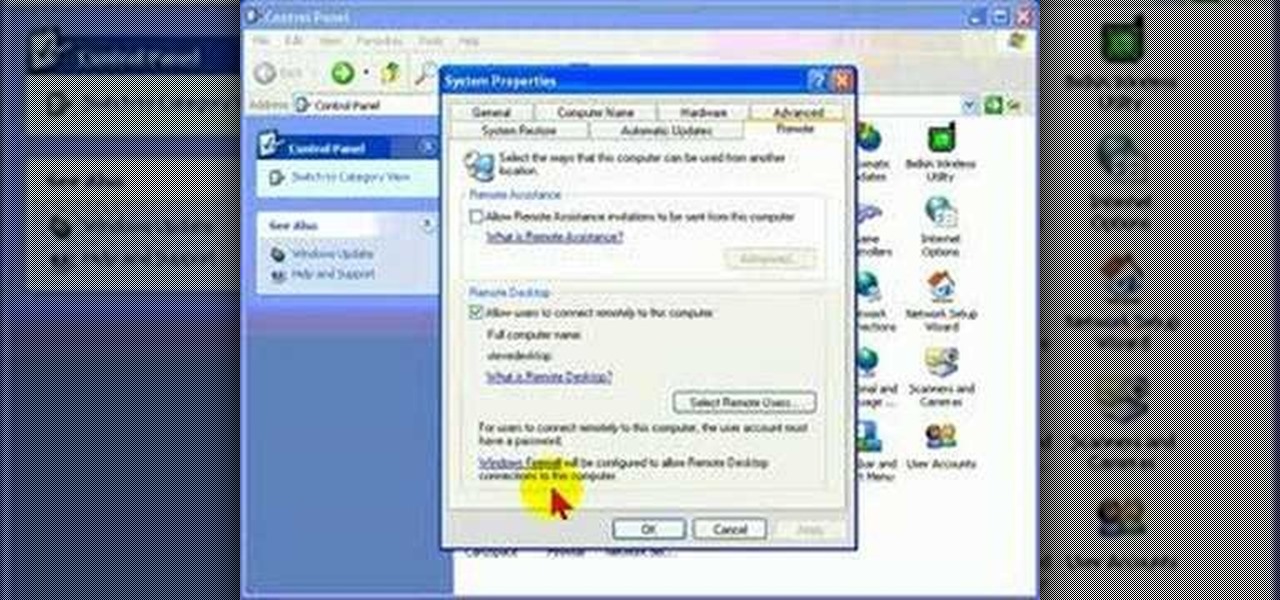
Remote Desktop is a feature of Microsoft Windows, that allows you to access your PC from anywhere in the world, and use it as if you were sat right in front of it.

One method you can use to protect yourself, is to ensure you clear your private data, such as your search history, and in this screencast tutorial, we show you how to do just that in Mozilla Firefox.

Gary Rosenzweig from MacMost looks at one method to protect a set of files with a password on a Mac. It involves using Disk Utility to create an encrypted disk image.

Veronica Belmont imparts her wisdom on how to be safe within social networks. Learn how to adjust the settings on your Facebook, MySpace, and/or LinkedIn profile to help protect your privacy.

This video segment will show you how to protect your LCD or DLP TV which is susceptible to irreparable damage. We can build you a custom screen for far less cost that a TV repair.

Andrew Burke from Videomaker magazine gives some advice for protecting your equipment while shooting in the rain.

Want to make your fingers look like they have flames shooting out of them? Learn how to protect your fingers while they are ablaze and make your friends think you are impervious to pain. Use easy to find material to protect your fingers while you light each one on fire.

In this video you will learn how to build scrolling credits in Final Cut and Photoshop CS3. He begins by showing you how to do it on Photoshop CS3. He does this by having his own finished credits and the steps you need to take to set up your own. Then, he moves on to Final Cut and drags his Photoshop credits into Final Cut. He explains how it may be off a little in size, but you can readjust everything for accuracy. This is all done through his computer and with vocals.

This Ruby on Rails instructional screencast demonstrates credit card validation within a Ruby on Rails application. It uses the credit card library from Lucas Carlson. This library validates the structure of a credit card number and can also return the type of card being used. Informative Ruby on Rails computer programming how to video.

When you're on the go, it's important to keep your belongings organized and at an arm's distance so you're not fumbling in public for your keys, cards, or phone.

In this video, we learn how to protect yourself and your mattress from bed bugs. These bugs live in your bed and hide anywhere in your home and even hotels. To see if you have them, you will see blood stains on your mattress and look on your skin for any bites you may have. If you suspect you have them, you should call a professional to help take care of the problem. Check the edges and corners of your bed to see if you have been infested with bed bugs, and look at the label as well. Be caref...

It's that time again. Snow days, Thanksgiving dinner, holiday presents ... and great Black Friday deals. Starting the Friday after Thanksgiving (or sometimes a few days before), millions of items will go on sale, including your next Android phone.

Equifax reported on Sept. 7 that it discovered a breach on July 29 which affects roughly half of Americans, many of whom don't realize they have dealings with the company. Hackers got away with social security numbers, addresses, and driver's license numbers, foreshadowing a "nuclear explosion of identity theft." Let's explore what really happened and what you and those around you can do to protect yourselves.

Check out this video for advice on how to build a brand new wallet out of duct tape. These aren't just ordinary wallets, either, they have slots for credit cards and everything! These are complete billfolds and can be made into plenty of different style depending on your preference. So, follow along and once you get the hang of it, why not experiment and create your own design?

Raise your credit score in five simple steps? Sounds too good to be true, doesn't it? Well, financial expert Linda Ferrari is here to to explain to you how this is possible. In these rough economic times, everyone could use a little boost, so why not take some of Linda's advice and give your score some help?

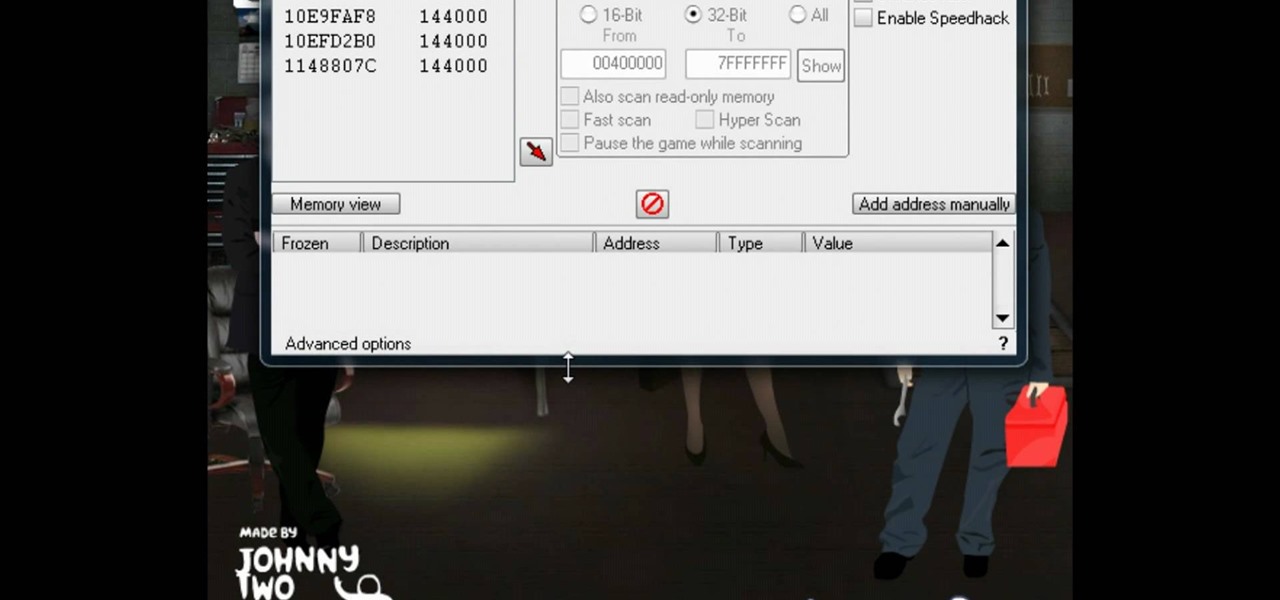
Having trouble with The Heist 2? Well in this quick and easy tutorial by Trevor4Ever595 you can kiss your troubles goodbye. In this video Trevor4Ever595 shows you how to hack the credit amount so credit is no longer in your way to buying all the upgrades you need to fly through the game. He shows you how to do this using Cheat Engine 5.5 you can edit your credit to your satisfaction. Trevor4Ever595 would be happy to help you with any questions you may have regarding the tutorial. Simply leave...