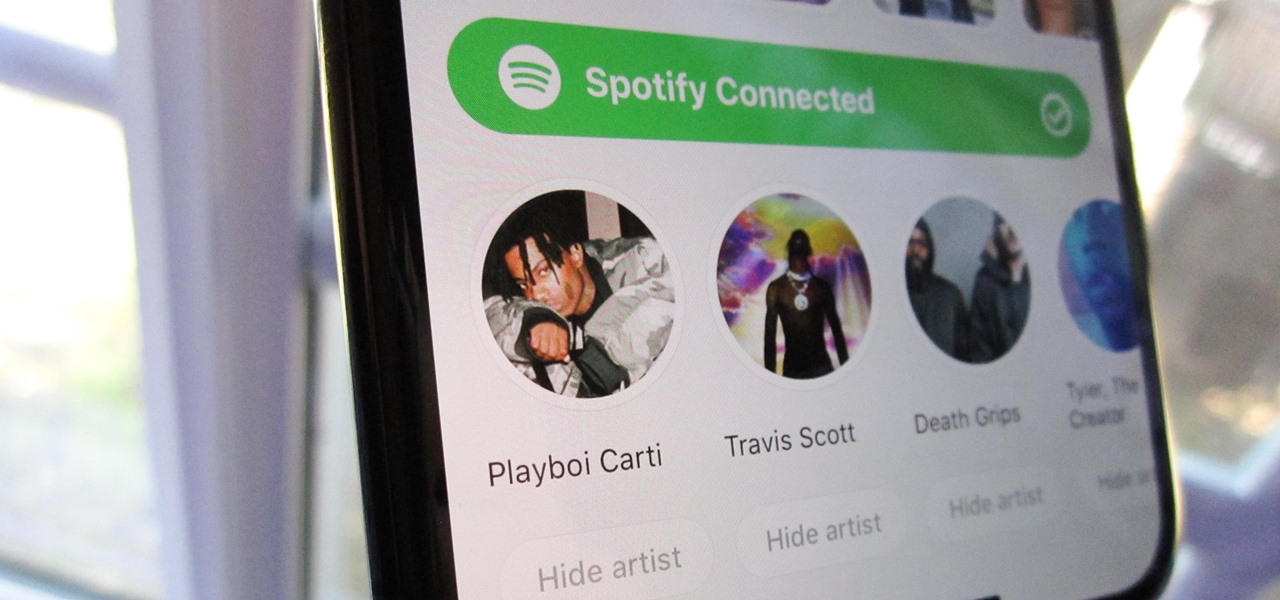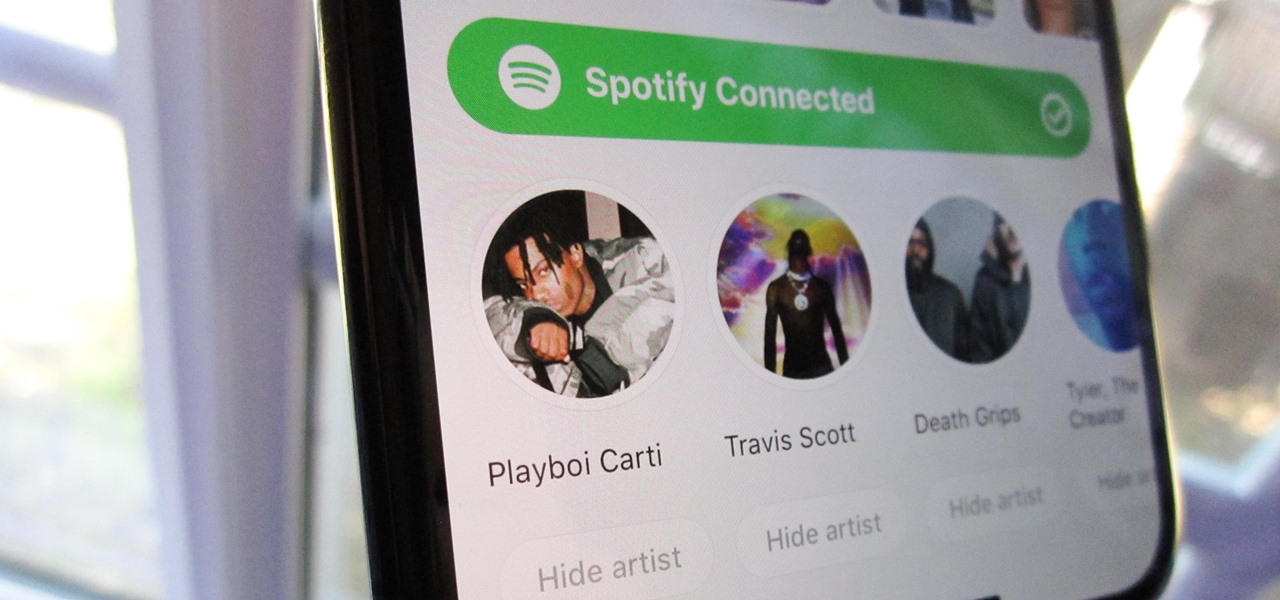
Spotify integration in Bumble has been around for a few years now, allowing prospective matches to view the artists you listen to the most on the popular music streaming service. It definitely helps people connect, but sadly, it doesn't work as well as it should because it rarely updates to show what you're listening to now.

Occipital's initial augmented reality module, the Structure Sensor, gave iPhones and iPads the depth-sensing abilities of the HoloLens. Now, the company's latest product promises to do the same for Android devices, as well as augmented reality and virtual reality headsets and other devices.

Facebook is preparing to make augmented reality experiences for brands more visible in its mobile app with Tuesday's introduction of augmented reality ads in its News Feed.

Despite the fact that Snap Inc.'s Spectacles weren't the hit some were expecting, the company is nevertheless taking another swing at it by releasing an updated version.

Apple has introduced a special edition iPhone 8 and 8 Plus to bring attention to the ongoing worldwide battle against AIDS. As the second iPhones to carry the (PRODUCT)RED name, these rare iPhones may quickly sell out when preorders open up on Tuesday, April 10, at 5:30 a.m. (PDT), so we'll go over some tips to help you secure a red iPhone before it's gone.

After Vuzix's scorching hot week at CES, the future of AR is so bright, we have to wear (smart) shades. Luckily, Vuzix is making it easier for consumers to grab a pair.

After hosting millions of free 3D models online, Sketchfab is betting that augmented reality and virtual reality developers and creators will be willing to pay for premium 3D content.

The Star Wars saga may have occurred a long time ago in a galaxy far, far away, but Nissan is using a futuristic technology to bring stormtroopers and droids into its dealerships.

Update 10/23: The hits just keep on coming. We're now seeing reports of a "smearing" effect when scrolling through apps on the Pixel XL 2. We'll expand on that at the bottom of this article, but it's still worth reading the background information on issues with LG's new POLED displays.

A survey by ABI Research revealed that only 25 percent of businesses have implemented augmented reality technology in some form or fashion.

If you live in New York City and are itching to sell your Yeezys, you're at risk of falling victim to thieves. A devious duo is searching Facebook to find people selling the popular sneakers and then robbing them at gunpoint when they meet up in person.

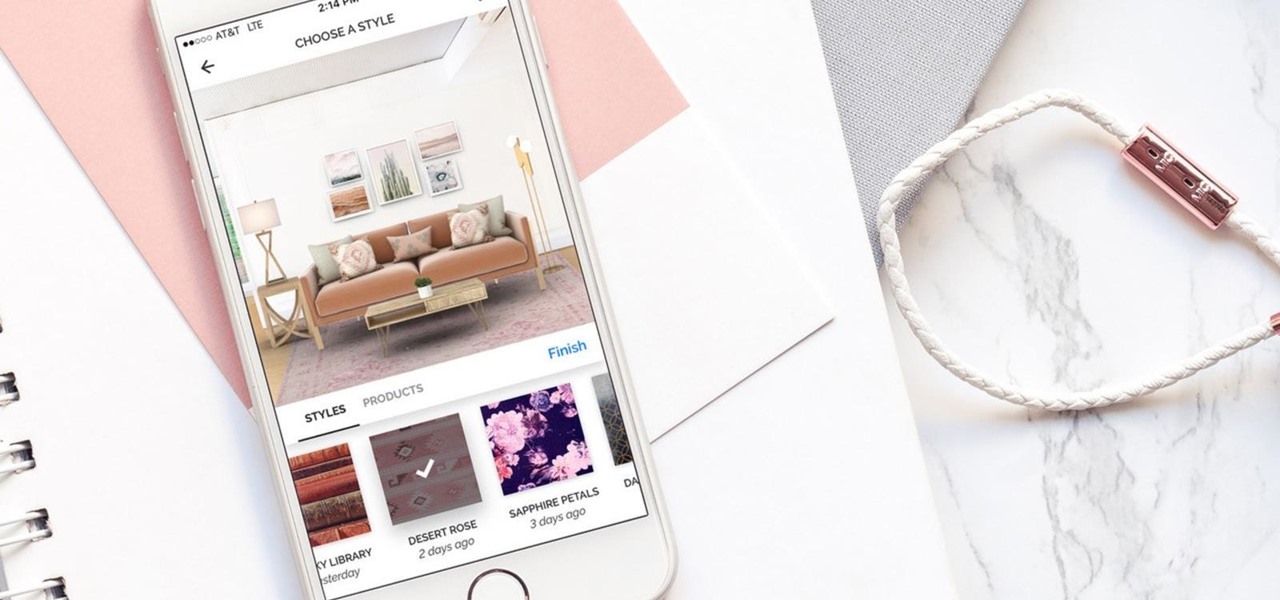
Hutch Interiors, Inc., makers of an eponymous augmented reality home design app for iOS and Android, has closed a series A round of funding, led by online real estate company Zillow Group, totaling $10 million.

When it comes to differentiating from the competition, brands are continuing to leverage augmented reality to give consumers to the point that there are few "firsts" left to achieve in the marketplace. While L'Oreal jumps on the augmented reality bandwagon for cosmetics, Acura finds a new way to make augmented reality a spectacle in the automotive industry.

Ride-hailing services are everywhere nowadays and with new companies developing all the time, it is one of the most convenient ways for people to get around. Companies like Uber make it easy for passengers to call a car to pick them up and drive them to their desired location. These services have been especially helpful for commuters as well as those who might need a ride home after a night at the bar. However, ride-hailing services require driving with a total stranger, which means the safet...

Tim Cook claimed 85% of new iPhone buyers are switchers from Android back in 2015. Now, after financial analysts noted a drop in the company's stock prices, Apple has unleashed a series of ad campaigns directly targeting the users it needs to win over. That's you, Android lovers.

The battle of the budget phone is well and truly underway, as both T-Mobile and ZTE have launched affordable new devices simultaneously.

Augmented reality seems to be the talk of the town lately, with everything from glasses to furniture stores prepping to implement exciting, new AR technology. Well now, it looks like even our food is getting a makeover for the augmented reality future.

Apple just unveiled a red iPhone and iPhone 7 Plus, dubbed the iPhone 7 (PRODUCT)RED Special Edition, to commemorate the ongoing global fight against AIDS. Apple fans the world over are sure to swarm in and gobble up the initial stock shortly after the new color is released at 8:01 a.m. (PDT) on March 24, 2017, so we'll go over some tips to help you secure a red iPhone before it's sold out.

A few days ago, there were flying piranha, snakes, and dragons roaming around freely at the Anaheim Convention Center in California, but they weren't real or even hallucinations—they were holograms brought to life with the Microsoft HoloLens.

Earlier this week, a mysterious tweet appeared on the HTC Twitter account of a picture containing the letter "U" topped with a tiny "for" and the date "01.12.2017" at the bottom. It is a pretty solid teaser, but for a company that has had a solid year with their Vive virtual reality headset, and all of the other technological appendages they have, it seems a bit ominous for them.

I've seen my fair share of heartbreaks when it comes to used phones. As a repair tech, I often had to try and help out customers who bought used handsets which turned out to be useless, either because it was stolen or not working on their carrier's network. More often than not, there was very little I could do. To help you from being stuck in the same situation, here are some tips to prevent you from getting scammed out of your hard earned money when buying a used handset.

While it's been rumored for a few months, Apple finally unveiled its new 4-inch iPhone SE at the Apple Special Event on March 21st.

You didn't have to attend this year's CES to have gadget envy. There are so many great smartphones, computers, laptops, and other gadgets available in the market that the real challenge becomes choosing the right one to fit your needs and your budget.

Welcome back, my greenhorn hackers! Before we attempt to exploit any target, it is wise to do proper reconnaissance. Without doing reconnaissance, you will likely be wasting your time and energy as well as risking your freedom. In previous guides, I have demonstrated multiple ways to perform reconnaissance including passive recon with Netcraft, active recon with Nmap or hping3, recon by exploiting DNS or SNMP, and many others.

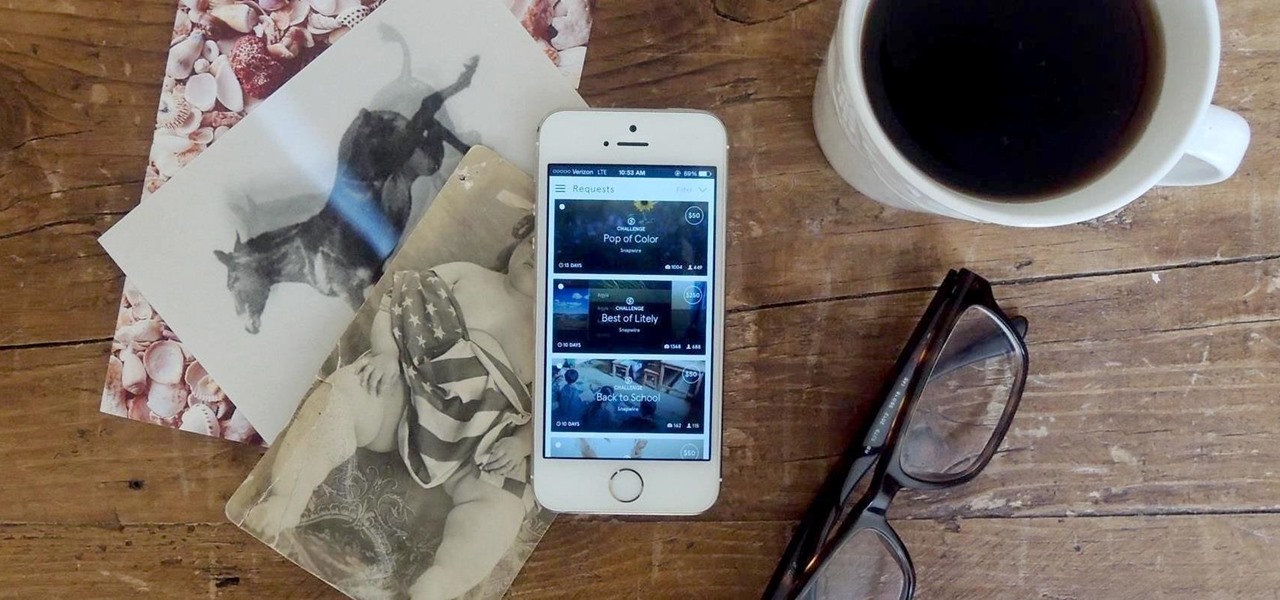
While the majority of photos taken on phones are used for personal reasons, mediums like Instagram and Flickr offer a means to show them off to the world. But those pictures of your brunch or beach day can actually go beyond that to make you some money.

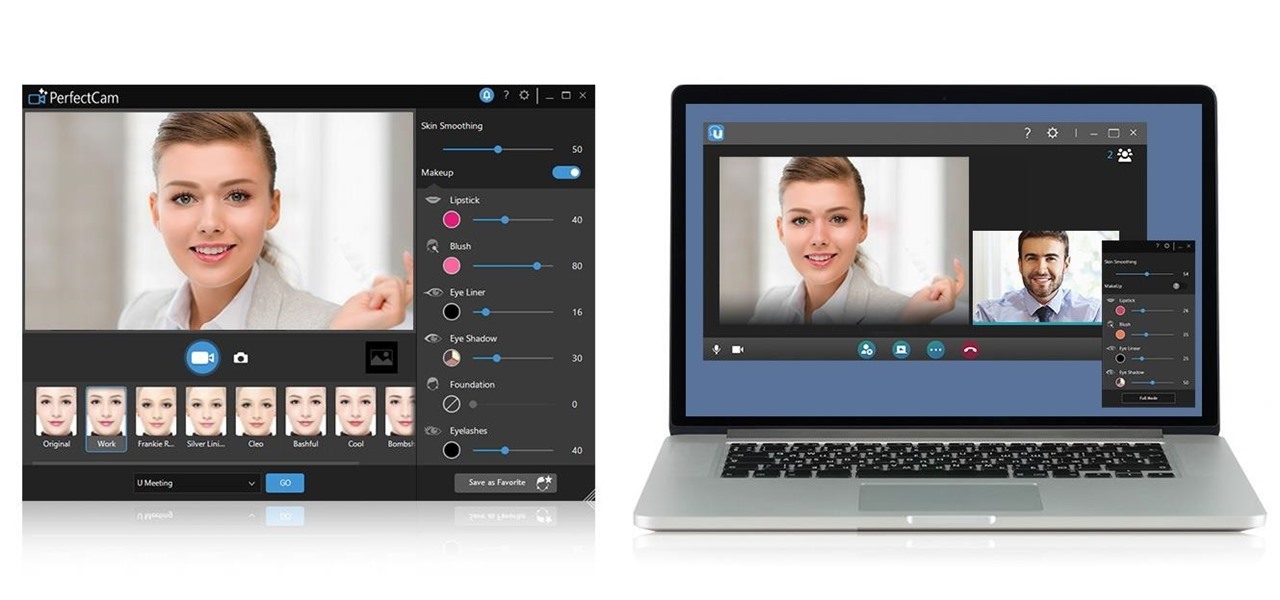
Have you ever heard the expression "Dress for Success" or "Clothes Make the Man"? When you're wearing a perfectly fitted designer shirt, something inside just shouts, "I look good" and when you genuinely think that, those feeling are radiated outward to all your come in contact with. That said, what kind of designer shirt are you interested in, a bargain basement discount, or one tailored made, outlining your best features?

If you weren't aware, all music purchased online through iTunes, Amazon, and other digital audio providers have information embedded that can be used to identify the buyer and transaction of the digital music file. This may seem like something you should be disclosed about in their terms of use, but it's not.

"Dude-man-bro, are you going to Coachella this year?" If I got a dollar for every time I was asked that question, I might just have enough money to actually buy the dang ticket. Concerts have been, for a very long time now, a great way to spend a night or a weekend having fun with friends and listening to some great tunes.

I loved the Gold Rush unit back in third grade. We went up to the American River and panned for gold, and my panning skills balled above all. I got like three tiny pellets. Of course, it was all fool's gold, aka pyrite, but it was still pretty legit. And this was before wearing gold chains was cool—or not.

After closing its office last year, enterprise AR company Daqri has moved on to the final stage of its lifecycle with the liquidation of its assets.

The long wait is over — the best augmented reality device on the planet is finally available.

Best known for its mobile phones and television sets, South Korea's LG has had a quieter presence in the US compared to the country's homegrown efforts.

In case you thought the long and unfortunate story of ODG was over, hold on, there's one last chapter to tell.

The story of Meta and its Meta 2 augmented reality headset isn't over, there's a new development that could impact its ultimate fate.

Mobile augmented reality pioneer Blippar has now completed its fall from hopeful AR startup to the immersive computing history books.

This week, saw two companies leaning on AR to prop up their financial futures. On one hand, Apple made quite a bit of AR-related news ahead of its quarterly earnings report next week. On the other hand, Vuzix launched a pre-order program for its Blade smartglasses and closed the largest financing deal in the company's history to fuel its ongoing headset production.

A Russian augmented reality startup wants the next frontier in real estate to be augmented reality estate.

For $0.25 per transaction, PayPal will soon be allowing you to transfer money through their app that will get delivered within seconds rather than days.

Toyota is testing blockchain and distributed ledger technology (BC/DL) for data sharing for driverless cars and other applications. This could eventually reassure buyers of its upcoming high-end cars by making sure their sensitive data is secure.

Updated 5/2/17: CultofMac reports analysts at Deutsche Bank are confirming the delays. The analysts believe the delays are due to "component shortages and technical challenges." This would corroborate the rumors listed below. We here at Gadget Hacks will bring you more on this story as it develops.