The results of Microsoft's $480 million contract with the US Army are on display and users continue to test the suped-up version of the HoloLens 2.

NetBIOS is a service that allows for communication over a network and is often used to join a domain and legacy applications. It is an older technology but still used in some environments today. Since it is an unsecured protocol, it can often be a good starting point when attacking a network. Scanning for NetBIOS shares with NBTScan and the Nmap Scripting Engine is a good way to begin.

Montezuma's revenge, the runs, the trots, or just diarrhea — everyone gets it sooner or later. What exactly is diarrhea good for, if anything?

A man-in-the-middle attack places you between your target and the internet, pretending to be a Wi-Fi network while secretly inspecting every packet that flows through the connection. The WiFi-Pumpkin is a rogue AP framework to easily create these fake networks, all while forwarding legitimate traffic to and from the unsuspecting target.

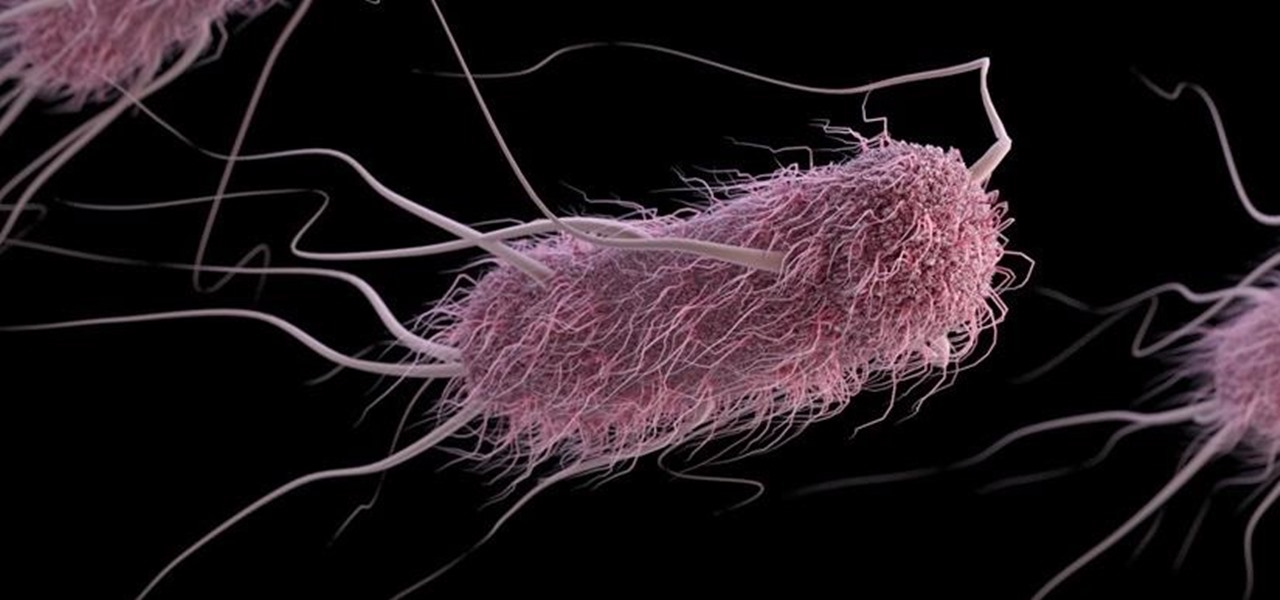
We know that healthcare-related facilities can be fertile ground for antibiotic-resistant bacteria, but recent research suggests your produce aisle might be too.

Move over whole wheat — white bread may be back in style after a new study shows that it may be your gut microbes that decide what kind of bread is best for you.

After California college student Luis Ortiz blacked out and was taken to the hospital in 2015, doctors were startled to discover the reason his brain was swelling—a one-centimeter long, wriggling tapeworm living within a ventricle in the middle of his brain.

A gold-medal winning entry into the iGEM synthetic biology competition could change the way we look at Esherichia coli, the bacteria better known as E. coli.

When to throw meat away is a common question, and one I often ask when faced with meat sitting in the fridge after a few days. With vegetables, you can usually tell on sight (or with this guide) when they're past due, but meat is not as simple.

While there are countless ways to welcome in the new year, many of them involve imbibing copious amounts of delightfully spirited libations. If you're anything like me, I know you're fearing the monster hangover on New Year's Day.

The food TV chefs prepare make our mouths water. From one scrumptious creation to another, they fly through preparation without frustration or error. They make us think we can do the same with similar ease and delectable, picture-perfect results. Some of us have noticed, though, that these TV chefs don't always adhere to the same safe food handling guidelines we've been taught to follow.

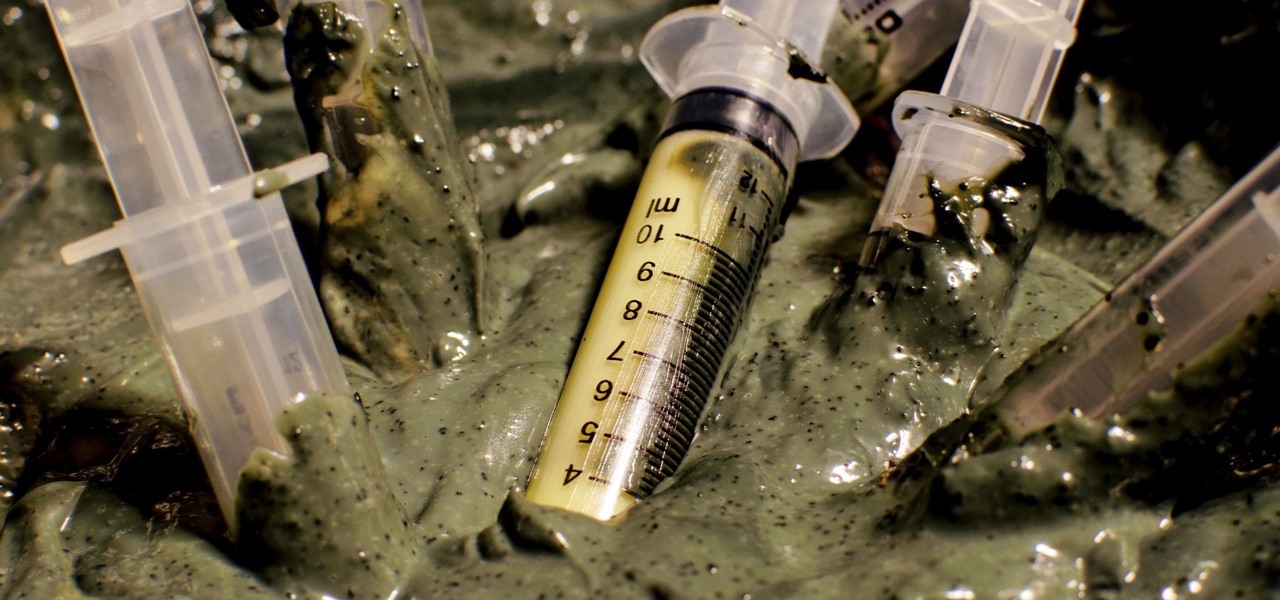
Bacteriotherapy sounds a lot more amenable of a term than "fecal transplant," yet they're both treatments that use bacteria itself to cure or treat infections. Fecal transplants, specifically, are an up-and-coming treatment option for a potentially deadly and difficult-to-treat diarrheal infection called Clostridium difficile.

Welcome back, my novice hackers! Previously in my "Spy on Anyone" series, we used our hacking skills to turn a target's computer system into a bug to record conversations and found and downloaded confidential documents on someone's computer. In this tutorial, I will show you how to spy on somebody's Internet traffic.

There are many tools out there for Wi-Fi hacking, but few are as integrated and well-rounded as Bettercap. Thanks to an impressively simple interface that works even over SSH, it's easy to access many of the most powerful Wi-Fi attacks available from anywhere. To capture handshakes from both attended and unattended Wi-Fi networks, we'll use two of Bettercap's modules to help us search for weak Wi-Fi passwords.

By using almost any packet-crafting tool, a hacker can perform denial-of-service (DoS) attacks. With the power to create just about any packet with any characteristics, a hacker can easily find one that will take down a host or network. Nmap and Hping are effective packet manipulation tools, but there's also Scapy, which is almost infinitely customizable.

Hashes containing login passwords are transmitted between Windows computers on local Wi-Fi networks. By intercepting and decrypting these hashes using Responder and John the Ripper, respectively, we can learn a target's login credentials which can be later used to gain physical access to their computer.

Knowing if your meat is cooked properly is both the difference between a delicious meal and an inedible one... and the difference between making your guests sick and keeping them safe.

Welcome back, my neophyte hackers! I have already done a few tutorials on password cracking, including ones for Linux and Windows, WEP and WPA2, and even online passwords using THC Hydra. Now, I thought it might be worthwhile to begin a series on password cracking in general. Password cracking is both an art and a science, and I hope to show you the many ways and subtleties involved.

Garlic—it stinks so good! It's one of nature's most wondrous foods, being both delicious and incredibly healthy. What's not to love? Well, it is kind of a pain to prep, whether you're peeling a couple of cloves for a sauce or a whole head and trying to mince it finely. One way to get around the whole peeling and mincing issue every time you want garlic in a dish is by buying pre-made garlic-infused olive oil, except that stuff is pretty pricey. Learn to make it at home and you'll get all the ...

Hello, all. In this article, I will be showing you how to make one of the most useful products known to man. I am talking, of course, about charcoal.

Router gateways are responsible for protecting every aspect of a network's configuration. With unfettered access to these privileged configurations, an attacker on a compromised Wi-Fi network can perform a wide variety of advanced attacks.

Over the past decade, Marvel Studios has been a dominant force at the box office, raking in more than $21 billion dollars. Averaged out over that span of time, the yearly earnings of those movies outweigh the gross domestic product of some countries.

The latest film addition in the American-produced Millennium series, The Girl in the Spider's Web, was just released on Blu-ray a few days ago. As you could expect, the movie has many hacking scenes throughout, just like the previous English and Swedish language movies centered around hacker Lisbeth Salander. Of course, with the quick pace of some scenes, the hacks can be hard to follow.

Smartphones are now indispensable when traveling. Domestic and overseas travel alike require food, navigation, translation, and so much more to make work or vacation successful. Gone are the days of lugging multiple tourist books around with you everywhere you go — you need to let your smartphone handle the dirty work.

Tuna is said to be bad for cats, but it also has toxins that affect humans, too. If eaten in large quantities, you could contract mercury poisoning or worse. But why subject yourself to that when you wouldn't even feed tuna to your kittens? Because it tastes good? Well, you can get that same great taste without any fish! Watch this recipe to learn how to make a tuna salad, full of vegetables and the secret ingredient— hijiki— a delicious fresh-from-the-sea flavor sold in dried black strips.

New Year's Eve. It will be one hell of a chaotic night. Trust me. The overcrowded streets. Long lines for the urinal. Maxing out your credit card on that shot of Cuervo. You'll be lucky to make it out alive.

You're lost. You're cold, thirsty— you're hungry. What if you're not much of a hunter? Maybe you're a gatherer. So, then you'll eat plants. But what if you eat something poisonous? What if you're allergic to it?

Is the Iron Curtain achievement in Assassin's Creed: Revelations getting you down? Well here, have an easier one to try out. The 'Mosh Pit' calls for ten guards to be poisoned at the same time. Do that, and you'll net a cool 20G on Xbox 360, or a bronze trophy on PlayStation 3.

SSL stands for Secure Socket Layer. It's an encryption standard used on most sites' login pages to avoid their users' passwords being packet sniffed in simple plain-text format. This keeps the users safe by having all of that traffic encrypted over an "https" connection. So, whenever you see "https://" in front of the URL in your browser, you know you're safe... or are you?

Would it have been possible to build a rudimentary telegraph network in the stone age? Not too long ago, Jamie O'Sheathe of the Office for the Development of Substitute Materials set out to discover just that, venturing into the wilderness to determine whether a working telegraph might be built without the use of modern tools. Inspiring? Certainly. Green? Don't be fooled:

Great Cleaning Products that Won't Leave You Feeling Dirty!

Hey Everyone! Welcome to my post. We have seen a numerous GUI Tool in kali linux. Armitage, wireshark, Burpsuite etc,. Lets see an another GUI tool.

If you haven't had a pile of pipe and fittings to play with before, it's hard to see what is so cool about a plain, plastic pipe. All it does in the house is carry the poop away. Really, who cares?

Torus knots are beautiful knots formed by wrapping a line around a torus and tying the ends together to form a loop. The resulting knot has a star-like appearance when viewed from above. The 36 examples with the least number of crossings can be seen at the Knot Atlas's page on torus knots.

In mathematics, a knot is a closed circle in a three-dimensional space that crosses itself multiple times. Since it is closed, it has no ends to tie, meaning you can't actually create such a knot. However, if you tie the ends together after you create a knot in the standard way, you will have something that is close to the mathematical description. In this post, we will explore the creation of mathematical knot sculputures using copper tubing and solid solder wire.

DO NOT eat a berry if you cannot identify it. I decided not to include the obvious blueberries, blackberries and raspberries, but this guide will assist you in identifying which wild berries are, in fact, poisonous.

I have had a lot of people ask me, "How does my neighbor keep getting into my wireless?!". Chances are, these people are all using WEP, a deprecated wireless encryption protocol. Either that, or you are using one weak WPA passphrase.
Long-Term Strategies for FrontierVilleWhen you first start to play FrontierVille, after you’ve cleared a bunch of trees and brush and started to build a schoolhouse or a barn and you’ve added a few neighbors, you look up at the people around Level 90 or Level 100, and wonder how they play the game and how they got that far.There’s a book (or a series of four books) you may notice – FrontierVille Tycoon Guide – that promises to tell you the secrets of the high level players. You can buy it on ...

Computer viruses are terrifying. They are undetectable, dangerous, and operate constantly right under your nose. For the average computer user, there are only a few repair options. You could buy expensive antivirus software that causes more problems than it fixes, you can wipe your hard drive clean and lose all of your important data, or if all else fails—just switch to Linux.

Sometimes mining and crafting gets boring. The thrill of hunting mobs, exploring strongholds, or the Nether is often much more satisfying and appeals to the RPG nerd in all of us. Well, Mojang took the hint and as part of the 1.9 release, there will be potions, more mobs, other worlds, and enchantments added to the game. To preview this release, read my tutorial on how to download and install 1.9.3.