In this tutorial, learn how to use your Facebook Fan Page to comment and write on other people's walls like you would a personal account. Your fan page is linked to your personal page, and sometimes you don't want to use your real identity to write messages. Check out this clip and get the hang of a FB glitch that will allow you to "tag" your friends so you can write on their walls.

Companies spend millions on advertising every year, wouldn't it be great to get some of that money? Well you can. Adding ads to your personal blogs can really bring in revenue for an at home business, or just for yourself. This video will demonstrate and explain how to make money from your personal blog with ads.
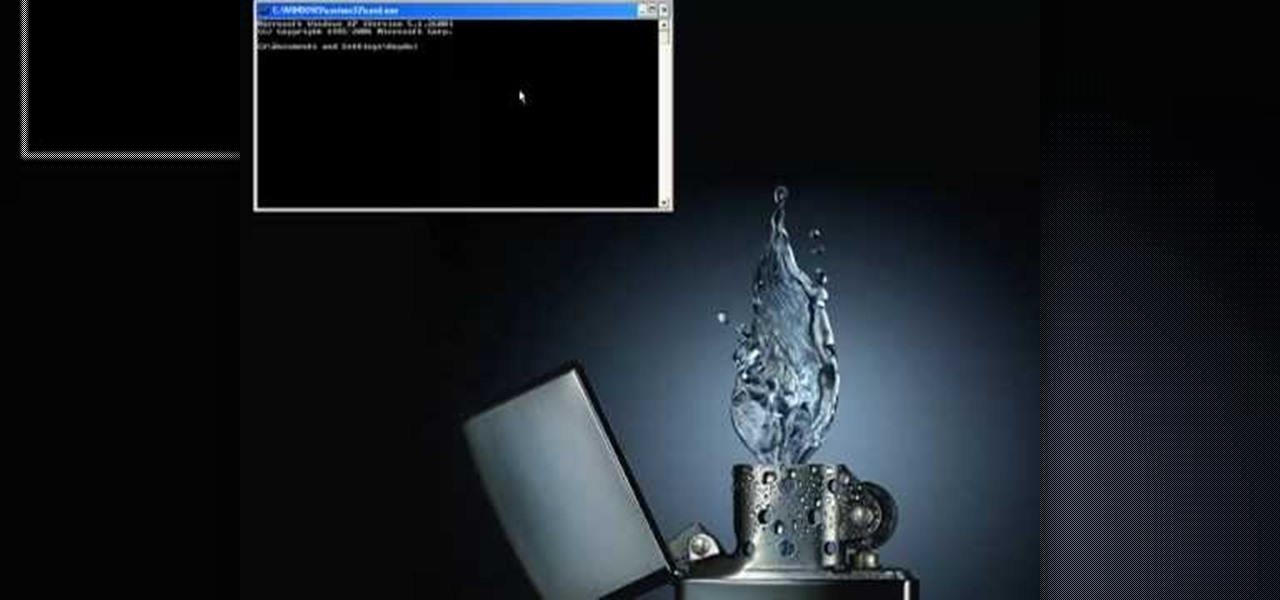
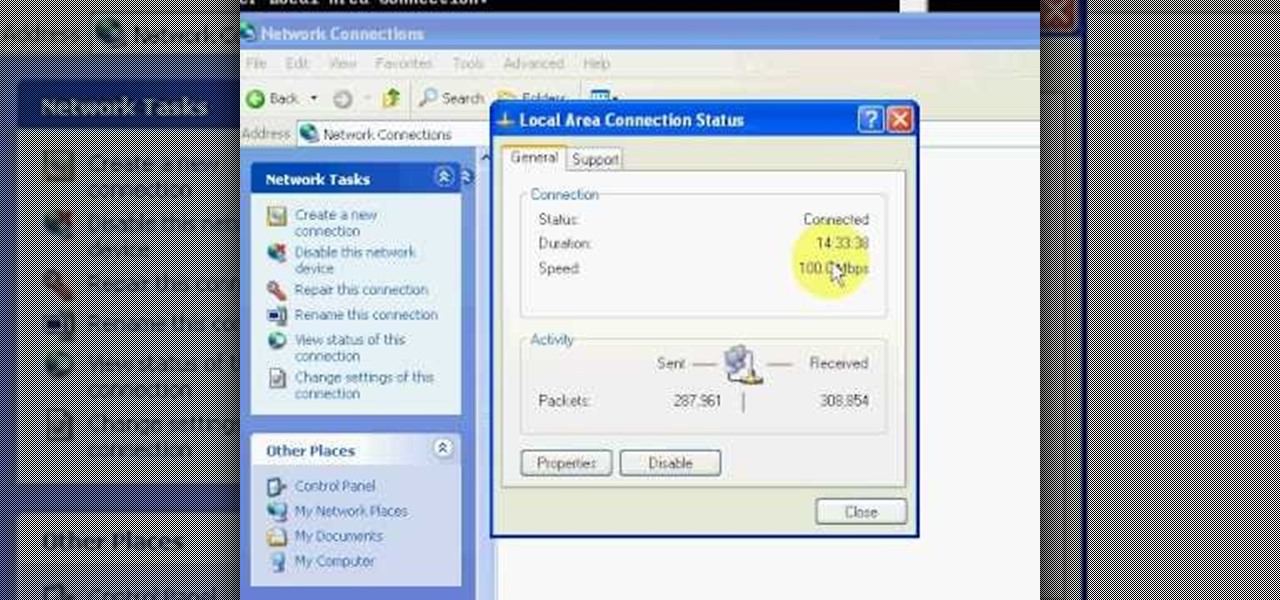
In this video Guides4tech teaches the secrets of finding your local IP and MAC address in simple steps. First click 'Start' and select 'Run' on your computer. Now type 'cmd' to open the command prompt. In the command prompt type 'ipconfig/all' and press 'Enter'. Your IP address will displayed under the 'Ethernet adapter local area connection' menu. Your MAC address will be displayed as 'Physical address' under the same menu.

Learn how to change your IP address using a Linksys router in simple steps. First search for your IP address in the internet and find it from any of the websites available. Now go to your Linksys setup page by accessing it with your username and password. Go to Mac address code and change the last set of digits by increasing or decreasing a value. Now save the settings and reset your modem and router. Finally check your new address to finish.
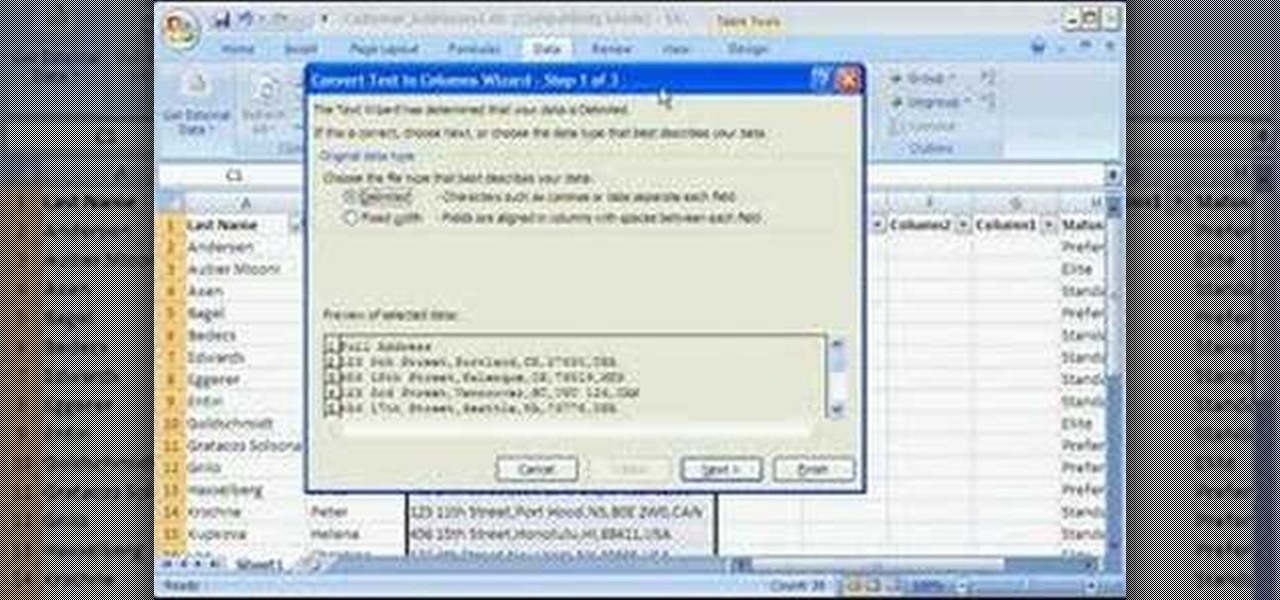
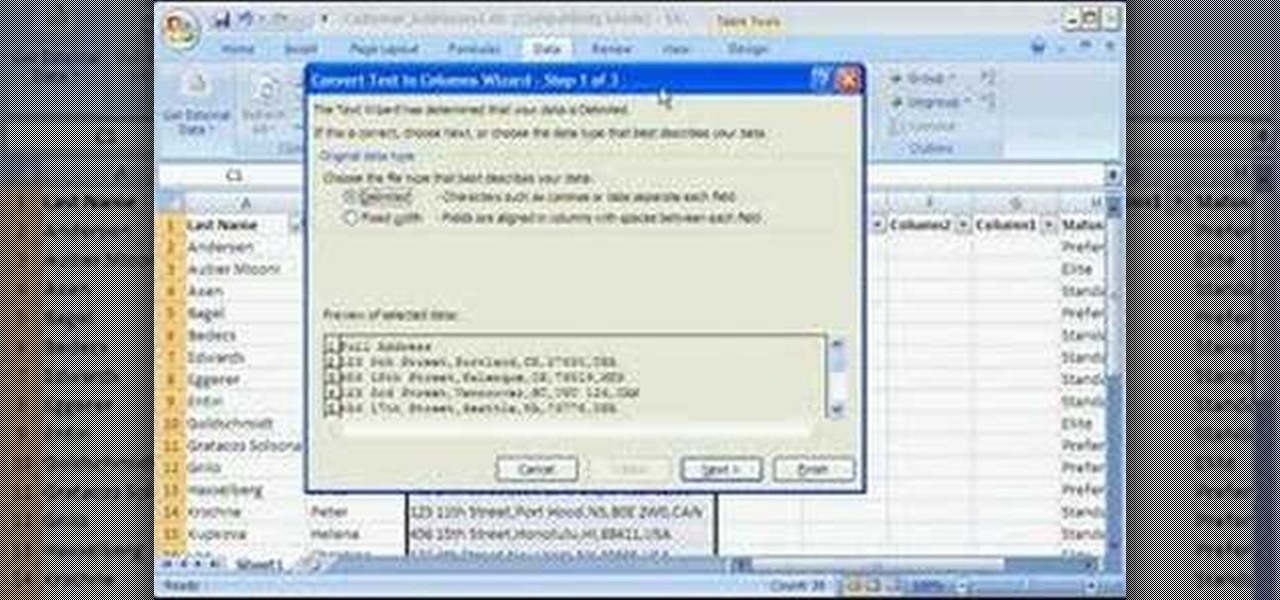
Storing information, such as a full address, in one column can limit what you can do with that information. For example, you can't easily filter or sort by part of the address, such as country/region or city. However, if you break up the address into its parts — street address, city, state/province, postal code, country/region — one for each column, you can remove those limits. Watch this instructional video to see how to use the Convert Text to Columns Wizard to automatically break up a sing...

Learn about assigning static IP addresses to a Windows 2003 server - a good idea if your server is constantly changing its IP address because of your DCHP server.

The easiest way around a security policy is to find users who don't follow it. The Have I Been Pwned database identifies accounts with information breached by major third parties like Yahoo and LinkedIn. With Maltego, hackers can locate breached accounts created using company email addresses, potentially giving attackers access to a company account if the employee reuses a compromised password.

Most of us skip through documents like privacy policies and EULAs (end-user license agreements) because they're long and boring. But, as Congress just passed the SJR34 bill in early April, you're probably a little concerned about your personal data, so we summarized the privacy policies for major ISPs and mobile carriers in the US.

Welcome back, my greenhorn hackers! As expected with Null Byte's dramatic growth over the last year, we have added many new aspiring hackers who are still lacking in the basics of networking. In addition, with the new "White Hat" certifications coming out shortly, the exam will require some basic networking skills and knowledge to pass.

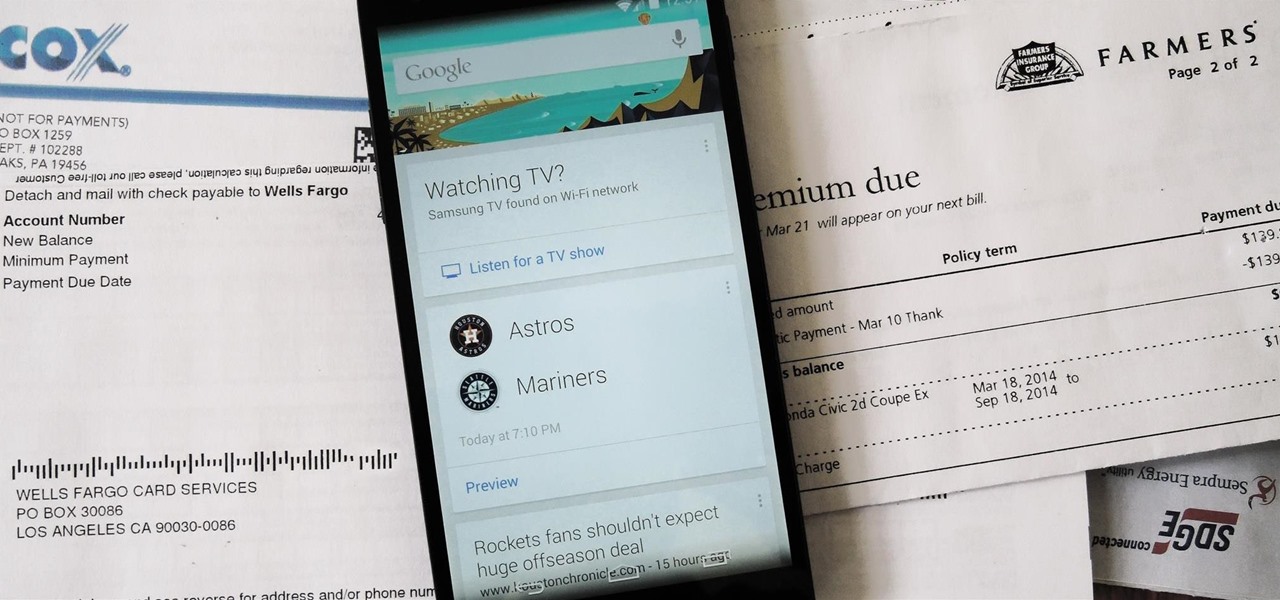
Google Now is a quick and intuitive way to tailor your device to work for you and, unlike other personal assistants, provide you with up-to-date information based on search habits, emails, and the general all-knowingness of Google.

Starbucks' app is the most used mobile payment app in the U.S. because it's well-designed and convenient. But if you use the iOS version on your iPhone, your username, email address, password and location data could be compromised because the app stores them in plain text.

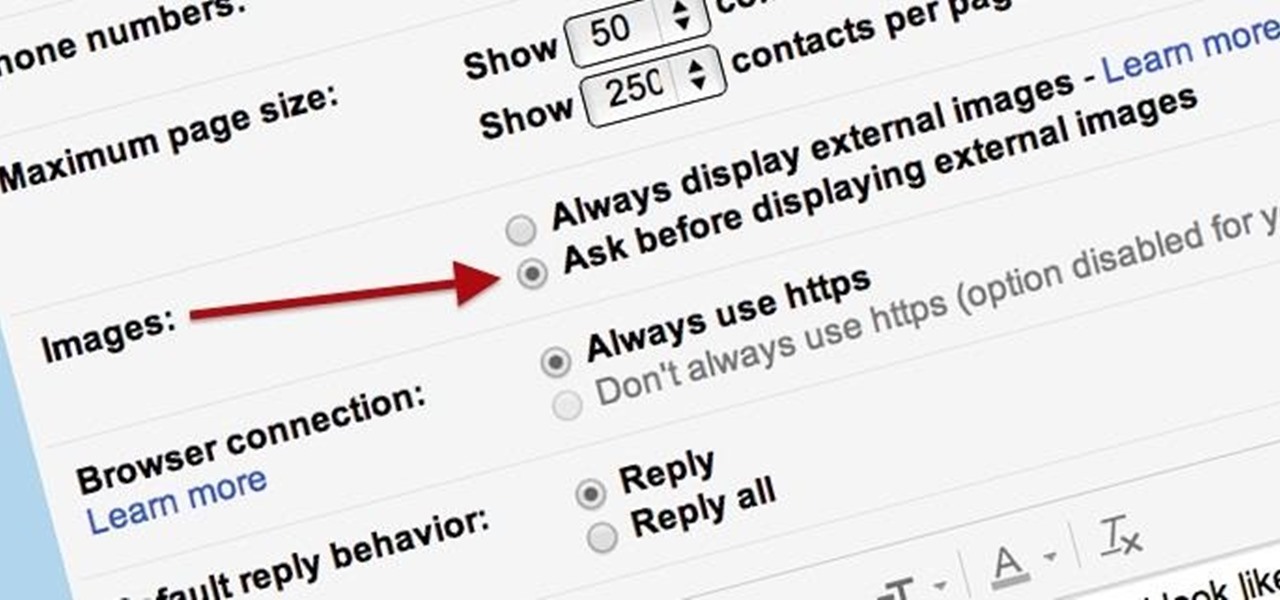
Securing your email address is one of the most important things you can do on the internet. Hackers, spammers, and overly aggressive marketers can turn your Gmail inbox into a heap trash if you're not careful.

While there were many highlights during Apple's keynote address at WWDC this year, the new advancements to the sassy personal assistant Siri in iOS 7 were amongst the most talked about—and something I was eager to test drive myself. Currently, there are ways to improve Siri in iOS 6, like making her play Spotify music or adding more commands, but those aren't easy tasks.

Alright BlackBerry users, it's time to wipe all that information before you sell, or pass on your BB to someone else. This simple how-to video will let you wipe it all, simply and easily. If you desire you can also choose to leave in your sim card and wipe the contents of that as well. The tutorial hose will guide you you step by step on how to remove your personal information from your Blackberry 8350i Curve. This instructional video is a simple but very detailed tutorial that instructs you ...

For most of us, working out at the gym is a time we have to schedule outside of our other work and family commitments. But how about making exercise your job? No, we're not talking about becoming a pro athelete. Rather, if you become a personal trainer you can work out, help others work out, and get paid good money while doing it.

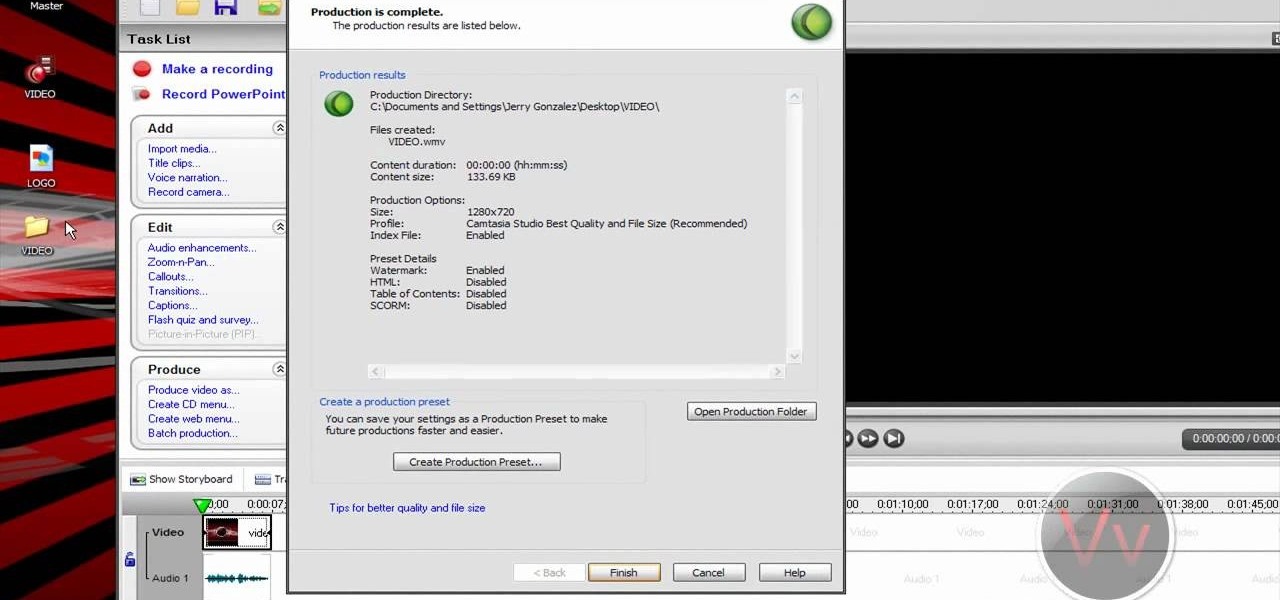
A watermark is like attaching your own personal sigil to a video clip. Camtasia Studio 5 offers a watermarking function you can add to your own projects. This tutorial demonstrates how you can create a watermark, and then add it to the videos you want to mark.

In this clip, you'll learn how to locate the Outlook personal storage folder when, for example, migrating between Outlook 2003 & 2010. Whether you're new to Microsoft's popular email application or are just looking to pick up a few new tips and tricks, you're sure to benefit from this free video software tutorial from Lynda. For more information, including detailed, step-by-step instructions, take a look.

Create your own personal seal from a piece of clay! This tutorial shows you the process, starting with a large piece of smooth clay, to cut your chosen sigil into the clay. Make sure you draw the sigil on in reverse. Now all you need is a letter and some sealing wax!

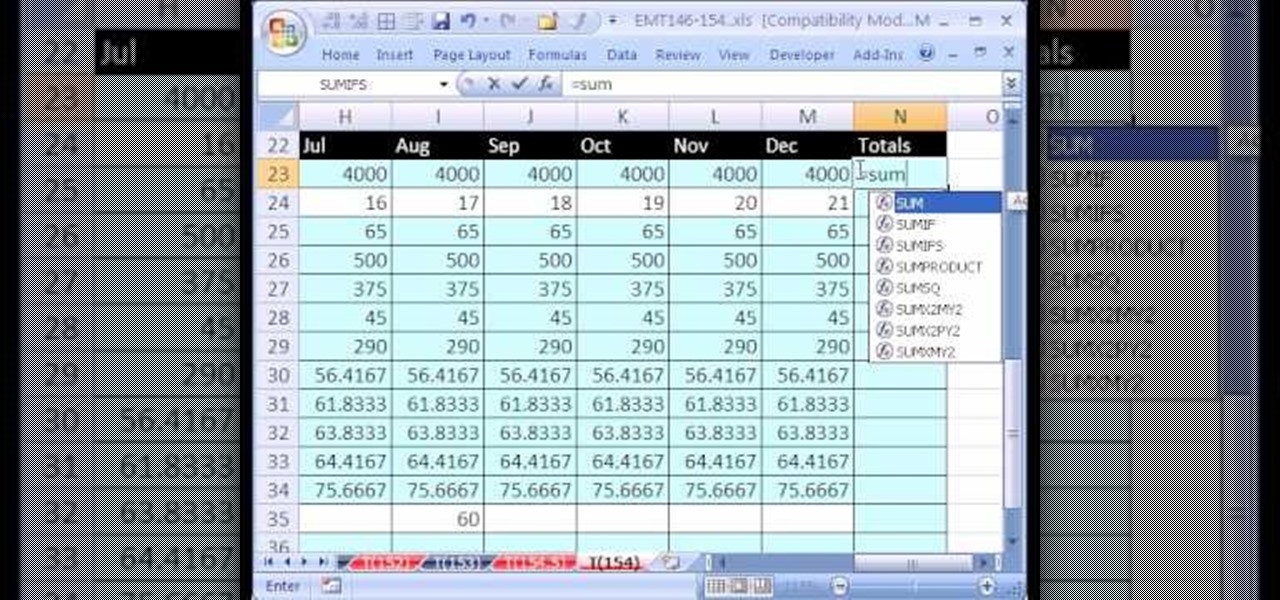
New to Microsoft Excel? Looking for a tip? How about a tip so mind-blowingly useful as to qualify as a magic trick? You're in luck. In this MS Excel tutorial from ExcelIsFun, the 154th installment in their series of digital spreadsheet magic tricks, you'll learn how to create a personal budget based on past data via the SUM function, cell references, subtraction and the VLOOKUP function.

Having problems with your anti-virus software on Windows? Learn how to remove the fake virus protector Personal Antivirus! Personal Anti-Virus is NOT a legitimate anit-virus software and will use spyware to steal info from your computer. Personal Anti-Virus is hard to get rid of and is totally annoying. To get rid of it, you don't have to download anything.

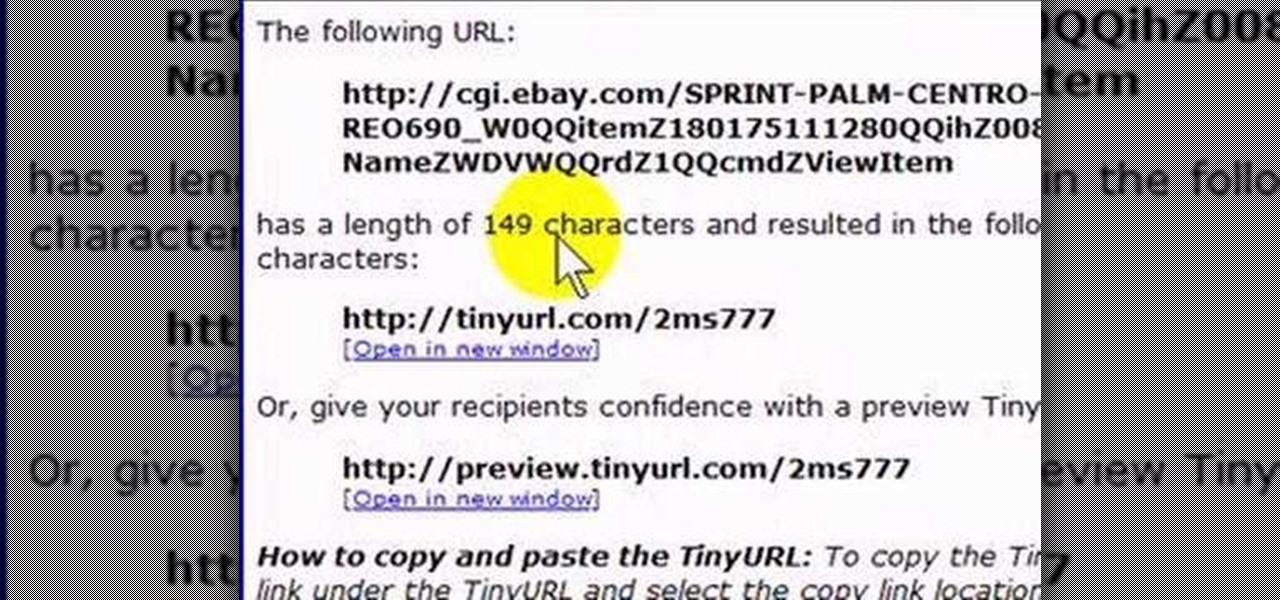
If you like to share websites via email, are a writer who needs to share email in her stories, or just need to make a quick written note of a website address, you need to know how to use web address shorthand. Some URLs can be hundreds of characters long and therefore too tedious to reproduce in writing. To make an easier-to-communicate link, you'll need to use a URL minimizer, like TinyURL. Learn how with this address-minimizing how-to!

Need to change your IP address? In this how-to, you'll find instructions for changing your IP address from the Windows command prompt with the ipconfig console application. For step-by-step instructions, take a look. NB: Changing your IP will not protect your identity; it's merely a simple expedient for getting around certain problems ones might encounter while using the Internet.

In this tutorial, Gary Rosenzweig of MacMost.com takes a look at two tiny, but nevertheless very useful, Web services. The first, tinyurl.com, will take a long Web address and shorten it to make it easier to send in email. The second, http://tinymail.me, will hide your email address. For more information consult this great how-to.

This video tutorial will show you how to hide/change your IP address so that you can bypass websites that have blocked your IP address or so that you can surf anonymously. The websites used in this video are cmyip.com

You’ve been blogging your fingers off for a few years now, and despite the ego rush of watching your hits soar, you’re wondering what’s the point—or, rather, how do I make some cold hard cash from this thing? Learn how to make money off of a personal blog by watching this video tutorial.

Many people have personal trainers in the gym. What about personal trainers for you entire life? Many celebrities hire life coaches to help them fix their lives. What do you do when you can not afford one? Watch this video tutorials for tips from a celebrity life coach on how to create big dreams and start living them.

Do you want to learn how to make your own, personal wrestling ring? Watch this video tutorial to learn how. You will need a trampoline, rope, small PVC pipes, electrical tape and steel metal poles.

In general, hacking and information security is not just one discipline, but a number of them, and today we will look into some of the networking concepts.

This video will show you how you can easily find out what your IP address is for a computer which is running the Windows XP operating system. You will first need to go to the start bar and click on the button which says "Run". Choose to run a program called "cmd" by typing this into the bar that appears. This will then open up a black box, where you should type in "ipconfig/all". Typing this in will offer you a list of information about the internet service you are currently using and one of ...

Now you can find your IP address if you need it and you don't know it, it very easy. Or if you have problem with a person on the internet, now you can discover who that person is. You can find her/his IP address and after that you can find her/his real name. But after you find the IP that you were looking for, you have to check if the person who own this computer is in your network, because if you want to find his/her name, the program works only if the owner is on your network. So if you are...

Check out this instructional language video to learn how to address someone in Russian. Learn basic Russian grammar with Viktor Dmitriyevich Huliganov in his 2nd lesson. Some other objectives in the lesson include 1a verbs and common adverbs. Watch this tutorial video that is great for language nerds and advanced Russian speakers who need to polish their skills or looking to improve their proficiency in Russian.

You may not know it, but the IPv4 address of your computer contains tons of useful information about whatever Wi-Fi network you're on. By knowing what your IPv4 address and subnet mask are telling you, you can easily scan the whole network range, locate the router, and discover other devices on the same network.

Google is widely renowned for its mastery in using data to tailor specific search results and ads. Their Android and iOS search apps put this ability to use in finding the most relevant pages for your query, and their desktop site is the most-used search engine on the web as a result of it.

One of the most frustrating things on the Internet are sites that make you register just to view content. I'm not talking about paywalls—I mean the sites that make you give them personal information to look at free articles or forum threads. Most people are uncomfortable with this because a lot of these sites either spam you themselves, or sell your information to someone else who will.

MAC addresses (not to be confused with Macs) are unique identifiers assigned to network devices in order to access the internet. Hotels use these Mac addresses in order to check if a registered patron has agreed to their terms and conditions, how much bandwidth is being consumed, and of course, whether they've paid or not.

The convenience of storing things on the cloud can definitely make life easier, but if you're storing sensitive files, it could be a total disaster if anyone hacked your account. Some encryption services can be expensive, but if you just need it for personal use, there are some really great ones that don't cost anything. Here are three programs that let you encrypt your cloud storage for free. BoxCryptor

In this video, we learn how to find your IP address with 3 different methods. First, go to the bottom of your screen and click on the computer icon you see. The next way is to go to WhatismyIP. When on the site, you will be given your IP address. The last way is to go to start, then run, and type in "CMD". Now, type in "ipconfig" and press enter. Once on here, you will be given your IP address. All of these will give you the same number, just use whichever option is easiest for you to use!

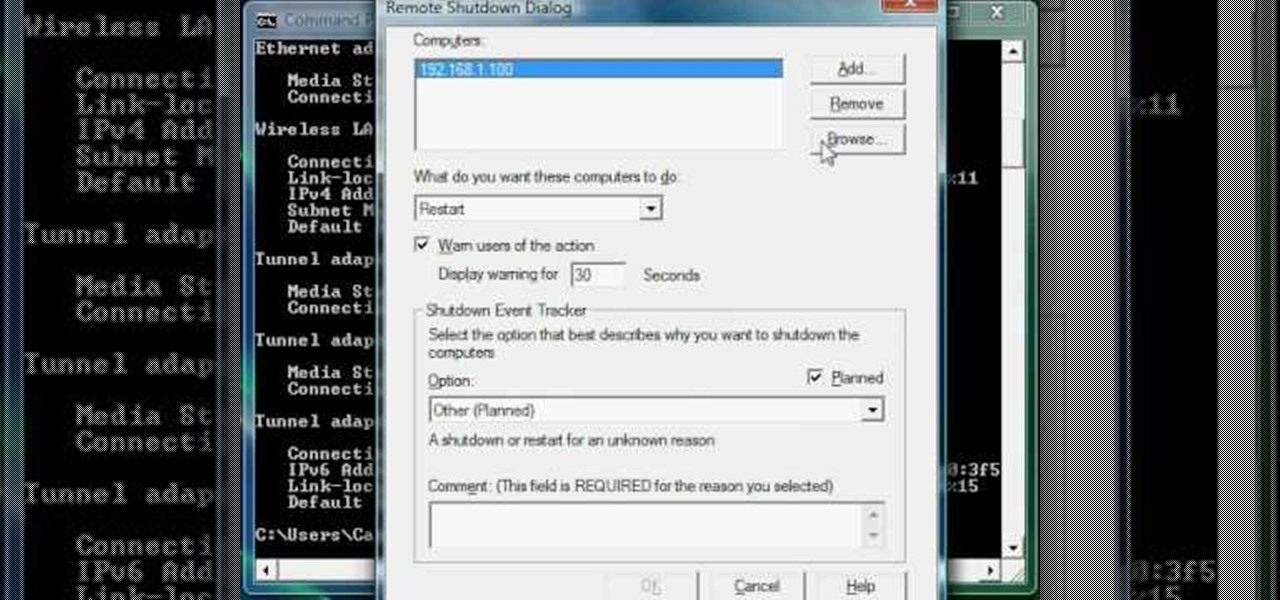
In this Computers & Programming video tutorial you will learn how to hack into a compuuter, the easiest way. Go to start > run, type in ‘cmd’ > OK. To find the IP address of a website, type in ‘tracert myspace.com’. This example is to find IP address of myspace.com. Then all the IP addresses of the website will be displayed. If you want to shut down a computer, now you type in ‘shutdown’. A remote shutdown dialog box will open up where you put in the IP address. That’s all. The ...

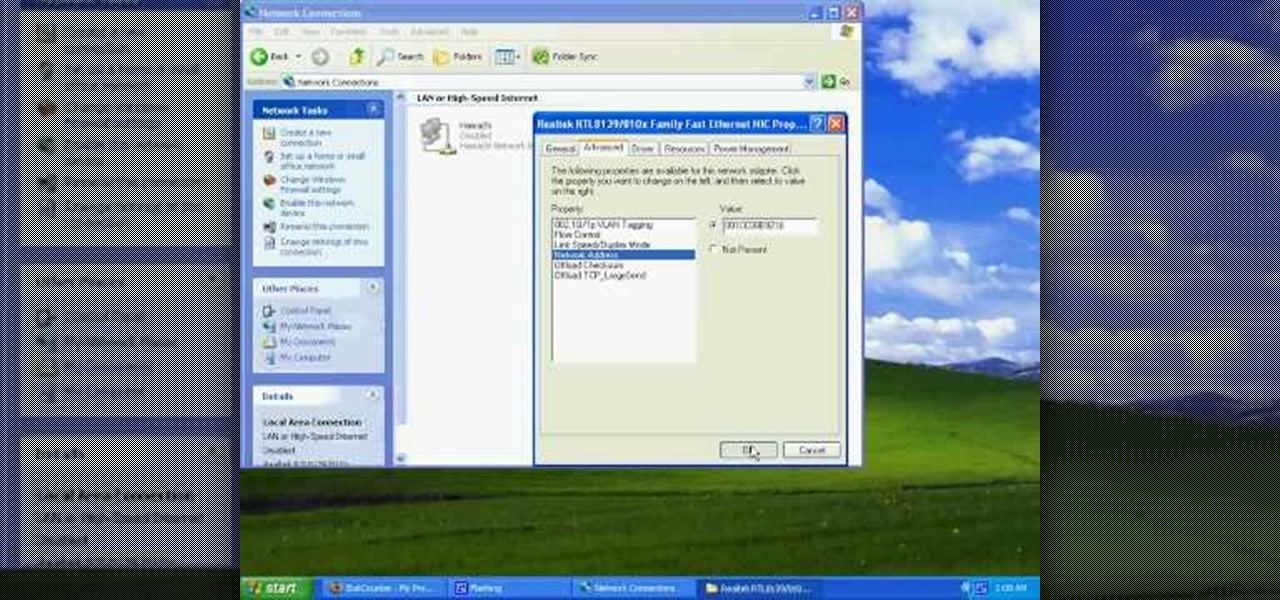
This video tutorial from tarunkumarsinghal shows how to change Mac address on Windows XP. Click Start menu and then Control Panel. Make sure control panel window is in classic view mode. If not, change it to classic from the left pane.