
How To: Decode VNC passwords with Cain
Hack a network computer by decoding Virtual Network Computing (VNC) hex passwords with Cain.


Hack a network computer by decoding Virtual Network Computing (VNC) hex passwords with Cain.
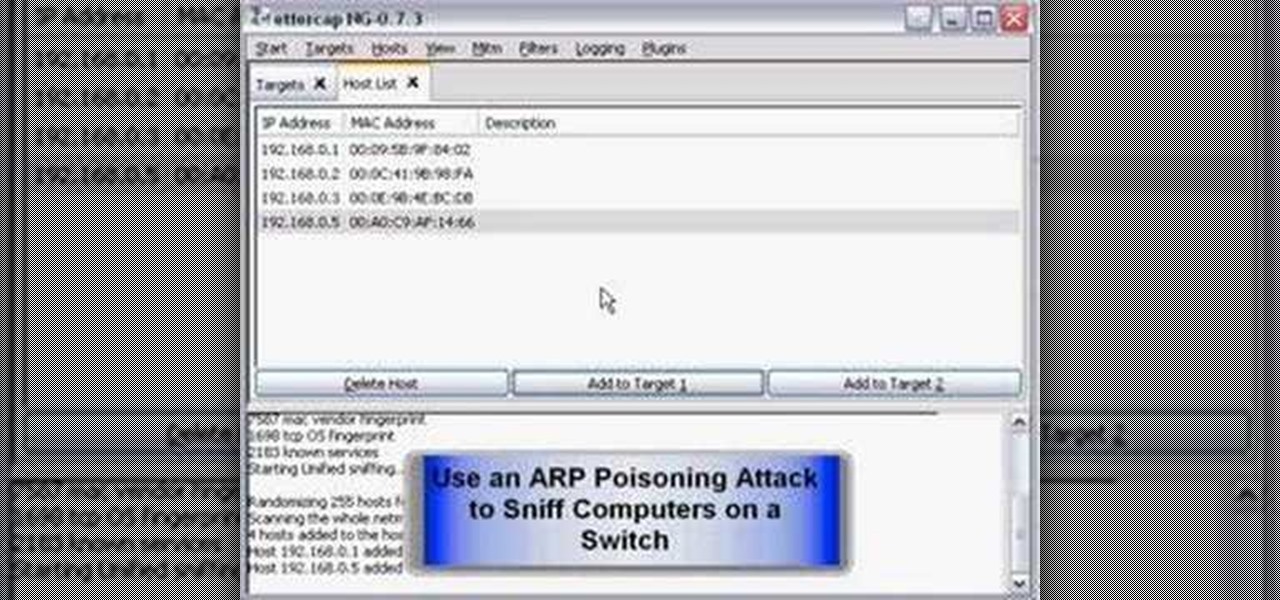
How to hack a network by sniffing passwords with Ettercap software.
With this useful video, you will learn some tips and tricks about how to delete your web browser history, passwords, cookies, also cache form data and temporary internet files.

If you have not used your eRecovery system in a long time and have forgotten the password, have no fear. This video is here to help you retrieve your details and use your program again. In this clip, learn how to recover any lost passwords with Acer's eRecovery Manager for Linux.
There are loads of reasons for somebody to want to recover a Windows password, and there are lots of different ways of doing it. My favorite of all of these ways is to use a piece of software called Ophcrack because:

A flaw in WPS, or WiFi Protected Setup, known about for over a year by TNS, was finally exploited with proof of concept code. Both TNS, the discoverers of the exploit and Stefan at .braindump have created their respective "reaver" and "wpscrack" programs to exploit the WPS vulnerability. From this exploit, the WPA password can be recovered almost instantly in plain-text once the attack on the access point WPS is initiated, which normally takes 2-10 hours (depending on which program you use).

Check out this computer hacking video tutorial from Unorthodox Hacking. The subject of today... hidden Windows passwords. This is a short episode with a fast pace is intended to expose a few of the areas where Windows hides stored authentication credentials. Be very cautious the next time you use a public kiosk!

Hello to you all I've been reading for a long time now and haven't seen anything about this vulnerability so i thought id post it to make sure it was here
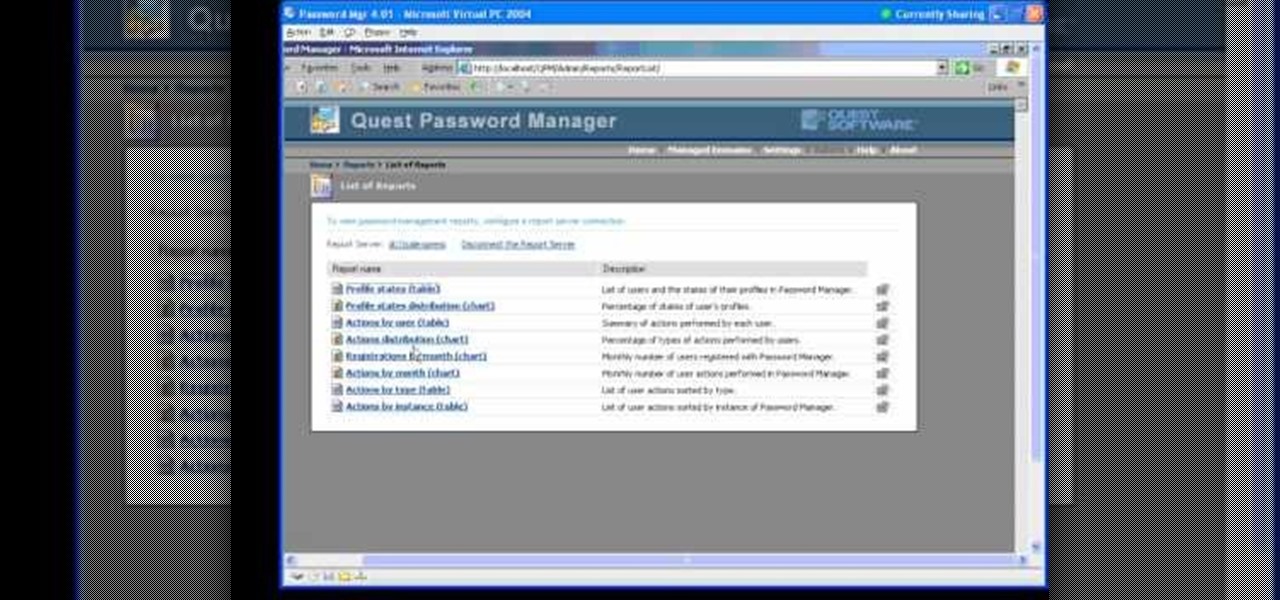
In this Webcast, Password Management for Windows and Beyond, you will learn how to: Increase security standards cross-organization by easily customizing and enforcing password policies for Windows, Unix, Linux, and Java users.

Been hacked once? Twice? Maybe more? You thought abc123 was the only password that is both 6 characters wide and easy to remember? I have some suggestions in store for you. Just read on...
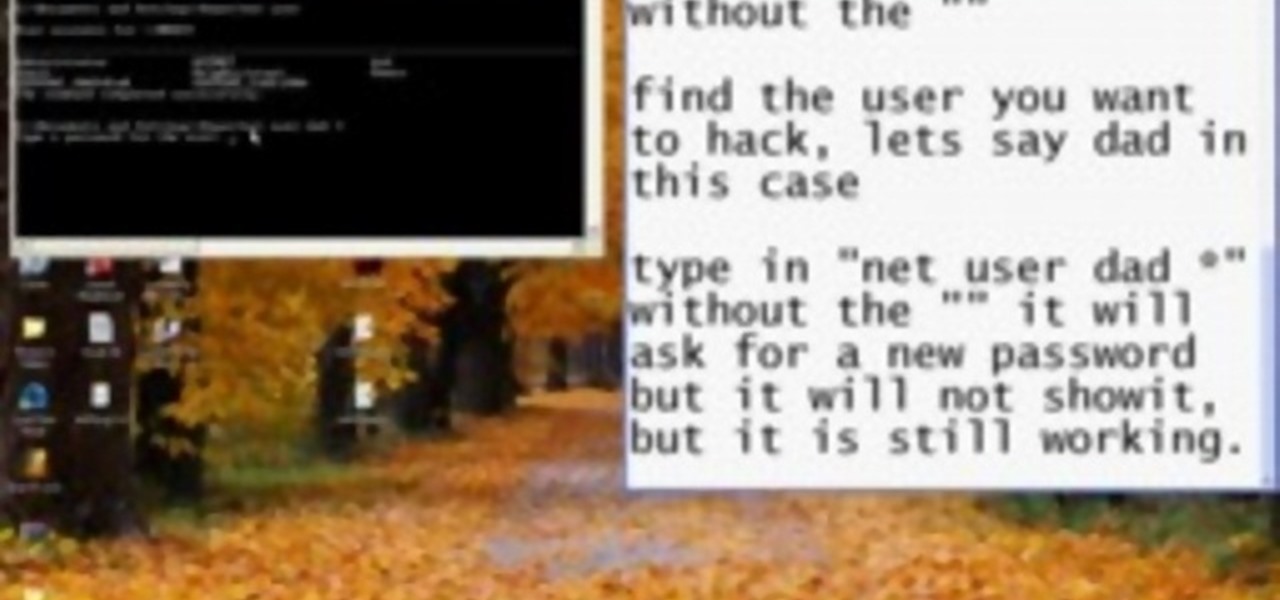
Use the cmd prompt to change passwords of users on a Windows XP computer.

I've seen numerous tutorials on how to create a "strong" password. This makes me laugh. These titles imply "one" password, which is wrong in and of itself. A person should have many passwords, all different, and all extremely long. People may ask how they're supposed to remember lengthy passwords and why their current password isn't good enough. Well, I'm going to show you.

I've previously mentioned how saving browser passwords is a bad idea, but I never went into much detail as to why. Passwords that are saved in your browser can be carved out and stolen very easily. In fact, even passwords you save for instant messaging and Wi-Fi are vulnerable. Windows is very inefficient with the way it stores passwords—it doesn't store them in key-vaults, nor does it encrypt them. You're left with passwords residing in memory and filespace that's unencrypted.

Movies like to show hackers breaking passwords with fancy software and ludicrous gadgets. The reality of busting passwords open is much more mundane. Simple as it may sound, most passwords are broken purely by guesswork. Check out this infographic from ZoneAlarm, as well as this list from the Wall Street Journal of the fifty most common passwords gleaned from the 2010 Gawker hack. If your password is on one of those lists, you need to change it. Right now.

This past Sunday, a group called Gnosis launched a massive hacker attack on Gawker media, one of the web's most popular blog networks (Lifehacker, Gizmodo, Jezebel, io9, Jalopnik, Kotaku, Deadspin and Fleshbot). 1.3 million registered users' passwords were compromised, and 188,279 of them were decoded and made public. The biggest takeaway? Many Gawker denizens use downright dumb passwords. (Guess they didn't see their own Lifehacker's story on avoiding such a thing.)

How to Crack Passwords Faster by Putting Your GPU to Work with HashcatSecurity on the internet is always changing. Not too long ago, having a 10 character password meant that you were safe from all forms of hash cracking. Hash cracking is when you take a string of characters that have been passed through a cryptographic hash and try to reverse them. The normal processors that are housed inside of our computer cases are general purpose. The processors are not meant for handling complex math an...

Lifehacker posts an article on the art of cracking weak passwords, courtesy of Internet standards expert, CEO of web company iFusion Labs, and blogger John Pozadzides. Pozadzides certainly knows a thing or two about password logic. (Note: this information is not intended to hack into accounts, but rather to protect you from using weak passwords).

Developers have created many tools for testing the strength of passwords (1, 2); there are also plenty of tips for coming up with a strong password in the first place. But why do the grunt work when an app could generate a perfectly secure one for you?

More password cracking action from Null Byte! Today we aren't going to be cracking passwords per se, rather, we are going to learn the basics of generating rainbow tables and how to use them. First, let's go over how passwords are stored and recovered.

You may have asked yourself, "How do hackers take my password, if the website owner can't?" The answer is simple. When a website stores your login password for the site, it is run through a cryptographic hash function before it enters the database (if the website isn't Sony).
JavaScript is the language of the internet. It is what allows us to create dynamic, interesting webpages that are fast, web-based applications and so much more. The primary use of JavaScript is to write functions that are embedded in or included from HTML pages and that interact with the Document Object Model (DOM) of the page. This is the magic that allows all of what we see to happen, and for our browser to be manipulated.

If you're interested in bypassing Windows and Linux passwords, there is a great tool from the good people at Kryptoslogic. Have you ever forgotten your administrator password? Have you ever bought a used computer with a password on it? Well, Kryptoslogic have created a boot-disc call 'Kon-Boot', which allows you to bypass any Windows 32 or 64 bit OS, as well as Linux passwords. There is both a paid and freeware version available.

This Null Byte is a doozey.

Archiving and compression is a great way to store and prepare files for sending. You can reduce the size of a file, turn a group of files into a single file, and even encrypt and password the contents! Just take a look at this image to see how much it compressed a 28GB text file.

Have an old-school tabula recta lying around? No? Then just print out the chart below. Nothing ensures better password security than this centuries-old cipher technique. Here's how it works, via Wikipedia:

Permanently deleting files is something that a lot of people aren't aware of. Actually, most people think that once a file is deleted, it is gone forever. This is not the case. Hard drives write to the disk via magnetic charges, positive and negative correlate to 1s and 0s for binary. This is then interpreted into information for the computer to use and access.
For the people who think "P3nC1l5" is a good password. http://packetstormsecurity.org/files/view/31979/31337_speak.gz

Here at Null Byte, we've spoken a lot about securing and anonymizing traffic. This is a big deal. With all of today's business taking place electronically via computers, we need to be secure when on-the-go. A lot of businesses don't even train their employees to secure their computers to protect from various threats. Here are a few things that should always happen when doing business on computers:

Leaving your wireless router at its default settings is a bad idea. The sad thing is, most people still do it. Once they've penetrated your network, hackers will change your router settings so they'll have an easy way back in. This allows them to change your network into a shell or proxy so they can forward their traffic anonymously through you when committing other dirty deeds.

How to administrate and manage user accounts and passwords in Windows XP. Add, delete, and change Windows passwords using CMD.

This is a little xp password cracker I'm going to show you how to get and use. Hack Windows XP passwords with a password cracker.

How to use Cain & Abel software to intercept passwords from an unsecured network. Intercept network passwords with Cain & Abel.

What's the easiest way to keep track of your website passwords? Maybe in a password-protected document on your computer? Makes sense.

Looking for instructions on how reset passwords on a Windows XP? With Winternals ERD 2005, it's easy! So easy, in fact, that this home-computing how-to from the folks at Britec can present a complete overview of the process in just over five minutes. For more information, including step-by-step instructions, take a look.

In this screencast from screencast central we look at how you can add passwords to your files and folders quickly and easily for free.

From email to online banking, you never want someone poking around in your personal information. Learn what to avoid when creating passwords, and try these tips to keep your passwords safe and secure.
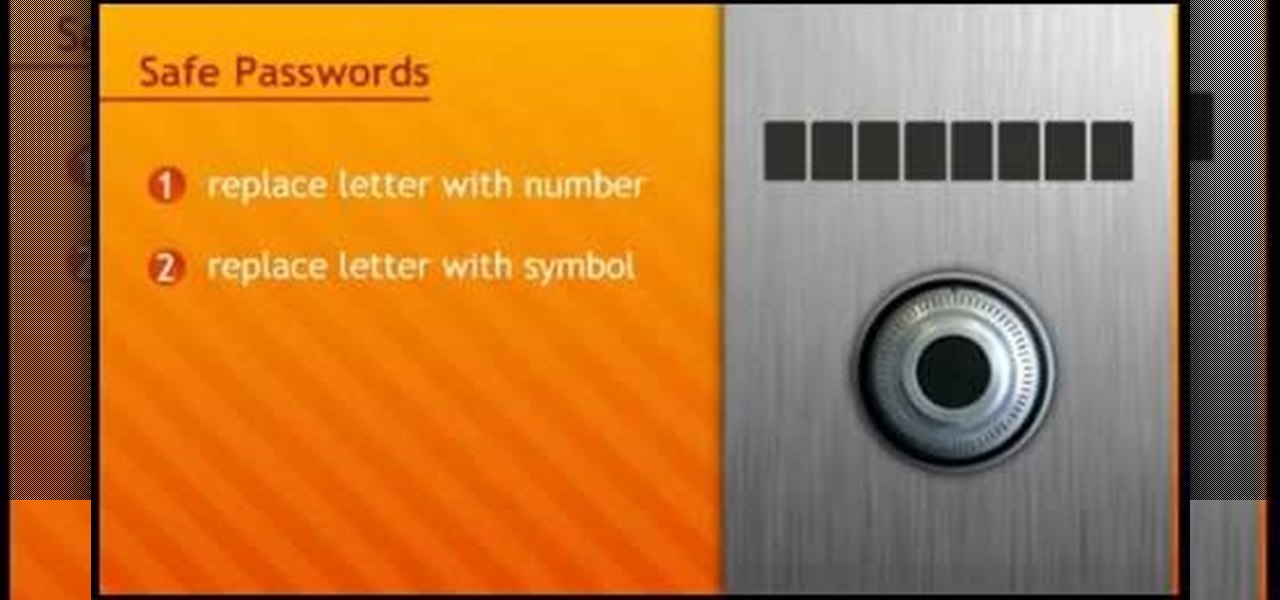
In this tutorial, we learn how to make a safe password. Passwords are essential, and need to be safe for when browsing around the internet. Other people aren't meant to be able to nose around your information, so protect your information with an indecipherable password. Don't choose a password that is easy to crack, never use personal information. A random number in the phone book isn't a good idea either, software used by hackers can crack these. Make sure your password is 8 characters long ...
Hacking into computer systems to steal passwords could be a bit complicated for the average everyday joe, but for all of your tech illiterate folks out there, there's any easy way to get that password, and all it takes is a camera.

We've all seen this warning message at one time or another while playing around on the internet in the Mozilla Firefox web browser:

To name just a few companies, VK, µTorrent, and ClixSense all suffered significant data breaches at some point in the past. The leaked password databases from those and other online sites can be used to understand better how human-passwords are created and increase a hacker's success when performing brute-force attacks.