Watch this ASP.Net video tutorial to learn how to create culture-aware and locale-specific web content with no additional code. Use the Resource Editor to create page-level and application-level resources.

A simple security flaw can allow an attacker to gain a strong foothold with little effort on their part. When a web application permits remotely hosted files to be loaded without any validation, a whole can of worms is opened up, with consequences ranging from simple website defacement to full-on code execution. For this reason, RFI can be a promising path to obtaining a shell.

If you've received a spam message in Signal Private Messenger, you know that anyone can contact you as long as they have your linked phone number. But when it comes to the people you're actually trying to have a private conversation with, how do you know it's really them?

'Tis the season... for cheap (and free!) video games. THQ's Humble Bundle lets you get 7 games for any price you want, and now they're making it even better by offering fans a free Steam copy of Metro 2033 just for liking Metro on Facebook, which is gearing up for the latest Metro: Last Night release.
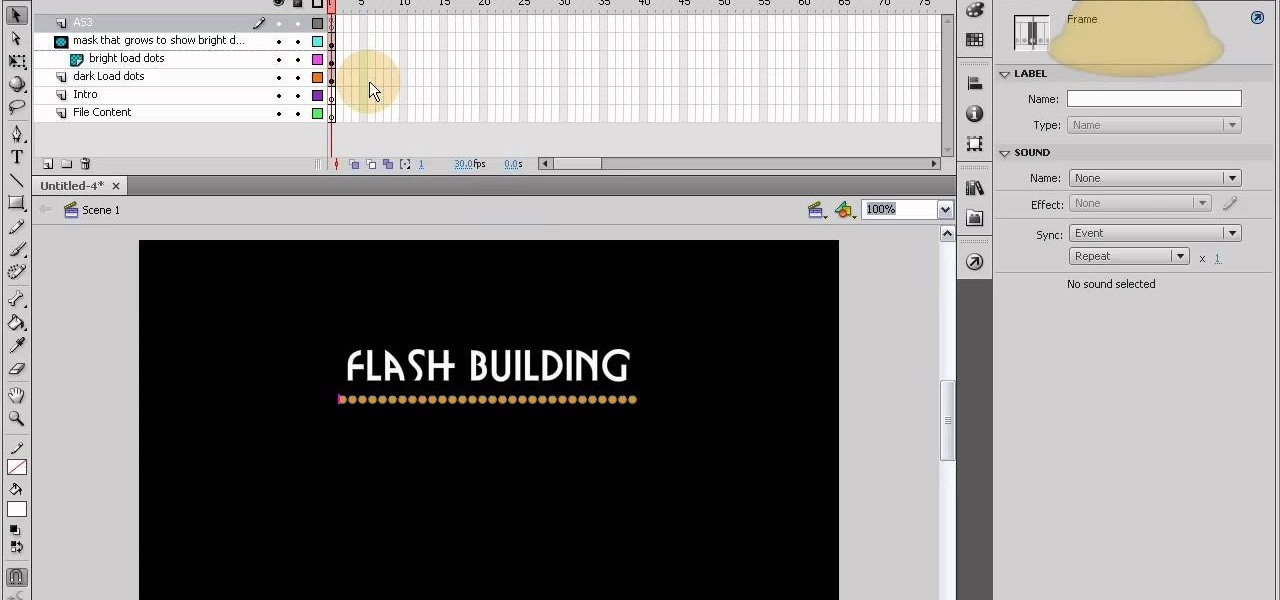
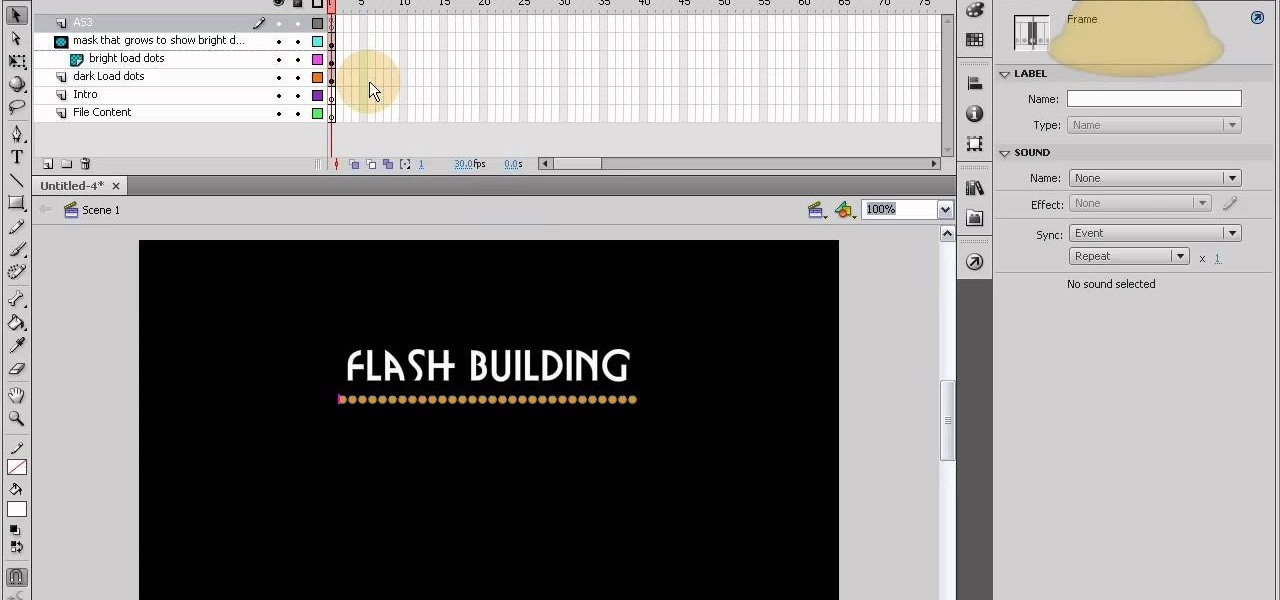
This tutorial shows you how to code an intro sequence for the first page of your Flash-based website. You're also shown how to code a dynamic loader bar, so visitors can easily tell how long the content will take to load in their browser.

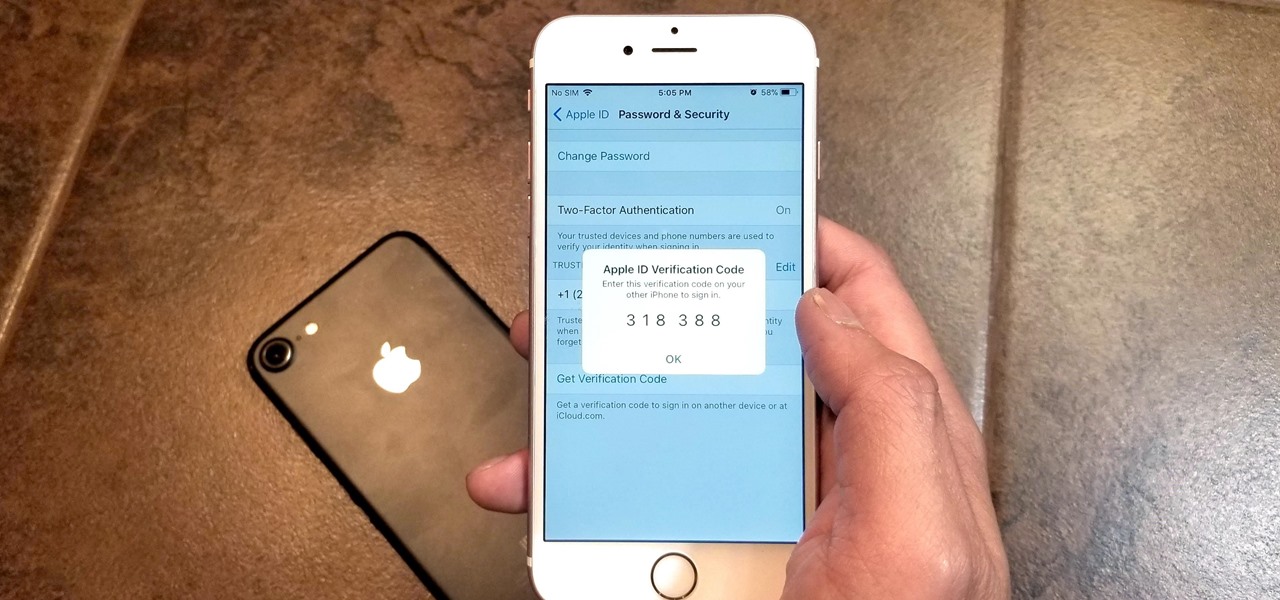
If you've ever received an email from a sketchy address purporting to be Uber, asking you to sign in with your credentials, you might be a phishing target. Hackers use a fake login page from real-looking domains to trick you into giving up your account information, and while it's been an issue in the past, Uber is making it more difficult on cyber thieves with the addition of two-step verification.

Two-factor authentication has been around since iOS 10. It's a handy option that adds an extra layer of security to your iPhone and makes its almost impenetrable security even stronger. This feature has remained intact in iOS 11 and iOS 12, and thanks to the straightforward nature of iOS, is relatively easy to enable.

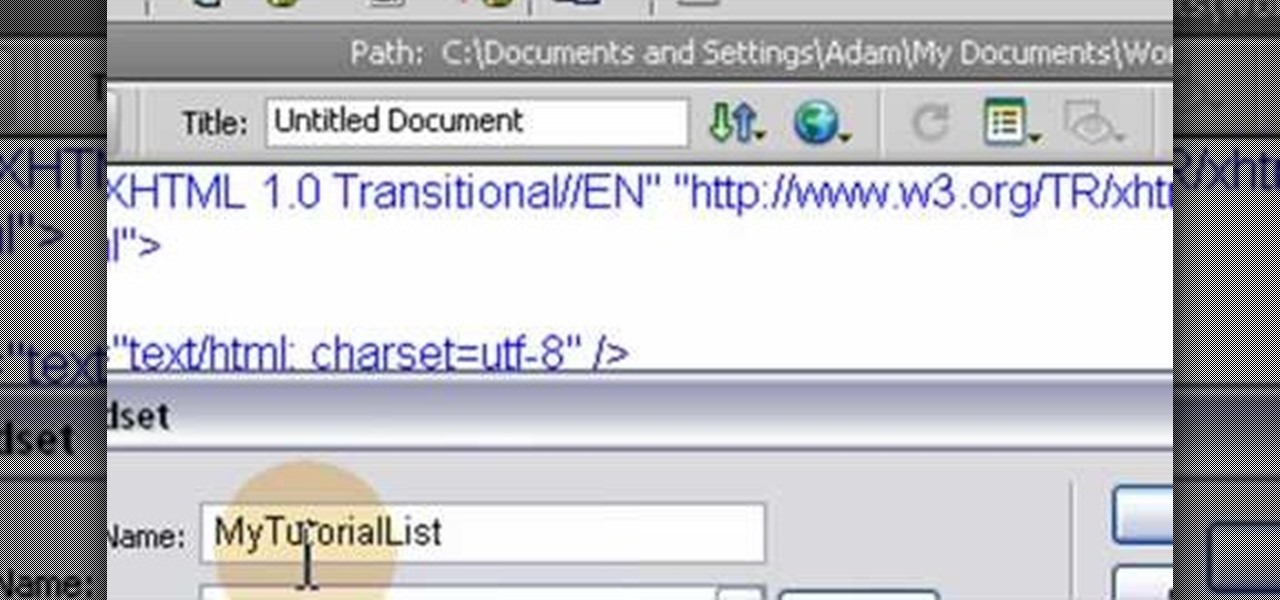
This HTML Web Design tutorial will explain how to add a Heading tag for your website. The heading tag is very important because it helps search engines to determine what the main topic is on a particular web page within your website. The HTML codes for heading tags range from h1 to h6 with h1 being the most important or in other words the main heading HTML web design tag. Make sure to give the h1 tag the most importance in terms of titles on your web page for headings. Another rule I recommen...

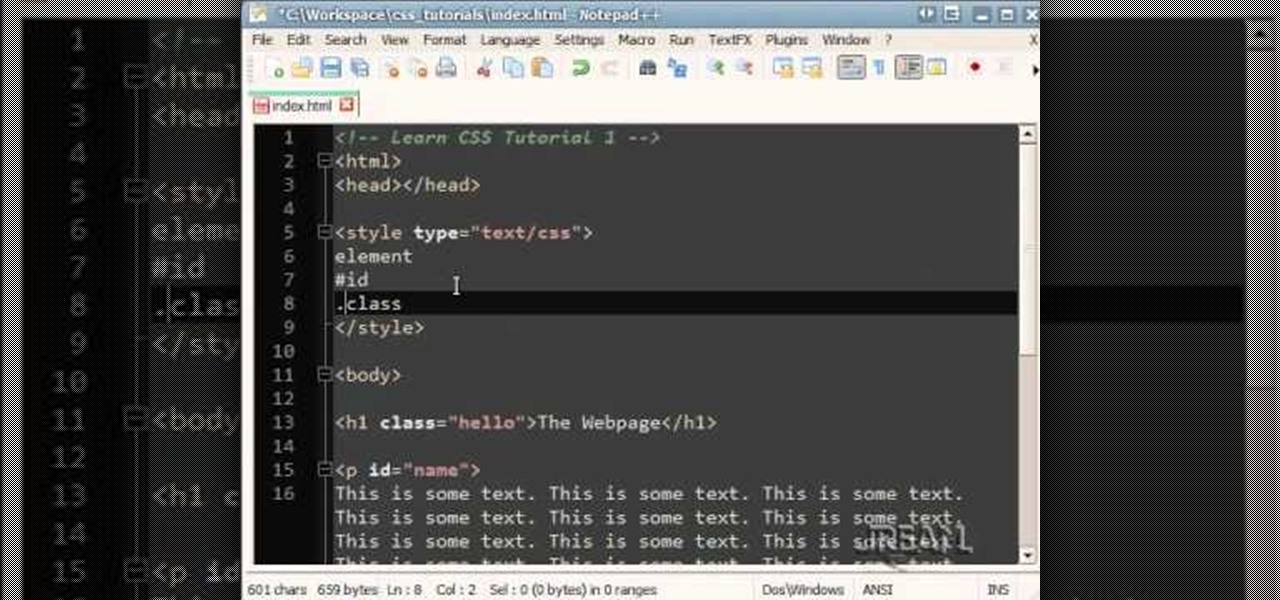
Looking for a place to quickly and easily learn CSS? This is the tutorial for you! This video covers every basic concept that you'll need to get under your belt, and shows you how to code a few simple procedures using CSS.

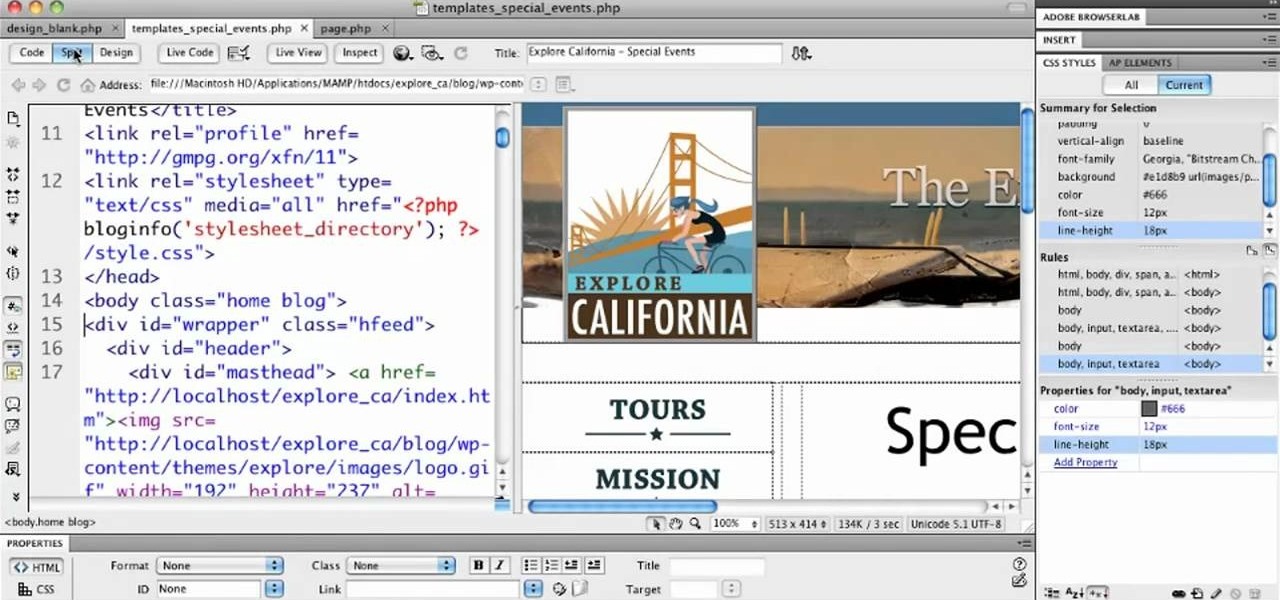
In this video tutorial, we learn how to employ live code when working with WordPress 3.0 from within Adobe Dreamweaver CS5. Whether you're new to Adobe's popular WYSIWYG HTML editor or a seasoned web development professional just looking to better acquaint yourself with the CS5 workflow, you're sure to be well served by this video tutorial. For more information, include detailed, step-by-step instructions, watch this free video guide.

Monitor visitors to your website by using a hit counter. This tutorial shows you how to use PHP and Flash to code a hit counter for your site. You can even use the counter to measure visitors to your site as a whole, or determine the most popular pages on your site.

Adobe Dreamweaver CS4 gives you several tools that you can use to manage your website without having to know the PHP or MySQL programming languages. This is a great way to keep track of and manage your website without having to learn how to code!

In Access 2010 you can now create a navigation form (like a home page) for your database without writing a single piece of code or logic! Great for busy people who need to organize their database quickly, but who don't have code writing skills. It's just drag and drop. There are predefined layouts which help you design the form and then simply drag the information you want into the form. Reports can be added and accessed quickly from the navigation form so you can analyze the data simply and ...

If you are building web applications in Microsoft Silverlight, and you want to give users the option to make the application or page full screen, then this Silverlight programming tutorial will be perfect. Watch and learn how easy it is to add some code to give users of your application the option to view it fullscreen, all within Silverlight.

Both the Gears of War 3 Limited and Epic Editions contain a DLC code that allows you to unlock and play the Adam Phoenix character. The code is a little hidden, and unlike most DLC codes, isn't printed on the back of the manual. This guide from IGN will show you where to find the Adam Phoenix DLC code.

There is no shortage of defenses against cross-site scripting (XSS) since it is so prevalent on the web today. Filters are one of the most common implementations used to prevent this type of attack, usually configured as a blacklist of known bad expressions or based on regex evaluation. But there is hope with a wide variety of techniques that can be used to defeat these filters.

Web application vulnerabilities are one of the most crucial points of consideration in any penetration test or security evaluation. While some security areas require a home network or computer for testing, creating a test website to learn web app security requires a slightly different approach. For a safe environment to learn about web app hacking, the OWASP Juice Shop can help.

There's actually more to the dialer screen on your OnePlus than meets the eye. Besides its obvious purpose of calling people, there's a vast array of secret codes that you can input to troubleshoot your device, in addition to revealing important information, making anonymous phone calls, and so much more.

Google I/O, the national developer conference for the Mountain View giant, has come and gone. We saw the preview for Android L (which you can get right now on your Nexus 5 or Nexus 7), Android Wear, and Android Car and TV.

Web applications are a prime target for hackers, but sometimes it's not just the web apps themselves that are vulnerable. Web management interfaces should be scrutinized just as hard as the apps they manage, especially when they contain some sort of upload functionality. By exploiting a vulnerability in Apache Tomcat, a hacker can upload a backdoor and get a shell.

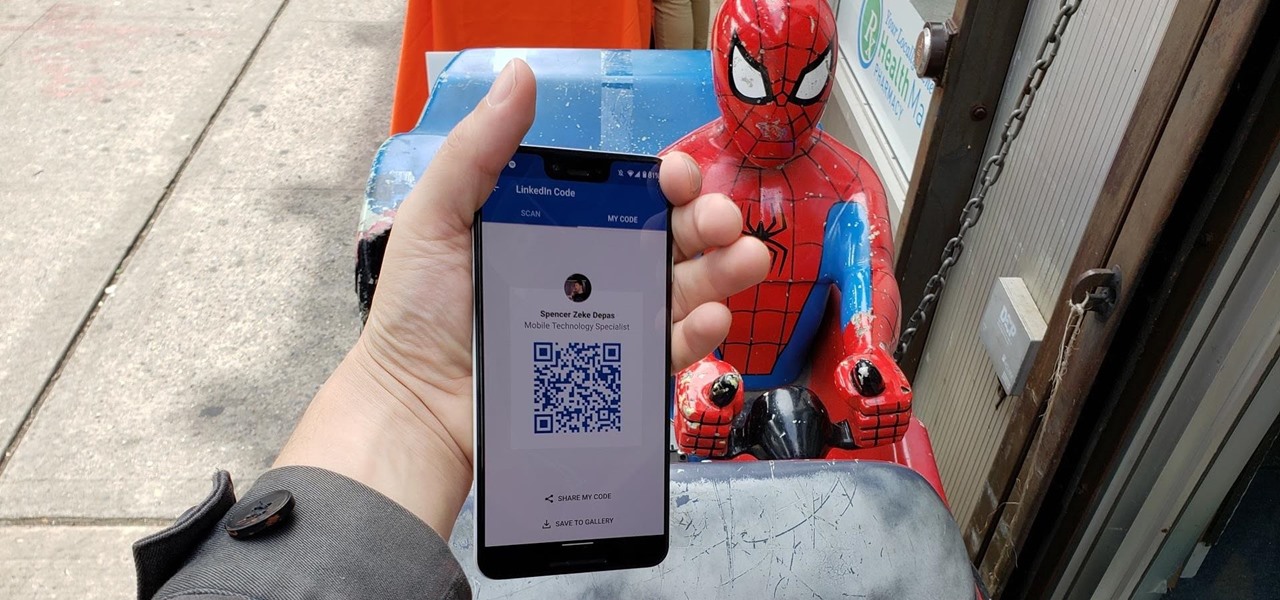
When attending networking events, a LinkedIn exchange is a common occurrence. Equally common is the awkward fumbling dance with how to add each other. Fortunately, we have the solution: the ultimate way to add LinkedIn contacts.

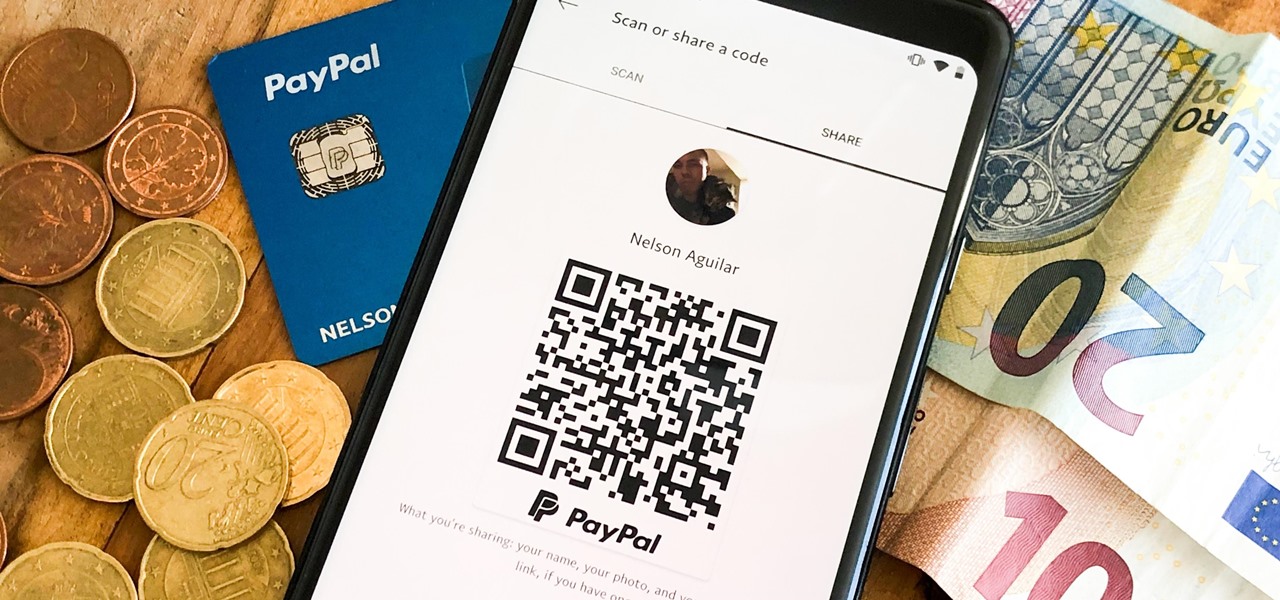
There are many ways to send and receive money on PayPal. You can use an email address, a phone number, or a PayPal.Me link, but if you're standing right next to the person you're trying to pay or get digital cash from, the easiest way, by far, is to use QR codes.

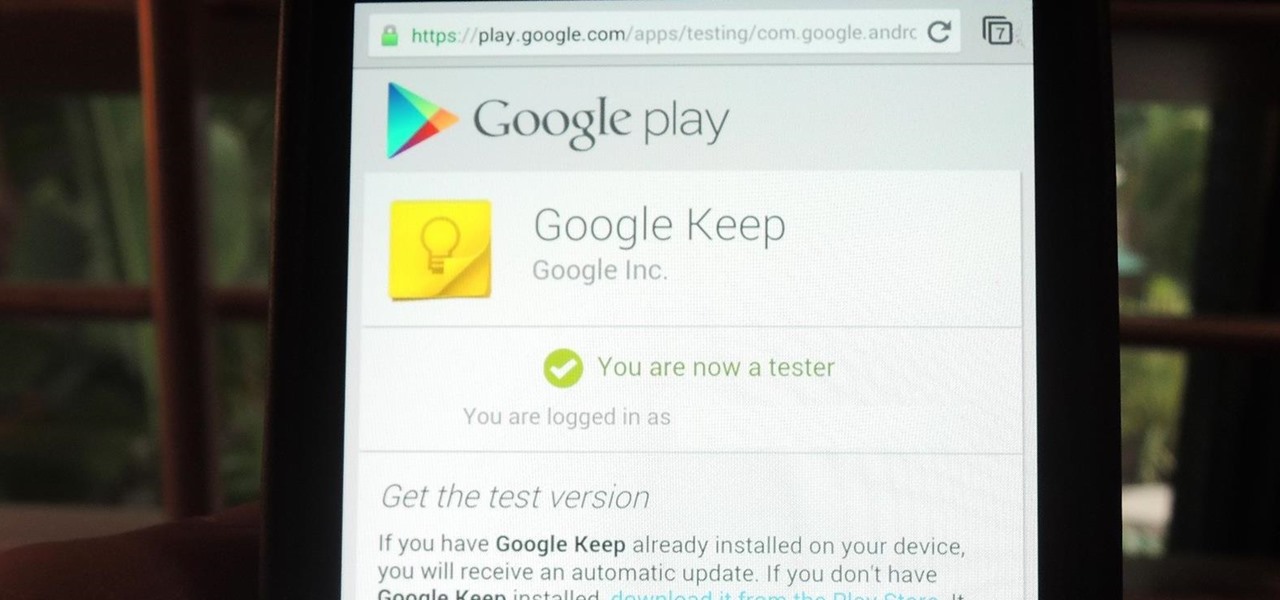
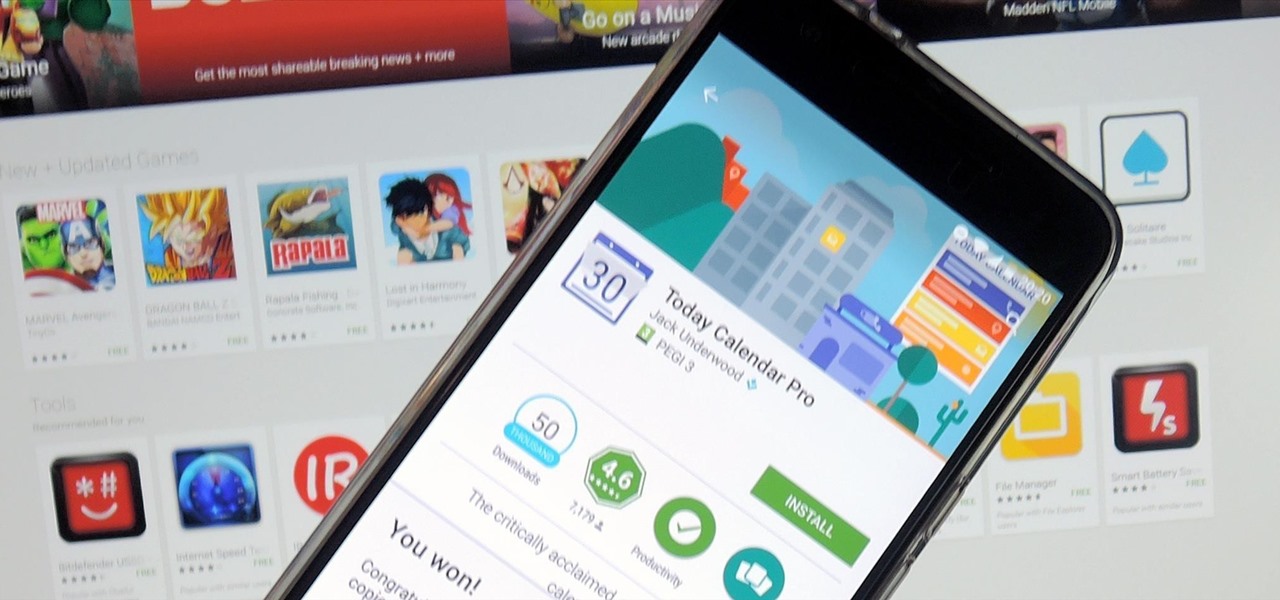
If you're a developer looking to get some exposure for your high-quality app, or if you're a user hunting for new apps and would like a chance to win a paid app at no cost, then Jack Underwood's new Promo Codes app may get you there, which you can install for free from the Google Play Store.

If you want to embed a video on your website and customize the player so it doesn't look like crap, you've come to the right place:

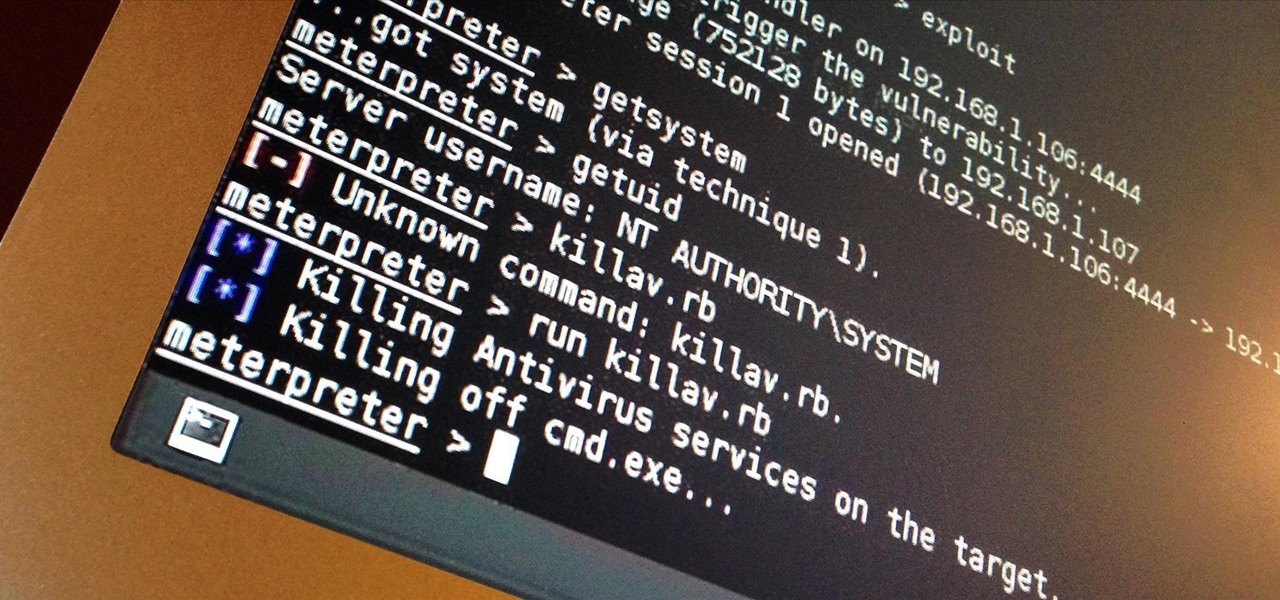
I've done numerous tutorials in Null Byte demonstrating the power of Metasploit's meterpreter. With the meterpreter on the target system, you have nearly total command of the victim.

Most of you viewers out there who are familiar with Flash, After Effects, or other creative software know what a tween is. But can you write the code for them? This video will teach you how to code different classes of tweens using Actionscript 3 in Flash CS4.

In this tutorial, we learn how to save music from MySpace as an MP3. First, download and install the Firefox plug-in from: https://addons.mozilla.org/en-US/firefox/addon/1843. After this, go to MySpace and search for the artist whose music you want. Then, click on the top of the browser on the "view" button, then click "page source". After this, search "mp3" at the bottom of the page, then scroll through until you see "<PARAN NAME="src"value=themp3linkwearelookingfor" and copy this. Paste thi...

This clip presents a general overview of how to utilize content tags when writing a website using HTML5, the new HTML standard. Whether you're using a fancy WYSIWYG (or what-you-see-is-what-you-get) page editor like Adobe Dreamweaver CS5 or a barebones text editor like Notepad, if you want to build websites, you'll need to have some understanding of HTML (for the structure of your web pages) and CSS (for their style). And this free coder's guide will get you started along that path.

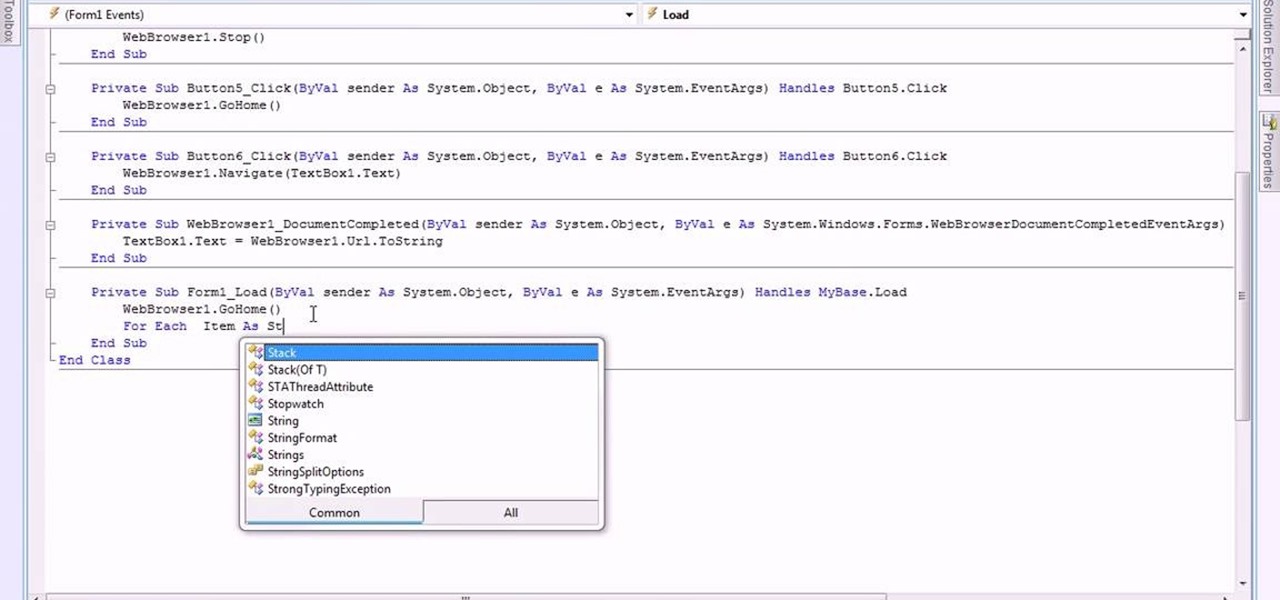
This video is about making a bookmark for your web browser in Visual Basic 2008.The videos begins with a simple web browser which consists of simple web components, a textbox and a go button. Pull the sides of the browser to stretch it and put in a listbox. Enlarge the listbox and use two buttons below the listbox. Enter the text for the buttons as "Enter current page" and "clear". Now go to selection explorer, double click "my project" and go to settings. Add a new setting called "Bookmarks"...

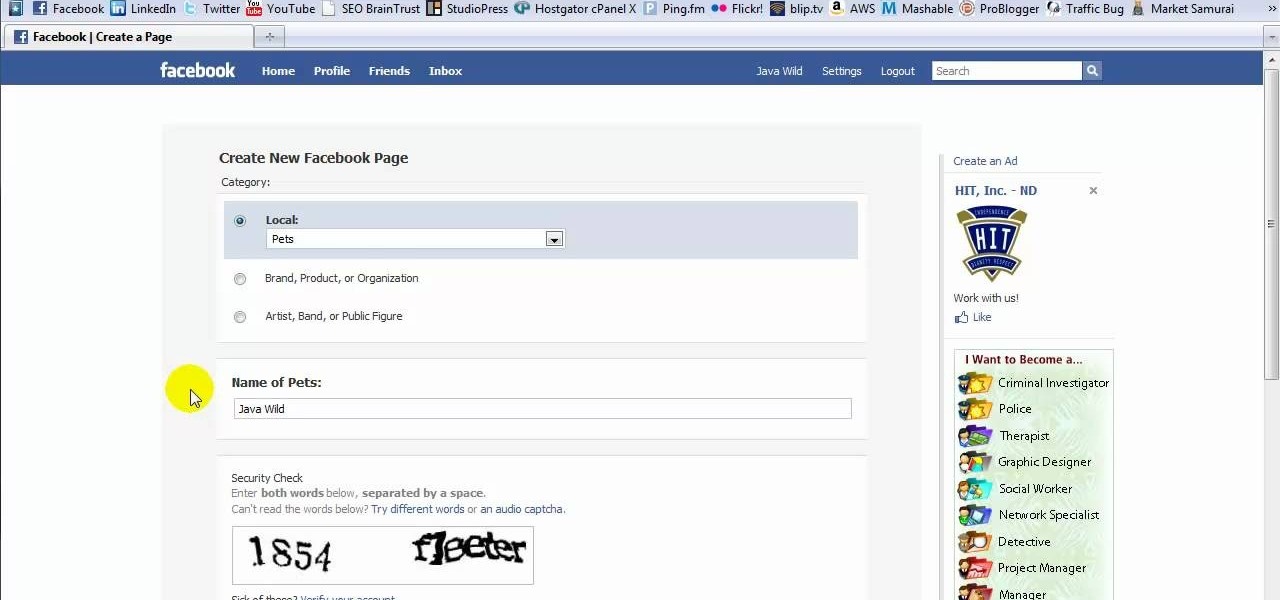
This tutorial is in response to mail to Facebook. Scott Wilde leads you through the process. You can start by creating a brand new profile page. In this case, Mr. Wilde created a profile page for his dog Java Wilde so he could have a fresh new page without having to alter his initial profile page. Fan pages are different than your base profile. Your base profile is not indexed, it is not public, it is private and limited to 5000 friends. A fan page is unlimited up to millions of fans and it c...

Jim Reppond of Coldwell Banker Bain demonstrates the way of getting postlets into Facebook. He says that by adding the postlets in your Facebook page, one can click on the link and directly go the postlets page if they are interested. He asks you to then go to the postlets page and log in using your username and password. Once inside, you can click on the 'My Postlets' tab to see your active postlets. Then chose the postlet you want to add to Facebook and click on the respective 'HOST' button...

Have you seen odd, square codes on some specific merchandise? These are called QR codes, or quick-response codes, and they are a type of bar code which your smartphone can read and then take you to a particular website, give you coupons or even a business card. Here's how you can get the most out of QR codes.

Any hacker worth her salt will need to debug from time to time. One particularly efficient way to check your code is with the RATS code checking tool. In this video, you'll learn how to use the RATS code checking tool for C/C++, PHP and Perl. For a detailed walkthrough on how to use RATS scanner to audit your source code, take a look!

Penetration-testing frameworks can be incredibly useful since they often streamline certain processes and save time by having a lot of tools available in one place. Of course, the most popular pentesting framework is undoubtedly Metasploit, but there are many others out there that cater to particular needs. For auditing web applications and servers, Tishna comes in handy.

Cross-site scripting can be one of the easiest vulnerabilities to discover, but to be successful with this type of attack, it is essential to learn how to get past filters. In the previous guide, we explored some ways to do this, such as abusing attributes and event handlers and tricking the application into accepting unusual characters. Now, let's take a look at more techniques used to defeat filters.

Cyanogen, Inc., the for-profit company that spun off from its CyanogenMod roots several years ago, has announced that they're shutting down all of their services. The company's impending demise shouldn't directly impact many Android users, but the announcement does have one major repercussion: The servers that used to host the popular CyanogenMod custom ROM have now been shut down.

In this series you will learn how to use PHP to perform attacks, gather information, and setup backdoors. Along with performing attacks you will learn how to protect yourself from them. In this part you will learn about PHP as well as install Apache and PHP. What you'll need for this series

hello hackers,newbies and followers of this great community, after some research here in our community, I noticed that there is not even one tutorial that teach Web Development. We have a lot of tutorials on how to hack web site but many do not know exactly how a web site is composed, then I decided, meeting the community's needs, begin to teach people how to develop web sites.

While password cracking and WPS setup PIN attacks get a lot of attention, social engineering attacks are by far the fastest way of obtaining a Wi-Fi password. One of the most potent Wi-Fi social engineering attacks is Wifiphisher, a tool that blocks the internet until desperate users enter the Wi-Fi password to enable a fake router firmware update.