
How To: Disable the uac on Windows Vista
1. To disable the UAC (User Account Controls), first click start button and type "msconfig" into the start search text box.


1. To disable the UAC (User Account Controls), first click start button and type "msconfig" into the start search text box.
This video shows the viewer how to disable User Account Control within either Windows 7 or Windows Vista. This is done by clicking on the start menu and then type ‘Microsoft config’ into the search box. This opens the ‘system configuration’ menu. Select the ‘tools’ section. For Windows Vista there is simply an option to disable User Account Control. For Windows 7 click on the ‘change UAC settings’ option before clicking launch. In Windows 7 the slider should be dragged to the bottom. Both met...

This video shows the method to recover deleted files in Ubuntu using Testdisk. The demonstration is done by deleting a set of pictures and recovering them later. The test disk is installed at first. Then we click on the terminal icon and go to the list options available. These include selecting the list of drives available, partition table type and the type of file system in the original photos. Then the system asks you to select the part to be analyze and destination folder. The tool then re...

In this video tutorial, viewers learn how to quickly troubleshoot memory problems in Windows. Begin by clicking on the Start menu. Type "mdsched" into the search bar and press Enter. The Windows Memory Diagnostic window will then appear. Click on "Restart now and check for problems". Your machine will then be rebooted and will run its memory diagnostics tool. It will look for any issues that may cause problems for your system. Advanced users can press F1 when it starts to specify certain opti...
Left-handers only make up about ten percent of the world, which means they typically have to use things made for the majority, i.e., right-handed people. If that wasn't annoying enough, there are studies that show that lefties actually get paid less.

There is nothing worse than losing valuable information or programs on your computer. And if you've ever accidentally deleted a file or document, you know how agonizing that entire process can be.

The Canon EOS 7D can be fine-tuned to adjust its auto focus to suit nearly any subject. See how you can customize your AF functions to get the best focusing options needed for your desired result. This video breaks down everything.

Windows 7 uses several options to make it easier to change and locate the cursor on the screen. 1) To access these options select “Start” then click on “Control panel“from the menu.
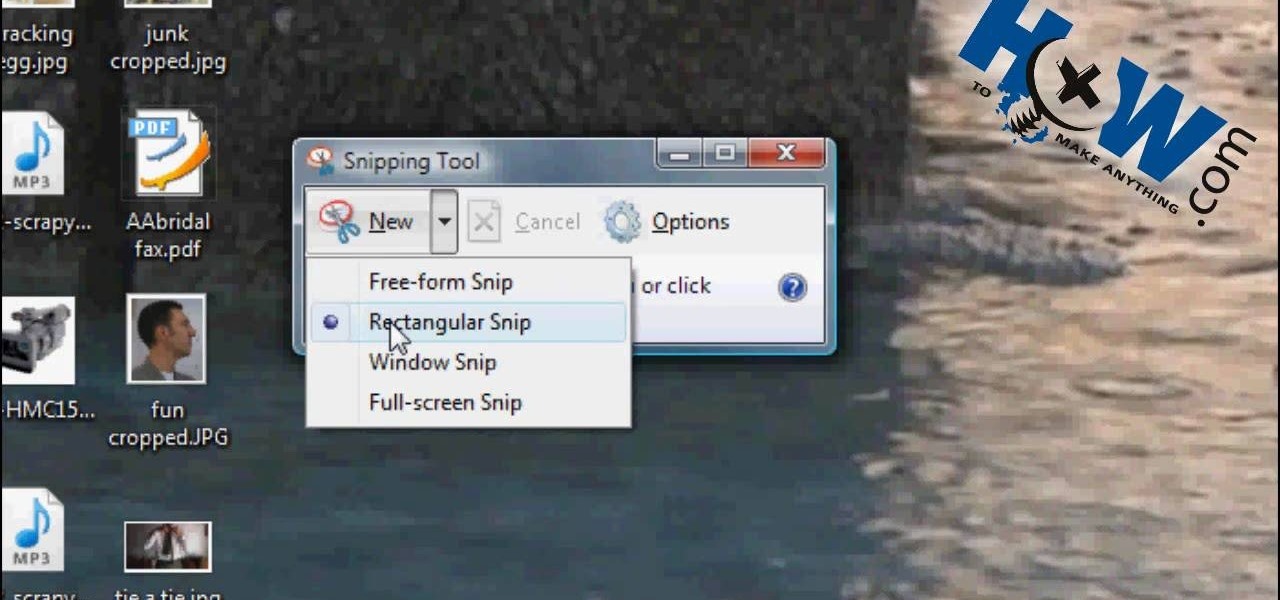
How to Make Anything demonstrates how to use Window Vista's snipping tool to make a screen capture. With previous operating systems, you'd have to install a third party application to make a screen capture. To find the snipping tool in Windows Vista, go to the start menu and type "snipping tool" into your search box. The snipping tool box will appear. Click on the options tab. In the next screen, tick display icon in the quick launch toolbar to enable the snipping tool in the toolbar. Click o...
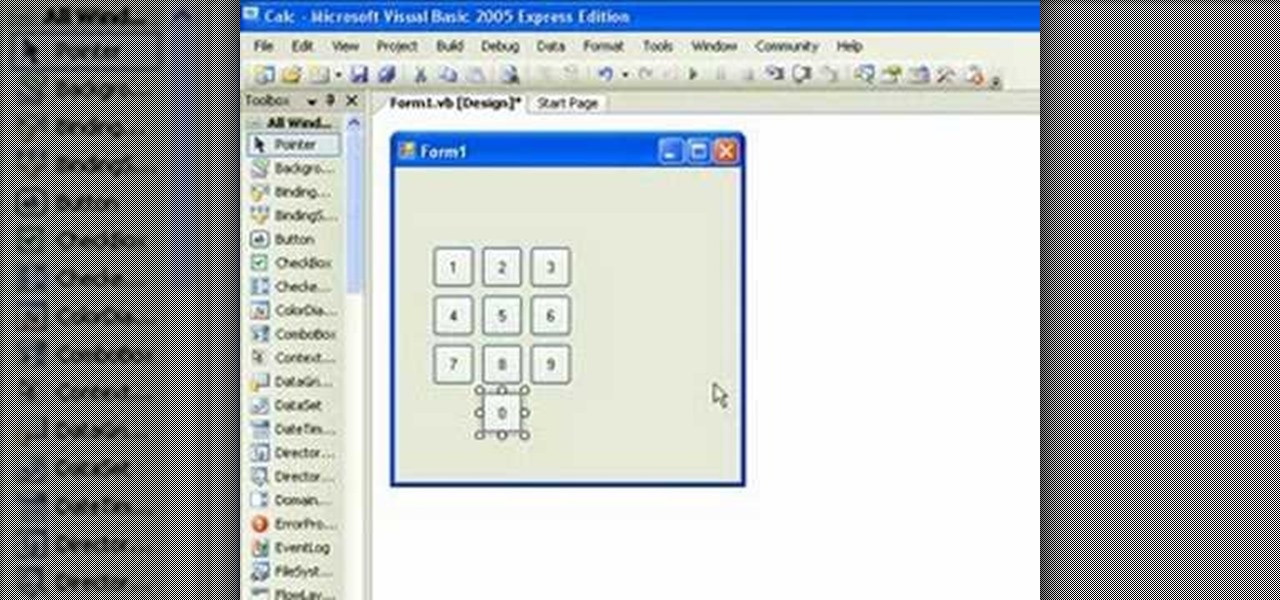
If you're new to the Visual Basic IDE, looking to brush up on your VB programming skills, or simply have a burning desire to code a simple calculator, this three-part video lesson is for you.

You can easily deck out your favorite phone with great wallpapers, ringtones, and icons, but what about fonts? Not all Android skins let you change the system font, and even when they do, the options are often limited to a few choices. Certain root apps can open up the system font to customization, but some of these can cause problems now that Google introduced a security measure called SafetyNet.

Transition animations are an essential element of any mobile operating system. They give the user a sense of what's happening on the screen, where the apps are coming from, and where they're going.

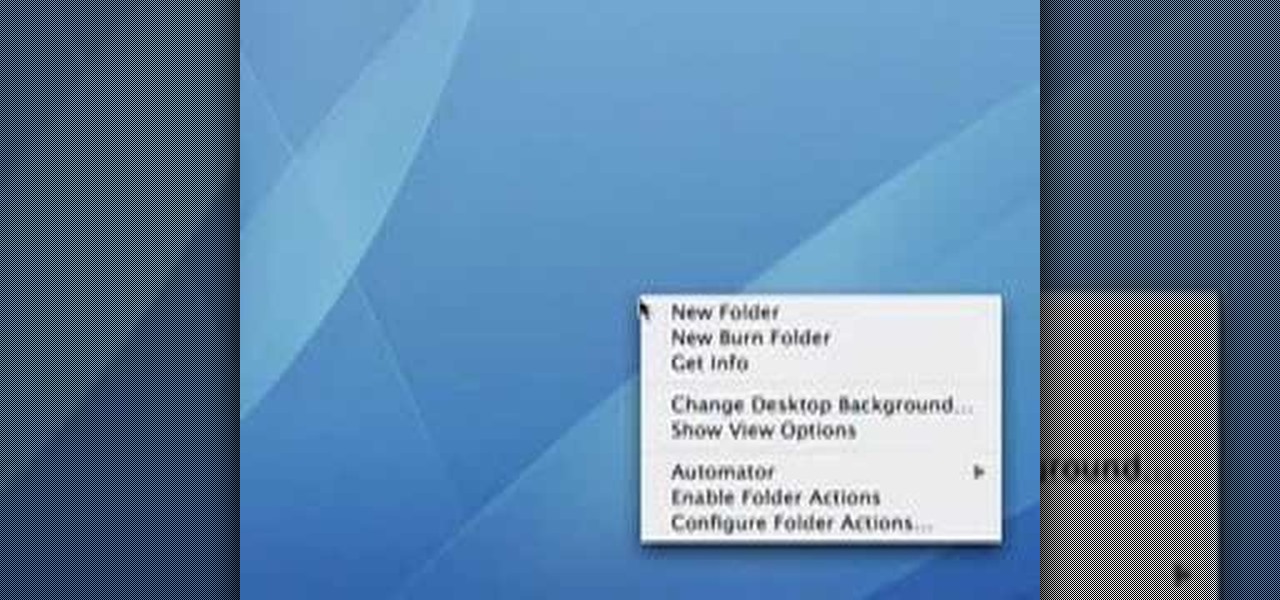
This is another HelpVids video on technology. In this segment we will learn how to set appearances and themes in the Microsoft Windows XP operating system. The videos starts by right-clicking on a blank area of the desktop, then selecting ‘Properties’. The presenter then clicks on the ‘Appearance’ tab. Clicking on ‘Advance’ will open some very detailed options such as changing the font in a title bar window. You can also change the size of the fonts in this window. The options are truly endle...

This video tells you how to set your default browser to Firefox3.5. In a few simple steps, you can set Firefox as your default browser and also make sure the browser is Firefox whenever you browse. Open Firefox browse- click on Files-Select Tools-Select options-select advanced-you will find System default at the end, just click the option button against". Always check to see if Firefox is the default browser on startup. This option changes your browser to Firefox and also makes sure that alwa...
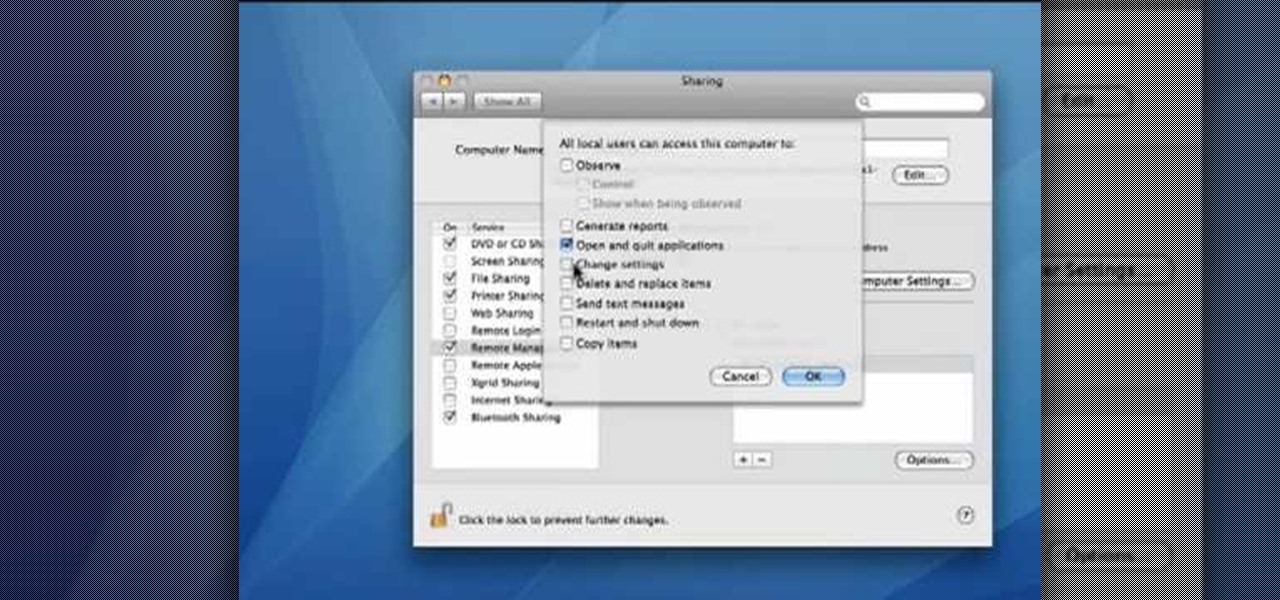
This video demonstrates how to set your Mac up to accept VNC connections.First we open up the "system preferences". Double click on Sharing and then go down to remote management and check this. We can see some options . Check the options Open and quit the application, Change settings, Delete and replace items, Send text messages, Restart and shutdown and Copy items. Then select "OK". Over here we can see "allow access for" and check "only these users". Remote management is now On. We can mana...

If you have upgraded your Windows to Windows 7 and want to stay current with all the new operating systems and software but hate it when you're faced with all the changes upgrading brings, you can download the 7 Taskbar Tweaker to configure your taskbar to your preferences. If you liked the old feel of Windows you can change that by choosing the option, you can also change what happens when you click on certain buttons to make your computer user friendly.

I don't know about you, but nothing is more annoying than when my phone hits 15% and I'm nowhere near a charger. Not just because I know my phone will die soon, but until I reach a charger, I have to deal with the annoying low battery notification and LED light. Well, with Android 9.0 Pie, we finally can escape this.
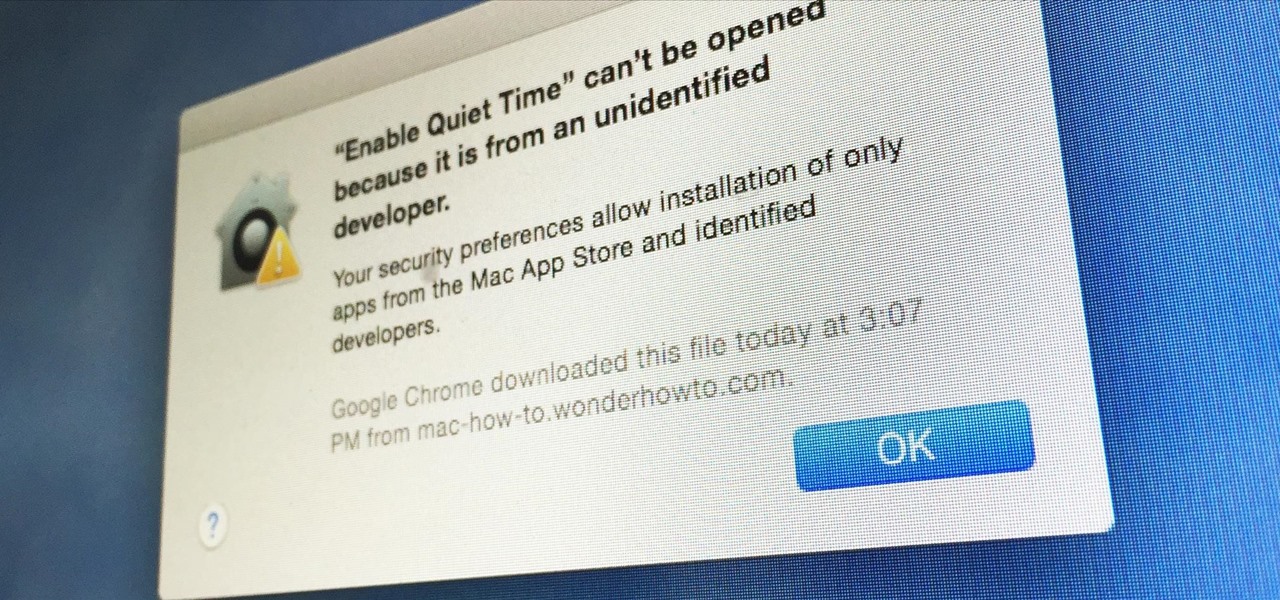
Apple has a built-in way to protect you from opening up potentially malicious apps on your computer in Mac OS X Lion, Mountain Lion, Mavericks, Yosemite, El Capitan, and macOS Sierra. This setting, named Gatekeeper, will never stop you from installing apps from the Mac App Store, but it could from anywhere else. If it's an app you're sure you want to install on your system, here's how to do it.

In my first few articles, we focused on operating system hacks. These hacks have been primarily on older operating systems such as Windows XP, Windows Vista, and Windows Server 2003.

In this tutorial, we learn how to use the zoom feature in Mac OS X Leopard. First, go to system preferences, then universal access. Find the zoom category, then turn it on of off. You will also see the keys that you can press which will make it appear. If you go to the options menu, you will be able to maximize or minimize the zoom. Test this out by zooming in on a page and holding the control key along with the tracking ball on your mouse. When you do this, everything will become far more zo...
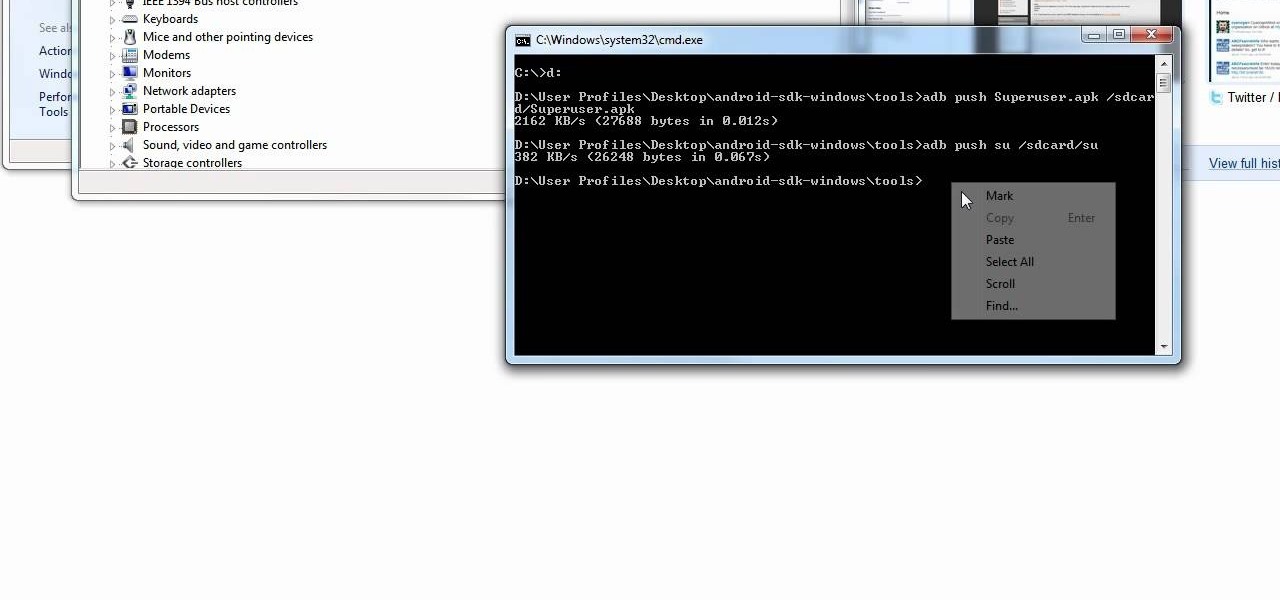
Yes, the Droid X from Motorola can be rooted, and yes, you can do it at home. Just make sure you follow the directions precisely. If you succeed, you'll have a completely rooted smartphone. eFuse doesn't matter. If you want to expand your options on Verizon Wireless's Droid X, then you just have to take a chance… use this video in conjunction with the links and description below.

Having an irrigation system installed in your back or front yard, can be an easy way to not only water your plants, but add investment to your home. Asking a professional can put you back thousands of dollars, so doing it yourself it a much better option. It will only take a few days to complete, the right tools, and some sweat and labor. So check out the tutorial above to find out what else it will take to have a great irrigation system in your yard. Enjoy!

Every time you download a game, movie, etc to your computer, you make changes to the computer. Sometimes, these downloads can make your computer unstable. By default, Windows Vista creates restore points in the background. What this means is every time you make these changes to your computer, Vista takes a snapshot of your computer before the changes are made. This enables you to go back in time and restore your computer to an earlier time. Documents, photo's and emails will still be saved. O...
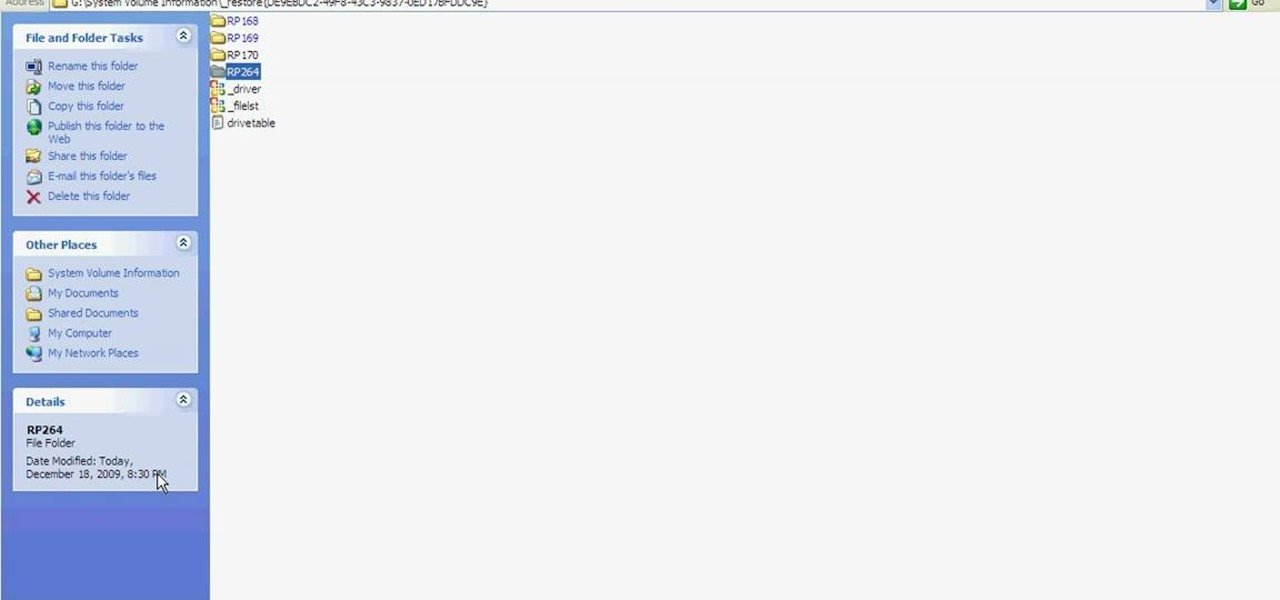
Learn how to fix or recover a corrupt windows registry following the steps outlined in this video tutorial. To begin, take the hard drive out of the computer with the corrupted registry and connect to another computer. To find the files you need to replace go to Start and My Computer. Look for the hard drive that you just added and double click on it. Go to Tools and Folder Options. On the View tab under Advanced Settings click Show Hidden Files and Folders, and unclick Hide Protected Operati...
Start by dragging your mouse down to system preferences on the dock and open it. If system preferences is not on your dock you can get to it alternatively by opening finder and selecting applications. Scroll through this until you find system preferences which should be located near the bottom because it's usually organized alphabetically. Then select the keyboard and mouse icon. After that click on the trackpad tab and check the option in this screen that says "place two fingers on trackpad ...
Prompt and frequent system updates are a big part of the Pixel's identity — we're even getting quarterly feature drops now. But not all devices receive these all-important updates at the same time because of Google's staged rollout system. If you want the update right away, there's a way to manually check without having to dig around in Settings every time.
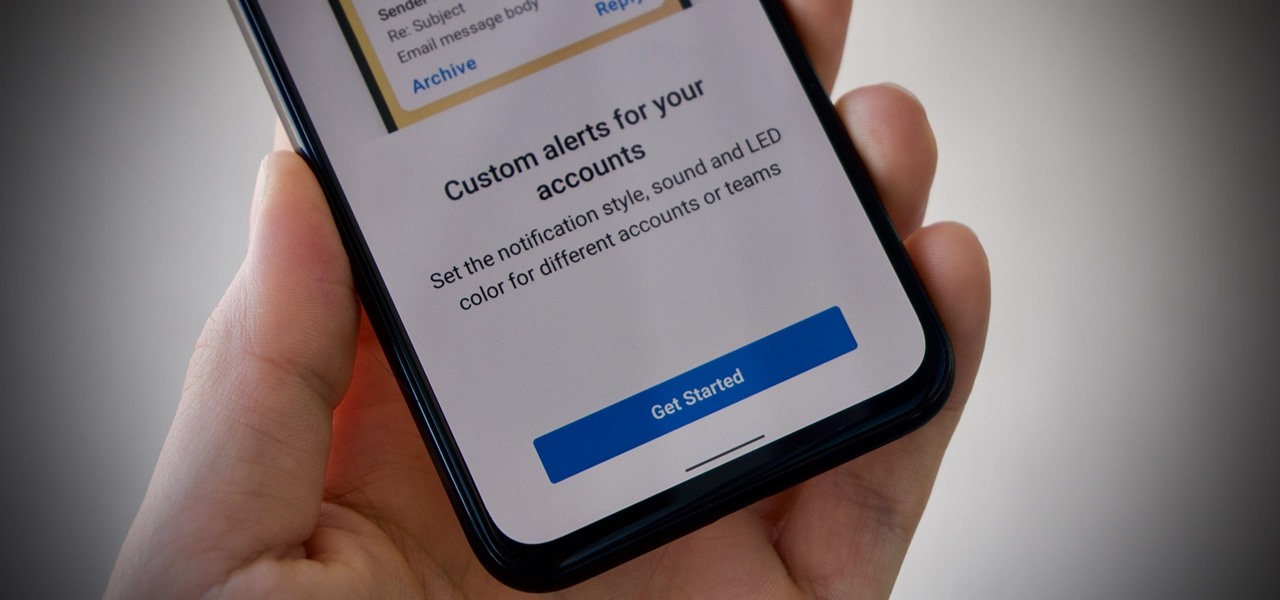
Android is all about customization. That's why it's entirely appropriate that Spark for Android's newest update adds a ton of customization options for your out-of-control email alerts. Now, you can add lights, sounds, and vibrations to notifications, and you can even set specific settings for all of your email accounts.
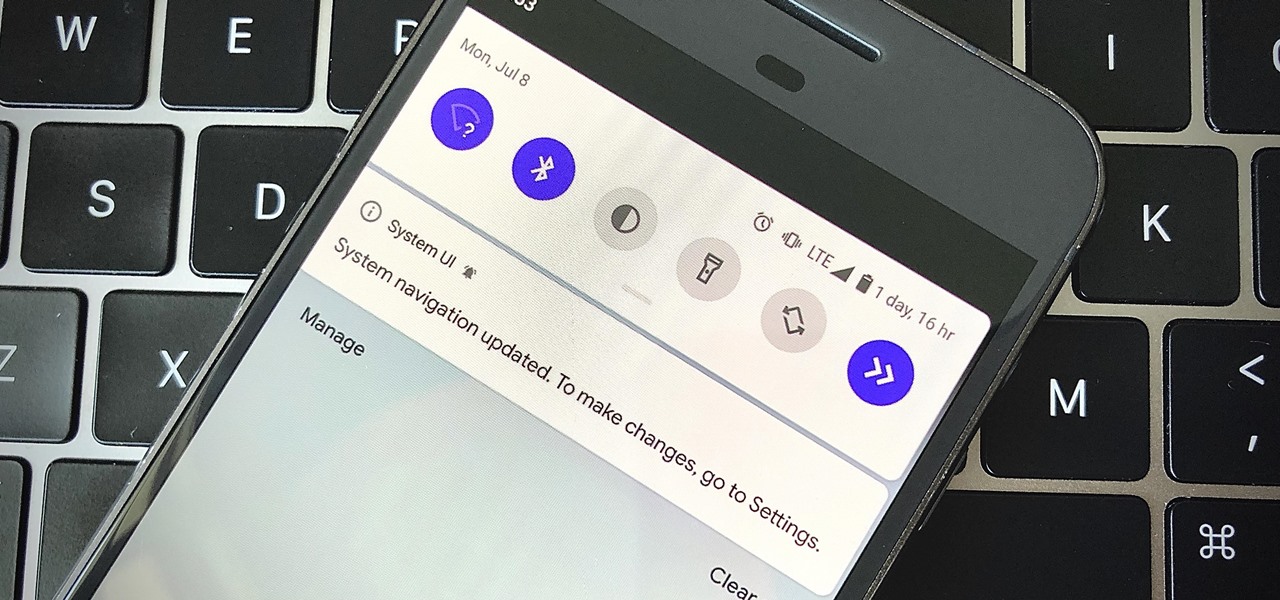
So, you just updated to Android 10, ready to explore all of the new features Google has to offer. There's just one hiccup — those gesture controls everyone talks about? They don't work. In fact, the option is completely grayed out, taunting you from the get-go. What's going on here, and how can you restore functionality to a staple Android Q feature?
If you ever want to go beyond the basics on your Android phone, unlocking the hidden "Developer options" menu is the first thing you should try out. With it unlocked, you can change the way parts of stock Android looks, enable ADB connectivity with your computer, add visual reactions to taps, and more.
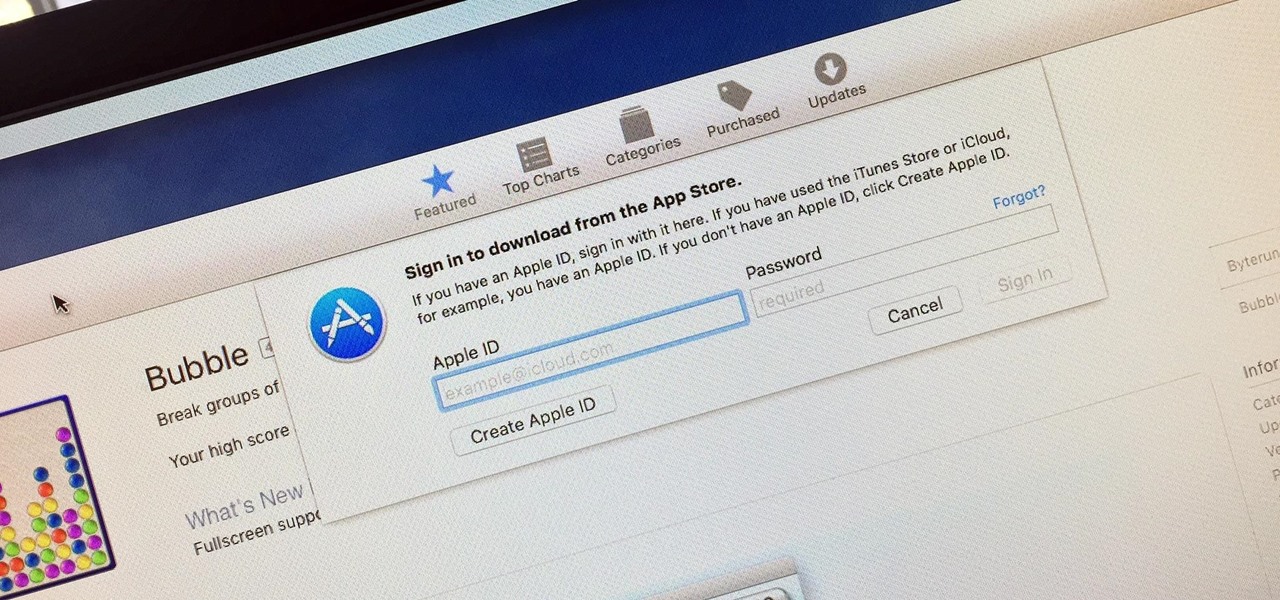
Whether you want to edit photos, compress files, play games, or DJ your next party, there's a free Mac app that can help you out. But things can get annoying real fast if you download a lot of free apps from the Mac App Store, since you have to type in your Apple ID password each time.

The world's most commonly-used desktop operating system is getting a huge makeover in the form of Windows 10. While there are many sweeping changes in this new version, some of the smaller tweaks may prove to be the most useful.

Welcome back, my neophyte hackers! In previous tutorials, we learned how to steal system tokens that we could use to access resources, how to use hashdump to pull password hashes from a local system, and how to grab password hashes from a local system and crack them.

When it comes to theming your Android device, it's the little touches that count the most. That's why developer SArnab created the Android Theme Engine, an Xposed Module to theme those hard-to-reach corners of the Android System that often go untouched with other themes.

Just about every softMod requires some kind of reboot. Whether it's because something in the System UI was changed, or because a ZIP needs to be flashed in custom recovery.

When I left off on our last hack, we had hacked into the ubiquitous Windows Server 2003 server by adding ourselves as a user to that system so that we can return undetected at any time. The problem with this approach is that a sysadmin who is on their toes will note that a new user has been added and will begin to take preventative action.

In my first installment in this series on professional hacking tools, we downloaded and installed Metasploit, the exploitation framework. Now, we will begin to explore the Metasploit Framework and initiate a tried and true hack.

Software expert David Steinlage guides the viewer through the step-by-step process of installing VMware and Windows XP on a computer driven by Ubuntu Linux. The first step is to get a serial number, which can be obtained free by visiting the site www.vmware.com and filling out the registration form. The VMware installer application Automatix is then opened and upon clicking the desired options, the installation of VMware starts automatically. At the end of installation, the user is prompted t...
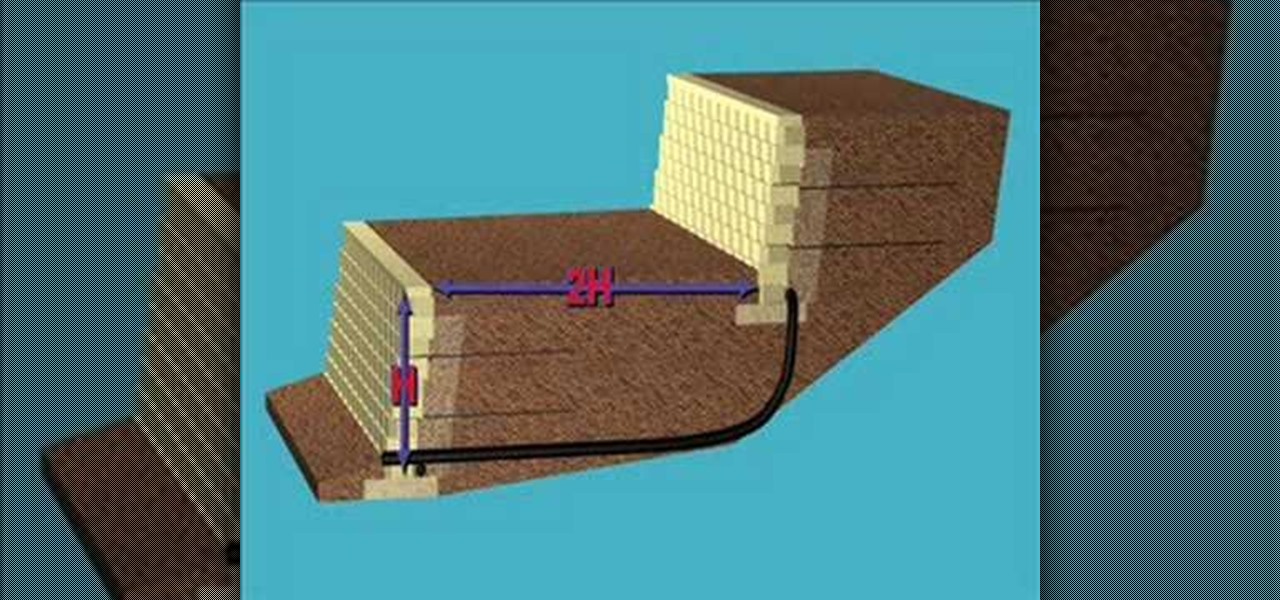
Terrace walls are an attractive option for steep grades. This video tutorial shows you how to build a terraced retaining wall system. This how-to video is a must-watch for everyone in the construction business.
You can create an image gallery of any directory on your file system with Konqueror. If you are a KDE user and you need to see the images in any directory, but if there are any other stuffs beside images in that directory then you will see that stuffs too. So if you do not want this, you need to click on tools in Konqueror menu and choose "create image gallery" for the current directory. There will be many options like folder, look etc. so set your options as you like and click on create, it ...

Post-exploitation is often not quite as exciting as popping the initial shell, but it's a crucial phase for gathering data and further privilege escalation. Once a target is compromised, there's a lot of information to find and sift through. Luckily, there are tools available that can make the process easy. One such tool is Postenum.