I don't know about you, but visions of pumpkin pie and cornbread stuffing and big, juicy turkeys are constantly dancing through my head right now. I'm sorry, healthy eating habits, but it's Thanksgiving week, and all I can do is think about food.

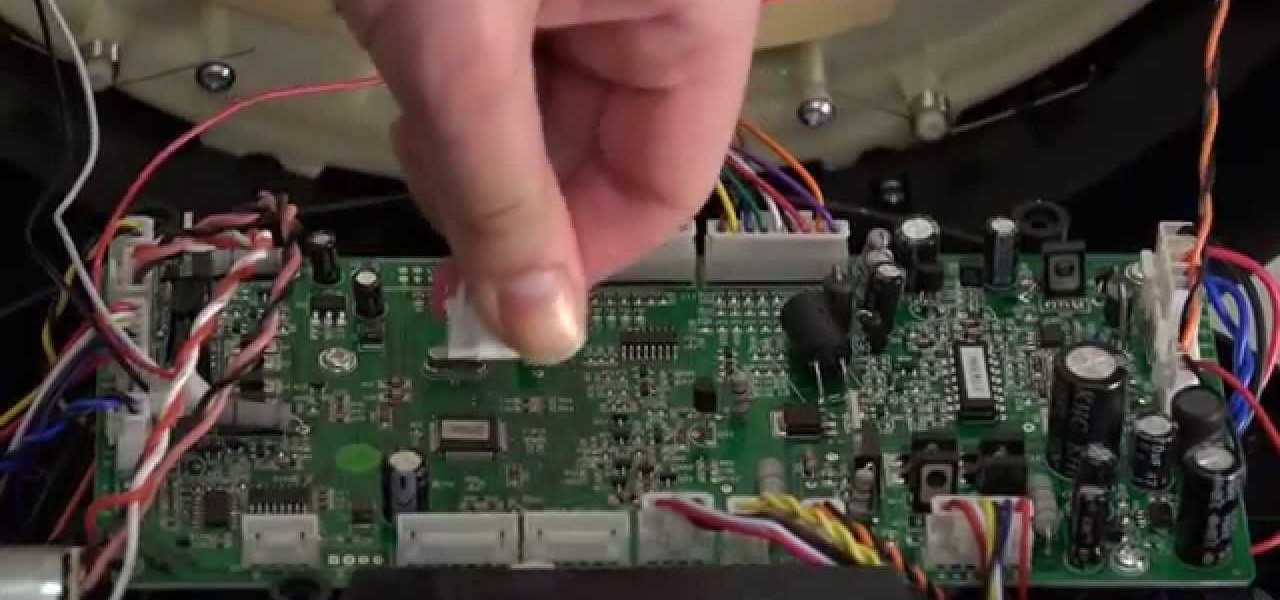
Both bObsweep Standard and Pethair models have two bumper sensors inside their covers. Whenever Bob runs into an obstacle, the sensors tell Bob to back away.

While still extremely awesome, the Samsung Galaxy Gear smartwatch is limited as to what you can download on to it, especially apps. It also doesn't have its own internet access (only Bluetooth), so apps like Instagram, Facebook, and Vine have yet to make their way to the Gear Store.

Cinema is a matter of what's in the frame and what's out, according to director Martin Scorsese, who asserted that when describing his life's work. Getting the perfect shot can turn an otherwise ordinary scene into something great, both on and off screen.

Somewhere around 600–800 million people in the world are infected with whipworm (Trichuris trichiura), an infection they got from ingesting soil or water contaminated with feces of infected animals or people containing the parasite's eggs.

So, you want to become anonymous? well let me give you everything I know (or at least most of it) to you.

The bumper for bObsweep Pethair and Standard are installed the same way. It holds the sensors that allow Bob to see any obstacles in his path. If a repair of the wall detection sensors is needed, the steps for replacing the whole bumper are the same when working on either bObsweep model.

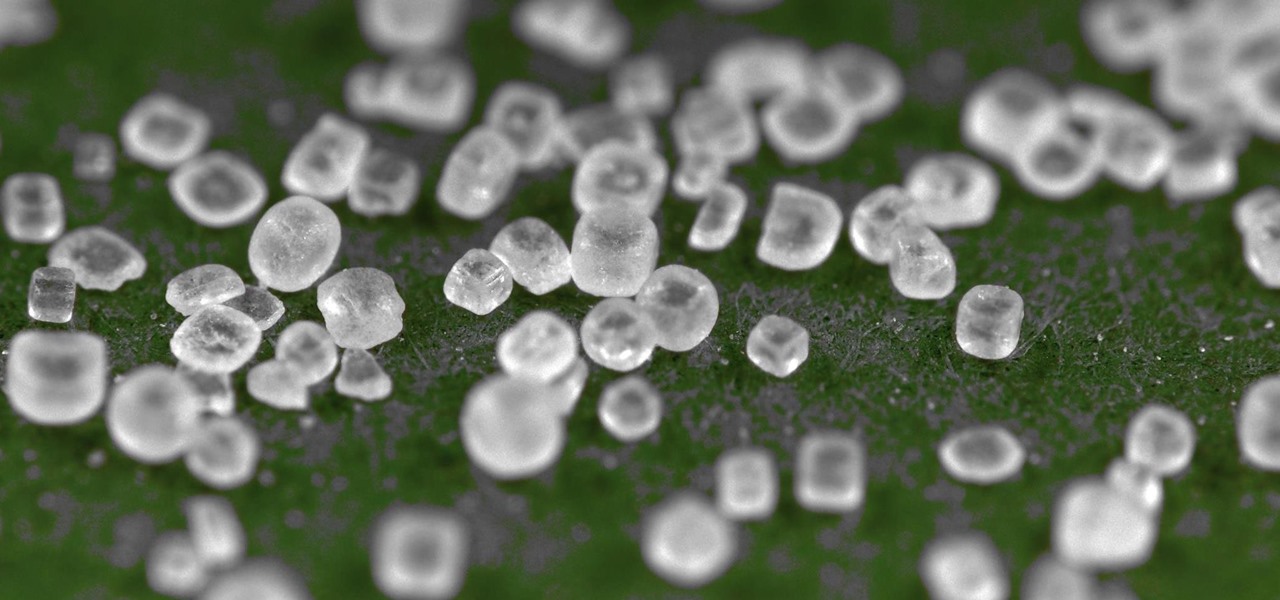
Salt is one of my favorite ingredients, by far, and also one of the most overlooked foods in the kitchen. This is probably due to the fact that it's an essential component of almost any recipe; because salt is a necessity, it's easy to forget how dynamic and versatile it can be as well.

If you've ever received an email from a sketchy address purporting to be Uber, asking you to sign in with your credentials, you might be a phishing target. Hackers use a fake login page from real-looking domains to trick you into giving up your account information, and while it's been an issue in the past, Uber is making it more difficult on cyber thieves with the addition of two-step verification.

Passwords and data stored in web browsers are extremely valuable to hackers. If not for financial gain, black hat hackers may still leak your passwords and personal information for amusement. Never undervalue what you're worth to a hacker.

If you're a regular reader of Next Reality, you're more likely to spread the joy of augmented reality than most others. But it can be difficult to introduce newbies into the AR fold if you don't give them exactly the right starting point in terms ease-of-use and affordability. But fear not, oh gift-giving AR pioneer, we're here to help!

There are a lot of manipulative people out there, but you don't have to let all of them push you around. It's time for the tables to turn.

We've already shown you our favorite new action games that have come out this year, but now it's time to share our all-time top ten list. These games are available for both Android and iPhone, they don't have intrusive ads or freemium schemes, and most importantly, they're all completely free to play.

With a tiny computer, hackers can see every website you visit, exploit services on the network, and break into your Wi-Fi router's gateway to manipulate sensitive settings. These attacks can be performed from anywhere once the attacker's computer has been connected to the router via a network implant.

Microsoft.com is one of the most extensive domains on the internet with thousands of registered subdomains. Windows 10 will ping these subdomains hundreds of times an hour, making it challenging to firewall and monitor all of the requests made by the operating system. An attacker can use these subdomains to serve payloads to evade network firewalls.

As you're surely aware, your phone can be used against you. Thanks to our cameras and microphones, a clever hacker can obtain access to your device and invade your privacy. But spying isn't limited to just these two sensors — gyroscopes, proximity sensors, QR codes, and even ads can be used to paint a very clear picture about who you are and what you're currently doing.

Social engineering makes headlines because human behavior is often the weakest link of even well-defended targets. Automated social engineering tools can help reclusive hackers touch these techniques, but the study of how to hack human interactions in person is often ignored. Today, we will examine how to use subtle, hard to detect persuasion techniques to compromise a human target.

It's odd to see grown humans attempting to bounce off walls doing parkour. It's another thing altogether to see a robot doing it.

My bathroom is like my own private arcade room. Whenever I'm seated comfortably on the toilet, no one is going to disturb me, so I can play anything I want on my smartphone. You probably do it, too — and your parents, kids, friends, colleagues, and boss — so don't be afraid to admit it.

Hello readers, and welcome to Null Byte. Before we start, for those of you who may not know me, my name is ghost_; I'm a relatively active member of our community and have been around for a while.

It only takes a few commands to manipulate a MacBook's secure HTTPS traffic and pluck login passwords out of the encrypted data. Let's take Facebook and Gmail hacking to the next level by intercepting Safari and Google Chrome web traffic in real time.

Conducting phishing campaigns and hosting Metasploit sessions from a trusted VPS is important to any professional security researcher, pentester, or white hat hacker. However, the options are quite limited since most providers have zero-tolerance policies for any kind of hacking, good or bad. After researching dozens of products, we came out with 5 potentials that are ideal for Null Byte readers.

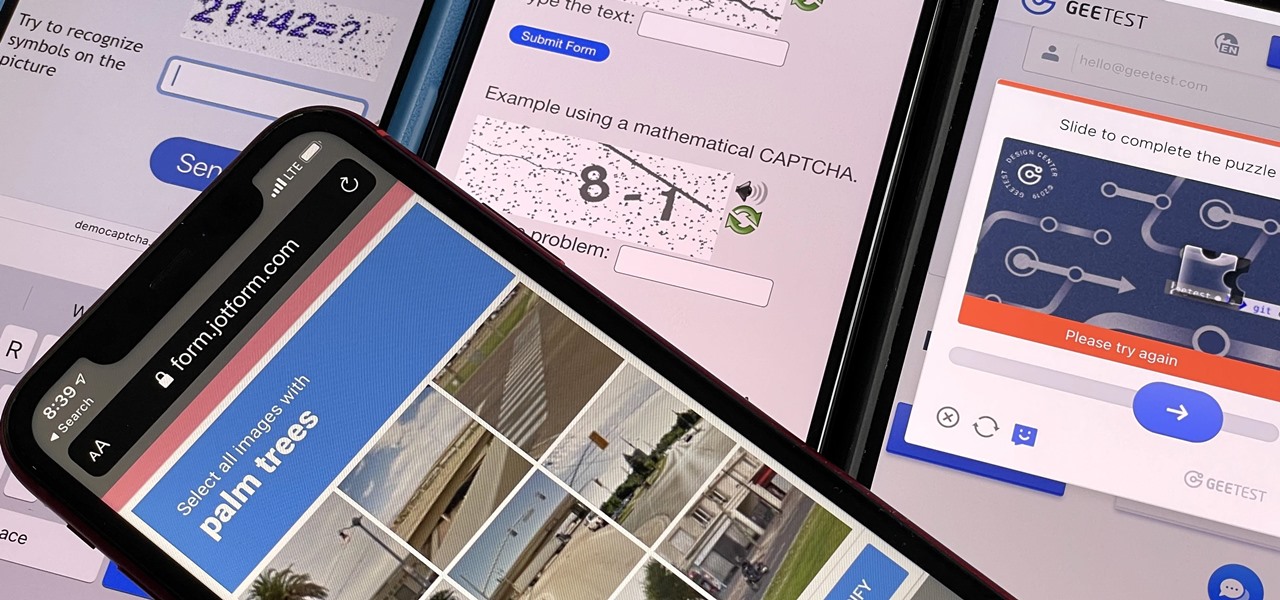
Some websites require you to perform a verification task so they know you're human and not a bot. It helps websites curb spam, abuse, unauthorized access, and cyberattacks but also adds an obstacle for anyone trying to visit their content. If you find it more of a nuisance than a necessary evil, there's an easy way to reduce the number of human verification prompts you receive on your iPhone, iPad, and/or Mac.

It's easier than you might think to hack into Wi-Fi routers using just one unrooted Android phone. This method doesn't require brute-forcing the password, a Windows OS for converting PowerShell scripts into EXE format, a reliable VPS for intercepting hacked Wi-Fi passwords, or Metasploit for post-exploitation tricks.

Apple's macOS operating system is just as vulnerable to attacks as any Windows 10 computer or Android smartphone. Hacker's can embed backdoors, evade antivirus with simple commands, and utilize USB flash drives to completely compromise a MacBook. In this always-updated guide, we'll outline dozens of macOS-specific attacks penetration testers should know about.

With an ordinary birthday card, we can introduce a physical device which contains malicious files into someone's home and deceive them into inserting the device into a computer.

Data can be injected into images quickly without the use of metadata tools. Attackers may use this knowledge to exfiltrate sensitive information from a MacBook by sending the pictures to ordinary file-sharing websites.

The App Store has been around for almost 14 years now, and during that time, we must have seen over a million games come and go and stay and expand. But only a tiny fraction of those games have become blockbuster sensations because of the mighty App Store's reach on iPhone and iPad, and many of the first big hits are still alive today for you to relive the good ol' days of mobile gaming.

Actor and teacher Benson Simmonds speaks on the actor's process that he teaches in this how-to video. This video acting lesson is about objective and obstacle. In addition, he remarks on the importance of the action. Whatever the objective, the actor needs to be able to translate that into a need and to express that feeling. Watch this video acting tutorial and learn how to build a character's objective.

Elise Paffrath began her dog agility career in the early 1970s. Dog agility is a sport in which a handler directs a dog without a leash through an obstacle course in a set amount of time.

Crane You need a giant crane with a magnet.

A pool shooting tutorial. Using a slight right English in this example, the cue ball bypasses an obstacle ball and kicks off the rail, sending the object ball into the pocket. The use of reverse English reduces the rebound angle as the object ball is deflected off the rail which enables you to hit previously unreachable balls. Straighten a kick shot in pool using reverse English.

Welcome to Minecraft World! Check out our advanced tutorials and come play on our free server. You may know that Minecraft is an excellent creative tool, but perhaps less well known are the fascinating array of redstone powered games that have been made by players like you.

China is a hot mess of traffic and is stereotyped for spawning some of the craziest drivers in the world. The traffic jams are known to be so bad, drivers have been gridlocked for 9 straight days.

Beauty and brains in one package! A ceiling fan offers many functional benefits while adding a certain decorative touch to a room. In the summer it can help cool a room (or even a porch) by helping to circulate air and by creating a slight breeze. In the winter it can be used at low speed to circulate warmer air that has risen to ceiling level. From the viewpoint of décor, ceiling fans come in many styles and colors and can even include a light kit to offer the added feature of overhead light...

GreenYou can tell a lot about a person's thought process by MTG color they favor: Red: aggressive, unsubtle, will surpass an obstacle by blowing it to bits with the largest explosives available (or Fireballs, as the case may be

This robot hasn't levitated any humans yet (especially not pictured Days of Our Lives star Deidre Hall), but it looks like the sky may be the limit with the Robo-Air Jet System.

Here's a nice little challenge for you to try this weekend. For those of you with Halo: Combat Evolved Anniversary, and are looking to make an easy 25G, this is for you. The 'How Pedestrian' achievement asks you to walk the entirety of the level "Halo". You know, the massive second level of the game. However, there's one big obstacle standing in your way, and that's where the Achievement Hunters come in. See, you have to grenade jump your way across a pretty large gap. I'd try to explain it, ...

The first thing you need to do in case of any emergency no matter what it is, it would be make a family plan you need to be aware on what are you going to do and this is not no option. Emergency's happen all the time it could happen right know or it may occur tomorrow it does not matter when it happens your suppose to be prepared already.

With the recent death of Osama bin Laden near Islamabad, the whole world has gone crazy for Navy SEALs. Everybody wants to know what it was like for SEAL Team Six to carry out their heroic mission last weekend. Others want to know what it takes to become one.