"Magic The Gathering" has many card types like land, spells, sorcery, enchantments and more, each with its own strategy. Learn "Magic The Gathering" cards and card types from a certified judge in this free magic cards video series.

Welcome back, my greenhorn hackers! One of the most important issues any hacker must address is how to get past security devices and remain undetected. These can include antivirus software, intrusion detection systems, firewalls, web application firewalls, and numerous others. As nearly all of these devices employ a signature-based detection scheme where they maintain a database of known exploits and payload signatures, the key is to either:

ShapeWriter is the iPhone version of Swype. With this app you can type texts extremely fast without ever lifting your finger off the keypad! In this tutorial, learn all about how to type at the speed of light using ShapeWriter and send messages so fast you'll wonder why you ever bothered to type things out in the first place. Have fun!
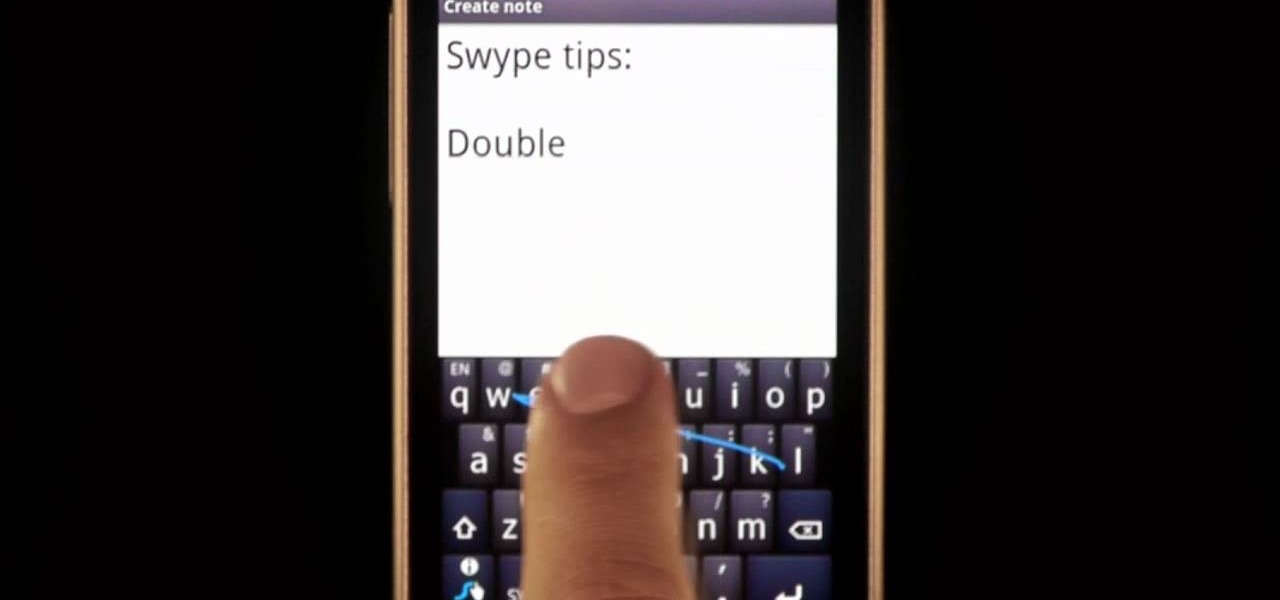
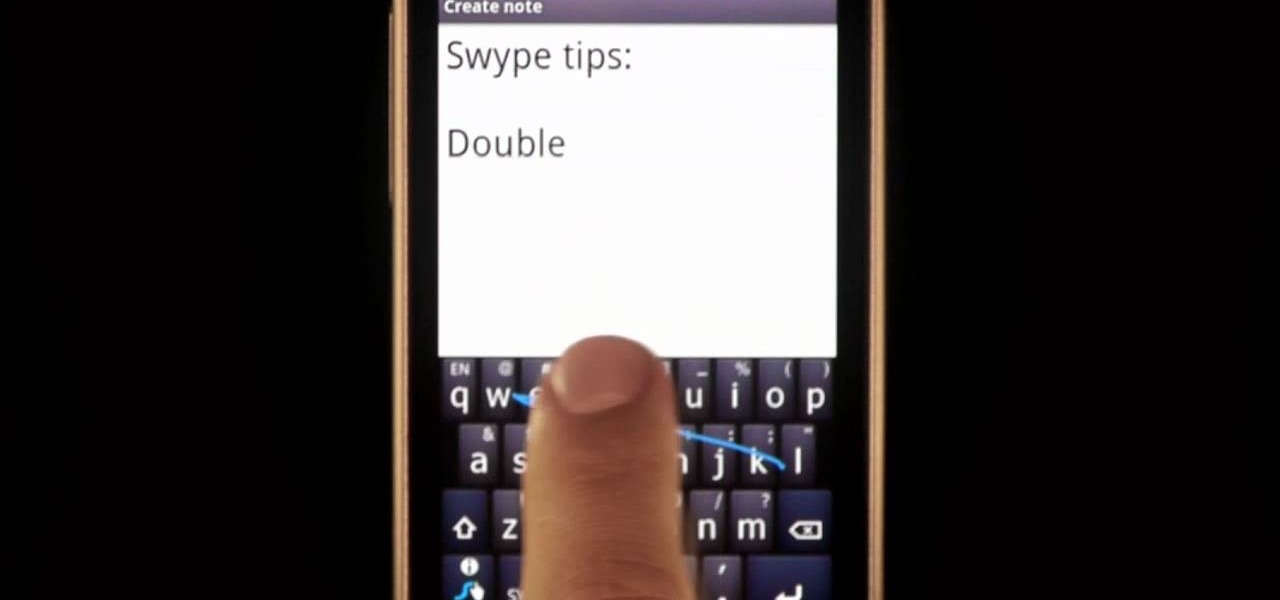
Typing notes with Swype is as fast and easy as you can get and in this clip, learn how to tackle less common word combos like double letters. For example, how would you type "cool", "common", "letters" or "bubble"? In this quick tip tutorial from the makers of Swype, learn how to add these words to your texts and not lose a second of speed! So, follow along and get started typing things like "speed", "follow", "Google".. there is no limit to the "speedy" words you will be sending!

Are you tired of wrinkled clothes? Have you ever had to iron one of your shirts more than once? Get tips and advice on how to fold your various items from ShaNay Norvell in this free clothing care video series.

Looking for a unique picture frame? Learn all about decorative picture frames including rustic frames, veneer frames, ornate and dark wood frames and more in this free video series about professionally framing pictures.

This film was awarded the Green Ribbon in Itami Film Festival, 1993. Learn how various techniques of animation work and see some amazing examples- including an animated pin up girl! The film is in Japanese dialogue with English subtitles.

In this video tutorial, viewers learn how to completely uninstall a program on a Mac computer. There are 2 ways to uninstall applications. The first way is to drag the application into the trash bin. With this method, users will also have to drag the related, numerous preference and supported files. The second ways is to download an application called App Zapper. With this program, users just need to simply drag the application into the App Zapper program to completely uninstall it. This vide...

Mozilla Firefox is the most powerful Internet browser and a good alternative to the plain old Microsoft Internet Explorer. Firefox has many advanced features and is much more customizable in numerous ways. Firefox when installed will have default settings, but you can tweak a few of these internal settings to make it run faster. Now to do this click Control + J shortcut and this brings up the downloads window in Firefox. Now having many files in that list can slow down you browser a little as...

Learn the basics of friendship bracelet making with this easy to understand video. You will learn what is known as the forward knot, the backwards knot, the forward-backwards knot and the backwards-forward knot. With these simple instructions, you can make countless bracelets for friends and family. There are numerous videos showing the how-to of friendship bracelet making, but this video gets back to basics. After you make the knots, you are free to pick a design of your choosing for your br...

There are almost as many types of sutures as there are types of wounds that a human can sustain. This video instructs the viewer in performing one popular type of suture: the vertical mattress stitch. This type of stitch is relatively simple and strong, and thus a good choice for many types of wounds.

By default, there aren't many customization options for the notification badges on iPhones — you can either leave the numbered red bubbles there, or turn them off. But thanks to a new jailbreak tweak, you can now give your badges a unique look with new functionality.

Welcome back, my tenderfoot hackers! WordPress-based websites are among the most numerous on this planet (maybe other planets too, but I can't vouch for that). According to WordPress's own website, WordPress powers 23% of the top 10 million websites. That's approximately 2.3 million sites using WordPress!

Welcome back, my greenhorn hackers! After the disaster that was Windows Vista and the limited and reluctant adoption of Windows 8 and 8.1, Windows 7 has become the de facto standard operating system on the desktop/client.

Captioning your YouTube videos not only makes them more acessable for the hearing impaired, but they also make the contents of your video more accessible to YouTube. Once YouTube knows exactly what is being said it your video you will be more likely to rank when people search for related words or phrases.

Welcome back, my tenderfoot hackers! In some of my past articles, I've shown numerous ways of embedding a listener/rootkit on a remote system, including buffer overflows of the operating system, getting the victim to click on a link to our malicious website, and sending a malicious Microsoft Office and Adobe Acrobat file.

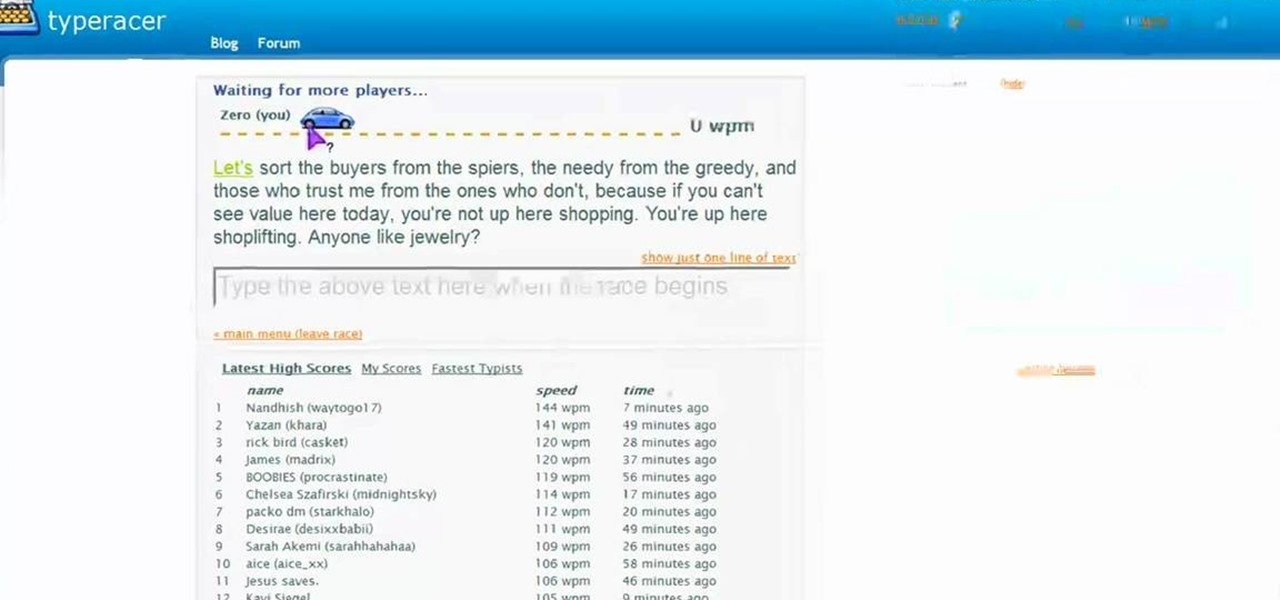
In this tutorial, we learn how to improve your typing speed. First, log onto your internet browser and go to the website, Typeracer. Once you are on this site, you can create an account and start to type on it! When you are on this, you can go into different types of races, then see what your scores are against other people. You continue to type until you win the race you are in. Once you are finished typing, you will see your stats and you will be able to improve from there. This is a great ...

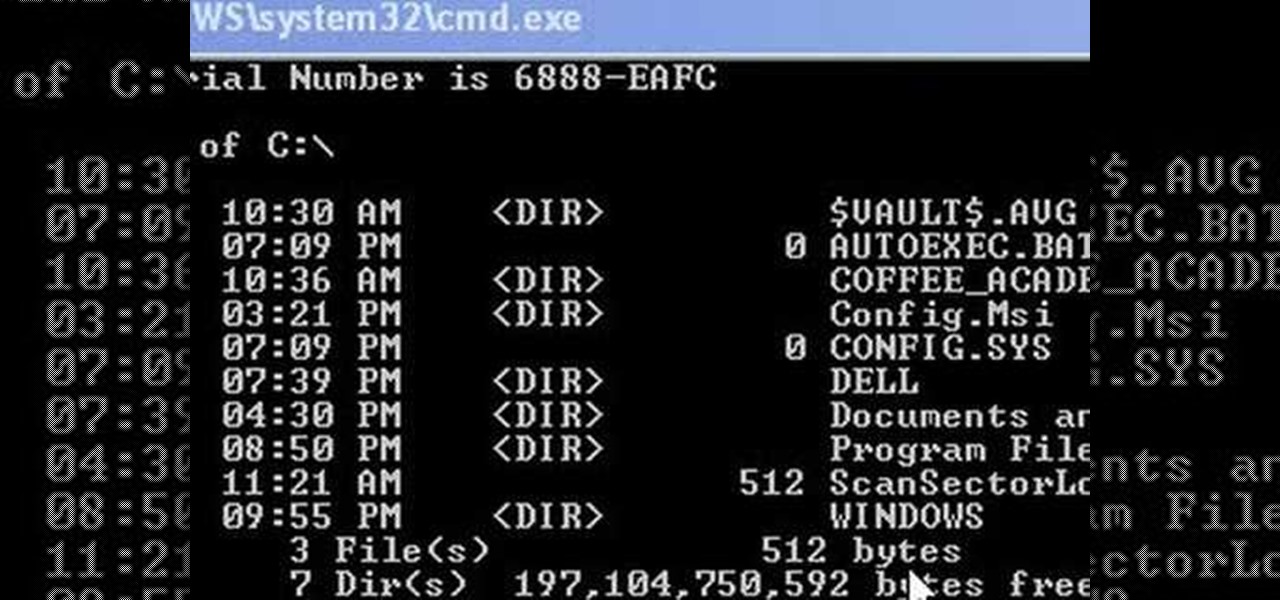
This video shows us how to change driving letters or directories in DOS command. Firstly go to start menu and then click on run. Then type cmd and press OK with which a DOS command cmd window will pop up. Now you need to change the directory and these is done by typing ‘cd..’ and after that press enter. Now you have changed the directory and now you need to see what’s in there and for that type ‘dir’ and press enter and this shows what’s in that directory. Now change to other directory by typ...

Welcome back, my novice hackers! In this continuing series on Metasploit basics, let's next look at a module that many aspiring hackers find useful—autopwn.

Welcome back, my hacker novitiates! As you know by now, the Metasploit Framework is one of my favorite hacking tools. It is capable of embedding code into a remote system and controlling it, scanning systems for recon, and fuzzing systems to find buffer overflows. Plus, all of this can be integrated into Rapid7's excellent vulnerability scanner Nexpose.

In this tutorial, we learn how to use task types in MS Project 2007. First, open up the form view of all the different tasks you have. Now, look at the unit task type and see if it's effort driven or fixed units. Now, change what you want the task type to be and then click on the next button. Assign a second resource if you need to, then change the duration if you need to as well. Continue to change the task types depending on what durations you have then make sure to save this. Double check ...

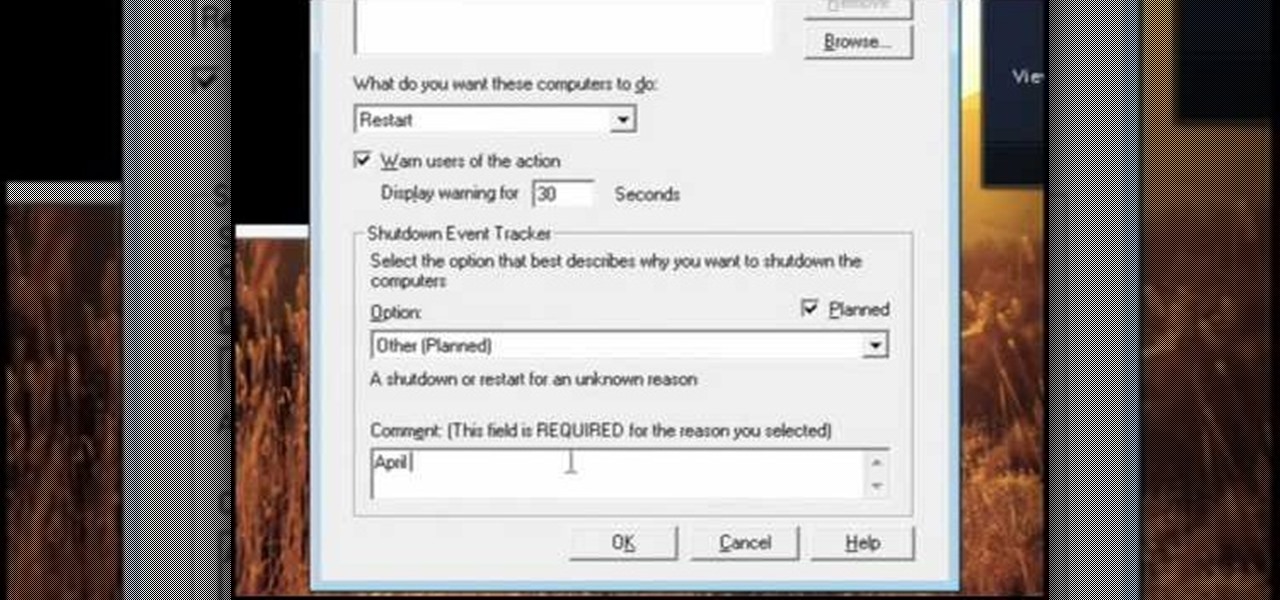
In this video, we learn how to pull a compilation of computer pranks on a friend. The first trip is a mouse prank where you will open up the control panel and find the mouse settings. From here, you can switch the buttons from left to right and change the speeds of the mouse. Next, you can do network pranks by running cmd.exe as administrator. Then, go and see who is on the network and type in "msg /server:(ip address) and message". You can also do a ghost typing prank, which you will create ...

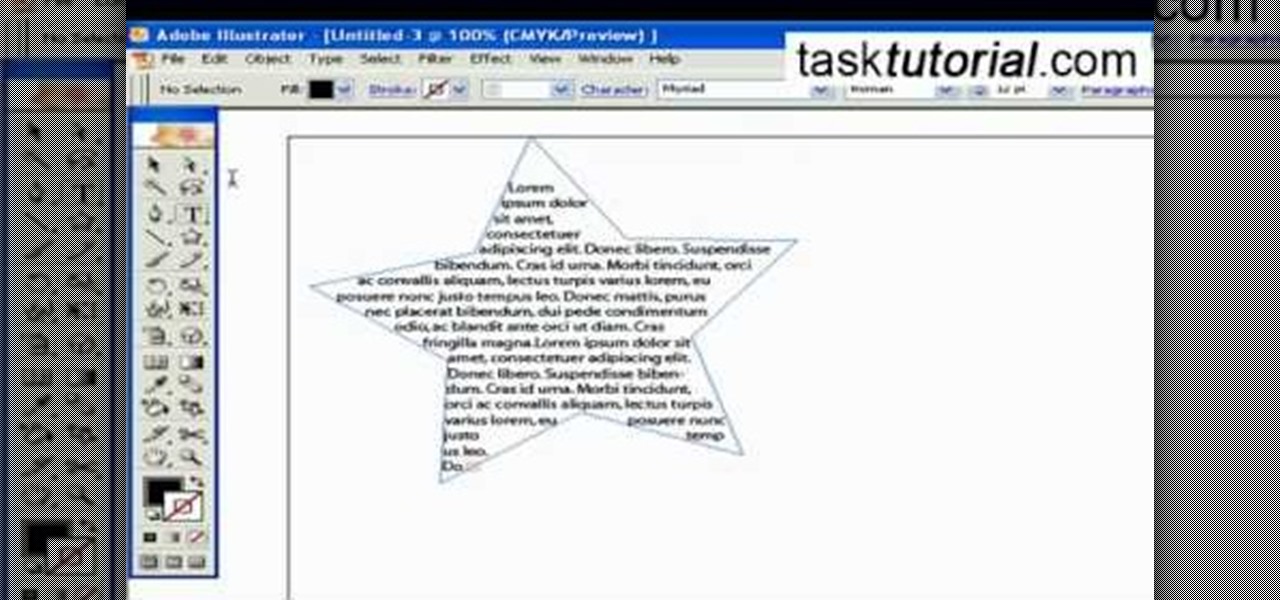
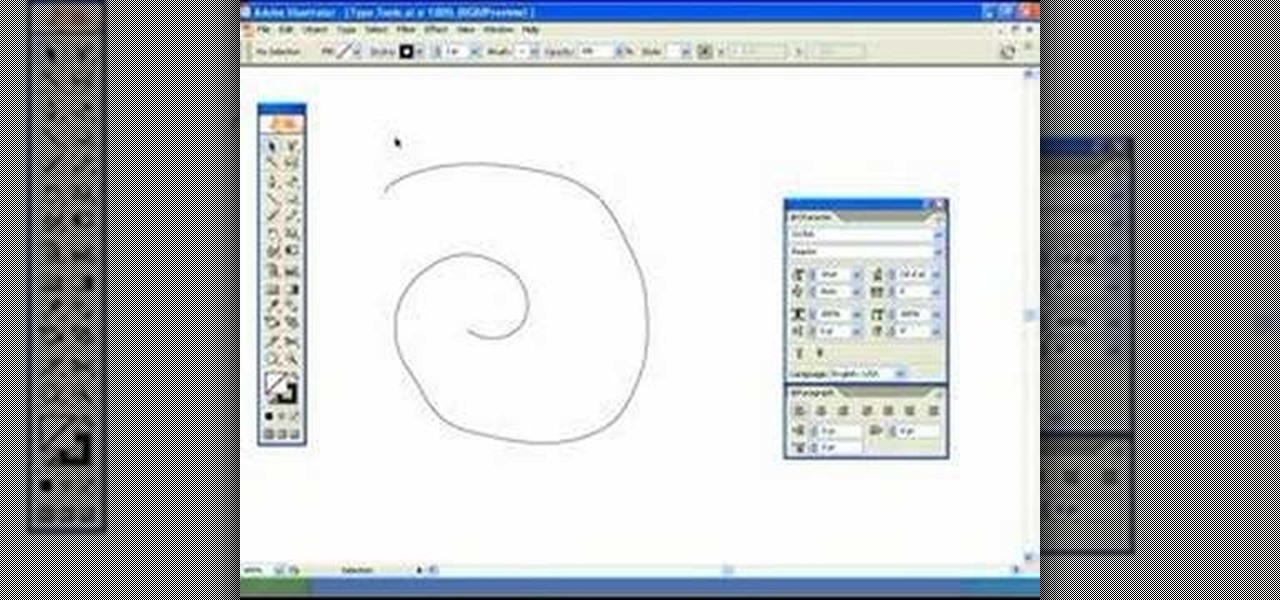
If you want to be serious about using Adobe Illustrator, then learning how to use type is an essential part of your skill set. Type can help you with a wide range of assignments, from designing logos to image building and much more. There are a number of settings and functions when using Type, so it's important to know all of the options that are available to you. This video tutorial will teach you how to use the area type tool in Illustrator.

Want to change your YouTube Channel type? YouTube user webduncetv shows you how. After signing into your YouTube account hover your mouse over user name and click on the word "Account" from the drop down list.

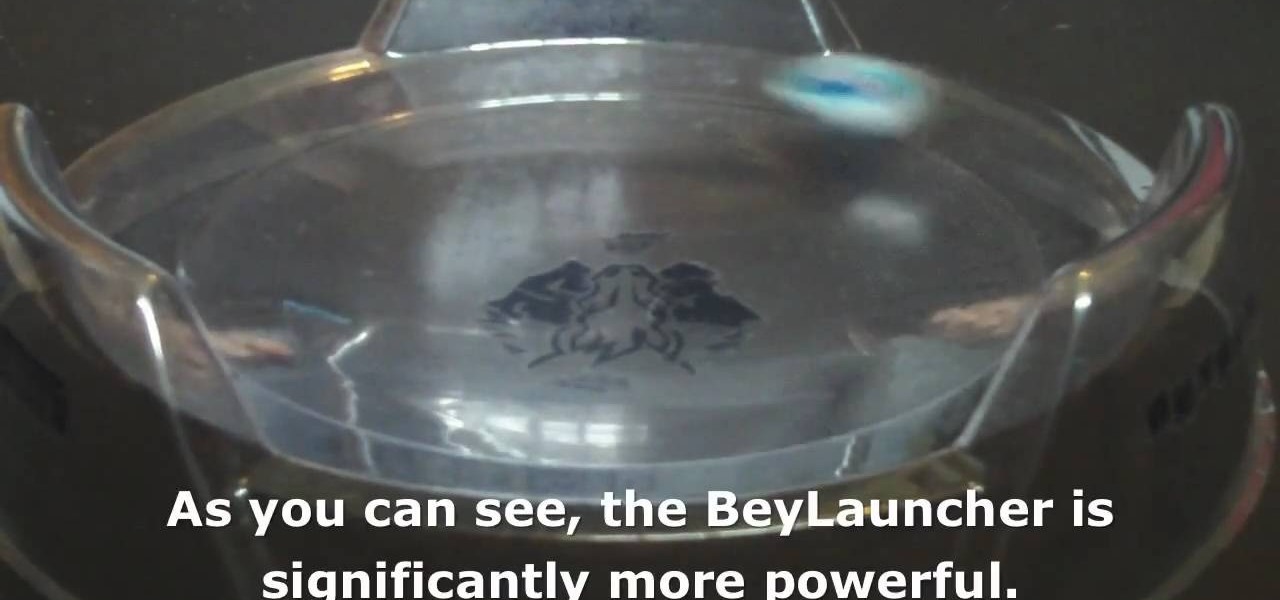
There are two basic types of launchers you can use to play Beyblade: light launchers and Beylaunchers. They are both effective but play rather differently, so watch this video for a rundown of the differences and different strategies for each launcher type.

In this how-to video, you will learn how to choose a dress that flatters your body type. Jazmin Whitley, the designer for Li Cari, will help you with this. There are three body types in this example: long and lean, curvy, and small and curvy. If you are lean, you should accentuate the waist line. A waist band will help. For a curvy figure, look for an empire waist and materials that have flow. For the last body type, clothes should accentuate the waist line and bring balance at the top. This ...

In this tutorial, Scott Atkinson shows us how to identify different types of bulbs. Common types of bulbs are: tulip, daffodil and lily. These are most easily identified but there are many that appear in flowers. A core looks similar to a bulb but it is a solid tissue and doesn't have an leaves, just a hard core with a protective covering. There is also tubers which are what potatoes and other foods grow from. These cause eyes to form and create different types of things to grow. You will now...

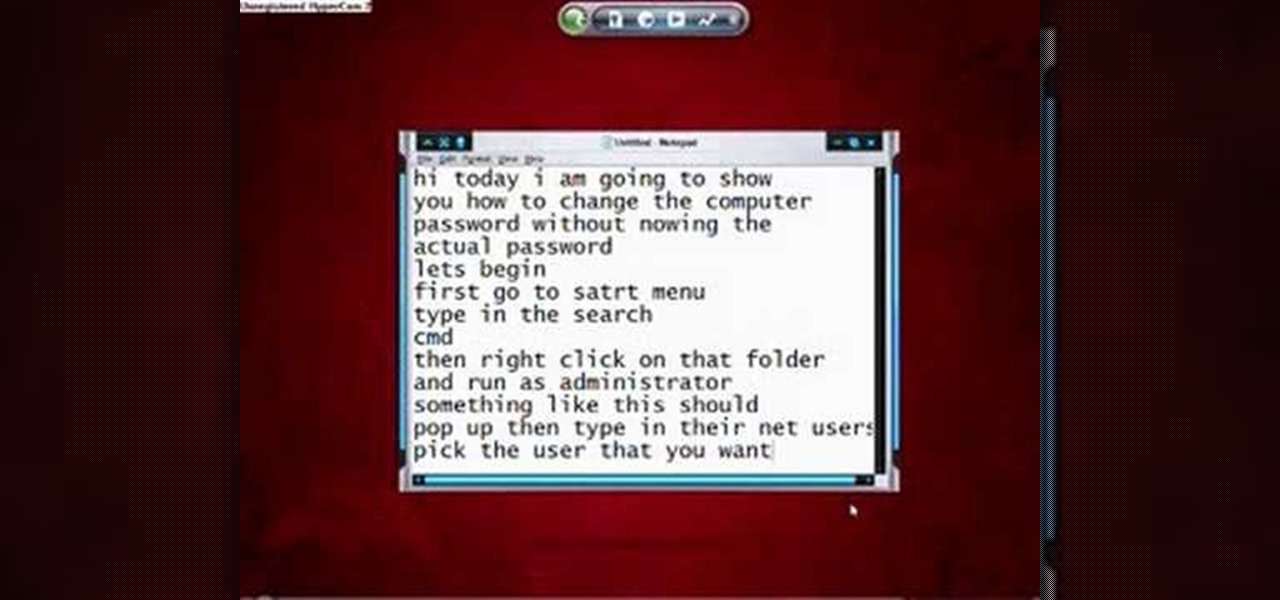
This video shows how to hack the computer password for Vista. We can change the computer password without knowing the actual password. First go to Start menu. Type in the Search "cmd". Then right click on that folder and run as administrator. Then we get a pop up. Type in their net users. Pick the user that we want to hack into. After picking the user type in net user the username and then * . After typing this hit enter key and it should say the command completed successfully and we have to ...

This video is about how to dress to flatter your body type. Curvy body types look good with vertical stripes and clothing that accentuates the waist. High-waisted and belted bottoms and over-sized accessories work well for this body type. Pear body shapes look good in structured clothing. Form fitting tops work well with a smaller bust, making "pears" look slimmer. Cinching in the waist is also flattering for pear body shapes. For athletic body types look good in skinny jeans to show off thei...

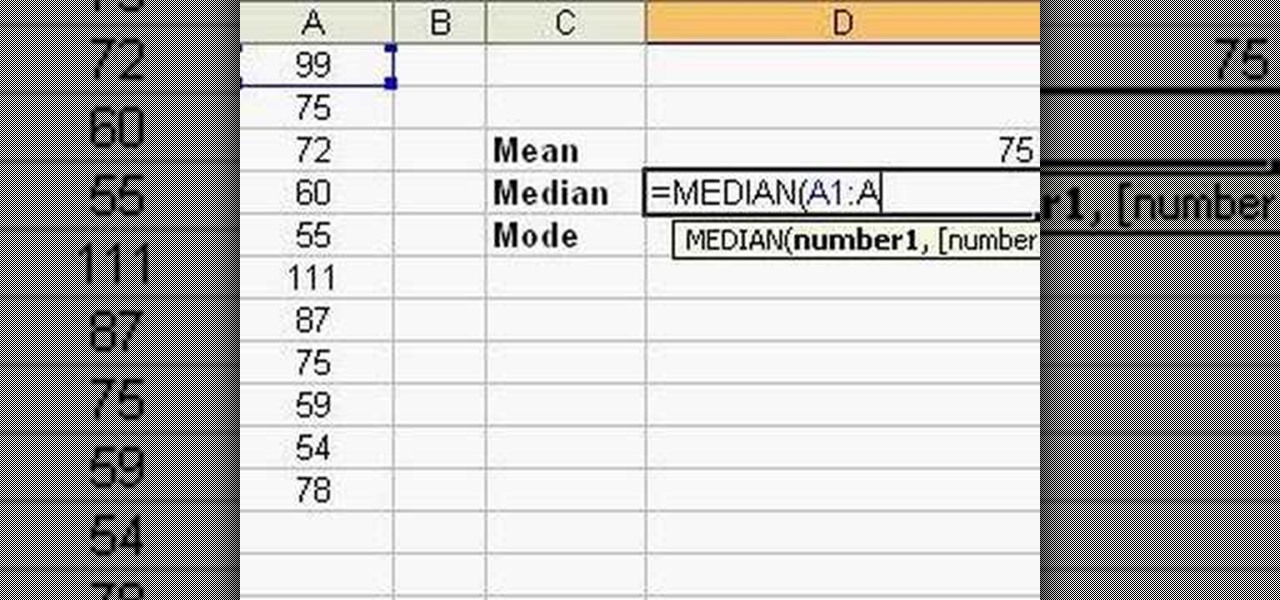
Follow this video to learn how to formulate calculations in Microsoft Excel. First type in a list of numbers in the cells. In order to calculate the median click on the cell where you want the answer to be shown. Then type equals, average, open bracket and insert the cell code where the first number is, colon, and then type in the cell where the last number in the list lies, and close brackets. In practice this is an example where the numbers are in a list from cell A1 to cell A11: =AVEARAGE(...

Get it at: http://www.facebook-bots.com Download it now and beat your friends!

Check out this video on creating type areas and paths in Illustrator. This uses more than just text boxes. You can adjust the font, color and area using the area type tool.

Learn how to airbrush three basic lines types.

In this free video series learn how to tie knots from knot tying expert and outdoor enthusiast Dan Schieffelin.

inDesign has some hidden special effects that will make your type on a path much more compelling. Granted Type on a Path is not a new concept and has been around in Illustrator for years. However, no other application out there can handle Type on a Path as well as InDesign CS2.

Today, Facebook Messenger is rolling out Discover, a feature that helps you chat with companies and locate nearby businesses of interest to you. First discussed in April at Facebook's developer conference F8, Discover is finally available for public use.

Welcome back, my budding hackers! Metasploit, one of my favorite hacking/pentesting tools, has so many capabilities that even after my many tutorials on it, I have only scratched the surface of it capabilities. For instance, it can be used with Nexpose for vulnerability scanning, with Nmap for port scanning, and with its numerous auxiliary modules, nearly unlimited other hacking related capabilities.

Managing hard drives in Linux is crucial to understanding your system and its operation as well as understanding the system you are exploiting or conducting a forensic analysis on. Linux has numerous commands that can provide us with information, control, and management of hard drives, and in this tutorial, we will examine a number of the most important ones.

Welcome back, my tenderfoot hackers! A number of you have written me telling me how much you enjoy the Mr. Robot series on USA Network. I am also a huge fan! If you haven't seen it yet, you should. It may be the best show on TV right now.

Welcome back, my rookie hackers! Most often, the professional hacker is seeking protected information from the target system or network. This might be credit card numbers, personally identifiable information, or intellectual property (formulas, plans, blueprints, designs, etc.). Most of my Null Byte guides have been focused on getting into the system, but this only begs the question—"what do I do when I get there?"