Brute-forcing is an easy way of discovering weak login credentials and is often one of the first steps when a hacker finds network services running on a network they gain access to. For beginners and experienced hackers alike, it's useful to have access to the right tools to discover, classify, and then launch customized brute-force attacks against a target. BruteDum does it all from a single framework.

While Wi-Fi networks can be set up by smart IT people, that doesn't mean the users of the system are similarly tech-savvy. We'll demonstrate how an evil twin attack can steal Wi-Fi passwords by kicking a user off their trusted network while creating a nearly identical fake one. This forces the victim to connect to the fake network and supply the Wi-Fi password to regain internet access.

Hi, dear co-apprentices and wise masters. I've been recently trying to learn the basics to hacking here, and I've read all guides on Wi-Fi hacking and noticed no word is dedicated to this awesome script that comes bundled with Kali!
Welcome back my social engineers/hackarians! Today we'll be looking into a fantastic piece of software, The Social-Engineer Toolkit or just SET for short. SET is designed, Developed and used by several Social-engineers. So... Let's get started!

Transition from day to night makeup by enhancing the colors and shades on the face. Learn about day and night makeup with this free beauty guide video series.

In this video series, our expert John Carstarphen will show you how to create boolean scripts, create the first light, streetlights, mood, and depth. He will also show you how to edit colors, do a graduated background, add illumination, and how to use volumetric light and shadows.

Taking professional photographs at night poses a whole new set of problems relative to taking pictures during the day. This four-part video is here to help, in great detail. It covers several topics, including subject selection, tools necessary, deterring depth of field, and all of the other things that you will have to do to take really good-looking photos at night.

Learn how to sleep in your car, and get a good night's sleep. This video will teach you how to outlast the economy in the wilderness, or your local Wal-Mart parking lot. If nothing else, you can do a road trip on the cheap, since you probably don't have a job anymore.

Check out this instructional video and learn how to hack a simple flashlight and transform it into a night vision flashlight! The items you'll need for the project cost less than ten dollars and you get a perfect night vision view. Watch this how-to video and learn how to build a night vision flashlight on the cheap.

ARP spoofing is an attack against an Ethernet or Wi-Fi network to get between the router and the target user. In an ARP-spoofing attack, messages meant for the target are sent to the attacker instead, allowing the attacker to spy on, deny service to, or man-in-the-middle a target. One of the most popular tools for performing this attack is Ettercap, which comes preinstalled on Kali Linux.

Users are often the weakest link when probing for vulnerabilities, and it's no surprise they can be easily fooled. One way to do this is called clickjacking. This type of attack tricks the victim into clicking something they didn't mean to click, something under the attacker's control. Burp Suite contains a useful tool called Clickbandit to generate a clickjacking attack automatically.

A vulnerability in the design of LiDAR components in driverless cars is far worse than anything we've seen yet outside of the CAN bus sphere — with a potentially deadly consequence if exploited.

While the USB Rubber Ducky is well known by hackers as a tool for quick in-person keystroke injection attacks, one of the original uses for it was automation. In this guide, I'll be going the latter, explaining how we can use it to automate Wi-Fi handshake harvesting on the Raspberry Pi without using a screen or any other input.

With tools such as Reaver becoming less viable options for pen-testers as ISPs replace vulnerable routers, there become fewer certainties about which tools will work against a particular target. If you don't have time to crack the WPA password or it's unusually strong, it can be hard to figure out your next step. Luckily, nearly all systems have one common vulnerability you can count on — users!

Welcome back, my fledgling hackers! Over the years, we have examined multiple ways to own, exploit, or compromise a system. On the other hand, we have not spent a lot of time on denial-of-service (DoS) attacks.

Welcome back, my hackers novitiates! As you read my various hacking tutorials, you're probably asking yourself, "What are the chances that this hack will be detected and that I'll land behind bars, disappointing my dear mother who already thinks I'm a loser?"

Tired of being attacked by the goblin army in Terraria? Here's a sure-fire, or rather sure-lava, method for defeating them. Watch this video to learn how to design a lava trap that will make the goblin army vulnerable to your attacks.

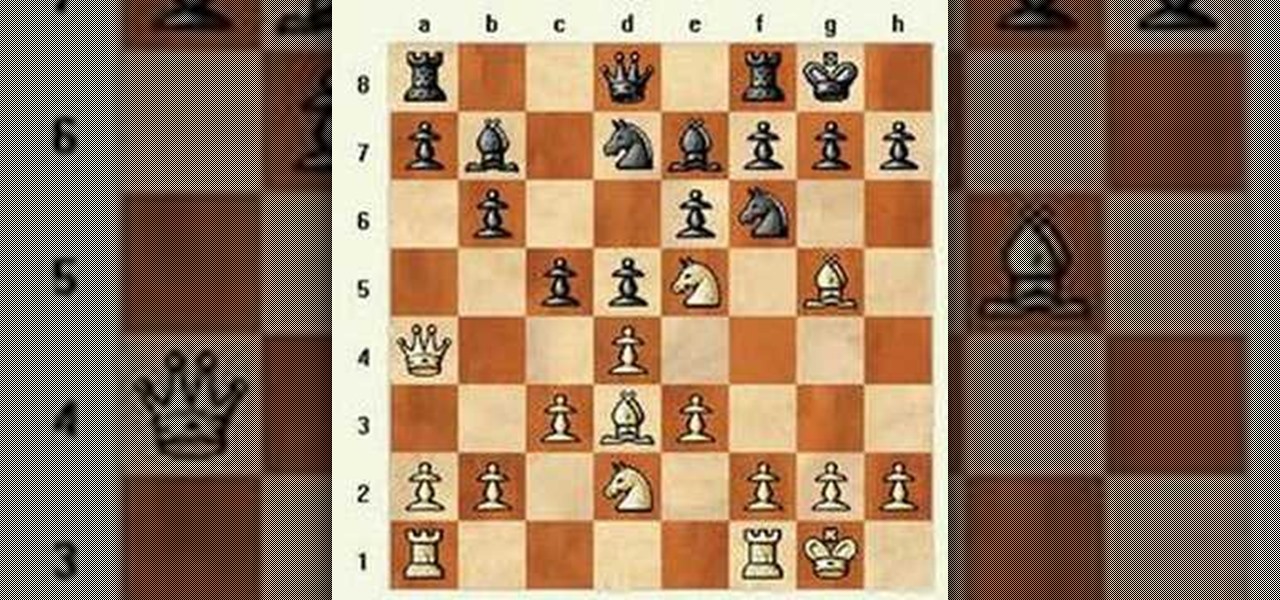
This is a match that takes a look at rapidly changing from a queen side attack to a king side attack, and how that can sometimes catch your opponent off guard. The match also shows how creating complications can sometimes mask the most deadly, yet subtle threat.

Here is a match with a Reti Opening transposing to a King's Indian Attack. See how to do it, and see why to do it.

This is an introduction to the Veresov Attack 1.d4 Nf6 2.Nc3. It features a game in which Matt crushes a reasonably strong guest who only makes 2 very natural looking errors (...O-O and ...c4). Try it out for yourself.

In this series, Matt will examine the Stonewall Attack for White and display defenses which he thinks are challenging and/or interesting. Here's a prototypical Stonewall game where everything goes right for White.

This video demonstrate a system against the King's Indian Attack. Enjoy! And don't get too good, because if we ever play, I don't want to lose.

This is a trap in the Torre Attack (1.d4 2.Nf3 3.Bg5). It's a favorite in opening traps, so watch and learn. You'll need it someday.

'Enemies Among Us' is one of the longest, most involved quest in Dragon Age 2, and this walkthrough of it spans a whopping five videos. Stick with it, it's really goods stuff and great viewing even if you aren't stuck on this quest.

In this video tutorial you'll learn how to play the Three Dog Night version of Hoyt Axton's "Joy to the World" on the ukulele. This video lesson covers both the song's chords changes and various strumming patterns. For more information, and to get started playing Three Dog Night's "Joy to the World" on your own ukulele, watch this helpful video guide.

In this video tutorial you'll learn how to play the Three Dog Night version of Hoyt Axton's "Joy to the World" on the ukulele. This video lesson covers both the song's chords changes and various strumming patterns. For more information, and to get started playing Three Dog Night's "Joy to the World" on your own ukulele, watch this helpful video guide.

Your job is to defeat Sapientia in this fight on the Xbox 360 game Bayonetta. In Chapter 13 - The Cardinal Virtue of Prudence, attack the red sphere over Sapientia's head. This fight starts with Bayonetta on the ocean, on a surfboard-like object. Sapientia will use two attacks. The first attack starts with his fin sticking out of the water, like a shark. He will then jump into the air and dive at you. Just keep moving in a straight line to avoid this attack. For the second attack the camera w...

Justin Sandercoe teaches you a beautiful but simple solo guitar arrangement of the Christmas song Silent Night. The first video shows left hand only, the second right hand only.

You may have heard of a signal jammer before, which usually refers to a device that blasts out a strong enough radio signal to drown out the reception of nearby devices like cell phones. Purpose-built jammer hardware is outright illegal in many countries. Still, Wi-Fi is vulnerable to several different jamming attacks that can be done with Kali Linux and a wireless network adapter.

Sophisticated hackers have been exploiting vulnerabilities in Chrome and Firefox to trick even the most careful internet users into logging into fake domains for sites like Apple, Google, and Amazon.

Welcome back, my rookie hackers!

Long Night of Solace, one of those missions with an actual space flight level! You don't really see that sort of thing in gaming these days, exciting right? You can also get a great achievement in this mission! But if you're playing this on Legendary it can be pretty tough, and if you're stuck recharging your shields more than wiping out the Covenant forces, check out this video! You will get a full walkthrough of the mission Long Night of Solace in Halo: Reach on the Xbox 360.

Night vision goggles are one of the iconic pieces of equipment of the modern military. Getting a real pair is prohibitively expensive, especially if you just want to use it as a prop in your film instead of actually seeing at night. This video features instructions for making your own set of prop night vision goggles for cheap, giving any action or spy movie that you are making a much more modern, authentic feel. Also, now your characters can see at night, opening up all sorts of potential sc...

Street Fighter IV : Blanka, the Brazilian Beast unleashes havoc upon the World Warriors once again. Street Fighter IV is a 2008 fighting game produced by Capcom. Street Fighter IV is currently released for PlayStation 3 and Xbox 360, with a Microsoft Windows version in the works as well.

Street Fighter IV : Vega, the beautiful Spaniard delivers gruesome damage. Street Fighter IV is a 2008 fighting game produced by Capcom. Street Fighter IV is currently released for PlayStation 3 and Xbox 360, with a Microsoft Windows version in the works as well.

A flaw in WPS, or WiFi Protected Setup, known about for over a year by TNS, was finally exploited with proof of concept code. Both TNS, the discoverers of the exploit and Stefan at .braindump have created their respective "reaver" and "wpscrack" programs to exploit the WPS vulnerability. From this exploit, the WPA password can be recovered almost instantly in plain-text once the attack on the access point WPS is initiated, which normally takes 2-10 hours (depending on which program you use).

So you like card games, huh? Don't we all. Well, have you ever heard of Heart Attack? I didn't think so.

You invited a girl over for a night of pleasure, but once you're done, how do you get rid of her? This dating how-to video offers some informative advice on how to get rid of your one night stand. She suggest two ways of doing this, the douchebag method and the non-douchebag way. Find out more about getting rid of a one night stand in this video.

The tactic of brute-forcing a login, i.e., trying many passwords very quickly until the correct one is discovered, can be easy for services like SSH or Telnet. For something like a website login page, we must identify different elements of the page first. Thanks to a Python tool for brute-forcing websites called Hatch, this process has been simplified to the point that even a beginner can try it.

Web 2.0 technology has provided a convenient way to post videos online, keep up with old friends on social media, and even bank from the comfort of your web browser. But when applications are poorly designed or incorrectly configured, certain flaws can be exploited. One such flaw, known as CSRF, allows an attacker to use a legitimate user's session to execute unauthorized requests to the server.